Chapter 2
Asset Security (Domain 2)
- Angela is an information security architect at a bank and has been assigned to ensure that transactions are secure as they traverse the network. She recommends that all transactions use TLS. What threat is she most likely attempting to stop, and what method is she most likely using to protect against it?
- Man-in-the-middle, VPN
- Packet injection, encryption
- Sniffing, encryption
- Sniffing, TEMPEST
- Control Objectives for Information and Related Technology (COBIT) is a framework for information technology (IT) management and governance. Which data management role is most likely to select and apply COBIT to balance the need for security controls against business requirements?
- Business owners
- Data processors
- Data owners
- Data stewards
- Nadia's company is operating a hybrid cloud environment with some on-site systems and some cloud-based systems. She has satisfactory monitoring on-site, but needs to apply security policies to both the activities her users engage in and to report on exceptions with her growing number of cloud services. What type of tool is best suited to this purpose?
- A NGFW
- A CASB
- An IDS
- A SOAR
- When media is labeled based on the classification of the data it contains, what rule is typically applied regarding labels?
- The data is labeled based on its integrity requirements.
- The media is labeled based on the highest classification level of the data it contains.
- The media is labeled with all levels of classification of the data it contains.
- The media is labeled with the lowest level of classification of the data it contains.
- Which one of the following administrative processes assists organizations in assigning appropriate levels of security control to sensitive information?
- Data classification
- Remanence
- Transmitting data
- Clearing
- How can a data retention policy help to reduce liabilities?
- By ensuring that unneeded data isn't retained
- By ensuring that incriminating data is destroyed
- By ensuring that data is securely wiped so it cannot be restored for legal discovery
- By reducing the cost of data storage required by law
- Staff in an information technology (IT) department who are delegated responsibility for day-to-day tasks hold what data role?
- Business owner
- User
- Data processor
- Custodian
- Helen's company uses a simple data lifecycle as shown in the figure here. What stage should come first in their data lifecycle?
- Data policy creation
- Data labeling
- Data collection
- Data analysis
- Ben has been tasked with identifying security controls for systems covered by his organization's information classification system. Why might Ben choose to use a security baseline?
- It applies in all circumstances, allowing consistent security controls.
- They are approved by industry standards bodies, preventing liability.
- They provide a good starting point that can be tailored to organizational needs.
- They ensure that systems are always in a secure state.
- Megan wants to prepare media to allow for its reuse in an environment operating at the same sensitivity level. Which of the following is the best option to meet her needs?
- Clearing
- Erasing
- Purging
- Sanitization
- Mikayla wants to identify data that should be classified that already exists in her environment. What type of tool is best suited to identifying data like Social Security numbers, credit card numbers, and similar well-understood data formats?
- Manual searching
- A sensitive data scanning tool
- An asset metadata search tool
- A data loss prevention system (DLP)
- What issue is common to spare sectors and bad sectors on hard drives as well as overprovisioned space on modern SSDs?
- They can be used to hide data.
- They can only be degaussed.
- They are not addressable, resulting in data remanence.
- They may not be cleared, resulting in data remanence.
- Naomi knows that commercial data is typically classified based on different criteria than government data. Which of the following is not a common criterion for commercial data classification?
- Useful lifespan
- Data value
- Impact to national security
- Regulatory or legal requirements
For questions 14–16, please refer to the following scenario:
Your organization regularly handles three types of data: information that it shares with customers, information that it uses internally to conduct business, and trade secret information that offers the organization significant competitive advantages. Information shared with customers is used and stored on web servers, while both the internal business data and the trade secret information are stored on internal file servers and employee workstations.
- What term best describes data that is resident in system memory?
- Data at rest
- Buffered data
- Data in use
- Data in motion
- What technique could you use to mark your trade secret information in case it was released or stolen and you need to identify it?
- Classification
- Symmetric encryption
- Watermarks
- Metadata
- What type of encryption is best suited for use on the file servers for the proprietary data, and how might you secure the data when it is in motion?
- TLS at rest and AES in motion
- AES at rest and TLS in motion
- VPN at rest and TLS in motion
- DES at rest and AES in motion
- What does labeling data allow a DLP system to do?
- The DLP system can detect labels and apply appropriate protections based on rules.
- The DLP system can adjust labels based on changes in the classification scheme.
- The DLP system can modify labels to permit requested actions.
- The DLP system can delete unlabeled data.
- Why is it cost effective to purchase high-quality media to contain sensitive data?
- Expensive media is less likely to fail.
- The value of the data often far exceeds the cost of the media.
- Expensive media is easier to encrypt.
- More expensive media typically improves data integrity.
- Chris is responsible for workstations throughout his company and knows that some of the company's workstations are used to handle both proprietary information and highly sensitive trade secrets. Which option best describes what should happen at the end of their life (EOL) for workstations he is responsible for?
