Chapter 11. Cloud Computing, Iot, And Botnets
This chapter covers the following topics:
Cloud Computing: Many organizations are moving to the cloud or deploying hybrid solutions to host their applications. Organizations moving to the cloud are almost always looking to transition from Capital expenditure (CapEx) to Operational expenditure (OpEx). Most Fortune 500 companies operate in a multicloud environment. It is obvious that cloud computing security is more important than ever. Cloud computing security includes many of the same functionalities as traditional IT security. This includes protecting critical information from theft, data exfiltration, and deletion, as well as privacy.
Internet of Things (IoT): Although not specifically designed to be hacking tools, sniffers can be used to find many types of clear-text network traffic.
Botnets: Botnets are a collection of compromised machines that the attacker can manipulate from a command and control (C2) system to participate in a DDoS, send spam emails, or perform other illicit activities.
This chapter introduces you to cloud computing, IoT, and botnets. Cloud computing is a new consumption and delivery model for IT services. The concept of cloud computing represents a shift in thought in that end users need not know the details of a specific technology. The service is fully managed by the provider. Users can consume services at a rate that is set by their particular needs. This on-demand service can be provided at any time.
The second part of this chapter covers IoT concepts, technologies, and security challenges. The third part of this chapter examines botnets. A botnet, or robot network, consists of at least one bot server and one or more botnet clients. Hackers like to use botnets because it gives them a way to carry out computing activities on a huge scale. These activities could include Distributed DoS, spam, malware, the capture of credit card numbers, financial fraud, and the like.
“Do I Know This Already?” Quiz
The “Do I Know This Already?” quiz enables you to assess whether you should read this entire chapter thoroughly or jump to the “Exam Preparation Tasks” section. If you are in doubt about your answers to these questions or your own assessment of your knowledge of the topics, read the entire chapter. Table 11-1 lists the major headings in this chapter and their corresponding “Do I Know This Already?” quiz questions. You can find the answers in Appendix A, “Answers to the ‘Do I Know This Already?’ Quizzes and Review Questions.”
Table 11-1 “Do I Know This Already?” Section-to-Question Mapping
Foundation Topics Section |
Questions |
|---|---|
Cloud Computing |
1–4 |
IoT |
5–8 |
Botnets |
9–10 |
Caution
The goal of self-assessment is to gauge your mastery of the topics in this chapter. If you do not know the answer to a question or are only partially sure of the answer, you should mark that question as wrong for purposes of the self-assessment. Giving yourself credit for an answer you correctly guess skews your self-assessment results and might provide you with a false sense of security.
1. Which of the following are advantages of using cloud-based services? (Choose all that apply.)
a. Distributed storage
b. Protection against SQL injection
c. Protection against XSS
d. Scalability and elasticity
2. Which cloud model uses all assets of the cloud provider?
a. IaaS
b. MaaS
c. SaaS
d. PaaS
3. Which of the following cloud services would include items such as Gmail, WebEx, or Google Drive?
a. SaaS
b. IaaS
c. MaaS
d. PaaS
4. For which of the following cloud models would a pen test not be recommended?
a. IaaS
b. PaaS
c. SaaS
d. None of the above
5. Which of the following is an example of a distributed intelligence architectural component of IoT implementations?
a. IaaS
b. Data collection
c. SaaS
d. None of the above
6. Which of the following is an example of IoT security challenges and considerations?
a. Numerous IoT devices are inexpensive devices with little to no security capabilities.
b. IoT devices are typically constrained in memory and compute resources and do not support complex and evolving security and encryption algorithms.
c. Several IoT devices are deployed with no backup connectivity if the primary connection is lost. In addition, numerous IoT devices require secure remote management during and after deployment (onboarding).
d. All of the above.
7. Which of the following is an example of an IoT communication protocol?
a. INSTEON
b. Zigbee
c. LoRaWAN
d. All of the above
8. Which of the following tools can be used to perform IoT security assessments?
a. HackRF
b. Binary Ninja
c. Ubertooth One
d. All of the above
9. Which of the following is not a botnet propagation technique?
a. Central source propagation
b. Back-chaining
c. Autonomous
d. Block-chaining
10. Which technique is focused on tracking packets back to the entry points to the domain?
a. Traceback
b. Intercept
c. TTL analysis
d. Focused
Foundation Topics
Cloud Computing
The National Institute of Standards and Technology (NIST) authored the Special Publication (SP) 800-145, “The NIST Definition of Cloud Computing” to provide a standard set of definitions for the different aspects of cloud computing. The SP 800-145 document also compares the different cloud services and deployment strategies.
