CHAPTER 1
Cloud Computing Concepts, Models, and Terminology
In this chapter, you will learn about
• Cloud service models
• Cloud deployment models and services
• Cloud characteristics and terms
• Advanced cloud services
Moving some or all of an organization’s infrastructure to the cloud provides a number of benefits to that organization, including power savings, on-demand storage, ease of administration, ability to pay for only the resources it uses, and a metered environment that can offer almost 100 percent uptime if included in the service level agreement (SLA)—a costly undertaking when provided by the organization itself. An SLA is a contract between a cloud service provider (CSP) and a cloud consumer that formally defines the cloud service and who is responsible for it.
This chapter covers the basic concepts, models, and terminology that are the building blocks of cloud computing. It lays a foundation for the rest of the book by building scenarios for cloud deployments that the subsequent chapters can be compared to and modeled against for a better understanding of what cloud computing is, how it can be deployed, and the value it provides both to information technology (IT) organizations and the customers that they support.
Cloud Service Models
A cloud service model is a set of IT-related services offered by a CSP. The CSP is responsible for supplying cloud-based IT resources to a cloud consumer under a predefined and mutually agreed upon SLA. The CSP is responsible for administrative maintenance and management of the cloud infrastructure, which allows the cloud consumer to focus its administrative effort on other aspects of the business. In essence, the cloud consumer is buying or leasing its IT infrastructure from the CSP.
The entity that legally owns the cloud service is known as the cloud service owner. Either the CSP or the cloud consumer can be the cloud service owner, depending on the terms of the SLA.
It is critical to understand who is responsible for the services hosted in the cloud. Before an organization migrates any piece of its business to the cloud, it needs to understand who is “in control” of those resources. A variety of cloud service models offer the cloud consumer a number of different options. To implement a successful cloud deployment, you need to understand each of the cloud service models and the service that each provides. In this section, you will learn about each of the different cloud service models and when to implement each.
Infrastructure as a Service
Infrastructure as a Service (IaaS) is the model by which the cloud consumer outsources responsibility for its computer hardware, network, and operating systems to an external CSP. The CSP not only owns the equipment that provides the infrastructure resources but is also responsible for the ongoing operation and maintenance of those resources. In this model, the cloud consumer is charged on a “pay-as-you-use” or “pay-as-you-grow” basis. IaaS can include the server storage, infrastructure, and connectivity domains. For example, the cloud consumer could deploy and run its own applications and operating systems, while the IaaS provider would handle the following:
• Storage resources, including replication, backup, and archiving
• Compute resources, which are the resources traditionally provided by servers or server farms, including processor, memory, disk, and networking
• Connectivity domains, including infrastructure management and security, such as network load balancing and firewalls
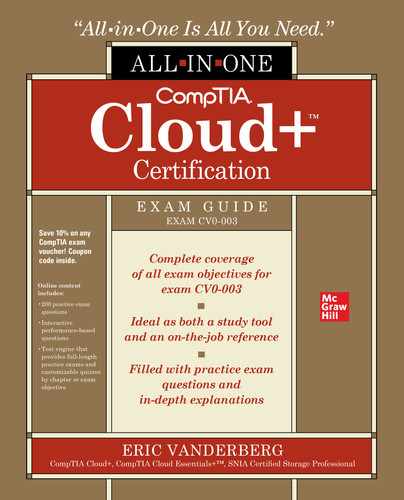
When an organization utilizes IaaS, it no longer has to buy, maintain, or upgrade server hardware, which can help it save resources, time, and money. Since IaaS allows an organization to pay only for the resources it uses, the organization no longer needs to outlay expenditures for hardware resources it either is not using or is not using to maximum capacity. IaaS allows an organization to spin up additional resources quickly and efficiently without having to purchase physical hardware. For example, the IT department might need a development environment to test a new application; with IaaS, this development environment could be spun up quickly and then removed when the new application has been fully tested. IaaS allows an organization to meet hardware capacity spikes without having to add resources to its data center. Figure 1-1 shows you a graphical representation of the services that are offered by an IaaS provider.
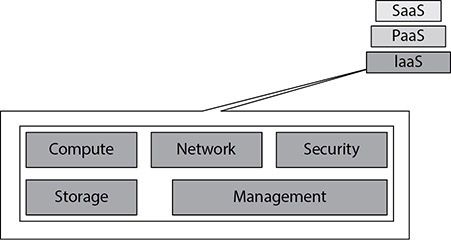
Figure 1-1 Infrastructure as a Service (IaaS) provider services
Platform as a Service
Platform as a Service (PaaS) enables customers to have applications deployed without the time, cost, and human resources required to buy and manage their own back-end hardware and software. PaaS applications are either consumer created or acquired web applications or services that are entirely accessible from the Internet. The tools and programming languages used to create PaaS applications are usually supplied by the CSP.
PaaS web applications enable cloud consumers to control the deployed applications via an application programming interface (API) without having to manage the complexity of all the underpinning servers, operating systems, or storage. In some circumstances, the cloud consumer is also allowed to control the application hosting environment. PaaS offers cloud consumers a speedy time to market and an integrated way to provision services over the Web. PaaS facilitates the immediate delivery of business requirements such as application design, development, and testing at a fraction of the cost.
PaaS providers offer a variety of services and service combinations spanning the entire application deployment life cycle. Some of the service features are source code, application usage tracking, versioning, and testing tools. Figure 1-2 shows a graphical representation of the services offered by PaaS providers.
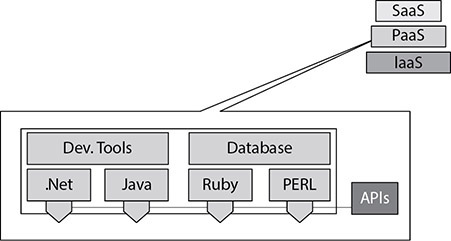
Figure 1-2 Platform as a Service (PaaS) provider services
Software as a Service
Software as a Service (SaaS) is a cloud service model that enables a cloud consumer to use on-demand software applications delivered by the CSP via a thin client device, typically a web browser over the Internet. The web-based application features of SaaS have been around for quite some time before cloud became a term. Such applications were referred to as application service provider (ASP) software. SaaS customers delegate both the management and control of the infrastructure, such as storage, servers, network, or operating systems, to their CSP.