- Erasing
- Clearing
- Sanitization
- Destruction
- Fred wants to classify his organization's data using common labels: private, sensitive, public, and proprietary. Which of the following should he apply to his highest classification level based on common industry practices?
- Private
- Sensitive
- Public
- Proprietary
- What scenario describes data at rest?
- Data in an IPsec tunnel
- Data in an e-commerce transaction
- Data stored on a hard drive
- Data stored in RAM
- If you are selecting a security standard for a Windows 10 system that processes credit cards, what security standard is your best choice?
- Microsoft's Windows 10 security baseline
- The CIS Windows 10 baseline
- PCI DSS
- The NSA Windows 10 Secure Host Baseline
For questions 23–25, please refer to the following scenario:
The Center for Internet Security (CIS) works with subject matter experts from a variety of industries to create lists of security controls for operating systems, mobile devices, server software, and network devices. Your organization has decided to use the CIS benchmarks for your systems. Answer the following questions based on this decision.
- The CIS benchmarks are an example of what practice?
- Conducting a risk assessment
- Implementing data labeling
- Proper system ownership
- Using security baselines
- Adjusting the CIS benchmarks to your organization's mission and your specific IT systems would involve what two processes?
- Scoping and selection
- Scoping and tailoring
- Baselining and tailoring
- Tailoring and selection
- How should you determine which controls from the baseline should be applied to a given system or software package?
- Consult the custodians of the data.
- Select based on the data classification of the data it stores or handles.
- Apply the same controls to all systems.
- Consult the business owner of the process the system or data supports.
- The company that Henry works for operates in the EU and collects data about their customers. They send that data to a third party to analyze and provide reports to help the company make better business decisions. What term best describes the third-party analysis company?
- The data controller
- The data owner
- The data subject
- The data processor
- The government defense contractor that Selah works for has recently shut down a major research project and is planning on reusing the hundreds of thousands of dollars of systems and data storage tapes used for the project for other purposes. When Selah reviews the company's internal processes, she finds that she can't reuse the tapes and that the manual says they should be destroyed. Why isn't Selah allowed to degauss and then reuse the tapes to save her employer money?
- Data permanence may be an issue.
- Data remanence is a concern.
- The tapes may suffer from bitrot.
- Data from tapes can't be erased by degaussing.
- Information maintained about an individual that can be used to distinguish or trace their identity is known as what type of information?
- Personally identifiable information (PII)
- Personal health information (PHI)
- Social Security number (SSN)
- Secure identity information (SII)
- Which of the following information security risks to data at rest would result in the greatest reputational impact on an organization?
- Improper classification
- Data breach
- Decryption
- An intentional insider threat
- Full disk encryption like Microsoft's BitLocker is used to protect data in what state?
- Data in transit
- Data at rest
- Unlabeled data
- Labeled data
- The company that Katie works for provides its staff with mobile phones for employee use, with new phones issued every two years. What scenario best describes this type of practice when the phones themselves are still usable and receiving operating system updates?
- EOL
- Planned obsolescence
- EOS
- Device risk management
- What is the primary purpose of data classification?
- It quantifies the cost of a data breach.
- It prioritizes IT expenditures.
- It allows compliance with breach notification laws.
- It identifies the value of the data to the organization.
- Fred's organization allows downgrading of systems for reuse after projects have been finished and the systems have been purged. What concern should Fred raise about the reuse of the systems from his Top Secret classified project for a future project classified as Secret?
- The Top Secret data may be commingled with the Secret data, resulting in a need to relabel the system.
- The cost of the sanitization process may exceed the cost of new equipment.
- The data may be exposed as part of the sanitization process.
- The organization's DLP system may flag the new system due to the difference in data labels.
- Which of the following concerns should not be part of the decision when classifying data?
- The cost to classify the data
- The sensitivity of the data
- The amount of harm that exposure of the data could cause
- The value of the data to the organization
- Which of the following is the least effective method of removing data from media?
- Degaussing
- Purging
- Erasing
- Clearing
For questions 36–38, please refer to the following scenario:
The healthcare company that Amanda works for handles HIPAA data as well as internal business data, protected health information, and day-to-day business communications. Its internal policy uses the following requirements for securing HIPAA data at rest and in transit.
Classification Handling Requirements Confidential (HIPAA) Encrypt at rest and in transit. Full disk encryption is required for all workstations. Files can only be sent in encrypted form, and passwords must be transferred under separate cover. Printed documents must be labeled with “HIPAA handling required.” Private (PHI) Encrypt at rest and in transit. PHI must be stored on secure servers, and copies should not be kept on local workstations. Printed documents must be labeled with “Private.” Sensitive (business confidential) Encryption is recommended but not required. Public Information can be sent unencrypted. - What encryption technology would be appropriate for HIPAA documents in transit?
- BitLocker
- DES
- TLS
- SSL
- Amanda's employer asks Amanda to classify patient X-ray data that has an internal patient identifier associated with it but does not have any way to directly identify a patient. The company's data owner believes that exposure of the data could cause damage (but not exceptional damage) to the organization. How should Amanda classify the data?
