Chapter 17. Industry Trends and Their Impact to the Enterprise
This chapter covers the following topics:
Perform Ongoing Research: This section covers best practices, new technologies, security systems and services, and technology evolution (for example, RFCs, ISO).
Threat Intelligence: This section describes the latest attacks, current vulnerabilities and threats, zero-day mitigation controls and remediation techniques, and threat models.
Research Security Implications of Emerging Business Tools: This section covers evolving social media platforms, integration within the business, the impact of big data, and AI/machine learning.
Global IA Industry/Community: Topics include Computer Emergency Response Team (CERT), conventions/conferences, research consultants/vendors, threat actor activities, and emerging threat sources.
This chapter covers CAS-003 objective 5.1.
While ensuring enterprise security, security professionals often find it hard to keep up with the latest trends. Technology usually moves along at such a fast pace that even the best-trained professionals find that they need to seek education to understand the newest trends. At different points in the past 40 years or so, security professionals have emphasized different areas of security: from physical security when mainframes were in use to dial-up modem security when personal computers first accessed remotely. In more recent years, security professionals have had to learn the ins and outs of managing larger networks as well as wireless networks. Today, with cloud computing and bring your own device (BYOD), you can easily see why it is important to stay abreast of—or preferably in front of—the latest industry trends to better protect your organization and its enterprise.
A security professional can very easily fall behind in this fast-paced world. Failing to keep up with trends may be detrimental to both your organization and your career. This chapter covers performing ongoing research, threat intelligence, researching security implications of new business tools, and sharing with and learning from the global information assurance (IA) industry and community.
Perform Ongoing Research
For a security professional, sometimes just keeping up with the day-to-day workload can be exhausting. But performing ongoing research as part of your regular duties is more important in today’s world than ever before. You should work with your organization and direct supervisor to ensure that you either obtain formal security training on a regular basis or are given adequate time to maintain and increase your security knowledge. You should research the current best security practices, any new technologies that are coming, any new security systems and services that have launched, and how technology has evolved recently.
Best Practices
Every organization should have a set of best practices that are based on the industry in which it is engaged. It is the responsibility of security professionals to ensure that the organization takes into consideration IT security best practices. Security professionals should research all established best practices to determine which practices should be implemented for their organizations. Organizations including the Computer Security Resource Center (CSRC) of the National Institute of Standards and Technology (NIST), the International Organization for Standardization/International Electrotechnical Commission (ISO/IEC), and the Institute of Electrical and Electronics Engineers (IEEE) provide publications on standards and best practices that can be used to guide your organization in its security program development.
Any organization that can provide documentation of its security policies is better protected against any litigation that could be brought against the organization, particularly if those policies are developed based on the standards and best practices recommended by national and international bodies of authority. The standards and best practices can vary based on the organization you consult. Your organization can choose to follow the standards and best practices of a single body or can combine the standards and best practices of several bodies to customize the organization’s internal policies.
As part of designing its security program, an organization should consider developing an overall organizational security policy. In addition, the organization should ensure that the appropriate security professionals are retained and that these professionals obtain the appropriate training. The security professionals should work to develop all the user, network, computer, device, and data policies that are needed.
Best practices vary based on the devices and operating systems to be protected. For example, security practices for protecting Windows computers vary slightly from those for protecting Linux or Mac computers. Security practices for protecting switches and routers are vastly different from those for protecting servers.
No matter which devices you are protecting, there are certain procedures you should always keep in mind:

Disable or rename the default accounts, including any administrator or guest accounts.
Change the default passwords for any default accounts.
Regularly update the software or firmware for all devices with the latest patches and hot fixes.
Implement firewalls when necessary, both at the network and device levels.
Disable remote login ability unless absolutely necessary. If it is necessary, ensure that you have changed default settings, including accounts and passwords.
Implement encryption to protect data.
Configure auditing.
Review audit and security logs on a regular basis.
Disable all unnecessary services and protocols.
While all these procedures are important, security professionals should ensure that they adopt new policies and procedures as technologies and attack methods change. Researching the latest security issues and threats will help ensure that your organization is protected in a timely manner. When deploying new technologies, devices, operating systems, and applications, security professionals should research any best practices to ensure that their organization is protected.
New Technologies, Security Systems and Services
It seems that new technologies, including devices, software, and applications, are being released at lightning speed. As technologies change, security professionals must ensure that the protections needed for these technologies are deployed to protect the organization and its assets.
Back when home networks involved the use of dial-up technologies, most users did not need to concern themselves with security issues. Most homes and small businesses today include wireless networks that introduce security issues that many users do not understand. Organizations also deploy wireless networks but usually employ the appropriate security professionals to ensure that these networks are protected. Without the appropriate controls, any user is able to access the wireless network and possibly breach the security of the entire network.
The popularity of mobile technologies, including flash drives, smartphones, and tablets, has introduced an entirely new level of security concerns. In most cases, senior management does not understand the issues that are introduced when these devices are allowed to access the organization’s network. It is the responsibility of the security professionals to ensure that the appropriate security and privacy controls are implemented to protect the organization.
These examples demonstrate why security professionals must always obtain training to protect their organizations. This is particularly true for security professionals who work for organizations that are usually early adopters of new technology. Early adopters should ensure that they have the appropriate agreements with the vendors of the new technologies so that the organization can be protected against new issues as soon as vendors discover them.