SaaS is a quick and efficient service model for key business applications such as customer relationship management (CRM), enterprise resource planning (ERP), human resources (HR), and payroll. Figure 1-3 shows you a graphical representation of the services offered by SaaS providers.
Figure 1-3 Software as a Service (SaaS) provider services
Database as a Service
Database as a Service (DBaaS) is essentially a form of software specializing in the delivery of database operations. This service enables CSPs to offer database functionality to multiple discrete cloud consumers. DBaaS infrastructures support the following competencies:
• Self-service database instance provisioning for the customer
• Monitoring of attributes and quality-of-service levels to ensure compliance with provider-defined service agreements
• Carefully measured usage of database services, enabling chargeback functionality for each individual cloud consumer
A DBaaS infrastructure may also support service elasticity, secure multitenancy, access using a wide range of devices, automated resource management, and capacity planning. These concepts will be discussed later in this chapter.
Communications as a Service
Communications as a Service (CaaS) enables customers to utilize enterprise-level voice over IP (VoIP), virtual private networks (VPNs), private branch exchange (PBX), and unified communications without the costly investment of purchasing, hosting, and managing their own infrastructure. With the CSP being responsible for the management and operation of this infrastructure, the customer also has the advantage of not having to source and staff its own trained personnel, bringing significant relief to both operational and capital costs.
Business Process as a Service
Business Process as a Service (BPaaS) mixes business process management (BPM) with one or more aspects of a cloud service model (SaaS, IaaS, or PaaS). BPM is an approach that aims to make a company’s workflow more effective, efficient, and agile, allowing it to respond quickly to changes driven by business requirements. This kind of workflow enables businesses to be more flexible and to decrease their spending.
Traditional business process management systems (BPMSs) integrate business processes and keep track of running their corresponding instances. A BPMS coordinates the execution of a business process step by step. Each process instance is monitored by the BPMS and provides users with feedback on progress to validate successful completion or to alert on failures. In case of a failure, the BPMS shows where the process failure occurred. By monitoring, analyzing, and identifying where business processes fail, companies can act proactively and optimize the deployment of their business service. This ultimately leads to lower costs and improved customer satisfaction.
A BPaaS is any business process that is delivered as a service by utilizing a cloud solution. With BPaaS, one or more business processes are uploaded to a cloud service that performs each process step and monitors them while they execute. As with any other cloud environment, BPaaS enables customers to use cloud software in a pay-per-use model instead of having to invest in hardware and maintenance.
Essentially, BPaaS is a cloud service that frees up not just internal computing resources but also human resources who may have been dedicated to performing that process. For example, a cloud-based payroll system can perform the functions of a payroll or HR employee by issuing paychecks and tax statements and processing deductions and benefits. Similarly, a cloud CRM can offload some tasks associated with qualifying leads, communicating with prospects, and sales project management.
Anything as a Service
Anything as a Service (XaaS) is the delivery of IT as a service through a combination of cloud service models; it works with one or a combination of SaaS, IaaS, PaaS, CaaS, DBaaS, or BPaaS. The X in XaaS is a variable that can be changed to represent a variety of different cloud services.
Accountability and the Shared Responsibility Model
Now that you understand all the different cloud service models, you need to become familiar with who is responsible for those services. Accountability in the cloud can be split between multiple parties, including cloud consumers, infrastructure providers, and CSPs. Accountability in cloud computing is about creating a holistic approach to achieve security in the cloud and to address the lack of consumer trust. The very nature of cloud computing brings a new level of complexity to the issue of determining who is responsible for a service outage, and CSPs are faced with the difficult task of achieving compliance across geographic boundaries. A service outage can be the result of a variety of issues, such as software vulnerabilities, power outages, hardware failure, network disruption, application error, or user error.
The three primary service models in cloud computing have differing security approaches for businesses. With SaaS, the CSP is responsible for maintaining the agreed-upon service levels between the CSP and the cloud consumer and for security, compliance, and liability expectations. When it comes to PaaS and IaaS, the cloud consumer is responsible for managing the same expectations, while the CSP takes some of the responsibility for securing the underlying infrastructure. Service outages can also be attributed to the end-user device having misconfiguration or hardware failures. Table 1-1 provides a quick reference for the party responsible for maintaining the service levels of each cloud service model.

Table 1-1 Service Level Responsibility
When discussing accountability and responsibility in the cloud, it is important to classify risk according to the service model being utilized and the location of the data. For example, if a business is using a hybrid cloud, both the consumer and the CSP can be responsible for the same risks, since part of the data is in the cloud and part is in the internal data center. It is important that the SLAs and any other agreements signed between the cloud consumer and CSP clearly state who is responsible for preventing and remedying outages and how those outages are classified, identified, and measured. Figure 1-4 shows who the typical cloud consumer is for each cloud model.
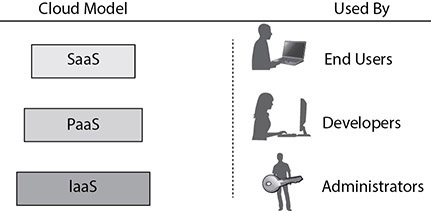
Figure 1-4 Cloud service models and their consumers
Another consideration is the division of responsibility for maintenance tasks in a cloud environment. Patching and maintenance contribute greatly to the overall security and performance in a cloud solution. Responsibility is broken out in such a way that the CSP is responsible for the patching and maintenance “of” the cloud, and the cloud consumer is responsible for patching “in” the cloud. We will explore this concept further in Chapter 10 when diving into systems management.