- Public
- Sensitive
- Private
- Confidential
- What technology could Amanda's employer implement to help prevent confidential data from being emailed out of the organization?
- DLP
- IDS
- A firewall
- UDP
- Jacob's organization uses the US government's data classification system, which includes Top Secret, Secret, Confidential, and Unclassified ratings (from most sensitive to least). Jacob encounters a system that contains Secret, Confidential, and Top Secret data. How should it be classified?
- Top Secret
- Confidential
- Secret
- Mixed classification
- Elle is planning her organization's asset retention efforts and wants to establish when the company will remove assets from use. Which of the following is typically the last event in a manufacturer or software provider's lifecycle?
- End of life
- End of support
- End of sales
- General availability
- Amanda has been asked to ensure that her organization's controls assessment procedures match the specific systems that the company uses. What activity best matches this task?
- Asset management
- Compliance
- Scoping
- Tailoring
- Chris is responsible for his organization's security standards and has guided the selection and implementation of a security baseline for Windows PCs in his organization. How can Chris most effectively make sure that the workstations he is responsible for are being checked for compliance and that settings are being applied as necessary?
- Assign users to spot-check baseline compliance.
- Use Microsoft Group Policy.
- Create startup scripts to apply policy at system start.
- Periodically review the baselines with the data owner and system owners.
- Frank is reviewing his company's data lifecycle and wants to place appropriate controls around the data collection phase. Which of the following ensures that data subjects agree to the processing of their data?
- Retention
- Consent
- Certification
- Remanence
- As a DBA, Amy's data role in her organization includes technical implementations of the data policies and standards, as well as managing the data structures that the data is stored in. What data role best fits what Amy does?
- Data custodian
- Data owner
- Data processor
- Data user
- The company Jim works for suffered from a major data breach in the past year and now wants to ensure that it knows where data is located and if it is being transferred, is being copied to a thumb drive, or is in a network file share where it should not be. Which of the following solutions is best suited to tagging, monitoring, and limiting where files are transferred to?
- DRM
- DLP
- A network IPS
- Antivirus
- What security measure can provide an additional security control in the event that backup tapes are stolen or lost?
- Keep multiple copies of the tapes.
- Replace tape media with hard drives.
- Use appropriate security labels.
- Use AES-256 encryption.
- Joe works at a major pharmaceutical research and development company and has been tasked with writing his organization's data retention policy. As part of its legal requirements, the organization must comply with the US Food and Drug Administration's Code of Federal Regulations Title 21. To do so, it is required to retain records with electronic signatures. Why would a signature be part of a retention requirement?
- It ensures that someone has reviewed the data.
- It provides confidentiality.
- It ensures that the data has been changed.
- It validates who approved the data.
- Susan wants to manage her data's lifecycle based on retention rules. What technique can she use to ensure that data that has reached the end of its lifecycle can be identified and disposed of based on her organization's disposal processes?
- Rotation
- DRM
- DLP
- Tagging
- Ben has been asked to scrub data to remove data that is no longer needed by his organization. What phase of the data lifecycle is Ben most likely operating in?
- Data retention
- Data maintenance
- Data remanence
- Data collection
- Steve is concerned about the fact that employees leaving his organization were often privy to proprietary information. Which one of the following controls is most effective against this threat?
- Sanitization
- NDAs
- Clearing
- Encryption
- Alex works for a government agency that is required to meet US federal government requirements for data security. To meet these requirements, Alex has been tasked with making sure data is identifiable by its classification level when it is created. What should Alex do to the data?
- Classify the data.
- Encrypt the data.
- Label the data.
- Apply DRM to the data.
- Ben is following the National Institute of Standards and Technology (NIST) Special Publication 800-88 guidelines for sanitization and disposition as shown here. He is handling information that his organization classified as sensitive, which is a moderate security categorization in the NIST model. If the media is going to be sold as surplus, what process does Ben need to follow?