Just as security professionals must understand the security implications of any new technologies they deploy on their organizations’ networks, security professionals should also make sure they understand any new security systems and services that are released. Firewalls first emerged two decades ago as the first IT security systems. Intrusion detection systems (IDSs) and intrusion prevention systems (IPSs) followed shortly thereafter. Today, unified threat management (UTM) combines a traditional firewall with content inspection and filtering, spam filtering, intrusion detection, and antivirus. Biometric systems have increased in popularity, and the security of routers, switches, and other network devices has evolved.
Today, security professionals only need to look at industry blogs, white papers, and knowledge bases to learn about the newest security systems and services. Recently, the biggest advances in security have occurred in the wireless network and mobile device areas. These two areas have introduced new security concerns that never needed to be considered in the past. Fortunately, learning about the security needs in these two areas is just a click away for security professionals. However, caution should be used when researching new security systems and services because not all information comes from reputable sources. Security professionals should always verify that the information, systems, and services they obtain are valid and do not pose a threat to their enterprise.
For many large enterprises, security systems and services are implemented and managed internally. However, some enterprises may choose to outsource to a managed security service provider. These providers may include a broad range of services, including monitoring security devices, providing penetration testing, providing analysis of network activity, and responding to any issues they discover, depending on the terms of the service-level agreement (SLA). Organizations must ensure that SLAs define all the services that the providers will be responsible for.
One emerging trend in which the proper crafting of SLAs is especially relevant is the increasing use of cloud vendors by organizations. Security professionals must ensure that all SLAs specify in detail the exact security measures to be deployed in defense of the organization’s data. Handing of data to a cloud provider does not diminish the obligation of an organization to protect its sensitive data, and security professionals must ensure that SLAs reflect this shared obligation.
Finally, security professionals should keep in mind that any new security technologies or services that are implemented may also introduce new security vulnerabilities. Security professionals should continually assess new security technologies and services to identify any vulnerabilities that exist.
Technology Evolution (e.g., RFCs, ISO)
As technologies evolve, organizations need a means to communicate any major technological advancement that has occurred. The Internet Engineering Task Force (IETF) is an international body of Internet professionals. The IETF is responsible for creating requests for comments (RFCs) that describe research and innovations on the Internet and its systems. Most RFCs are submitted for peer review and, once approved, are published as Internet standards.
RFCs have been issued for a number of Internet protocols and systems. While many RFCs are now obsolete, there are still a great many that are in use today, including the following:

RFC 5198, which covers Telnet
RFCs 2228, 2640, 2773, 3659, 5797, and 7151, on File Transfer Protocol (FTP)
RFCs 1101, 1183, 1101, 1183, 1348, 1876, 1982, 2065, 2181, 2308, 2535, 4033, 4034, 4035, 4343, 4035, 4592, 5936, and 8020, which discuss domain names and the Domain Name System (DNS)
RFC 1157, on Simple Network Management Protocol (SNMP) version 1
RFC 2131, on Dynamic Host Configuration Protocol (DHCP)
RFCs 3337, 3771, 4510, 4511, 4513, and 4512, which cover Lightweight Directory Access Protocol (LDAP) version 3
RFCs 8200, 5095, 5722, 5871, 6437, 6564, 6935, 6946, 7045, and 7112, on IPv6
RFC 2821, which discusses Simple Mail Transfer Protocol (SMTP)
RFCs 2865, 2866, and 3575, on Remote Authentication Dial-in User Server (RADIUS)
RFCs 3315, 4361, 5494, 6221, 6422, 6644, 7083, 7227, 7283, and 7550, on DHCP version 6
While the IETF is primarily concerned with the Internet, the ISO/IEC establishes guidelines and general principles. The Internet Engineering Task Force (IETF) is an international body of Internet professionals. The IETF is responsible for creating requests for comments (RFCs) that are industry standards in many areas. One of the primary standards of concern to security professionals is ISO 17799, which was issued in 2005. It establishes guidelines and general principles for information security management in an organization. ISO 27000 is a family of information security management system (ISMS) standards.
Threat Intelligence
Threat intelligence is a process that is used to inform decisions regarding responses to any menace or hazard presented by the latest attack vectors and actors emerging on the security horizon. It involves analyzing evidence-based knowledge, including context, mechanisms, indicators, implications, and actionable advice, about an existing or emerging menace or hazard to assets.
Performing threat intelligence requires the generation of a certain amount of raw material. This information includes data on the latest attacks, knowledge of current vulnerabilities and threats, specifications on the latest zero-day mitigation controls and remediation techniques, and descriptions of the latest threat models. The following sections cover these topics.
Latest Attacks
To understand client-side attacks, security professionals must first understand server-side attacks. Servers provide services that clients can use, including DNS, DHCP, FTP, and so on. Clients make use of these services by connecting to the server through a port. By allowing connections, servers are vulnerable to attacks from hackers. Any attack directly against a server is considered a server-side attack.