The advantages of using a cloud-based service include the following:
Distributed storage
Scalability
Resource pooling
Access from any location
Measured service
Automated management
According to NIST, the essential characteristics of cloud computing include the following:
On-demand self-service
Broad network access
Resource pooling
Rapid elasticity
Measured service
Cloud deployment models include the following:
Public cloud: Open for public use
Private cloud: Used just by the client organization on-premise (on-prem) or at a dedicated area in a cloud provider
Community cloud: Shared between several organizations
Hybrid cloud: Composed of two or more clouds (including on-prem services).
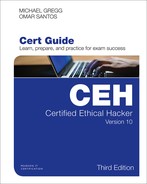
Cloud computing can be broken into the following three basic models, a comparison of which is shown in Figure 11-1:
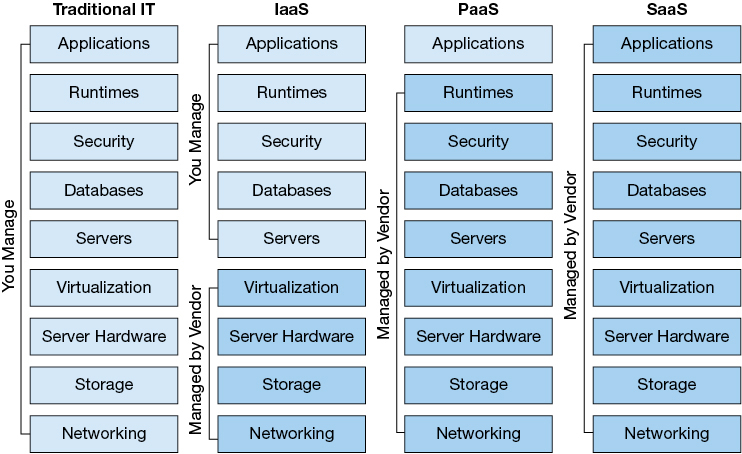
Figure 11-1 Cloud Computing

Infrastructure as a Service (IaaS): IaaS describes a cloud solution where you are renting infrastructure. You purchase virtual power to execute your software as needed. This is much like running a virtual server on your own equipment except you are now running a virtual server on a virtual disk. This model is similar to a utility company model because you pay for what you use.
Platform as a Service (PaaS): PaaS provides everything except applications. Services provided by this model include all phases of the system development life cycle (SDLC) and can use application programming interfaces (API), website portals, or gateway software. These solutions tend to be proprietary, which can cause problems if the customer moves away from the provider’s platform.
Software as a Service (SaaS): SaaS is designed to provide a complete packaged solution. The software is rented out to the user. The service is usually provided through some type of front end or web portal. While the end user is free to use the service from anywhere, the company pays a per-use fee.
Note
NIST Special Publication 500-292, “NIST Cloud Computing Reference Architecture,” is another resource to learn more about cloud architecture.
Cloud Computing Issues and Concerns
There are many potential threats when organizations move to a cloud model. For example, although your data is in the cloud, it must reside in a physical location somewhere. Your cloud provider should agree in writing to provide the level of security required for your customers. The following are questions to ask a cloud provider before signing a contract for its services:

Who has access? Access control is a key concern because insider attacks are a huge risk. Anyone who has been approved to access the cloud is a potential hacker, so you want to know who has access and how they were screened. Even if it was not done with malice, an employee can leave, and then you find out that you don’t have the password, or the cloud service gets canceled because maybe the bill didn’t get paid.
What are your regulatory requirements? Organizations operating in the United States, Canada, or the European Union have many regulatory requirements that they must abide by (for example, ISO/IEC 27002, EU-U.S. Privacy Shield Framework, ITIL, and COBIT). You must ensure that your cloud provider can meet these requirements and is willing to undergo certification, accreditation, and review.
Do you have the right to audit? This particular item is no small matter in that the cloud provider should agree in writing to the terms of the audit. With cloud computing, maintaining compliance could become more difficult to achieve and even harder to demonstrate to auditors and assessors. Of the many regulations touching upon information technology, few were written with cloud computing in mind. Auditors and assessors may not be familiar with cloud computing generally or with a given cloud service in particular.
Note
Division of compliance responsibilities between cloud provider and cloud customer must be determined before any contracts are signed or service is started.
What type of training does the provider offer its employees? This is a rather important item to consider because people will always be the weakest link in security. Knowing how your provider trains its employees is an important item to review.
What type of data classification system does the provider use? Questions you should be concerned with here include what data classified standard is being used and whether the provider even uses data classification.
How is your data separated from other users’ data? Is the data on a shared server or a dedicated system? A dedicated server means that your information is the only thing on the server. With a shared server, the amount of disk space, processing power, bandwidth, and so on, is limited because others are sharing this device. If it is shared, the data could potentially become comingled in some way.