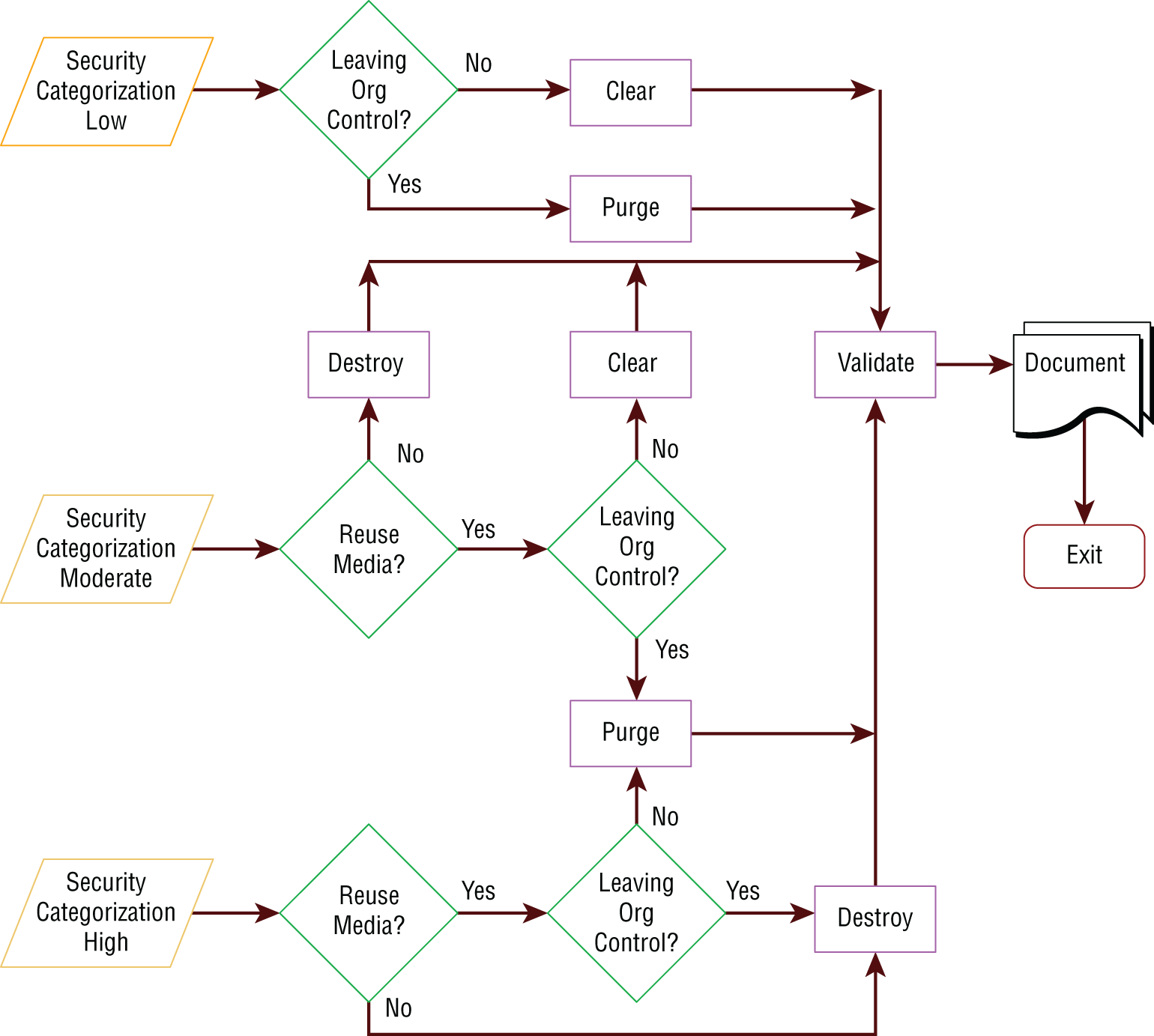
Source: NIST SP 800-88.
- Destroy, validate, document
- Clear, purge, document
- Purge, document, validate
- Purge, validate, document
- What methods are often used to protect data in transit?
- Telnet, ISDN, UDP
- BitLocker, FileVault
- AES, Serpent, IDEA
- TLS, VPN, IPsec
- Which one of the following data roles bears ultimate organizational responsibility for data?
- System owners
- Business owners
- Data owners
- Mission owners
- Shandra wants to secure an encryption key. Which location would be the most difficult to protect, if the key was kept and used in that location?
- On a local network
- On disk
- In memory
- On a public network
For questions 56–58, please refer to the following scenario:
Chris has recently been hired into a new organization. The organization that Chris belongs to uses the following classification process:
- Criteria are set for classifying data.
- Data owners are established for each type of data.
- Data is classified.
- Required controls are selected for each classification.
- Baseline security standards are selected for the organization.
- Controls are scoped and tailored.
- Controls are applied and enforced.
- Access is granted and managed.
- If Chris is one of the data owners for the organization, what steps in this process is he most likely responsible for?
- He is responsible for steps 3, 4, and 5.
- He is responsible for steps 1, 2, and 3.
- He is responsible for steps 5, 6, and 7.
- All of the steps are his direct responsibility.
- Chris manages a team of system administrators. What data role are they fulfilling if they conduct steps 6, 7, and 8 of the classification process?
- They are system owners and administrators.
- They are administrators and custodians.
- They are data owners and administrators.
- They are custodians and users.
- If Chris's company operates in the European Union and has been contracted to handle the data for a third party, what role is his company operating in when it uses this process to classify and handle data?
- Business owners
- Mission owners
- Data processors
- Data administrators
For questions 59–62, please refer to the following scenario:
Chris has been put in charge of his organization's IT service management effort, and part of that effort includes creating an inventory of both tangible and intangible assets. As a security professional, you have been asked to provide Chris with security-related guidance on each of the following topics. Your goal is to provide Chris with the best answer from each of the options, knowing that in some cases more than one of the answers could be acceptable.
