In this chapter, you will learn about sniffing and how this technique is used. You will gain an understanding of protocols that may be vulnerable to sniffing and how to detect types of sniffing attacks. In this chapter, you will also be introduced to countermeasures for sniffing. You will also learn about different types of social engineering plus countermeasures to protect individuals from attack.
- 1.
Identify types of sniffing and the protocols vulnerable to sniffing.
- 2.
Recognize types of sniffing attacks.
- 3.
Identify methods for detecting sniffing.
- 4.
Identify countermeasures for sniffing.
- 5.
Identify different types of social engineering and social engineering countermeasures.
Sniffers
Sniffers are programs that monitor data on a network. Monitoring programs use sniffers to produce metrics and are used for analysis, and the sniffer does not intercept or alter data. Alternatively, sniffing is used to steal passwords, emails, and files on a network.
In this chapter, you will learn about the fundamental concepts of sniffing and how sniffers are used in hacking. It is important for an administrator to know about sniffers and be aware of various tools and techniques to secure a network.
Switched Ethernet

Switched network
Types of Sniffing
Passive sniffing: Using a switch on a network is a countermeasure against passive sniffing. On a switched network, if there is a passive sniffer, it can only see data that goes to and from the machine on which it is installed. Passive sniffing is common on networks with hubs where the data is gathered from all machines. An active sniffing switch actively monitors the MAC address on each port and injects traffic into the LAN to enable sniffing of traffic.
- Active sniffing: An active sniffing switch actively monitors the MAC address on each port and injects traffic into the LAN to enable sniffing of traffic. Active sniffers can be classified as address resolution protocol (ARP) spoofing, MAC flooding, and MAC duplicating.
The result of ARP spoofing is that the target machine has the wrong entry for the gateway, so all traffic destined for the gateway will now pass through the attacker system.
If a switch gets flooded with MAC addresses to the point that it cannot keep up, the switch enters a “failopen mode” and it will start broadcasting packets to all ports on the switch just like a hub would.
MAC duplicating occurs when the network is sniffed for MAC addresses of clients that associate with a switch port and reuses one of those addresses .
Protocols Vulnerable to Sniffing
Protocols that send passwords and data in clear text across the network are vulnerable to sniffing. Do not let the requirement of a username and password lull you into a false sense of security.
Telnet
Simple Network Protocol (SNMP)
Network News Transfer Protocol (NNTP)
Post Office Protocol (POP)
Hypertext Transfer Protocol (HTTP)
File Transfer Protocol (FTP)
Internet Message Access Protocol (IMAP)
Electronic Surveillance
There is an application for sniffing as a legal tool. Electronic surveillance when authorized by a judicial administrative order uses a wiretap to gather data using the target’s service provider, for example. Mediation devices handle the processing and tools used include Wireshark and Tcpdump.
How to Detect Sniffing

Process for detecting sniffing
Ping method : The investigator using the ping method changes the MAC address of the suspect computer in the route table and then sends a ping with the IP address and the modified MAC address. A system with a sniffer responds to this ping.
ARP method : A system that responds to a non-broadcast IP address request is suspected of executing a sniffer.
Source-route method : The loose-source route lists the IP address of systems that the packets travel to reach the destination machine. If a machine with an IP address in the loose-source route fails, the packet cannot reach the destination. If the investigator disables one of the computers within the path and the packets still reach the destination, it is likely that the destination computer is running a sniffer.
Decoy method : The decoy method uses a decoy server with dummy user accounts and a client with a script to connect to the server. With an intrusion detection system (IDS), the investigator can see when an attacker tries to log in.
Reverse DNS Method : Some sniffers perform reverse DNS lookups to determine a domain name that is linked to a particular IP address. The computer carrying out the reverse DNS lookup responds to the ping, which recognizes it as having a sniffer.
Latency method : With the latency method, the investigator calculates the response times of the pings to determine what system the excessive load affects. A computer running a sniffer is the one that has a longer response time and is affected by the higher load.
Wget

Wget
Spearfish Attack
The copied website exists on the attacker’s machine. The attacker now uses spear phishing to get an internal user to go to the site and enter their credentials.