Is encryption being used? Encryption should be discussed. Is it being used while the data is at rest and in transit? You will also want to know what type of encryption is being used. For example, there are big technical differences between DES and AES. However, for both of these algorithms, the basic questions are the same: Who maintains control of the encryption keys? Is the data encrypted at rest in the cloud? Is the data encrypted in transit, or is it encrypted at rest and in transit?
What are the service level agreement (SLA) terms? The SLA serves as a contracted level of guaranteed service between the cloud provider and the customer that specifies what level of services will be provided.
What is the long-term viability of the provider? How long has the cloud provider been in business, and what is its track record? If it goes out of business, what happens to your data? Will your data be returned, and if so, in what format?
Will they assume liability in the case of a breach? If a security incident occurs, what support will you receive from the cloud provider? While many providers promote their services as being unhackable, cloud-based services are an attractive target to hackers.
What is the disaster recovery/business continuity plan (DR/BCP)? Although you may not know the physical location of your services, it is physically located somewhere. All physical locations face threats such as fire, storms, natural disasters, and loss of power. In case of any of these events, how will the cloud provider respond, and what guarantee of continued services is it promising?
Even when you end a contract, you must ask what happens to the information after your contract with the cloud service provider ends.
Note
Insufficient due diligence is one of the biggest issues when moving to the cloud. Security professionals must verify that issues such as encryption, compliance, incident response, and so forth are all worked out before a contract is signed.
Cloud Computing Attacks
Because cloud-based services are accessible via the Internet, they are open to any number of attacks. As more companies move to cloud computing, look for hackers to follow. Some of the potential attack vectors criminals may attempt include the following:

Session hijacking: This attack occurs when the attacker can sniff traffic and intercept traffic to take over a legitimate connection to a cloud service.
DNS attack: This form of attack tricks users into visiting a phishing site and giving up valid credentials.
Cross-site scripting (XSS): Used to steal cookies that can be exploited to gain access as an authenticated user to a cloud-based service.
SQL injection: This attack exploits vulnerable cloud-based applications that allow attackers to pass SQL commands to a database for execution.
Session riding: EC Council uses this term to describe a Cross-Site Request Forgery attack. Attackers use this technique to transmit unauthorized commands by riding an active session by using an email or malicious link to trick users while they are currently logged in to a cloud service.
Distributed Denial of Service (DDoS) attack: Some security professionals have argued that the cloud is more vulnerable to DDoS attacks because it is shared by many users and organizations, which also makes any DDoS attack much more damaging.
Man-in-the-middle cryptographic attack: This attack is carried out when the attacker places himself in the communications path between two users. Anytime the attacker can do this, there is the possibility that he can intercept and modify communications.
Side-channel attack: An attacker could attempt to compromise the cloud by placing a malicious virtual machine in close proximity to a target cloud server and then launching a side-channel attack.
Authentication attack: Authentication is a weak point in hosted and virtual services and is frequently targeted. There are many ways to authenticate users, such as based on what a person knows, has, or is. The mechanisms used to secure the authentication process and the method of authentication used are frequent targets of attackers.
Wrapping attack: This attack occurs when the attacker duplicates the body of a SOAP message and sends it to the cloud server as a legitimate user.
Note
Social engineering is another potential threat to cloud computing. Social engineering targets people, not hardware or software.
Cloud Computing Security
Regardless of the model used, cloud security is the responsibility of both the client and the cloud provider. These details will need to be worked out before a cloud computing contract is signed. The contracts will vary depending on the given security requirements of the client. Considerations include disaster recovery, SLAs, data integrity, and encryption. For example, is encryption provided end to end or just at the cloud provider? Also, who manages the encryption keys: the cloud provider or the client? Overall, you want to ensure that the cloud provider has the same layers of security (logical, physical, and administrative) in place that you would have for services you control. Table 11-2 provides some examples of cloud security control layers.
Table 11-2 Cloud Security Control Layers
Layer |
Details |
|---|---|
Application |
Web application firewalls, SDLC, vulnerability scanners |
Information |
Database activity monitor, encryption |
Management |
Configuration management, monitoring |
Network |
HIDS, NIDS, anti-DDoS, DNSSEC |
Computer and storage |
Firewalls, IDS, log management, syslog |
Physical |
Locks, guards, alarm systems |
IoT

The Internet of Things (IoT) includes any computing devices (mechanical and digital machines) that can transfer data over a network without requiring human-to-human or human-to-computer interaction—for example, sensors, home appliances, connected security cameras, wearables, and numerous other devices.