- Chris needs to identify all of the active systems and devices on the network. Which of the following techniques will give him the most complete list of connected devices?
- Query Active Directory for a list of all computer objects.
- Perform a port scan of all systems on the network.
- Ask all staff members to fill out a form listing all of their systems and devices.
- Use network logs to identify all connected devices and track them down from there.
- Chris knows that his inventory is only accurate at the moment it was completed. How can he best ensure that it remains up-to-date?
- Perform a point-in-time query of network connected devices and update the list based on what is found.
- Ensure that procurement and acquisition processes add new devices to the inventory before they are deployed.
- Require every employee to provide an updated inventory of devices they are responsible for on a quarterly basis.
- Manually verify every device in service at each organizational location on a yearly basis.
- Chris knows that his organization has more than just physical assets. In fact, his organization's business involves significant intellectual property assets, including designs and formulas. Chris needs to track and inventory those assets as well. How can he most effectively ensure that he can identify and manage data throughout his organization based on its classification or type?
- Track file extensions for common data types.
- Ensure that data is collected in specific network share locations based on the data type and group that works with it.
- Use metadata tagging based on data type or security level.
- Automatically tag data by file extension type.
- Chris has been tasked with identifying intangible assets but needs to provide his team with a list of the assets they will be inventorying. Which of the following is not an example of an intangible asset?
- Patents
- Databases
- Formulas
- Employees
- Which of the following is not a common requirement for the collection of data under data privacy laws and statutes?
- Only data that is needed is collected.
- Data should be obtained lawfully and via fair methods.
- Data should only be collected with the consent of the individual whose data is being collected.
- Data should be collected from all individuals equally.
- Susan works in an organization that labels all removable media with the classification level of the data it contains, including public data. Why would Susan's employer label all media instead of labeling only the media that contains data that could cause harm if it was exposed?
- It is cheaper to order all prelabeled media.
- It prevents sensitive media from not being marked by mistake.
- It prevents reuse of public media for sensitive data.
- Labeling all media is required by HIPAA.
- Data stored in RAM is best characterized as what type of data?
- Data at rest
- Data in use
- Data in transit
- Data at large
- What issue is the validation portion of the NIST SP 800-88 sample certificate of sanitization (shown here) intended to help prevent?
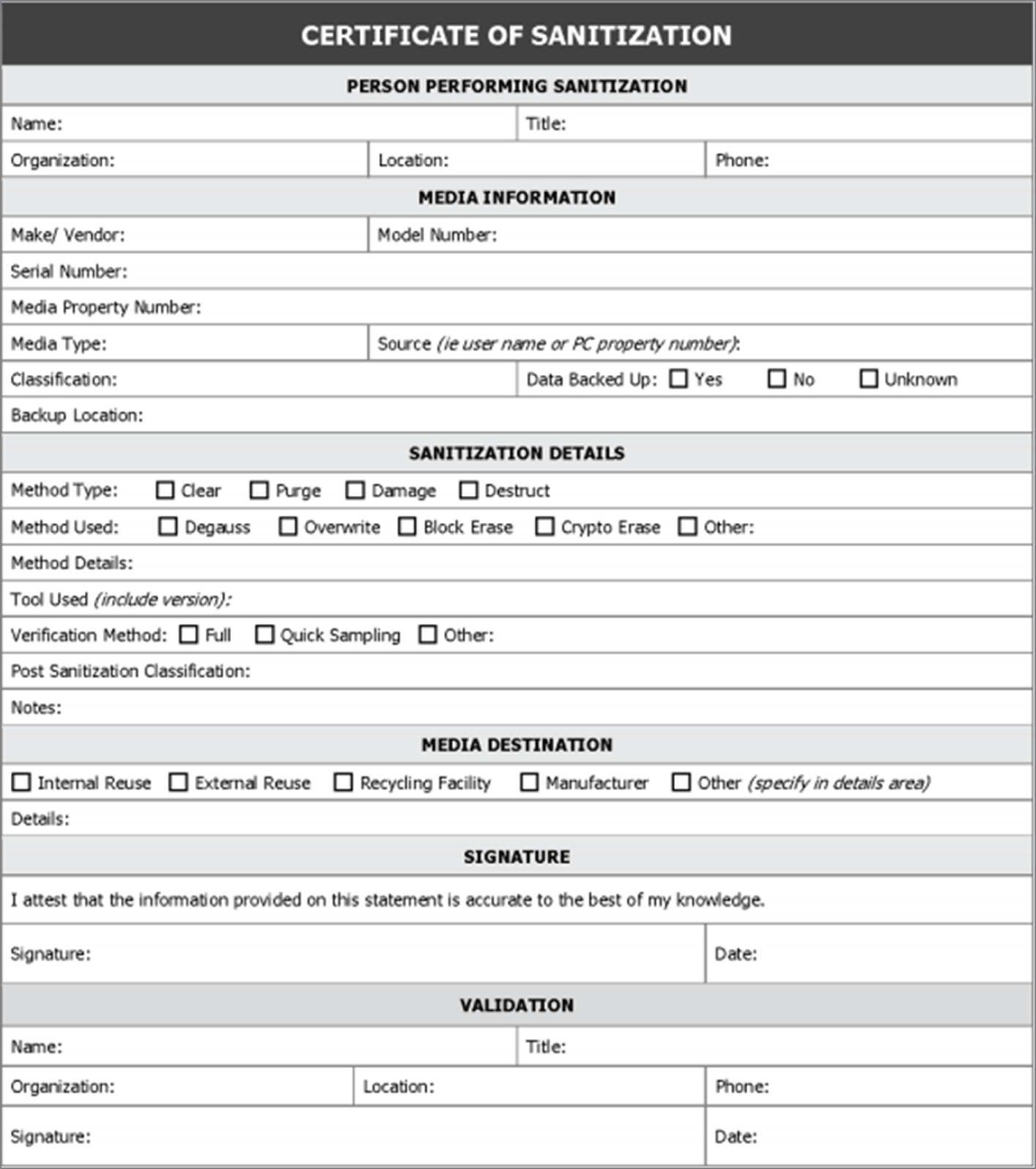
Source: Certificate of Sanitization.