A client-side attack targets vulnerabilities in the client’s applications that work with the server. A client-side attack can occur only if the client makes a successful connection with the server. Client-side attacks are becoming increasingly popular because attackers usually find it easier to attack a client computer and because of the proliferation of client computers. Administrators often ensure that the servers are well protected with the latest updates and security patches. However, the same care is not always taken with client computers, particularly those owned by individuals. Client-side attacks can involve web servers but can also involve client/server configurations using other technologies, including FTP, video streaming, and instant messaging.
To prevent client-side attacks, security professionals should ensure that the client computers are kept up-to-date with the latest updates and security patches for the operating system and all applications. A single update for an application can cause a vulnerability in a client computer that can be exploited. Also, security professionals should ensure that installed applications are limited and that firewalls have rules configured to watch for the use of nonstandard ports. An organization can implement network access control (NAC) policies to ensure that client computers attaching to the network have certain security minimums. Client computers that do not comply with these NAC policies are not allowed to connect. Finally, security awareness training for users should include instruction on how attacks occur and how to report suspected attacks.
As has been stated many times in this book, information technology changes quickly. Security professionals are constantly challenged to ensure that they understand emerging threats and issues and can mitigate these problems. Today, the main emergent threats and issues generally involve mobile computing, cloud computing, and virtualization.
Security professionals face unique challenges due to the increasing use of mobile devices combined with the fact that many of these devices connect using public networks with little or no security. Educating users on the risks related to mobile devices and ensuring that they implement appropriate security measures can help protect against threats involved with these devices. Some of the guidelines that should be provided to mobile device users include implementing a device-locking PIN, using device encryption, implementing GPS location, and enabling remote wiping. Also, users should be cautioned about downloading apps without ensuring that they are coming from a reputable source. In recent years, mobile device management (MDM) and mobile application management (MAM) systems have become popular in enterprises. They are implemented to ensure that an organization can control mobile device settings, applications, and other parameters when those devices are attached to the enterprise.
With cloud computing, a third-party vendor is closely involved in the computer operations of an organization. Security and privacy concerns should be addressed as part of any contract and should include provisions regarding the ownership and dispersion of data. The level of protection for data should be explicitly defined to ensure that the provider will give the level needed. Also, keep in mind that crossing international borders can affect the laws and regulations that govern service.
Today, physical servers are increasingly being consolidated as virtual servers on the same physical box. Virtual networks using virtual switches even exist in the physical devices that host these virtual servers. These virtual network systems and their traffic can be segregated in all the same ways as in a physical network—using subnets, VLANs, and, of course, virtual firewalls. Virtual firewalls are software that has been specifically written to operate in the virtual environment. Increasingly, virtualization vendors such as VMware are making part of their code available to security vendors to create firewalls (and antivirus products) that integrate closely with their products.
Keep in mind that in any virtual environment, each virtual server that is hosted on the physical server must be configured with its own security mechanisms, including antivirus and anti-malware software and all the latest service packs and security updates for all the software hosted on the virtual machine. Also, remember that all the virtual servers share the resources of the physical device. Security professionals should always be on guard for new emerging threats and issues by performing ongoing research. Networking with other security professionals can also provide a great deal of information on these threats and issues.
The following are some examples of the types of attacks that occurred in 2017:
The rise of highly organized groups like Shadow Broker, a group that hacked the U.S. National Security Agency (NSA) and released versions of the hacking tools the NSA has developed
Ransomware attacks such as WannaCry, Petya, and GoldenEye
Cloud vulnerabilities—such as the bugs Cloudflare announced were patched
Multiple hacks of campaign servers, not only in the United States but also in France
Knowledge of Current Vulnerabilities and Threats
A vulnerability is an absence of a countermeasure or a weakness of a countermeasure that is in place. Vulnerabilities can occur in software, hardware, or personnel. An example of a vulnerability is unrestricted access to a folder on a computer. Most organizations implement vulnerability assessments to identify vulnerabilities. A threat is the next logical progression in risk management. A threat occurs when a vulnerability is identified or exploited. An example of a threat is an attacker identifying a folder on a computer that has a misconfigured or absent access control list (ACL).
Because technology changes quickly, security professionals need to have knowledge of the technology used by their organization, the tools used by attackers, and any vulnerabilities within their enterprise that a potential attacker could exploit. To ensure that they have the knowledge they need, security professionals should obtain periodic intensive security training to bring their skills up-to-date.
Currently, some of the biggest threats to organizations are related to the use of mobile devices, wireless networks, and social engineering attacks. Mobile devices, BYOD policies, and wireless networks are gaining popularity with many organizations. Security professionals should familiarize themselves with the vulnerabilities and threats of these technologies and ensure that the enterprise is protected. Social engineering attacks are constantly becoming more complex and convincing, and security awareness training should include examples of the latest techniques.
To identify current vulnerabilities, an organization should perform a vulnerability assessment. Such an assessment helps identify areas of weakness in a network. Vulnerability assessments usually fall into one of three categories:
Personnel testing: Reviews standard practices and procedures that users follow
Physical testing: Reviews facility and perimeter protections
System and network testing: Reviews systems, devices, and network topology
A security analyst who will be performing a vulnerability assessment must understand the systems and devices that are on the network and the jobs they perform. Having this information ensures that the analyst can assess the vulnerabilities of the systems and devices based on known and potential threats to the systems and devices.