Cloud Deployment Models and Services
You have just learned about the different service models available for implementing a cloud computing solution. To realize the value from these service models and for the customers to have access to them, a deployment model must be chosen. Implementing a cloud deployment model can vastly affect an organization. Implementation requires careful consideration and planning to be successful. If your role is the IT administrator, it is your responsibility to educate the organization on the benefits and challenges of implementing a cloud deployment model. You need to evaluate the business needs and determine what benefits a cloud deployment model would bring to your organization. Whichever cloud deployment model you choose, whether it be private, public, or hybrid (all described next), it needs to map well to the business processes you are trying to achieve.
Private Cloud
In a private cloud deployment model, the cloud is owned by a single organization and enables central access to IT resources for departments and staff distributed among a variety of locations. A private cloud solution is implemented behind the corporate firewall and is maintained by the same organization that is using it. A private cloud utilizes internal resources and is designed to offer the same benefits of a public cloud without relinquishing control, security, and recurring costs to a CSP. In a private cloud model, the same organization is both the cloud consumer and the CSP.
The decision to implement a private cloud is usually driven by the need to maintain control of the environment because of regulatory or business reasons. For example, a bank might have data security issues that prevent it from using a public cloud service, so the bank might implement a private cloud to achieve the benefits of a cloud computing model.
A private cloud is a combination of virtualization, data center automation, chargeback metering, and identity-based security. Virtualization allows for easy scalability, flexible resource management, and maximum hardware utilization. A private cloud solution also involves having the ability to auto-provision physical host computers through orchestration software, which is discussed later in this chapter. Some organizations use private clouds to share storage between internal systems or departments. This is referred to as a private cloud space (PCS).
One of the downsides to a private cloud is that an organization does not get the return on investment it does with other cloud models. This is because the organization is still responsible for running and managing the resources instead of passing that responsibility to a CSP.
Public Cloud
Unlike a private cloud that is owned by the organization, a public cloud is a pool of computing services delivered over the Internet via a CSP. A CSP makes resources such as applications and storage available to organizations over the Internet. Public clouds use a pay-as-you-go model, which gives organizations the benefit of paying only for the resources that they consume. Public clouds allow for easy and inexpensive setup because the hardware, application, and bandwidth costs are covered and maintained by the CSP and charged as part of the service agreement.
You may recognize SaaS offerings such as cloud storage and online office applications (e.g., Microsoft Office 365) as public cloud offerings. What you may not know is that IaaS and PaaS offerings, including cloud-based web hosting and development environments, can be part of a public cloud as well.
Public clouds are used when an organization is less likely to need full customization or the level of flexibility and control offered by private clouds. Organizations requiring data security can still utilize public clouds to make their operations significantly more efficient with the storage of nonsensitive content, online document collaboration, and webmail.
A public cloud offers ultimate scalability because cloud resources are available on demand from the CSP’s vast pool of resources. Organizations do not need to purchase and implement hardware to scale the environment; they just need to obtain more resources from the CSP. The availability of the public cloud via an Internet connection allows the services to be used wherever the client is located, making a public cloud location-independent. Some examples of public CSPs are Microsoft Azure, Google Cloud, SAP Cloud Platform, Oracle Cloud, IBM Cloud Foundry, VMware vCloud, and Amazon Web Services.
Hybrid Cloud
A hybrid cloud is a cloud service that utilizes both private and public clouds to perform distinct functions within the same organization. An organization might have a need for both a local server running specific applications for security reasons and a public cloud hosting additional applications, files, and databases. These two environments would be configured for scalability and interoperability.
In a hybrid cloud model, an organization continues to provide and manage some resources internally, while other resources are provided externally by a CSP. A hybrid cloud allows an organization to take advantage of the scalability and cost-effectiveness of a public cloud without exposing mission-critical data to a public CSP.
A cloud model is defined as a hybrid cloud if an organization is using a public development platform that sends data to a private cloud. Another example of a hybrid cloud model is when an organization uses multiple SaaS applications and moves that application data between a private cloud or an internal data center.
A cloud is not considered a hybrid if an organization uses SaaS applications and does not move the data to a private cloud or internal data center. A cloud environment is labeled a hybrid cloud only if there is a combination of private and public clouds or if data is moved between the internal data center and the public cloud. You can see an example of a hybrid cloud environment in Figure 1-5.

Figure 1-5 Components of a hybrid cloud environment
Community Cloud
A community cloud is a cloud offering where the infrastructure is shared between several organizations from a specific group with common computing needs or objectives. Community clouds are built and operated specifically for a targeted group of entities that have common cloud requirements and whose ultimate goal is to work together to achieve a specific business objective.
Community clouds are usually implemented for organizations working on joint projects that require a central cloud for managing and executing those projects. A finance community cloud, for example, could be set up to provide specific security requirements or optimized to provide low latency to perform financial transactions. A community cloud can be either on-premises or off-premises and can be managed by a CSP or by the organizations themselves.
Cloud Within a Cloud
Cloud within a cloud offers the flexibility of a private cloud without the investment and operational cost of the infrastructure. Essentially, public cloud resources are used to create a private cloud for the consumer. The consumer would use the public cloud resources to provision the virtual infrastructure and systems for their services and manage access to those systems.
On-Premises vs. Off-Premises Hosting
On-premises hosting is the solution that IT professionals are likely most familiar with. On-premises hosting is the traditional way of managing a data center. In an on-premises environment, the virtualized servers are hosted on-site at the organization’s internal data center, and the organization owns and maintains that server hardware. The benefit of on-premises hosting is that the organization has complete control over the daily management and maintenance of its servers. The downside to on-premises hosting is that the organization has to pay the costs of maintaining the internal data center, including power, security, maintenance, licenses, hardware, and other costs.