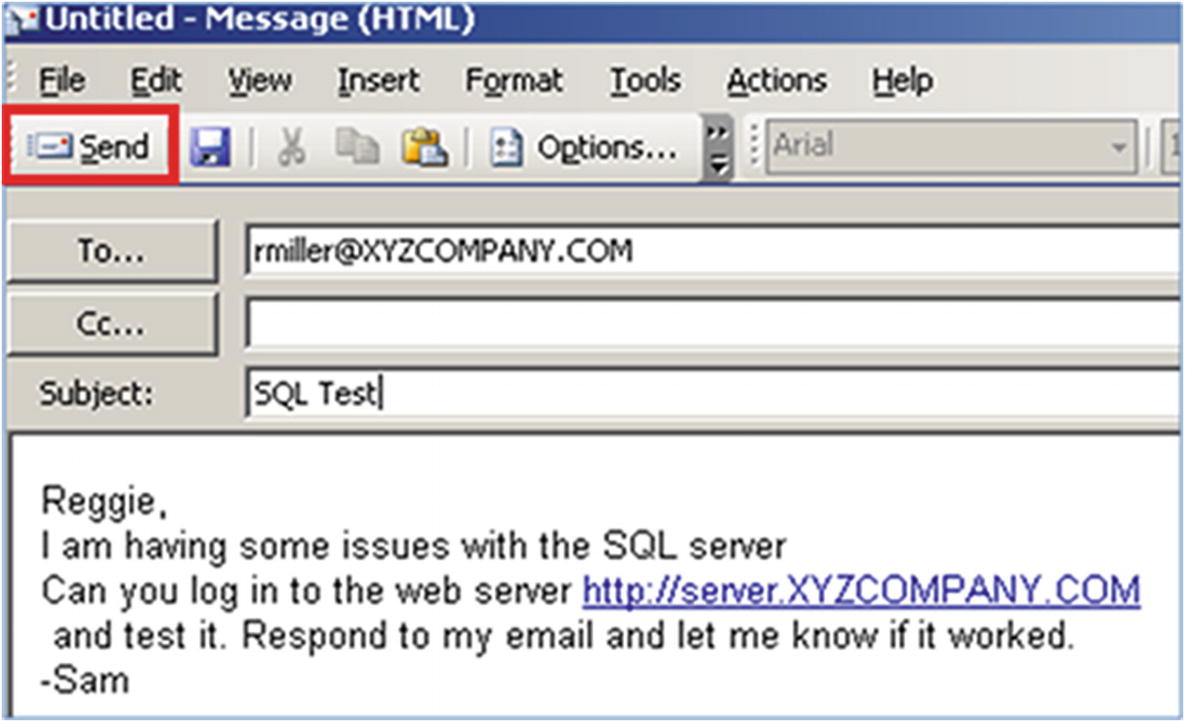
Spearfish attack
Viewing Credentials
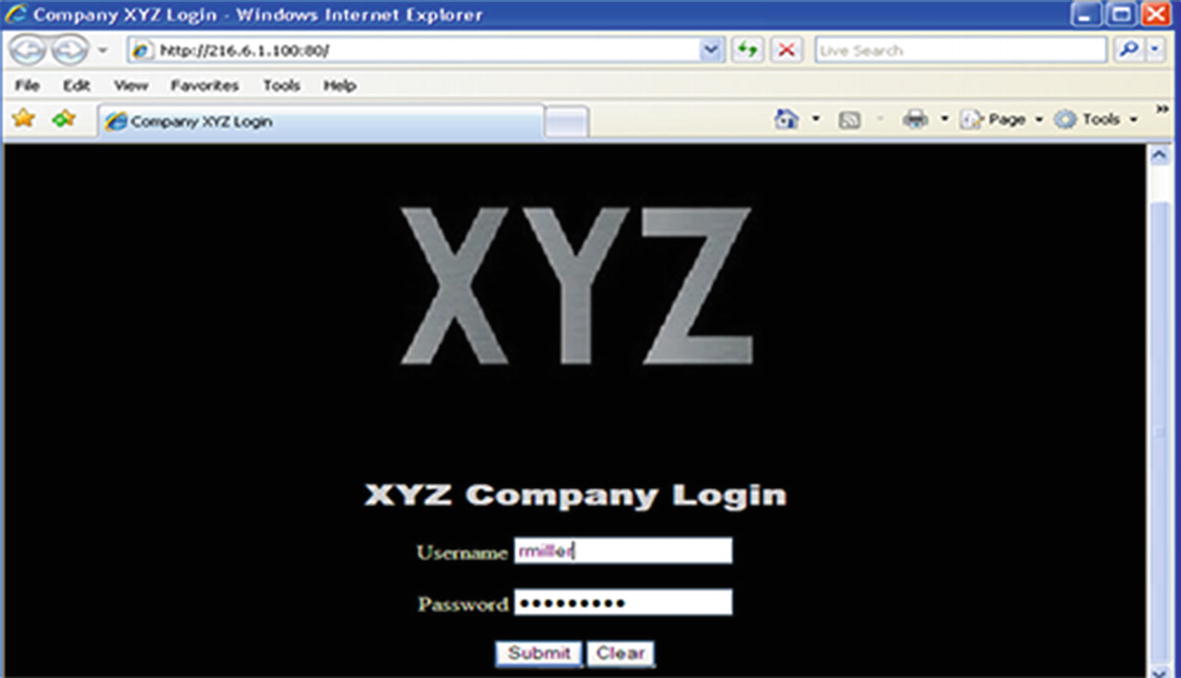
Web page login

Captured user name and password
Social Engineering
Social engineering is using one’s “gift of gab” to make another individual let their guard down, so to speak, so that they divulge information that would not normally be divulged or to take an action that would not normally be taken.