The capability of distributed intelligence in the network is a core architectural component of the IoT:
Data Collection: Centralized data collection presents a few challenges for an IoT environment to be able to scale. For instance, managing millions of sensors in a Smart Grid network cannot efficiently be done using a centralized approach.
Network Resource Preservation: This is particularly important because network bandwidth may be limited, and centralized IoT device data collection leads to using a large amount of the network capabilities.
Closed Loop Functioning: IoT environments often require reduced reaction times.
Fog Computing is a concept of a distributed intelligence architecture designed to process data and events from IoT devices as close to the source as possible. The Fog edge device then sends the required data to the cloud. For example, a router may collect information from numerous sensors and then communicate to a cloud service or application for the processing of such data.
The following are some of the IoT security challenges and considerations:
Numerous IoT devices are inexpensive devices with little to no security capabilities.
IoT devices are typically constrained in memory and compute resources and do not support complex and evolving security and encryption algorithms.
Several IoT devices are deployed with no backup connectivity if the primary connection is lost.
Numerous IoT devices require secure remote management during and after deployment (onboarding).
IoT devices often require the management of multiparty networks. Governance of these networks is often a challenging task. For example, who will accept liability for a breach? Who is in charge of incident response? Who has provisioning access? Who has access to the data?
Crypto resilience is a challenge in many IoT environments. These embedded devices (such as smart meters) are designed to last decades without being replaced.
Physical protection is also another challenge, because any IoT device could be stolen, moved, or tampered with.
The IoT device must authenticate to multiple networks securely.
An organization must ensure that data is available to multiple collectors at all times.
IoT technologies like INSTEON, Zigbee, Z-Wave, LoRaWAN, and others were not designed with security in mind (however, they have improved significantly over the past few years).
IoT devices typically communicate to the cloud via a Fog Edge device or directly to the cloud. Figure 11-2 shows several sensors are communicating to a Fog Edge router, and subsequently the router communicates to the cloud.
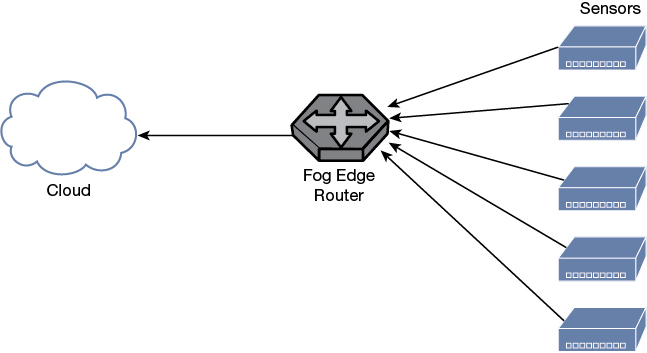
Figure 11-2 Fog Computing Device Example
Figure 11-3 shows how a smart thermostat communicates directly to the cloud using a RESTful application programming interface (API) via a Transport Layer Security (TLS) connection. The IoT device (a smart thermostat in this example) sends data to the cloud, and an end user checks the temperature and manages the thermostat using a mobile application.
Figure 11-3 IoT, Cloud Applications, and APIs
In the example illustrated in Figure 11-3, securing the thermostat, the RESTful API, the cloud application, and the mobile application is easier said than done.
IoT Protocols
The following are some of the most popular IoT protocols:

Zigbee: One of the most popular protocols supported by many consumer IoT devices. Zigbee takes advantage of the underlying security services provided by the IEEE 802.15.4 MAC layer. The 802.15.4 MAC layer supports the AES algorithm with a 128-bit key for both encryption and decryption. Additional information about Zigbee can be obtained from the Zigbee Alliance at https://www.zigbee.org.
Bluetooth Low Energy (BLE) and Bluetooth Smart: BLE is an evolution of the Bluetooth protocol that is designed for enhanced battery life for IoT devices. Bluetooth Smart enabled devices default to “sleep mode” and “wake up” only when needed. Both operate in the 2.4 GHz frequency range. Bluetooth Smart implements high-rate frequency-hopping spread spectrum and supports AES encryption. Additional information about BLE and Bluetooth Smart can be found at https://www.bluetooth.com.
Z-Wave: Another popular IoT communication protocol. It supports unicast, multicast, and broadcast communication. Z-Wave networks consist of controllers and slaves. Some Z-Wave devices can be both primary and secondary controllers. Primary controllers are allowed to add and remove nodes from the network. Z-Wave devices operate at a frequency of 908.42 MHz (North America) and 868.42 MHz (Europe) with data rates of 100 kb/s over a range of about 30 meters. Additional information about Z-Wave can be obtained from the Z-Wave Alliance at https://z-wavealliance.org.