Off-premises hosting is sometimes referred to as cloud computing. With off-premises hosting, the IT resources are hosted in the cloud and accessed online. Off-premises hosting can be used for server virtualization or applications to be hosted in the cloud. One of the benefits of off-premises hosting is that the cost is usually lower than on-premises hosting because the resources are hosted online instead of in the organization’s data center. This allows the organization to convert IT costs to the pay-as-you-grow model, keeping IT costs down. Off-premises hosting is sometimes perceived as less secure or as having a higher security risk, since the organization loses control of its data because it is hosted in the cloud.
Orchestration Platforms
Automation of day-to-day administrative tasks is becoming more and more of a requirement for IT departments. Orchestration platforms provide an automated way to manage the cloud or computing environment. They make it possible to achieve a dynamic data center by aligning business requests with applications, data, and infrastructure. A typical business model defines policies and service levels that an IT department must meet. Orchestration platforms help an IT department meet these requirements through automated workflows, provisions, and change management features. This allows for a dynamic and scalable infrastructure that is constantly changing based on the needs of the business. For example, with an orchestration platform, a developer could request the creation of a virtual machine via a service portal, and the orchestration software would automatically create that virtual machine based on a predefined template. Orchestration software can also be used for centralized management of a resource pool, including billing, software metering, and chargeback or showback for resource utilization.
Orchestration platforms provide companies with automated tools to perform tasks that would typically take a team of administrators to complete. These platforms offer an automated approach to creating hardware and software, allowing them to work together to deliver a predefined service or application. Orchestration platforms make it possible for the cloud environment to easily scale and provision new applications and services on demand through workflows.
Some examples of orchestration platforms include Cloudify, Terraform, Ansible, IBM Cloud Orchestrator, Flexiant Cloud Orchestrator, and Microsoft System Center Orchestrator. All of the orchestration platforms allow for the creation of workflows to automate day-to-day administrative tasks.
Multicloud
Most organizations today utilize a large number of cloud systems. Multicloud is the use of two or more cloud systems to comprise a system. Multicloud allows a company to take the best components from multiple vendors and combine them together into a solution that meets their needs. Some cloud solutions may be too rigid for a company’s needs, so they take the pieces they need from multiple providers. In other cases, a single CSP presents too much risk to the organization, so they spread an application across two or more providers for redundancy. If one CSP goes down, services are rebalanced across the other providers.
Cloud Characteristics and Terms
When implementing a cloud computing model, an organization needs to understand the terminology of cloud computing and the characteristics of remote provisioning of a scalable and measured IT resource. The IT administrator, as a cloud consumer, needs to work with the CSP to assess these characteristics and measure the value offering of the chosen cloud platform.
Elasticity
Elasticity can be thought of as unlimited space that allows the organization to dynamically provision and deprovision processing, memory, and storage resources to meet the demands of its network. Elasticity allows an organization to shift and pool resources across dissimilar infrastructure, allowing data to be more synchronized and avoiding overprovisioning of hardware. It is one of the many benefits of cloud computing because it allows an IT department to be scalable without having to purchase and stand up hardware in its internal data center. The primary difference between elasticity and scalability is that scalability is the ability of a system to increase its workload on the current hardware resources, whereas elasticity is the ability of a system to increase its workload by adding hardware resources or shrink resources for decreasing workloads.
Demand-Driven Service
In an on-demand self-service environment, users have access to cloud services through an online portal. This gives them the ability to provision cloud resources on demand wherever and whenever they need to. On-demand, or “just-in-time,” self-service allows cloud consumers to acquire computing resources automatically and on demand without human interaction from the CSP.
Pay-as-You-Grow
One of the advantages of the public cloud is the pay-as-you-grow philosophy. The pay-as-you-grow charging model allows an organization to pay for services by the hour or based on the compute resources it uses. Therefore, pay-as-you-grow does not require a large up-front investment by the organization for infrastructure resources. It is important for an organization to design and plan its cloud costs before deploying its first application in the cloud. Most CSPs have a calculator to help organizations figure the costs they would incur by moving to the cloud. This gives organizations a better understanding of the pay-as-you-grow model when it comes to cloud pricing and using the public cloud infrastructure.
Chargeback
IT chargeback is an accounting strategy that attempts to decentralize the costs of IT services and apply them directly to the teams or divisions that utilize those services. This system enables organizations to make better decisions about how their IT dollars are spent, as it can help determine the true cost of a particular service. Without a chargeback system, all IT costs are consolidated under the IT department umbrella, and the ability to determine the true profitability of the individual business services the IT department supports is limited or impossible. Most private clouds and internal IT departments use the term “showback” instead of chargeback to describe the amount of resources being consumed by a department.
Ubiquitous Access
With ubiquitous access, a CSP’s capabilities are available over the network and can be accessed through standard mechanisms by many different types of clients, and without the requirement for application deployment or a specific operating system configuration. This does not necessarily mean Internet access. Ubiquitous access does, however, allow a cloud service to be widely accessible via a web browser from anywhere. A cloud consumer can get the same level of access, whether at home, at work, or in a coffee shop.
Metering
Metering is the ability of a cloud platform to track the use of its IT resources and is geared primarily toward measuring usage by cloud consumers. A metering function allows the CSP to charge a cloud consumer only for the IT resources actually being used. Metering is closely tied to on-demand or demand-driven cloud usage.
Metering is not only used for billing purposes; it can also be used for general monitoring of IT resources and usage reporting for both the consumer and the provider. This makes metering a benefit for not only public clouds but private cloud models as well.
Multitenancy
Multitenancy is an architecture that provides a single instance of an application to serve multiple clients or tenants. Tenants are allowed to have their own view of the application and make customizations while remaining unaware of other tenants who are using the same application.
Multitenant applications ensure that tenants do not have access to change the data and configuration of the application on their own. However, tenants are allowed to change the user interface to give the application a personalized look and feel.
Implementing a multitenant application is, of course, more complicated than working with a single-tenant application. Multitenant applications must support the sharing of multiple resources by multiple users (e.g., databases, middleware, portals) while maintaining the security of the environment.