Social engineering plays upon the desire of most people to be helpful in the workplace. How many organizations do you know of that emphasize customer service? Information that is gained can sometimes be used directly in an attack, but most times it is used indirectly as part of a more elaborate scheme.
- 1.
Reciprocation: Being compelled to take action when given something, such as buying a product after receiving a free sample.
- 2.
Consistency: Behavior patterns are the same, which may occur when, for instance, you ask a question and wait as someone fills the pause.
- 3.
Social validation: Doing what everyone else is doing. An example of this is if you look up on a crowded street, others will look up as well.
- 4.
Liking: Tending to say yes to those we like or those who are attractive. Models are used in ads to generate interest.
- 5.
Authority: Heeding advice of those in a position of authority, such as ads that say 4 out of 5 doctors agree.
- 6.
Scarcity: The less of it, the more appealing it becomes, like popular toys at Christmas.
Social Engineering Cycle
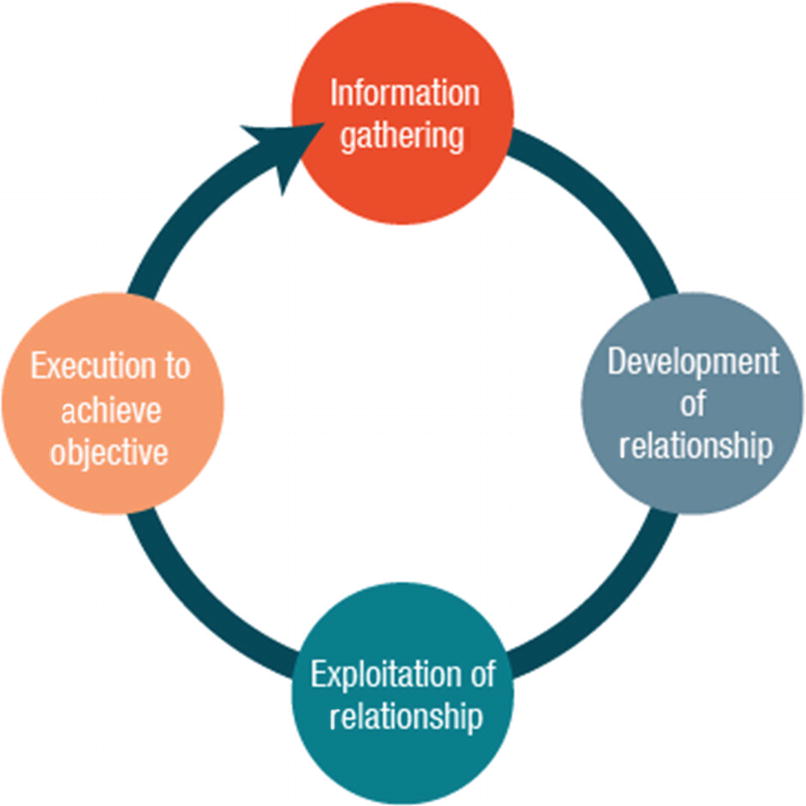
Social engineering cycle
Techniques
Human-based social engineering involves human interaction and includes actions such as impersonation, eavesdropping, shoulder surfing, dumpster diving, third-party authorization, and piggybacking (Figure 6-8). For example, an attacker may impersonate an employee and give a false identity. An attacker may even take this one step further by assuming the identity of an important employee, such as a director or a member of upper management. An attacker may also pose as a technical support person.