As we look ahead, the following are some of the trends we expect:

Ransomware is expected to subside somewhat in 2018. While ransomware has cost billions, initiatives such as the No More Ransom! collaboration, the development and release of anti-ransomware technologies, and continued law enforcement actions will reduce the volume and effectiveness of ransomware.
Vulnerability exploits on Windows should cool down as other platforms heat up. As fewer and fewer opportunities exist to compromise Windows in user mode, attackers will turn to attacking Windows in kernel mode and mounting attacks on more attractive options, such as virtualization software, Adobe Flash, and infrastructure software such as OpenSSL.
Hardware and firmware threats are expected to become an increasing target for sophisticated attackers. While typically only successful when mounted by the skilled hands of a nation-state or advanced persistent threat APT group, an attack on hardware and firmware can be devastating as this firmware forms the platform for the entire device.
Dronejacking is sure to place threats in the sky. At some point, someone will hack into a drone with a laptop and a directional antenna and take over the drone.
Mobile threats will include ransomware, remote access trojan (RATs), and compromised app markets. The app markets for mobile devices will become more dangerous places as RATs, ransomware, and other threats become more widespread.
Zero-Day Mitigation Controls and Remediation
Vulnerabilities are often discovered in live environments before a fix or patch exists. Such vulnerabilities are referred to as zero-day vulnerabilities. A zero-day attack occurs when a security vulnerability in an application is discovered on the same day the application is released. The best way to prevent zero-day attacks is to write bug-free applications by implementing efficient design, coding, and testing practices. It is better to have your staff discover zero-day vulnerabilities than to have those looking to exploit the vulnerabilities find them. Monitoring known hacking community websites can often provide an early alert because hackers often share zero-day exploit information. Honeypots and honeynets can also provide forensic information about hacker methods and tools for zero-day attacks.
New zero-day attacks against a broad range of technology systems are announced regularly. A security manager should create an inventory of applications and maintain a list of critical systems to manage the risks of these attack vectors.
Because zero-day attacks occur before a fix or patch has been released, it is difficult to prevent them. As with many other attacks, keeping all software and firmware up-to-date with the latest updates and patches is important. Enabling audit logging of network traffic can help reconstruct the path of a zero-day attack. Inspection of logs helps security professionals determine the presence of an attack in the network, estimate the damage, and identify corrective actions. Zero-day attacks usually involve activity that is outside “normal” activity, so documenting normal activity baselines is important. Also, routing traffic through a central internal security service can ensure that any fixes affect all the traffic in the most effective manner. Whitelisting can also aid in mitigating attacks by ensuring that only approved entities are able to use certain applications or complete certain tasks. Finally, security professionals should ensure that their organization implements the appropriate backup schemes to ensure that recovery can be achieved, thereby providing remediation from an attack.
Threat Model
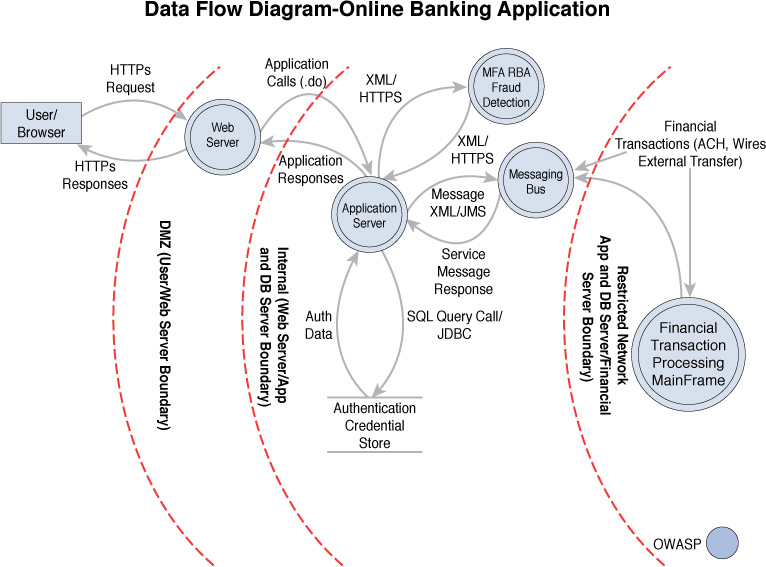
A threat model is a conceptual design that attempts to provide a framework on which to implement security efforts. Many models have been created. Let’s say, for example, that you have an online banking application and need to assess the points at which the application faces threats. Figure 17-1 shows how a threat model in the form of a data flow diagram might be created using the Open Web Application Security Project (OWASP) approach to identify where the trust boundaries are located.
Threat modeling tools go beyond these simple data flow diagrams. Some recent tools are:

Threat Modeling Tool (formerly SDL Threat Modeling Tool) identifies threats based on the STRIDE threat classification scheme.
MyAppSecurity identifies threats based on a customizable comprehensive threat library and is intended for collaborative use across all organizational stakeholders.
IriusRisk offers both community and commercial versions of a tool that focuses on the creation and maintenance of a live threat model through the entire Software Development Life Cycle (SDLC). It connects with several different tools to empower automation.
securiCAD focuses on threat modeling of IT infrastructures using a computer-based design (CAD) based approach where assets are automatically or manually placed on a drawing pane.