INSTEON: A protocol that allows IoT devices to communicate wirelessly and over the power lines. It provides support for dual-band, mesh, and peer-to-peer communication. Additional information about INSTEON can be found at https://www.insteon.com/technology/.
Long Range Wide Area Network (LoRaWAN): A networking protocol designed specifically for IoT implementations. LoRaWAN has three classes of endpoint devices: Class A (lowest power, bidirectional end-devices), Class B (bidirectional end-devices with deterministic downlink latency), and Class C (lowest latency, bidirectional end-devices). Additional information about LoRaWAN can be found at the LoRa Alliance at https://lora-alliance.org.
Wi-Fi: Still one of the most popular communication methods for IoT devices.
Low Rate Wireless Personal Area Networks (LRWPAN) and IPv6 over Low Power Wireless Personal Area Networks (6LoWPAN): IPv4 and IPv6 both play a role at various points within many IoT systems. IPv6 over Low Power Wireless Personal Area Networks (6LoWPAN) supports the use of IPv6 in the network-constrained IoT implementations. 6LoWPan was designed to support wireless Internet connectivity at lower data rates. 6LoWPAN builds upon the 802.15.4 Low Rate Wireless Personal Area Networks (LRWPAN) specification to create an adaptation layer that supports the use of IPv6.
Cellular Communication: Also a popular communication method for IoT devices, including connected cars, retail machines, sensors, and others. 4G and 5G are used to connect many IoT devices nowadays.
IoT devices often communicate to applications using REST and MQTT on top of lower-layer communication protocols. These messaging protocols provide the ability for both IoT clients and application servers to efficiently agree on data to exchange. The following are some of the most popular IoT messaging protocols:
MQTT
Constrained Application Protocol (CoAP), the Data Distribution Protocol (DDP)
Advanced Message Queuing Protocol (AMQP)
Extensible Messaging and Presence Protocol (XMPP)
Hacking IoT Implementations
Many of the tools and methodologies for hacking applications and network apply to IoT hacking. However, several specialized tools perform IoT hardware and software hacking.

The following are a few examples of tools and methods to hack IoT devices.
Hardware tools:
Multimeters
Oscilloscopes
Soldering tools
UART debuggers and tools
Universal interface tools like JTAG, SWD, I2C, and SPI tools
Logic analyzers
Reverse engineering tools, such as disassemblers and debuggers:
IDA
Binary Ninja
Radare2
Hopper
Wireless communication interfaces and tools:
Ubertooth One (for Bluetooth hacking)
Software-defined radio (SDR) like HackRF and BladeRF to perform assessments of Z-Wave and Zigbee implementations.
Botnets

“All things must change to something new.” Ever hear that famous quotation? You might not have thought that the quote pertained to DDoS, but that too has changed. Today’s current threat in the DDoS arena is botnets. A botnet is a collection of zombie computers, or bots, that is controlled by a hacker, or bot herder. What most botnets have in common is that they are designed to make money. So, these botnets may be used to send spam, install Trojans, attempt pump-and-dump stock manipulation, attempt extortion, or even launch DDoS attacks. What is important to note is how big botnets can get and how many computer users are unknowingly participating in this activity. Botnet developers are becoming more sophisticated and developing better obfuscation techniques so that end users won’t discover that their computers have become bots. An end user’s computer can become infected by visiting a malicious site, clicking the wrong email attachment, or following a link in a social networking site. Even legitimate websites can lead to infection. After the end user’s computer is infected, the bot herder can use it for any number of illegal activities.
Botnets get started when the bot herder starts the propagation process and spreads the malware to unprotected computers. After those systems are infected as bots, they may scan and infect other unprotected computers, thereby adding more zombie computers to the botnet. The bot herder usually communicates with the infected systems via Internet Relay Chat (IRC). IRC servers may not always be the best choice for bot communication, but IRC is freely available and simple to set up. Some bots are controlled via private peer-to-peer (P2P) networks. A P2P network is a network in which any node in the network can act as both a client and a server. Botnets make use of web-based communication, command, and fast flux. Fast flux is used because individual botnet nodes can be shut down. Fast-flux botnets work by hiding behind an ever-changing network of compromised hosts that act as proxies. This allows IP addresses to be swapped out quickly and makes it much harder for law enforcement to shut down the botnet. An example of this is shown in Figure 11-4.