- Destruction
- Reuse
- Data remanence
- Attribution
- Why is declassification rarely chosen as an option for media reuse?
- Purging is sufficient for sensitive data.
- Sanitization is the preferred method of data removal.
- It is more expensive than new media and may still fail.
- Clearing is required first.
- Incineration, crushing, shredding, and disintegration all describe what stage in the lifecycle of media?
- Sanitization
- Degaussing
- Purging
- Destruction
- What term is used to describe information like prescriptions and X-rays?
- PHI
- Proprietary data
- PID
- PII
- Why might an organization use unique screen backgrounds or designs on workstations that deal with data of different classification levels?
- To indicate the software version in use
- To promote a corporate message
- To promote availability
- To indicate the classification level of the data or system
- Charles has been asked to downgrade the media used for storage of private data for his organization. What process should Charles follow?
- Degauss the drives, and then relabel them with a lower classification level.
- Pulverize the drives, and then reclassify them based on the data they contain.
- Follow the organization's purging process, and then downgrade and replace labels.
- Relabel the media, and then follow the organization's purging process to ensure that the media matches the label.
- Which of the following tasks is not performed by a system owner per NIST SP 800-18?
- Develops a system security plan
- Establishes rules for appropriate use and protection of data
- Identifies and implements security controls
- Ensures that system users receive appropriate security training
- NIST SP 800-60 provides a process shown in the following diagram to assess information systems. What process does this diagram show?
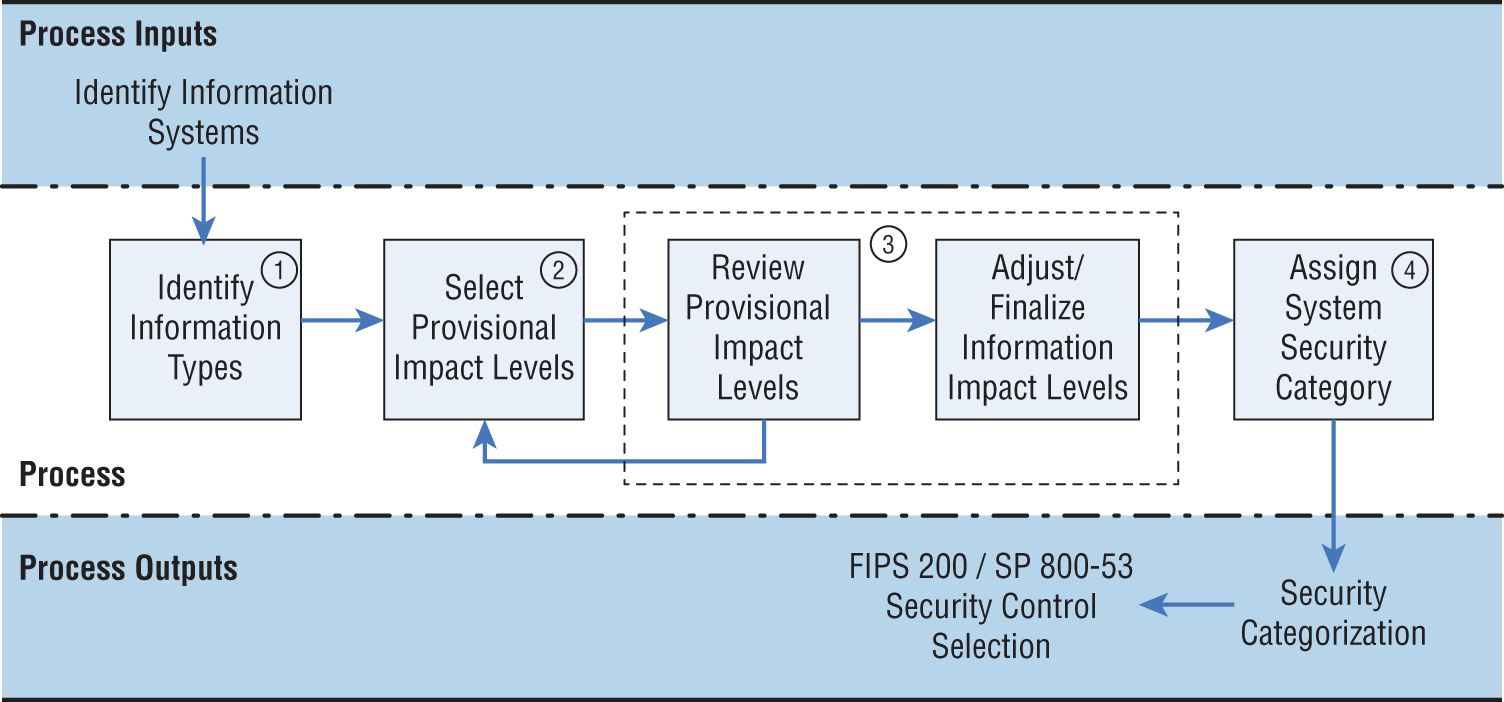
Source: NIST SP 800-60.
