-
Systems Engineering Principles and Practice, 2nd Edition
Author Steven M. Biemer , Samuel J. Seymour , William N. Sweet , Alexander Kossiakoff
The Bestselling Guide to the Engineering of Complex Systems, Now Thoroughly UpdatedThe first edition of this unique interdisciplinary guide has become the foundational systems engineering textbook for colleges and universities worldwide. It has helped countless rea....
Release Date 2011/05 -
Author Sunil Wadhwa , Joe Kelly , Ken Draper , David Delcourt , Vik Davar , Stefan Brunner
Written by key members of Juniper Network's ScreenOS development team, this one-of-a-kind Cookbook helps you troubleshoot secure networks that run ScreenOS firewall appliances. Scores of recipes address a wide range of security issues, provide step-by-step solutio....
Release Date 2008/02 -
Author Max Muller
Human resource law is a complex, confusing compilation of federal, state, county and city laws and ordinances cured in the crucible of the courtroom. The Legal Side of HR Practice leads human resources professionals, managers, supervisors, and students through the ....
Release Date 2012/01 -
Author P. Carlo Cacciabue , Erik Hollnagel , Pietro C. Cacciabue , Jean-Michel Hoc
Technological development has changed the nature of industrial production so that it is no longer a question of humans working with a machine, but rather that a joint human machine system is performing the task. This development, which started in the 1940s, ha....
Release Date 2013/06 -
Complex Systems and Systems of Systems Engineering
Author Jean-Luc Wippler , Jean-René Ruault , Dominique Luzeaux
With the growing maturity of information and communication technologies, systems have been interconnected within growing networks, yielding new services through a combination of the system functionalities. This leads to an increasing complexity that has to be manage....
Release Date 2011/10 -
Author David D. Busch
DAVID BUSCH'S NIKON D3200 GUIDE TO DIGITAL SLR PHOTOGRAPHY is your onestop resource and reference for the Nikon D3200, the latest entrylevel DSLR in the Nikon product line, featuring a 16.2 megapixel sensor, full HDTV video, and ISO up to 12,800. With this book in ....
Release Date 2012/07 -
Author Anmol Misra , James Ransome
"... an engaging book that will empower readers in both large and small software development and engineering organizations to build security into their products. ... Readers are armed with firm solutions for the fight against cyber threats."—Dr. Dena Haritos Tsamiti....
Release Date 2013/12 -
Software Engineering: A Methodical Approach
Author Elvis C. Foster
This text provides a comprehensive, but concise introduction to software engineering. It adopts a methodical approach to solving software engineering problems proven over several years of teaching, with outstanding results.The book covers concepts, principles, d....
Release Date 2014/12 -
Key Case Law Rules for Government Contract Formation
Author Patrick Butler
Go Beyond the FAR!The guidance contained in the almost 2000 pages of the Federal Acquisition Regulation and the various agency supplements are just a part of the resources government acquisition professionals need to do their jobs effectively. Accessing and un....
Release Date 2014/09 -
Learning Nessus for Penetration Testing
Author Himanshu Kumar
Master how to perform IT infrastructure security vulnerability assessments using Nessus with tips and insights from real-world challenges faced during vulnerability assessmentIn DetailIT security is a vast and exciting domain, with vulnerability assessment and penet....
Release Date 2014/01 -
The Ransomware Threat Landscape
Ransomware will cost companies around the world $20 billion in 2021. Prepare for, recognise and survive ransomware attacks with this essential guide which sets out clearly how ransomware works, to help business leaders better understand the strategic risks, and explores measures that can be put in p.... -
Incident Response with Threat Intelligence
Author Roberto Martínez
Learn everything you need to know to respond to advanced cybersecurity incidents through threat hunting using threat intelligenceKey FeaturesUnderstand best practices for detecting, containing, and recovering from modern cyber threatsGet practical experience embracing incident response using intelli....
Release Date 2022/06 -
Practical Threat Intelligence and Data-Driven Threat Hunting
Get to grips with cyber threat intelligence and data-driven threat hunting while exploring expert tips and techniquesKey FeaturesSet up an environment to centralize all data in an Elasticsearch, Logstash, and Kibana (ELK) server that enables threat huntingCarry out atomic hunts to start the threat h.... -
Enhancing Learning and Teaching Through Student Feedback in Social Sciences
Author Patricie Mertova , Chenicheri Sid Nair
This title is the second Chandos Learning and Teaching Series book that explores themes surrounding enhancing learning and teaching through student feedback. It expands on topics covered in the previous publication, and focuses on social science disciplines. The edi....