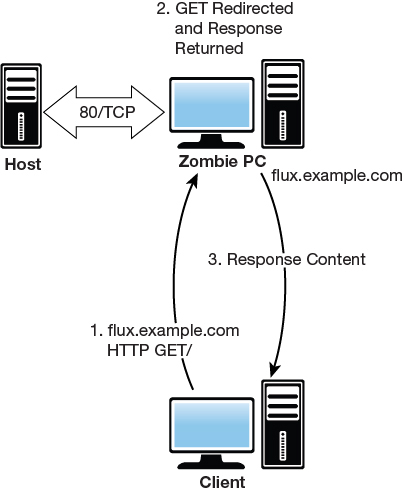
Figure 11-4 Fast-Flux Botnet
Well-known botnets include the following:

Zeus
Citadel
Storm
Mariposa
Rustock
Mirai
Silentbanker
Many of these botnets are financially driven. One example of this is the Metamorfo Banking Trojan. After infection, the malware waits until the computer is used for a banking transaction. Financially motivated cybercriminals have used banking Trojans for years to steal sensitive financial information from victims. They are often created to gather credit card information and login credentials for various online banking and financial services websites so this data can be monetized by the attackers. Common ones include the following:
TAN grabber: The bot intercepts the transaction authentication number and replaces it with an invalid number to be used by the client. The attacker uses the valid number to perform banking transactions.
HTML injection: Creates fake form fields to be displayed to the end user.
Form grabber: Captures and modifies the POST requests and alters information.
Some botnets are sold as crimeware kits. Citadel is an example of this type of botnet, as shown in Figure 11-5. Its price ranges from several thousand dollars or more, depending on the package and amount of options you require. Crimeware kits can offer a variety of services, such as a hosting provider to house your botnet server. These hosting companies are usually located in distant parts of the world. Unlike most hosting companies, they provide their customer considerable leniency in the kinds of material they may upload and distribute. These bulletproof hosting companies turn a blind eye to customers hosting malware or operating fraud-based services.
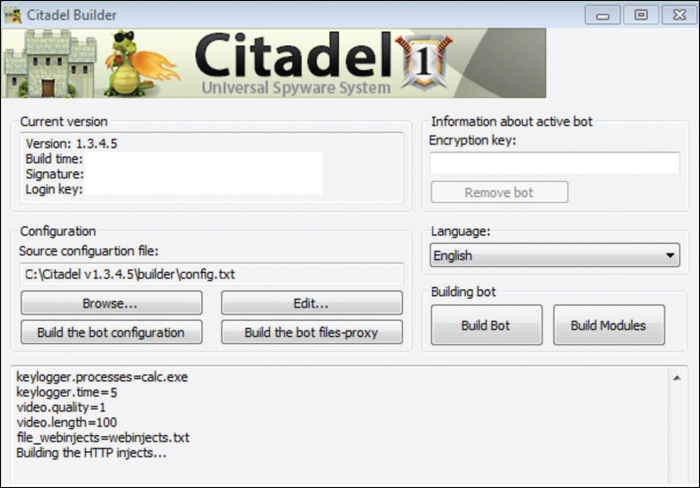
Figure 11-5 Citadel
Next comes the installation process. It’s an automated process that steps you through the configuration in much the same way as any modern OS or application. If you run into trouble, you can always consult the manual. If that does not help, you can even submit a trouble ticket. For a fee, you can get additional support. With the bot up and running, you can now use it for any number of money-making activities, such as running keyloggers to obtain banking credentials, stealing credit card numbers, capturing logins and passwords to email accounts, and even sending spam.
Most financial-based botnet attacks make use of a money mule. A money mule is nothing more than a person who transfers stolen money or merchandise from one country to another or from one person to another. Most plead ignorance when caught and claim they did not know they were doing anything wrong.
Note
Crimeware is a class of botnet or other malware designed specifically to automate cybercrime.
Botnet Countermeasures

Malicious users can launch many types of attacks. According to www.computerworlduk.com, from July to October 2015, sites that were monitored generated roughly half of all traffic by bots. These included good bots, such as search engine spiders (19.5 percent), and bad ones, such as spam and DDoS traffic (29 percent). Only about half of overall traffic was initiated by a person clicking a mouse. This should make clear the need for security professionals to deal with this threat. A large portion of this threat is DDoS. As more emphasis is placed on e-commerce, more businesses rely on network connectivity, and supervisory control and data acquisition (SCADA) systems depend on constant connectivity. DDoS will continue to be a real threat. It’s not possible to completely prevent the threat of DDoS from botnets and other sources, but you can take steps to reduce the threat and the possibility that your network will be used to attack others.