SD Elements is a software security requirements management platform that includes automated threat modeling capabilities
Research Security Implications of Emerging Business Tools
While many organizations are cautious about early implementation of new business tools, the senior managers of some organizations are quick to push their IT departments into implementing these business tools even before all the security issues introduced by these tools are known. Security professionals must meet the demands of senior management while keeping enterprise security at the forefront. Recent new business tools include social media/networking and end-user cloud storage. Integration of these business tools within the organization’s enterprise should be carefully planned.
Evolving Social Media Platforms
With the rise in popularity of social media and networking, cybercriminals have started targeting social media users. In 2018, Facebook announced plans to address the posting of fake news or false news stories on its site. Such abuse of the site can have startling effects on public opinion. Any data—whether true or false—can be used to further political causes.
Suppose a company is evaluating a new strategy involving the use of social media to reach its customers so that the marketing director can report important company news, product updates, and special promotions on the social websites. After an initial and successful pilot period, other departments want to use social media to post their updates as well. The chief information officer (CIO) has asked the company security administrator to document three negative security impacts of allowing IT staff to post work-related information on such websites. In this scenario, the security administrator should report back to the CIO that the major risks of social media include malware infection, phishing attacks, and social engineering attacks. The company should dedicate specific staff to act as social media representatives of the company. The security policy needs to be reviewed to ensure that the social media policy is properly implemented.
If an organization decides to allow its employees to access and use social media at work, strict policies and guidelines should be established, including:

Make sure all devices and applications are up-to-date.
Ensure that the organization employs layers of security to defend the enterprise against security threats.
Create acceptable use policies that explicitly spell out the details about social media usage at work. These policies should include what type of company information can be published by all personnel and what type should only come from senior management or public relations.
Include social media training as part of the security awareness training that all personnel must obtain.
End-User Cloud Storage
Although cloud technologies have been out for a few years, they are just now starting to become popular with end users. Unfortunately, most end users do not fully understand the security implications of cloud storage.
Cloud services give end users more accessibility to their data. However, this also means that end users can take advantage of cloud storage to access and share company data from any location. At that point, the IT team no longer controls the data. This is the case with both public and private clouds.
With private clouds, organizations can:
Ensure that the data is stored only on internal resources.
Ensure that the data is owned by the organization.
Ensure that only authorized individuals are allowed to access the data.
Ensure that data is always available.
However, a private cloud is only protected by the organization’s internal resources, and this protection can often be affected by the knowledge level of the security professionals responsible for managing the cloud security.
With public clouds, organizations can be sure that:
Data is protected by enterprise-class firewalls and within a secured facility.
Attackers and disgruntled employees are unsure of where the data actually resides.
The cloud vendor will provide security expertise and must maintain the level of service detailed in the contract.
However, public clouds can grant access to any location, and data is transmitted over the Internet. Also, the organization depends on the vendor for all services provided.
End users must be educated about cloud usage and limitations as part of their security awareness training. In addition, security policies should clearly state where data can be stored, and ACLs should be configured properly to ensure that only authorized personnel can access data. The policies should also spell out consequences for storing organizational data in cloud locations that are not authorized.
Integration Within the Business
As with many other technologies, most organizations had very strict policies against the use of social media at its advent. But through the years, organizations have adopted more lenient policies when it comes to the use of social media at work.
When cloud implementations were first becoming popular, many organizations shied away from giving a vendor so much control over organizational data. However, as more cloud providers have been established and prices have continued to improve, more organizations are choosing to use some sort of cloud implementation for their enterprise.
If your organization decides to implement these new business tools or any new tool that comes in the future, it is important that a full risk assessment be done before the organization implements the new tool. Policies should be put into place to protect the organization and its assets, and user security awareness is essential. Users should be aware of exactly what is allowed with these new tools. For example, regular users should never announce new products on their own pages until an official organizational announcement is made, and then the users should only divulge the information that is given in the official announcement.
Integrating new tools within a business can often bring many advantages and make the organization work more effectively. However, security professionals must be given the time and resources to ensure that these tools do not adversely affect the organization’s security.
Big Data
Big data is a term for sets of data so large or complex that they cannot be analyzed by using traditional data processing applications. Specialized applications have been designed to help organizations with their big data. The big data challenges that may be encountered include data analysis, data capture, data search, data sharing, data storage, and data privacy.
While big data is used to determine the causes of failures, generate coupons at checkout, recalculate risk portfolios, and find fraudulent activity before it ever has a chance to affect the organization, its existence creates security issues. The first issue is its unstructured nature. Traditional data warehouses process structured data and can store large amounts of it, but there is still a requirement for structure.
Big data typically uses Hadoop, which requires no structure. Hadoop is an open source framework used for running applications and storing data. With the Hadoop Distributed File System, individual servers that are working in a cluster can fail without aborting the entire computation process. There are no restrictions on the data that this system can store.
While big data is enticing because of the advantages it offers, it presents a number of issues:

Organizations still do not understand it very well, and unexpected vulnerabilities can easily be introduced.
Open source codes are typically found in big data, which can result in unrecognized backdoors. It can contain default credentials.
Attack surfaces of the nodes may not have been reviewed, and servers may not have been hardened sufficiently.
Authentication of users and data access from other locations may not be controlled.
Log access and audit trails may be an issue.
Opportunities for malicious activity, such as malicious data input and poor validation, are plentiful.