Cloud computing has broadened the definition of multitenancy because of the new service models that can take advantage of virtualization and remote access. A SaaS service provider can run an instance of its application on a cloud database and provide web access to multiple customers. Each tenant’s data is isolated and remains invisible to other tenants.
Cloud Bursting
Cloud bursting is the concept of running an application on the organization’s internal computing resources or private cloud and “bursting” that application into a public cloud on demand when the organization runs out of resources on its internal private cloud. Cloud bursting is normally recommended for high-performance, noncritical applications that have nonsensitive data. It allows a company to deploy an application in an internal data center and “burst” to a public cloud to meet peak needs.
When an organization is looking to take advantage of cloud bursting, it needs to consider security and regulatory compliance requirements. An example of when cloud bursting is a good option is in the retail world, where a company might experience a substantial increase in demand during the holiday season. The downside to this is that the retailers could be putting sensitive data into the public cloud and exposing their customers to risk. Figures 1-6 and 1-7 show an example of an application experiencing heavy use and subsequently “bursting” into the public cloud.
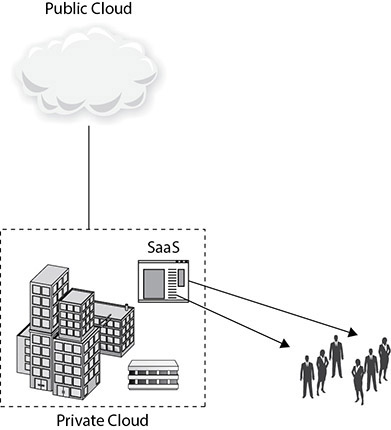
Figure 1-6 Operating within the organization’s internal computing resources (no public cloud needed)
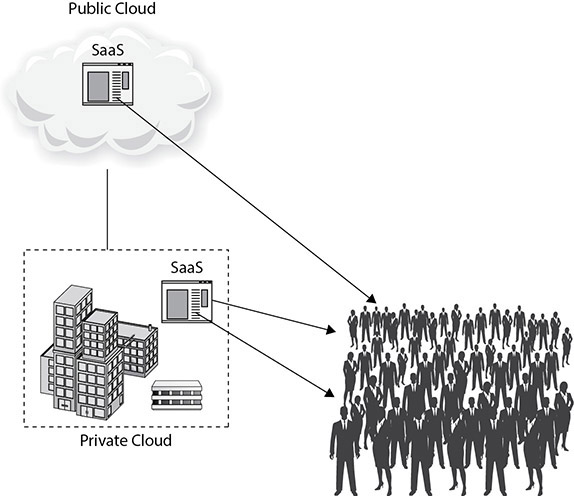
Figure 1-7 Operating after cloud bursting (using the public cloud)
Auto-Scaling Technology
Auto-scaling is the logical next step after cloud bursting for the demand-driven cloud. Cloud consumers can capitalize on the elasticity and orchestration of a CSP by bursting resources to the cloud automatically when necessary. This feature takes the enablement of cloud resources to the next level by provisioning not just more compute resources as necessary for the subscribed set of virtual machines or instances but also provisioning more virtual machines and instances themselves to deliver the performance and availability that the consumer is looking to achieve. Auto-scaling technology can help consumers offset unknown or unexpected spikes in demand without adversely affecting their deliverables.
Baselines
Baselines are the starting point for all measurements to be compared against. A baseline is a recorded state or configuration against which planned changes and performance comparisons can be made. Establishing a baseline is the first step in controlling any environment.
Organizations typically take a baseline of an existing system when migrating it to the cloud. They take another baseline when the system is deployed and under normal load to compare performance metrics between the two baselines and ensure that performance meets the needs of the business and application. Baselines should be taken at different milestones in the cloud life cycle. For example, when a cloud is deployed and is being used by the workforce, conduct a baseline to understand normal activity. However, the system’s usage may grow or shrink over time, and new behavior will be considered normal, thus requiring a new baseline. Similar applications on the same platform should also be baselined and compared against each other to ensure that the organization takes advantage of optimizations that may be in place in one application but not another.
The importance of baselines cannot be overemphasized in cloud operations. Appropriate tools and procedures should be put in place to perform the following functions:
• Evaluate performance
• Ensure user satisfaction
• Fulfill service level agreement requirements
• Demonstrate proof of compliance
The inability to prove compliance may put a company at risk financially, as many contracts specify penalties if the company is unable to demonstrate their fulfillment of the stated requirements.
The following methodology can be used to demonstrate proof of compliance:
1. Establish baselines. Create a baseline measurement of the environment for each area that has defined service levels.
2. Monitor baselines. Establish procedures to regularly and consistently monitor and measure the baseline and to understand the pattern of varying measurements over the course of time, in a process known as trending. The cloud service administrator (CSA) also needs to be alerted to significant deviations from the baseline so that they can restore service to the previously defined baseline state.
3. Make baselines available. Share baselines with customers to provide evidence of SLA compliance.
4. Maintain baseline states. Once the baselines have been established, documented, and contractually agreed upon, it is then the goal of service operations to ensure that they consistently beat baseline performance metrics.
Source and Target Hosts
When moving workloads in a cloud environment, the compute resources that run the workload in the current position are owned by the “source” host. The host that owns the compute resources that an administrator intends to move to is referred to as the “target” host.
Existing Systems
Cloud environments are not usually developed as an entirely new solution running by itself. Workloads are often shared by existing systems and cloud systems to provide continuity. Migration plans are established, and existing systems are slated for removal over time as functionality is slowly migrated to the cloud.
Cloud Elements
The cloud is not made up only of virtual machines and virtualization hosts. Services have been developed that allow consumers to leverage cloud objects such as storage, databases, and applications from disparate CSPs. A wide variety of computing resources are available to cloud consumers through cloud services. These resources can become pieces of a larger system or solution. When utilizing cloud services, application components are called from APIs and are referred to as “target objects.”