One of the first things you can do is be proactive. If something does not look right, investigate. By using a combination of techniques and building a defense in depth, a more secure network can be built. Intrusion detection systems (IDS) can help play a part in defending against attacks. Although they might not prevent the attack, they can help you detect it early on, block suspect traffic, and remove bots from infected systems. Often, these computers are infected without their owners’ knowledge. If an end client is suspected to be infected, Ngrep can be used to search for string patterns in the application layer payloads and is useful in looking at IRC traffic. Wireshark can be used to analyze real-time traffic. In some cases, it might not even be computers that are infected: IoT devices were targeted by the Mirai botnet. Expect IoT to be a larger area of concern in the coming years as hackers find more and new vulnerable IoT devices, or ways to infect those vulnerable devices hidden behind the corporate firewall or home router.
You also want to block bogus and unwanted addresses. Some of the source addresses you want to filter out include those shown in Table 11-3.
Table 11-3 Egress Filtering
Network |
Details |
|---|---|
0.0.0.0/8 |
Historical broadcast |
10.0.0.0/8 |
RFC 1918 private network |
127.0.0.0/8 |
Loopback |
169.254.0.0/16 |
Link-local networks |
172.16.0.0/12 |
RFC 1918 private network |
192.0.2.0/24 |
TEST-NET |
192.168.0.0/16 |
RFC 1918 private network |
224.0.0.0/4 |
Class D multicast |
240.0.0.0/5 |
Class E reserved |
248.0.0.0/5 |
Unallocated |
255.255.255.255/32 |
Broadcast |
The next approach is traceback. This technique is focused on tracing packets back to the entry points to the domain. You will first need to determine if the traffic is spoofed or coming from a legitimate IP address. You can use several techniques to help determine whether the traffic is coming from a legitimate source, including the following:
IPID analysis: The IPID value found in the IPv4 header increments in a known manner. If these numbers differ vastly between incoming traffic and what is believed to be the real source, the traffic might be spoofed.
TTL inspection: This can be checked by sending a packet to the claimed host and examining the reply. If the TTL in the reply is not the same as in the packet being checked, the traffic is spoofed.
TCP window size: If the attacker is sending spoofed packets, the sending computer will not receive the victim’s ACK packet and cannot properly respond when the TCP receive window is exhausted.
Note
A SYN flood attack is a type of resource exhaustion attack. SYN cookies can be used to mitigate SYN flood attacks. The idea is to use SYN cookies to allow a server to avoid dropping connections when the SYN queue is full.
When you have some idea as to whether the traffic is coming from a legitimate source or is spoofed, and you know the entry point, the upstream Internet service provider (ISP) can configure its routers to reject all packets flooding the DDoS target; this results in Internet Control Message Protocol (ICMP) type 3 destination unreachable messages being returned to the upstream source. The ISP can then identify the next specified router interfaces through which the attack is entering. This process repeats itself as the defender continues to work back toward the attacker, tracing the attack back to the original source.
Mitigation is another approach. I consider this technique a more proactive defense. Mitigation makes use of a traffic-cleaning center that operates at peering points on the Internet. The traffic-cleaning nodes operate as scrubbers and redirect only clean valid traffic to the company’s web servers. Symantec, Verisign, and others offer these services. Tools such as Tripwire can be used for file integrity checks.
The most important defense is to be proactive. This means that you need to have a plan in place with the ISP; it can help stop traffic upstream. Black hole filtering and DDoS prevention services from ISPs are available for a fee. If you use these services, make sure your ISP gives you contact information so that you know whom to contact if you are attacked.
Note
If you are using Cisco gear, you can use TCP intercept capability for intercepting and validating a TCP connection, thereby reducing some types of DDoS.
Summary
In this chapter, you learned about cloud computing. The use of cloud computing services is increasing and will continue to do so. Because of the concerns of regulatory issues with the cloud, many companies are initially moving only data-intensive, low-security services to the cloud. The long-term issue remains how the security and protection of sensitive data will be protected and what types of controls the industry will adopt.
Botnets are used for many types of money-making activities, such as pump-and-dump stock manipulation, spam, fake pharmaceuticals, fake goods, illegal software, bootleg music, and even extortion. The motive might even be just for kicks. When botnets are used for DDoS attacks, they prevent availability and users from gaining the access they require.
Exam Preparation Tasks
As mentioned in the section, “How to Use This Book” in the Introduction, you have several choices for exam preparation: the exercises here, Chapter 12, “Final Preparation,” and the exam simulation questions in the Pearson Test Prep Software Online.
Review All Key Topics
Review the most important topics in this chapter, noted with the Key Topic icon in the outer margin of the page. Table 11-4 lists a reference of these key topics and the page numbers on which each is found.