The relative security of a big data solution rests primarily on the knowledge and skill sets of the individuals implementing and managing the solution and the partners involved rather than the hardware and software involved.
AI/Machine Learning
Artificial intelligence (AI) and machine learning have fascinated humans for decades. Since the first time we conceived of the idea of talking to a computer and getting an answer like characters did in comic books years ago, we have waited for the day to come when smart robots would not just do the dirty work but also learn just as humans do.
Today, robots are taking on increasingly more and more detailed work. One of the exciting areas where AI and machine learning is yielding dividends is in intelligent network security—or the intelligent network. These networks seek out their own vulnerabilities before attackers do, learn from past errors, and work on a predictive model to prevent attacks.
For example, automatic exploit generation (AEG) is the “first end-to-end system for fully automatic exploit generation,” according to the Carnegie Mellon Institute’s own description of its AI named Mayhem. Developed for off-the-shelf as well as the enterprise software being increasingly used in smart devices and appliances, AEG can find a bug and determine whether it is exploitable.
Global IA Industry/Community
The global information assurance (IA) industry and community comprise many official groups that provide guidance on information security. Three groups that are involved in this industry include the SysAdmin, Audit, Network, and Security (SANS) Institute, the International Information Systems Security Certification Consortium [(ISC)2], and the International Council of Electronic Commerce Consultants (EC-Council). These groups provide guidance on establishing information technology security and also offer security certifications. The IT security community is also full of individuals and small groups who are often very willing to help security professionals in their day-to-day struggles.
The following sections discuss CERT, conventions/conferences, threat actors, and emerging threat sources and threat intelligence.
Computer Emergency Response Team (CERT)
CERT is a community comprised of many official groups that provide guidance on information security. These groups study security vulnerabilities and provide assistance to organizations that fall victim to attacks. It is part of the Software Engineering Institute at Carnegie Mellon University. It offers 24-hour emergency response service and shares information for improving web security.
A similar organization is the U.S. Computer Emergency Readiness Team (US-CERT), part of the National Cyber Security Division of the U.S. Department of Homeland Security. US-CERT works closely with CERT to coordinate responses to cybersecurity threats.
An organization should have an internal incident response team. When establishing its incident response team, an organization must consider the technical knowledge of each individual. The members of the team must understand the organization’s security policy and have strong communication skills. Members should also receive training in incident response and investigations.
When an incident has occurred, the primary goal of the team is to contain the attack and repair any damage caused by the incident. Security isolation of an incident scene should start immediately when the incident is discovered. Evidence must be preserved, and the appropriate authorities should be notified.
An incident response team should have access to the organization’s incident response plan. This plan should include the list of authorities to contact (including CERT), team roles and responsibilities, an internal contact list, procedures for securing and preserving evidence, and a list of investigation experts who can be contacted for help. The organization should create a step-by-step manual for the incident response team to follow to ensure that no steps are skipped. It may be necessary to involve CERT early in the process if help is needed. After the incident response process has been engaged, all incident response actions should be documented.
If the incident response team determines that a crime has been committed, senior management and the proper authorities should be contacted immediately.
Conventions/Conferences
Perhaps one of the best avenues for security professionals to get the latest on information security is to attend security conventions and conferences. Such conventions and conferences cover different facets of security, but the majority of them fit into one of three categories: security industry, academic security, and hacking.
Probably the most well-known conference is RSA Conference, which covers all facets of security and draws security professionals from across the employment spectrum, including educators, government personnel, and other security professionals. This conference has an agenda that includes several tracks, including cloud and data security, cybercrime and law enforcement, mobile security, and security infrastructure.
The Black Hat convention is an annual conference held in Las Vegas and other locations in Europe and Asia. It includes four days of training and two days of briefings, providing attendees with the latest in information security research, development, and trends in a vendor-neutral environment.
DEFCON conferences are focused on hacking and are considered more technical in nature than many of the other popular conferences.
It is important for security professionals to use security conventions and conferences as the learning tools they are intended to be. Often the training obtained at these events can help prepare a security professional for what is coming, while also covering what has already occurred in the security field.
Research Consultants/Vendors
Organizations are increasingly looking outside themselves for research, including research on trends in security. Well-respected organizations such as Accenture, BAE Systems Applied Intelligence, Booz Allen, and KPMG provide much better research than organizations can do for themselves—for a price. Only the very largest corporate entities can afford to maintain research departments that can produce the quality that can be obtained at the prices commanded by these vendors.
Threat Actor Activities
A threat is carried out by a threat actor. An attacker who takes advantage of an inappropriate or absent ACL is a threat agent. Keep in mind, though, that threat actors can discover and/or exploit vulnerabilities. Not all threat actors will actually exploit an identified vulnerability.
The U.S. Federal Bureau of Investigation (FBI) has identified three categories of threat actors:

Organized crime groups primarily threatening the financial services sector and expanding the scope of their attacks
State sponsors, usually foreign governments, interested in pilfering data, including intellectual property and research and development data from major manufacturers, government agencies, and defense contractors
Terrorist groups that want to impact countries by using the Internet and other networks to disrupt or harm the viability of a society by damaging its critical infrastructure
While there are other less organized groups out there, law enforcement considers these three groups to be the primary threat actors. However, organizations should not totally disregard the threats of any threat actors that fall outside these three categories. Lone actors or smaller groups that use hacking as a means to discover and exploit any discovered vulnerability can cause damage just like the larger, more organized groups.