- Selecting a standard and implementing it
- Categorizing and selecting controls
- Baselining and selecting controls
- Categorizing and sanitizing
The following diagram shows a typical workstation and server and their connections to each other and the internet. For questions 74–76, please refer to this diagram.

- Which letters on this diagram are locations where you might find data at rest?
- A, B, and C
- C and E
- A and E
- B, D, and F
- What would be the best way to secure data at points B, D, and F?
- AES-256
- SSL
- TLS
- 3DES
- What is the best way to secure files that are sent from workstation A via the internet service (C) to remote server E?
- Use AES at rest at point A, and use TLS in transit via B and D.
- Encrypt the data files and send them.
- Use 3DES and TLS to provide double security.
- Use full disk encryption at A and E, and use SSL at B and D.
- Susan needs to provide a set of minimum security requirements for email. What steps should she recommend for her organization to ensure that the email remains secure?
- All email should be encrypted.
- All email should be encrypted and labeled.
- Sensitive email should be encrypted and labeled.
- Only highly sensitive email should be encrypted.
- How can a data retention policy reduce liabilities?
- By reducing the amount of storage in use
- By limiting the number of data classifications
- By reducing the amount of data that may need to be produced for lawsuits
- By reducing the legal penalties for noncompliance
- What data role does a system that is used to process data have?
- Mission owner
- Data owner
- Data processor
- Custodian
- Which one of the following is not considered PII under US federal government regulations?
- Name
- Social Security number
- Student ID number
- ZIP code
- What type of health information is the Health Insurance Portability and Accountability Act required to protect?
- PII
- PHI
- SHI
- HPHI
- The system that Ian has built replaces data in a database field with a randomized string of characters that remains the same for each instance of that data. What technique has he used?
- Data masking
- Tokenization
- Anonymization
- DES
- Juanita's company processes credit cards and wants to select appropriate data security standards. What data security standard is she most likely to need to use and comply with?
- CC-Comply
- PCI-DSS
- GLBA
- GDPR
- What is the best method to sanitize a solid-state drive (SSD)?
- Clearing
- Zero fill
- Disintegration
- Degaussing
For questions 85–87, please refer to the following scenario:
As shown in the following security lifecycle diagram (loosely based on the NIST reference architecture), NIST uses a five-step process for risk management. Using your knowledge of data roles and practices, answer the following questions based on the NIST framework process.