This enables a diverse approach to cloud computing and gives consumers more choice on how they can develop the solutions they want to build. As a foundation for understanding cloud computing, it is important to understand how the terms cloud element and target object are used. Cloud elements are the pieces that make up a cloud solution. Some of those pieces could be accessed by cloud consumers and programs, while others are used in support of those resources. When cloud consumers reference cloud elements, those elements are referred to as target objects. For example, when a backup program is pointed to cloud storage to archive it onto another storage medium, the cloud storage is the target object. Table 1-2 shows a number of cloud elements and how they can be a target object. It provides an example of how it would be a target object and chapter references for where you can learn more. Since these are foundational terms, you will learn much more about them as they are used in conveying other important cloud concepts.
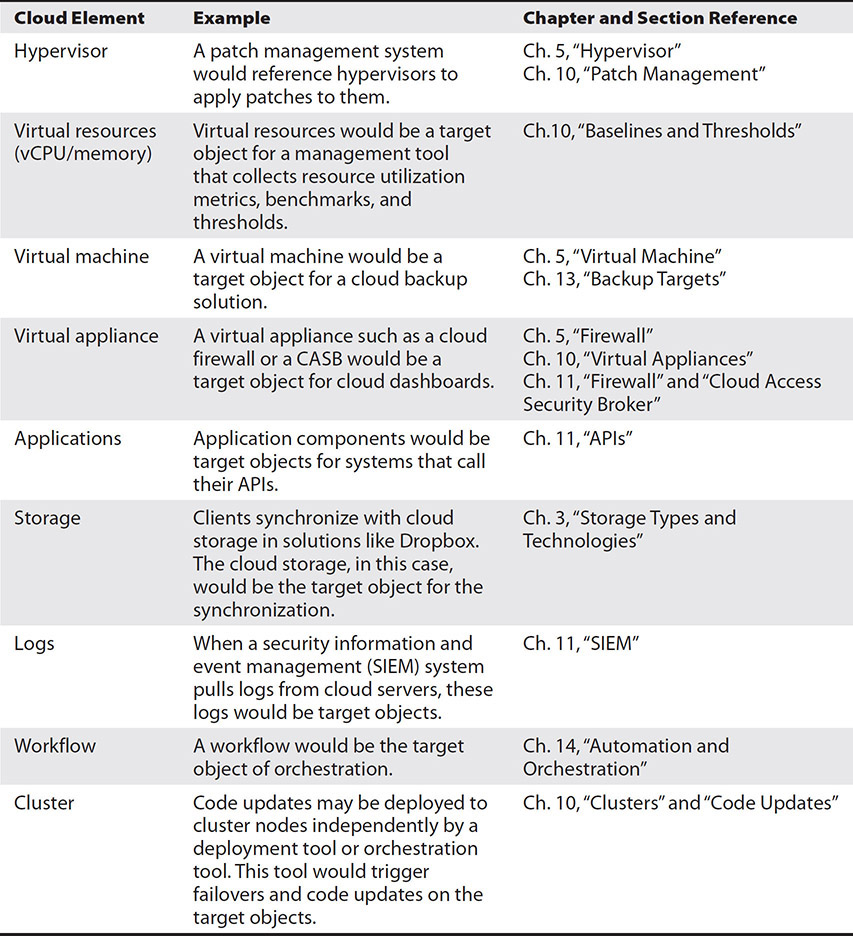
Table 1-2 Cloud Elements and Target Objects
Advanced Cloud Services
The cloud is the platform supporting some of the latest technologies, including Internet of Things (IoT), machine learning, and artificial intelligence. This section introduces both of those concepts, as well as the ability to deploy applications with a serverless architecture.
Machine Learning and Artificial Intelligence
Many companies want to develop services that utilize a level of machine learning (ML) or artificial intelligence (AI). ML is a computer program that can make increasingly better decisions or predictions based on data as it observes more patterns and relationships between the data. For example, the prediction ML in Netflix suggests programs you might be interested in based on programs you have watched before and programs viewed by others who viewed the same or similar programming. Likewise, Amazon uses an ML model to suggest other products that you might like based on previous purchase decisions. ML algorithms go through a process of training where they are given data to learn from. They develop a model from this training that then is applied to larger data sets.
Another method ML uses is reinforcement learning. Reinforcement learning is where a program is given metrics for success and then it uses the tools available to perform millions of iterations, where it attempts to achieve the most optimal solutions.
Similar to ML, AI learns from its interactions with data to make better decisions. However, AI is a broader concept of which ML is a part. AI is concerned with developing computer programs that exhibit learning and problem-solving abilities similar to that of human cognition.
There are huge barriers to creating new ML or AI models and algorithms from scratch. Fortunately, CSPs like Google and Amazon have been pioneers in this space and offer consumers the ability to utilize pretrained and tuned models for their applications. For example, if you want to develop an application that needs to receive speech-based instructions, you can utilize a predeveloped speech AI platform to do that portion of the application. Figure 1-8 shows Google’s AI Hub, where you can select predeveloped AI services.

Figure 1-8 Predeveloped AI services in Google’s AI Hub
Some predeveloped ML/AI solutions include
• Image recognition
• Video analysis
• Personalized recommendations
• Natural language processing (NLP)
• Speech recognition
• Code review
• Forecasting
• Enterprise search
• Anomaly detection
• Language translation
• Transcription
Serverless
Serverless computing uses cloud resources to host an application, and the CSP manages the provision of the system and management of its resources transparently to the cloud consumer. This makes it very fast and easy to develop and deploy applications. The consumer is charged only for the resources they use, and there is no set minimum. Let’s try an exercise.
Exercise 1-1: Creating a Basic Serverless Application on AWS Lambda
In this exercise, we will create a serverless application using AWS Lambda. You will need an AWS account to perform these steps. The application is a simple Hello World application that will run on an AWS server instance, but we will not need to configure the server to run our code. We will also be using some built-in templates to make it simpler.