Hacker and cracker are two terms that are often used interchangeably in media but do not actually have the same meaning. Hackers are individuals who attempt to break into secure systems to obtain knowledge about the systems and possibly use that knowledge to carry out pranks or commit crimes. Crackers, on the other hand, are individuals who attempt to break into secure systems without using the knowledge gained for any nefarious purposes. Hacktivists are the latest new group to crop up. They are activists for a cause, perhaps for animal rights, that use hacking as a means to get their message out and affect the businesses that they feel are detrimental to their cause.
In the security world, the terms white hat, gray hat, and black hat are more easily understood and less often confused than the terms hackers and crackers. A white hat does not have any malicious intent. A black hat has malicious intent. A gray hat is somewhere between the other two. A gray hat may, for example, break into a system, notify the administrator of the security hole, and offer to fix the security issues for a fee.
Threat actors use a variety of techniques to gather the information required to gain a foothold.
Topology Discovery
Topology discovery entails determining the devices in the network, their connectivity relationships to one another, and the internal IP addressing scheme in use. Any combination of these pieces of information allow a hacker to create a “map” of the network, which aids tremendously in evaluating and interpreting the data gathered in other parts of the hacking process. If the hacker is completely successful, he will end up with a diagram of the network. Your challenge as a security analyst is to determine whether such a mapping process is possible, using some of the processes and tools covered later in this chapter. Based on your findings, you should determine steps to take that make topology discovery either more difficult or, better yet, impossible.
OS Fingerprinting
Operating system fingerprinting is the process of using some method to determine the operating system running on a host or a server. By identifying the OS version and build number, a hacker can identify common vulnerabilities of that operating system using readily available documentation from the Internet. While many of the issues will have been addressed in subsequent updates, service packs, and hot fixes, there might be zero-day weaknesses (issues that have not been widely publicized or addressed by the vendor) that the hacker can leverage in the attack. Moreover, if any of the relevant security patches have not been applied, the weaknesses the patches were intended to address will exist on the machine. Therefore, the purpose of attempting OS fingerprinting during assessment is to assess the relative ease with which it can be done and identify methods to make it more difficult.
Service Discovery
Operating systems have well-known vulnerabilities, and so do common services. By determining the services that are running on a system, an attacker also discovers potential vulnerabilities of the service and may attempt to take advantage of them. This is typically done with a port scan, in which all “open,” or “listening,” ports are identified. Once again, the lion’s share of these issues will have been mitigated with the proper security patches, but that is not always the case; it is not uncommon for security analysts to find that systems that are running vulnerable services are missing the relevant security patches. Consequently, when performing service discovery, patches should be checked on systems found to have open ports. It is also advisable to close any ports not required for the system to do its job.
Packet Capture
Packet capture is the process of using capture tools to collect raw packets from the network. Attackers are almost certain to attempt packet capture if given the opportunity. By using packet capture, attackers may discover the following:
Sensitive data that is not encrypted
Information that, while not sensitive, may help with the OS, network, and service discovery process
Packets sent between routers that may reveal network and device information
By performing packet capture, a security analyst can see what attackers see and can take steps to mitigate the most revealing issues.
Log Review
Although logs are not generally available to an attacker until a specific host is compromised, security analysts should examine logs of all infrastructure devices and critical server systems for signs of attempted access, both successful and unsuccessful. It is likely that the first thing an attacker will do after compromising a system is to clear entries in the log related to her access, but attackers may at times fail to do this. Moreover, in some cases careful examination of system and application logs may reveal that access entries are not present or have been deleted by the attacker.
Router/Firewall ACLs Review
Routers and firewalls perform critical networking functions in the environment. They may contain routing tables and access list configuration information that can greatly assist in network fingerprinting. Information regarding a device’s operating system may also reveal common attacks that may be successful on the device. Probing your own devices can help you see what information would be available to an attacker. As a part of this process, both the operating system and firmware present on the device should be checked for any missing updates and patches, which are frequently forgotten on these devices.
Email Harvesting
Attackers often attempt a process called email harvesting, and a security analyst should do this as well. Typically email harvesting bots (automated processes) are used for this. Common ways in which email addresses are gathered include the following:
From posts with email addresses
From mailing lists
From web pages and web forms
Through the Ident daemon (The Identification Protocol [often called the Ident Protocol or IDENT], specified in RFC 1413, is an Internet protocol that helps identify the user of a particular TCP connection.)
From Internet Relay Chat and chat rooms
By accessing a computer used by a valid user
Through social engineering
By buying lists from other spammers
By accessing the emails and address books in another user’s computer
So why do attackers gather email addresses? One of the biggest reasons is to use the addresses as source addresses for spamming. That’s bad enough, but certain social engineering attacks involve sending emails to targeted employees in an organization. In a type of phishing attack called a spear phishing attack, emails are designed to lure a user or group of users to connect to a site that appears to be a well-known and secure site for the purpose of harvesting access credentials.