Release Date 2013/02 -
ISO27001 / ISO27002 A Pocket Guide
Author Alan Calder
Use ISO27001 to protect your organisation's information assets This helpful, handy ISO27001/ISO27002 pocket guide gives a useful overview of these two important information security standards. Read this pocket guide to learn about: The ISO/IEC 27000Family of Info....
Release Date 2008/10 -
Nmap 6: Network Exploration and Security Auditing Cookbook
Author Paulino Calderon Pale
Want to master Nmap and its scripting engine? Then this book is for you – packed with practical tasks and precise instructions, it’s a comprehensive guide to penetration testing and network monitoring. Security in depth.Master the power of Nmap 6Learn how the Nmap S....
Release Date 2012/11 -
Author Ashok Mohanty , Jibitesh Mishra
Software Engineering covers both function oriented as well as object oriented (OO) approach and emphasises on emerging areas such as 'web engineering', 'software maintenance' and 'component based software engineering'. This book further includes case studies o....
Release Date 2011/07 -
CCSP Self-Study: Cisco Secure Intrusion Detection System (CSIDS)
Author Earl Carter
Understand how Cisco IDS can be used to protect, monitor, and enforce physical security policiesReview techniques applicable to both network- and host-based platformsReview the security wheel concepts and apply security to AVVID using the SAFE BlueprintInstall and c....
Release Date 2004/02 -
Mike Meyers's CompTIA Security+ Certification Passport, Fourth Edition (Exam SY0-401)
Author T. J. Samuelle , Dawn Dunkerley
From the #1 Name in Professional CertificationPrepare for CompTIA Security+ Exam SY0-401 with McGraw-Hill Professional—a Platinum-Level CompTIA Authorized Partner offering Authorized CompTIA Approved Quality Content to give you the competitive edge on exam day.Get o....
Release Date 2014/06 -
Author Richard Enbody , Aditya Sood
Cyber-crime increasingly impacts both the online and offline world, and targeted attacks play a significant role in disrupting services in both. Targeted attacks are those that are aimed at a particular individual, group, or type of site or service. Unlike worms and....
Release Date 2014/04 -
How to Become an International Disaster Volunteer
Author Michael Noone
How to Become an International Disaster Volunteer discusses the immense value an experienced water systems engineer, trauma surgeon, or communications specialist could bring to a disaster stricken community, while also explaining how their professional educations d....
Release Date 2017/02 -
A Short Overview of Social Networks and Their Uses
Author Juliette Powell
This Element is an excerpt from 33 Million People in the Room: How to Create, Influence, and Run a Successful Business with Social Networking (9780137154357) by Juliette Powell. Available in print and digital formats.Profiling the world of social networks: what you ....
Release Date 2010/05 -
Author Luke Wroblewski
Our industry’s long wait for the complete, strategic guide to mobile web design is finally over. Former Yahoo! design architect and co-creator of Bagcheck Luke Wroblewski knows more about mobile experience than the rest of us, and packs all he knows into this entert....
Release Date 2011/05 -
The PayPal Official Insider Guide to Internet Security: Spot scams and protect your online business
Author Michelle Savage
Technology moves fast. So do criminals. Cyber attacks hit large and small merchants alike, phishers and fraudsters seem to be everywhere, and identity theft is prevalent. But this is not the end of the world, and you can’t afford to hide in the closet. Your customer....
Release Date 2012/10 -
Performing Information Governance: A Step-by-Step Guide to Making Information Governance Work
Author Anthony David Giordano
Make Information GovernanceWork: Best Practices, Step-by-Step Tasks, and Detailed DeliverablesMost enterprises recognize the crucial importance of effective information governance. However, few are satisfied with the value of their efforts to date. Information gover....
Release Date 2014/09 -
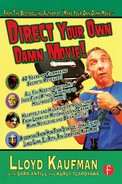
Author Lloyd Kaufman
Film is a visual medium, the work of Eric Rohmer and Kevin Smith notwithstanding. It is important for a director and cinemtographer to use their VISUAL EYES in order to VISUALIZE how to make their movie most effective. Also, there is the messy business of actors. ....
Release Date 2013/04 -
Author Neal Allen
Network Maintenance and Troubleshooting GuideField-Tested Solutions for Everyday Problems, Second EditionNeal AllenThe 100% practical, real-world guide to anticipating, finding, and solving network problems—fast!Real-life networks don’t always behave “by the book.” ....
Release Date 2009/10 -
Network Access Control For Dummies®
Author Denzil Wessels , Rich Campagna , Jay Kelley
Network access control (NAC) is how you manage network security when your employees, partners, and guests need to access your network using laptops and mobile devices. Network Access Control For Dummies is where you learn how NAC works, how to implement a program, a....
Release Date 2009/05