1. Log in to your AWS account. You will be presented with the management console, which will show the available services you can choose from.
2. Click on Lambda under the All Services/Compute section, and the AWS Lambda functions screen will load.
3. Click Create Function.
4. AWS Lambda gives you some precreated functions that you can use under Blueprints. Click Use A Blueprint and a list of blueprints will appear.
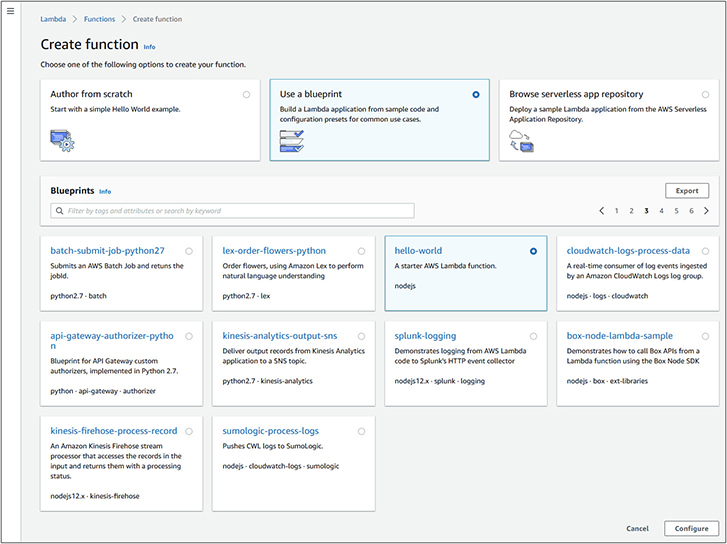
5. Type hello-world in the search box and then press ENTER.
6. Select the hello-world blueprint.
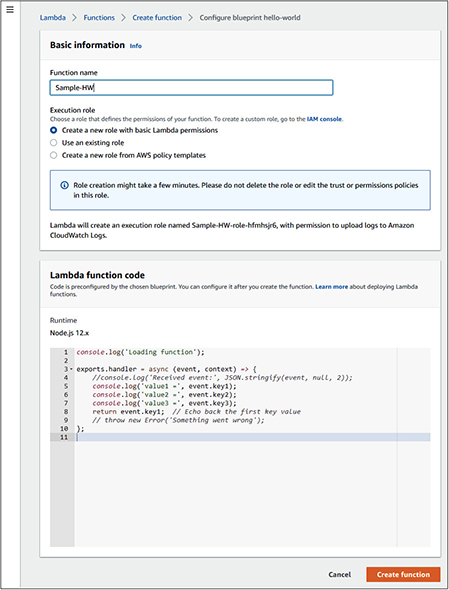
7. The basic information screen will load. Enter a function name and leave the default options selected, as shown next, and then click Create Function.
8. Click the test button in the upper right to display the Configure Test Event screen.
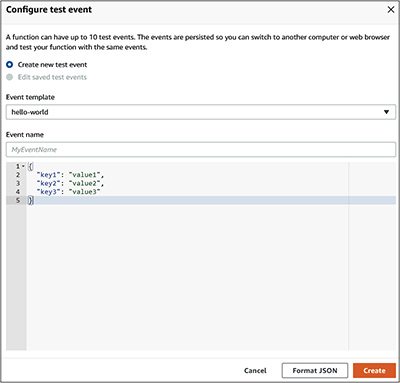
9. Give the event a name and click Create.
10. Click Test again.
11. Expand the execution result details, and it will show the resulting output shown here.
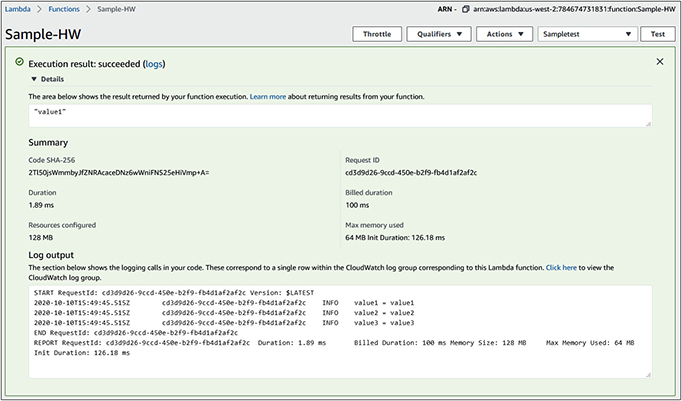
Note that the log output shows the memory that you were billed for to perform the operation. In this case, we were billed for 128MB of memory for 100 milliseconds. Amazon allocated the resources needed for the work and then removed them when we were done. We are only billed for what was actually used.

Internet of Things
The cloud is an ideal way of managing the IoT. IoT refers to devices that are connected to the Internet. The primary purpose of IoT is not computing, but some other task. Some IoT devices include IP cameras, sensors, lights, thermostats, and many other devices. The primary purpose of the IoT camera is to record footage, but it also is connected to the Internet to allow for remote management, footage archiving, and live streaming. Manufacturing uses IoT to embed sensors into equipment so as to better track utilization and determine when maintenance is required. Companies may have digital signage that displays content from the cloud, tracking systems for assets, or sensors to measure heat, humidity, or other things. IoT has also entered the home with smart water heaters, sprinkler systems, light bulbs, thermostats, security systems, and entertainment devices.
IoT can be provisioned quickly when it is cloud-enabled. Out of the box, a device can connect back to a cloud service to report in and then be attached to the customer’s cloud account for ongoing management and operations. This is especially important for sensors or equipment that is distributed around the globe, outside organizational boundaries, or mobile. As long as the IoT has Internet access, it can connect to the CSP to allow for data exchange or management. For example, a water company could deploy IoT sensors at homes so that data can be collected automatically. This saves them the trouble of sending someone out to record the data from each sensor, and they receive the data in real time so they can make better decisions.