Table 11-4 Key Topics for Chapter 11
Key Topic Element |
Description |
Page Number |
|---|---|---|
List |
Understand the different cloud computing models |
551 |
List |
Questions to ask a cloud service provider prior to signing a contract |
552 |
List |
Describes common cloud computing attacks |
554 |
Section |
Describes IoT and IoT security |
556 |
List |
IoT technologies and protocols |
558 |
List |
Tools and methods to hack IoT devices |
560 |
Section |
Botnets |
560 |
List |
Identifies well-known botnets |
562 |
Section |
Botnet countermeasures |
563 |
Define Key Terms
Define the following key terms from this chapter and check your answers in the glossary:
distributed denial of service (DDoS)
Exercise
11.1 Scanning for DDoS Programs
In this exercise, you scan for DDoS tools.
Estimated Time: 15 minutes.
Step 1. Download the DDoS detection tool DDoSPing. It is available from http://www.mcafee.com/us/downloads/free-tools/ddosping.aspx.
Step 2. Unzip the program into its default directory.
Step 3. Use Windows Explorer to go to the DDOSPing folder and launch the executable.
Step 4. Set the transmission speed to MAX by moving the slider bar all the way to the right.
Step 5. Under the target range, enter your local subnet.
Step 6. Click Start.
Step 7. Examine the result to verify that no infected hosts were found.
Review Questions
1. Which of the following cloud models places the cloud service provider in complete control of the company’s computing resources?
a. MaaS
b. SaaS
c. PaaS
d. IaaS
2. Which of the following is not used for traceback?
a. IPID analysis
b. TTL inspection
c. IP header size
d. TCP window size
3. Which attack steals cookies that are used to authenticate users?
a. SYN cookies
b. CSRF
c. XSS
d. Wrapping
4. You believe one of your host systems has become infected. Which of the following tools can you use to look for malicious traffic in real time?
a. NetworkMiner
b. Netstat
c. Tripwire
d. Wireshark
5. Which type of attack is carried out by compromising a co-resident user in the cloud?
a. SOAP attack
b. Wrapping attack
c. Side channel
d. Passive sniffing
6. Which of the following can be used for file integrity checking after infection with a botnet?
a. Wireshark
b. Tripwire
c. IPTables
d. TCP wrappers
7. Which form of paid botnet is preconfigured for the attackers so that they have everything they need to launch a variety of attacks?
a. Crimeware
b. Distributed botnet
c. Logic bomb
d. None of the above
8. Which of the following can be used to search for string patterns in application layer payloads?
a. Ngrep
b. Type
c. NSlookup
d. Grep
9. Which type of botnet adds fields to existing web pages?
a. TAN grabber
b. TAN injection
c. Form grabber
d. HTML injection
10. Which type of botnet is used for banking attacks to overwrite the authentication number with an invalid one?
a. TAN grabber
b. Fast flux
c. Form grabber
d. HTML injection
11. Which of the following tools can be used to perform IoT hardware security research?
a. Hopper
b. IDA
c. JTAG analyzer
d. Binary Ninja
12. ______ enabled devices default to “sleep mode” and “wake up” only when needed?
a. Bluetooth Smart
b. Zigbee
c. INSTEON
d. Z-Wave
Suggested Reading and Resources
https://www.rackspace.com/cloud/cloud-computing: What is cloud computing
http://www.infoworld.com/article/3041078/security/the-dirty-dozen-12-cloud-security-threats.html: Cloud computing threats
https://cloudsecurityalliance.org/research/: Cloud Security Alliance Research and Working Groups
http://www.infoworld.com/article/2887258/cloud-security/for-cloud-security-not-hackers-you-should-fear.html: Cloud hacking
https://www.zigbee.org: Zigbee Alliance
https://www.bluetooth.com: The Bluetooth Special Interest Group (SIG)
https://z-wavealliance.org: Z-Wave Alliance
https://www.insteon.com/technology: INSTEON Technology Specification
https://lora-alliance.org: LoRa Alliance
http://www.businessnewsdaily.com/5215-dangers-cloud-computing.html: Eight reasons to fear the cloud
http://www.trendmicro.com/us/security-intelligence/current-threat-activity/global-botnet-map/: Botnet trends
http://arstechnica.com/information-technology/2016/10/inside-the-machine-uprising-how-cameras-dvrs-took-down-parts-of-the-internet/: Rent a botnet
http://static.usenix.org/event/hotbots07/tech/full_papers/grizzard/grizzard_html/: Peer-to-peer botnets
http://www.computerworlduk.com/security/botnet-trafffic-in-2015-invisible-force-that-wants-eat-internet-3632097/: Botnet Traffic in 2015
https://krebsonsecurity.com/tag/mirai-botnet/: Mirai botnet