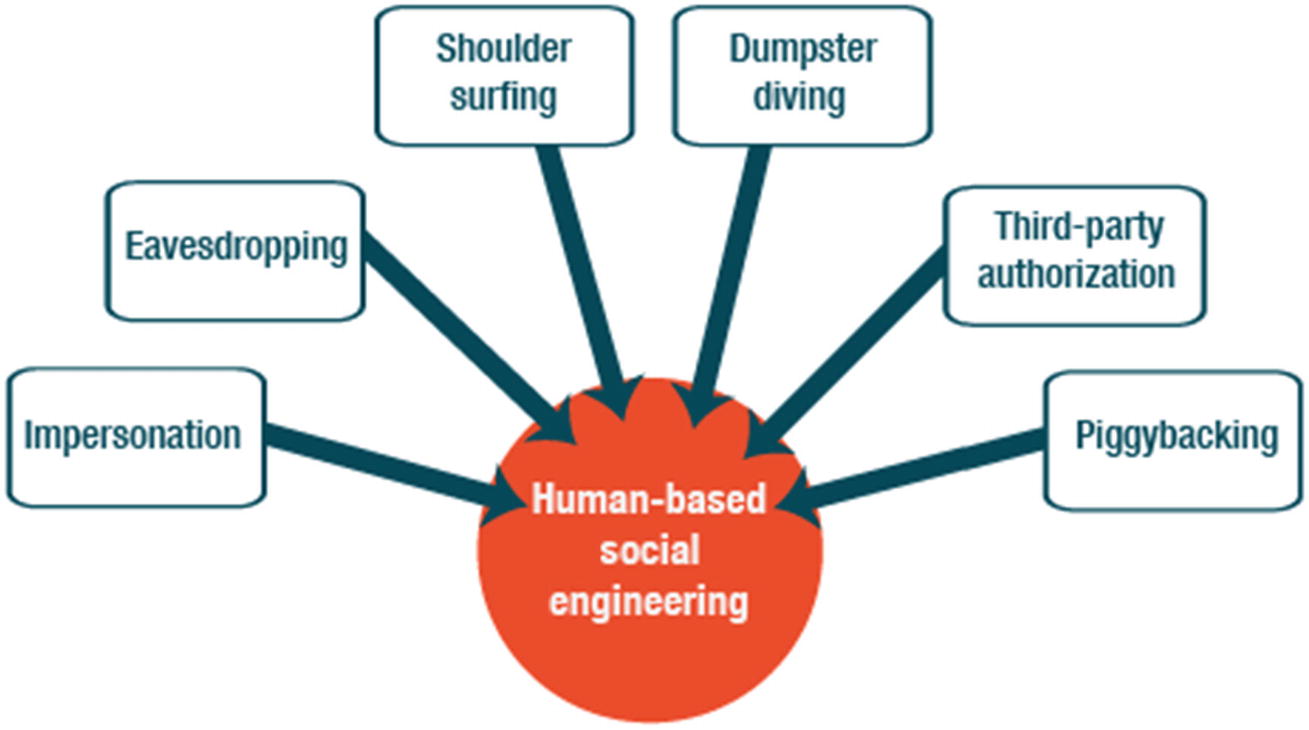
Human-based social engineering techniques
Computer-Based Social Engineering
Computer-based social engineering depends on software to carry out the targeted action. For example, a Trojan horse is malware that appears to be a normal, usable program, but there is actually a virus hidden inside. A backdoor can be used to bypass the usual authentication methods on a system.