Cloud IoT allows for effective global asset management. For example, a car rental company could place sensors on its fleet to track location, speed, or other data. An IoT cloud platform would allow the devices to be managed wherever the customer drives them. Furthermore, because cloud resources are distributed across the globe, a company can manage systems centrally but communicate with IoT devices close to the device to reduce latency for high-speed or real-time processing of data that would not be possible if distributed systems were tied directly to a central hub.
Lastly, IoT cloud platforms make it easy for consumers to take the data from IoT devices and analyze that data with other cloud services. It can be hard to collect and analyze data from devices when they are managed on-premises, but cloud systems can be easily scaled or the data can be ported from one system to another with standard APIs for ease of management and analysis. Suppose the company wants to integrate the data with another service. In that case, it is as simple as connecting the new service to the existing platform API.
Chapter Review
The cloud offers multiple ways for consumers to deploy and manage applications with varying levels of complexity. It also allows consumers to reduce their security and compliance burden by sharing it with the CSP. Understanding the similarities and differences between the cloud models is key to understanding which one meets the business needs of the application or service you want to provide. It is equally important to grasp how the cloud can benefit an organization. Cloud computing also makes it easy for customers to integrate IoT systems into their cloud infrastructure or deploy ML or AI solutions. Cloud computing is a growing industry, and IT professionals are going to be required to grow with it.
Questions
The following questions will help you gauge your understanding of the material in this chapter. Read all the answers carefully because there might be more than one correct answer. Choose the best response(s) for each question.
1. Which of the following would be considered an example of IaaS?
A. Providing productivity software for use over the Internet
B. A multiuser program that is hosted by a third party
C. Providing hardware resources over the Internet
D. A database that is hosted in the cloud
2. Which term is used to define the increasing number of services delivered over the Internet?
A. XaaS
B. CaaS
C. MaaS
D. C-MaaS
3. Voice over IP (VoIP) is an example of what type of cloud service?
A. IaaS
B. PaaS
C. MaaS
D. CaaS
4. Which of the following cloud solutions provides only hardware and network resources to make up a cloud environment?
A. SaaS
B. CaaS
C. PaaS
D. IaaS
5. Which of the following would give developers a place to build applications and services over the Internet?
A. IaaS
B. SaaS
C. PaaS
D. Virtual machines
6. What type of computing solution would be defined as a platform that is implemented within the corporate firewall and is under the control of the IT department?
A. Private cloud
B. Public cloud
C. VLAN
D. VPN
7. A cloud deployment has been created explicitly for the finance department. What type of cloud deployment would this be defined as?
A. Public cloud
B. Hybrid cloud
C. Community cloud
D. Private cloud
8. Which of the following statements would be used to explain a private cloud but not a public cloud?
A. Used as a service via the Internet
B. Dedicated to a single organization
C. Requires users to pay a monthly fee to access services
D. Provides incremental scalability
9. Which of the following statements is a benefit of a hybrid cloud?
A. Data security management
B. Requirement of a major financial investment
C. Dependency of internal IT department
D. Complex networking
10. Which of the following would be considered an advantage of cloud computing?
A. Increased security
B. Ability to scale to meet growing usage demands
C. Ease of integrating equipment hosted in other data centers
D. Increased privacy for corporate data
11. Which statement defines chargeback?
A. The recovery of costs from consumers of cloud services
B. The process of identifying costs and assigning them to specific cost categories
C. A method of ensuring that cloud computing becomes a profit instead of a cost
D. A system for confirming that billing occurs for the cloud services being used
12. When you run out of compute resources in your internal data center and expand to an external cloud on demand, this is an example of what?
A. SaaS
B. Hybrid cloud
C. Cloud bursting
D. Elasticity
13. A company wants to deploy a private cloud but does not want to invest in the infrastructure associated with a private cloud. Which solution should they consider?
A. Hybrid cloud
B. Cloud within a cloud
C. Community cloud
D. On-premises hosting
14. Given the shared responsibility model, under which of the following services models would the CSP only be responsible for the directory infrastructure?
A. SaaS
B. PaaS
C. IaaS
D. All of the above
Answers
1. C. Providing hardware resources over the Internet is an example of IaaS. Infrastructure as a Service (IaaS) is a cloud service model that offers server storage, infrastructure, and connectivity domains to a cloud consumer.
2. A. XaaS is a collective term that means “Anything as a Service” (or “Everything as a Service”).
3. D. Voice over IP is an example of Communications as a Service (CaaS) because it is a cloud-based phone system, which is a form of communications.
4. D. In a cloud service model, IaaS providers offer computers and other hardware resources. Organizations would outsource the equipment needed to support their business.
5. C. PaaS provides a platform that an organization can use to build their applications and services on. These systems can then be accessed over the Internet. PaaS is hosted in the cloud and accessed with a web browser.
6. A. A private cloud is a cloud computing solution that is implemented behind a corporate firewall and is under the control of the internal IT department.
7. C. A community cloud is a cloud solution that provides services to a specific or limited number of individuals who share a common computing need.
8. B. A private cloud is dedicated to a single organization and is contained with the corporate firewall.
9. A. A hybrid cloud offers the ability to keep the organization’s mission-critical data behind a firewall and outside of the public cloud.
10. B. One of the benefits of cloud computing is the ability to easily scale and add resources to meet the growth of the organization.
11. A. The purpose of a chargeback system is to measure the costs of IT services, hardware, or software and recover them from the business unit or cloud consumer that used them.
12. C. Cloud bursting allows you to add resources from an external cloud on an on-demand basis. The internal resource is the private cloud, and the external resource is the public cloud.
13. B. Cloud within a cloud offers the flexibility of a private cloud without the investment and operational cost of the infrastructure.
14. C. Under IaaS, the CSP is responsible for everything except data, end-user systems, and user and service account management.