Social Media Profiling
A great deal of information can be exchanged or made available to the world through social media. In some cases, employees may unwittingly (or intentionally) reveal sensitive information that can be used to further an attack. As a part of a security policy, it should be made clear to users what can and cannot be revealed in social media. Training should also be provided to the organization on the dangers of social media as well as malware. As a part of assessing the environment, security analysts should employ the same social media profiling activities as an attacker.
Social Engineering
As a part of assessing the security environment, analysts should attempt the most common social engineering attacks to determine the level of security awareness of the organization’s users. These attacks involve gaining the trust of a user and in some way convincing him or her to reveal sensitive information such as a password or to commit other actions that reduce the security of the network. In this way, an attacker enlists a user as an unwitting assistant in attacking the network. When social engineering issues are found, training should be provided to users to prevent these attacks in the future.
Phishing
Phishing is a social engineering attack that involves sending a mass email that appears to come from a trusted party, such as the recipient’s bank. It includes a link that purports to connect to the bank’s site, when in reality it is a fake site under the attacker’s control that appears to be identical to the bank’s site in every way. When the user enters his or her credentials, the attacker collects them and can then use them to impersonate the user at the real site. As a part of assessing your environment, you should send out these types of emails to assess the willingness of your users to respond. A high number of successes indicates that users need training to prevent successful phishing attacks.
Emerging Threat Sources
New threat sources and threat intelligence are emerging daily. Many organizations may find themselves victims of cybercrime. Organizations must constantly battle to stay ahead of the attackers to protect their data and other assets. Unfortunately, no organization today is immune to attacks.
Security professionals can use emerging threat reports and intelligence as a means to convince management of the need to invest in new security devices and training. Emerging threat reports paired with company attack trends can be even more convincing. So make sure to use all the tools at your disposal to make your case!
Our society depends on computers and information technology so much today that it is very rare to find an organization that is not connected to the Internet. It is vital that security professionals from across the spectrum work together to battle the emerging threats and share with each other information regarding these threats and their attack vectors. Consider groups like Anonymous and Julian Assange’s WikiLeaks that are known for their attacks but were relatively unknown just a few years ago. Even terrorist organizations are becoming more technologically savvy in their methods of attack. As in most other cases, education is key. A security professional never stops learning!
Exam Preparation Tasks
As mentioned in the section “How to Use This Book” in the Introduction, you have a couple choices for exam preparation: the exercises here and the practice exams in the Pearson IT Certification test engine.
Review All Key Topics
Review the most important topics in this chapter, noted with the Key Topics icon in the outer margin of the page. Table 17-1 lists these key topics and the page number on which each is found.

Table 17-1 Key Topics for Chapter 17
Key Topic Element |
Description |
Page Number |
List |
Best practices |
640 |
List |
Key RFCs |
643 |
List |
Upcoming vulnerabilities and threats |
647 |
List |
648 |
|
List |
Social media guidelines |
650 |
List |
Big data security issues |
652 |
List |
FBI categories of threat actors |
655 |
Define Key Terms
Define the following key terms from this chapter and check your answers in the glossary:
Computer Emergency Readiness Team (CERT)
Internet Engineering Task Force (IETF)
intrusion detection system (IDS)
intrusion protection system (IPS)
operating system fingerprinting
U.S. Computer Emergency Readiness Team (US-CERT)
unified threat management (UTM)
Review Questions
1. Senior management at your organization has implemented a policy which states that best practice documentation must be created for all security personnel. Which of the following is a valid reason for this documentation?
Using this documentation will ensure that the organization will not have any legal issues due to security.
Using this documentation will ensure that the organization will not have any security breaches.
Using this documentation will allow security personnel to ensure that they know what to do according to industry standards.
Using this documentation will ensure that the security personnel are properly trained.
2. Which organization issues RFCs?
IETF
IEEE
ISO
IEC
3. Which threat modeling tool allows for assets to be automatically or manually placed on a drawing pane?
Threat Modeling Tool
SD Elements
securiCAD
IriusRisk
4. Recently, your organization has fallen victim to several client-side attacks. Management is very concerned and wants to implement some new policies that could negatively impact your business. You explain to management some of the measures that should be taken to protect against these attacks. Management asks why client-side attacks are increasing. What should be your reply? (Choose all that apply.)
Servers are more expensive than clients.
Client computers cannot be protected as well as servers.
Client computers are not usually as protected as servers.
There are more clients than servers.
5. The application development team of your organization has released a new version of an application today. Within hours, several posts regarding a security vulnerability in the application appear on popular hacker forums. Which type of attack does this indicate?
client-side attack
end-user attack
advanced persistent threat
zero-day attack
6. Which of the following entails determining the devices in the network, their connectivity relationships to one another, and the internal IP addressing scheme in use?
OS fingerprinting
service discovery
packet capture
topology discovery
7. Which of the following is a social engineering attack that involves sending a mass email that appears to come from a trusted party, such as the recipient’s bank?
SYN flood
phishing
tailgating
shoulder surfing
8. How are new technologies submitted for peer review to the IETF and, once approved, published as Internet standards?
as SLAs
as RFCs
as RFPs
as SPDs
9. Which of the following is not one of the three threat actors listed by the FBI?
organized crime groups
state sponsors
terrorist groups
natural disasters
10. Which of the following is typically used with big data?
Hadoop
BGP
AI
CERT