Pop-up windows
Mail attachments
Web sites
Instant messenger
Phising
Insider attack
Shark
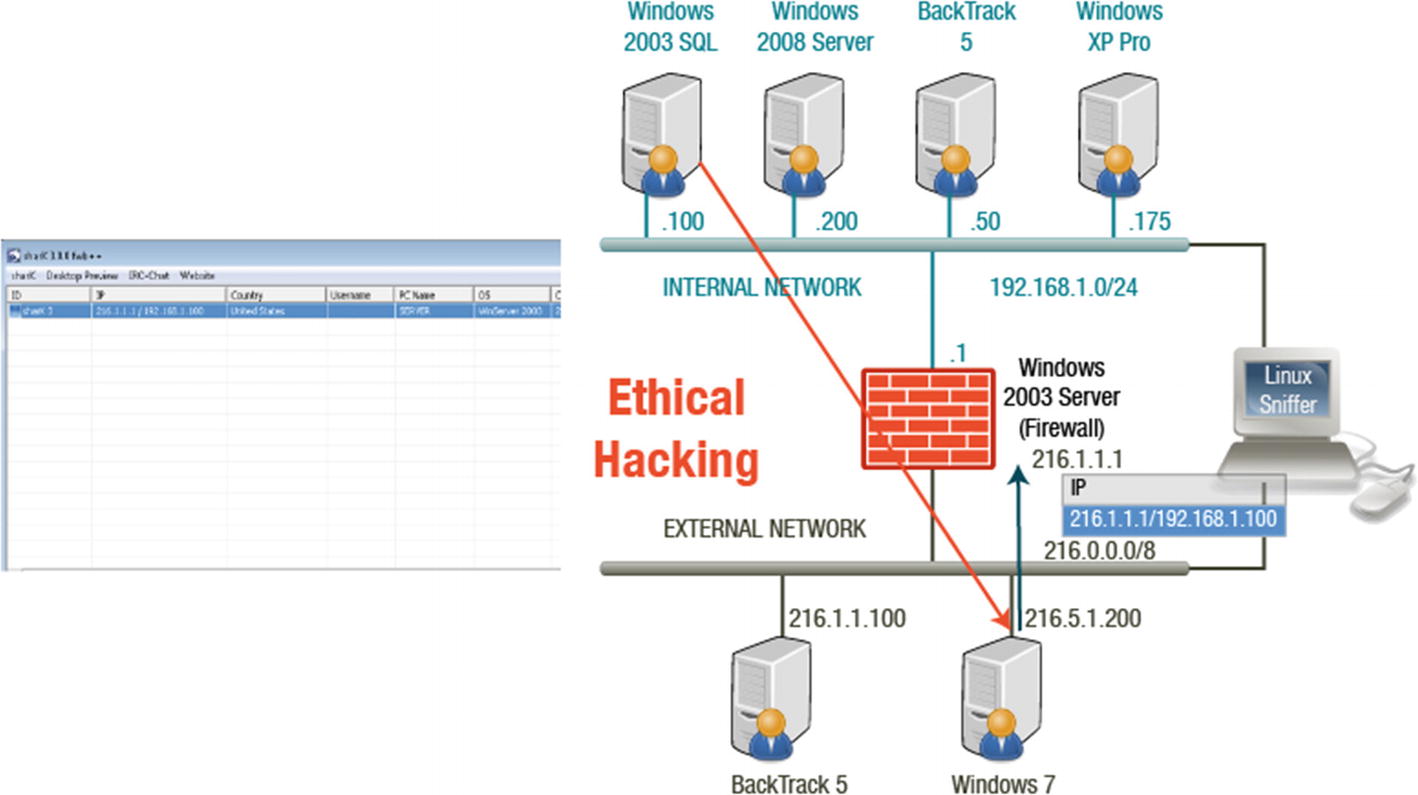
Remote shark connection
Prevention Recommendations
An organization can take several steps to prevent an insider threat. Dividing responsibilities among various employees so that no one employee has total control is called separation of duties. Similar in concept is to rotate a single duty to different employees at different times.
Access control policies must also be implemented throughout the organization to restrict unauthorized access. Logging and auditing access are preventative measures and instituting legal policies and archiving critical data will also help an organization.
General Defense Measures
- 1.
Management should develop a set of security goals and assign staff members to those goals.
- 2.
The company should perform risk management assessments.
- 3.
Implementing defenses within the company’s security policy is essential. Employees need to be made aware of how to handle social engineering threats through policies and security awareness.
Countermeasures
The specific countermeasures that an organization can implement include training, password policies, operational guidelines, physical security policies, classification of information, access privileges, background checks, incident response system, and policies and procedures. It all comes down to adequately training employees, though, about these countermeasures. Users must be able to recognize what kind of information a social engineer can use.
Summary
You explored sniffers and social engineering in this chapter. You understand how attackers use sniffing to steal passwords, emails, and files from organizations and individuals. You can also describe the two types of social engineering and the countermeasures to protect organizations and individuals from attack.