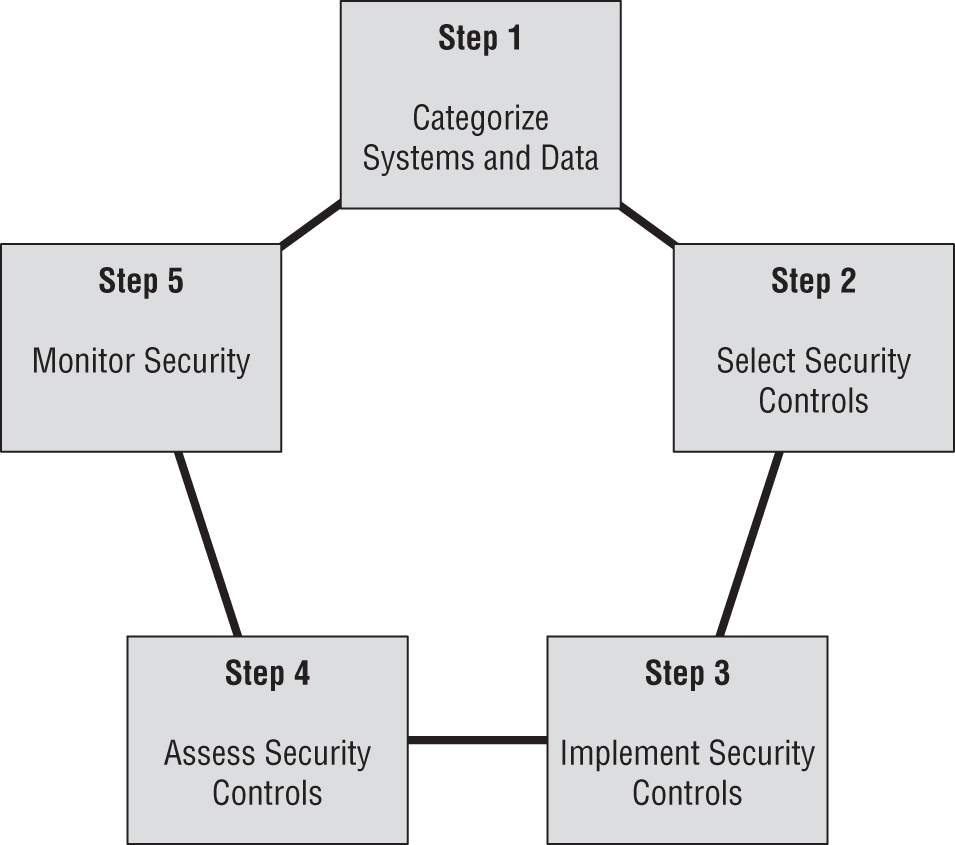
- What data role will own responsibility for step 1, the categorization of information systems; to whom will they delegate step 2; and what data role will be responsible for step 3?
- Data owners, system owners, custodians
- Data processors, custodians, users
- Business owners, administrators, custodians
- System owners, business owners, administrators
- If the systems that are being assessed all handle credit card information (and no other sensitive data), at what step would the PCI DSS first play an important role?
- Step 1
- Step 2
- Step 3
- Step 4
- What data security role is primarily responsible for step 5?
- Data owners
- Data processors
- Custodians
- Users
- Susan’s organization performs a secure disk wipe process on hard drives before they are sent to a third-party organization to be shredded. What issue is her organization attempting to avoid?
- Data retention that is longer than defined in policy
- Mishandling of drives by the third party
- Classification mistakes
- Data permanence
- Mike wants to track hardware assets as devices and equipment are moved throughout his organization. What type of system can help do this without requiring staff to individually check bar codes or serial numbers?
- A visual inventory
- WiFi MAC address tracking
- RFID tags
- Steganography
- Retaining and maintaining information for as long as it is needed is known as what?
- Data storage policy
- Data storage
- Asset maintenance
- Record retention
- Which of the following activities is not a consideration during data classification?
- Who can access the data
- What the impact would be if the data was lost or breached
- How much the data cost to create
- What protection regulations may be required for the data
- What type of encryption is typically used for data at rest?
- Asymmetric encryption
- Symmetric encryption
- DES
- OTP
- Which data role is tasked with apply rights that provide appropriate access to staff members?
- Data processors
- Business owners
- Custodians
- Administrators
- What element of asset security is often determined by identifying an asset's owner?
- It identifies the individual(s) responsible for protecting the asset.
- It provides a law enforcement contact in case of theft.
- It helps establish the value of the asset.
- It determines the security classification of the asset.
- Fred is preparing to send backup tapes off-site to a secure third-party storage facility. What steps should Fred take before sending the tapes to that facility?
- Ensure that the tapes are handled the same way the original media would be handled based on their classification.
- Increase the classification level of the tapes because they are leaving the possession of the company.
- Purge the tapes to ensure that classified data is not lost.
- Decrypt the tapes in case they are lost in transit.
- Which of the following does not describe data in motion?
- Data on a backup tape that is being shipped to a storage facility
- Data in a TCP packet
- Data in an e-commerce transaction
- Data in files being copied between locations
- A new law is passed that would result in significant financial harm to your company if the data that it covers was stolen or inadvertently released. What should your organization do about this?
- Select a new security baseline.
- Relabel the data.
- Encrypt all of the data at rest and in transit.
- Review its data classifications and classify the data appropriately.
- Which of the following data roles are typically found inside of a company instead of as a third-party contracting relationship? (Select all that apply.)
- Data owners
- Data controllers
- Data custodians
- Data processors
- What commercial data classification is most appropriate for data contained on corporate websites?
- Private
- Sensitive
- Public
- Proprietary
- Match each of the numbered data elements shown here with one of the lettered categories. You may use the categories once, more than once, or not at all. If a data element matches more than one category, choose the one that is most specific.
Data elements
- Medical records
- Trade secrets
- Social Security numbers
- Driver's license numbers
Categories
- Proprietary data
- Protected health information
- Personally identifiable information