How Stored Procedure Attacks Work
As you would hope from a security perspective, stored procedures are not always available for attackers to use right out of the box. For example, SQL Server may not have stored procedures available for you to utilize (an administrator may have removed them or they may be disabled by default), and it does require you to have appropriate permissions when accessing these procedures. Certain conditions, therefore, may need to exist before initiating an attack utilizing SQL's stored procedures.
Initiating Access
The first step in the attack methodology is to obtain access to accounts or applications with proper permissions to interact with the stored procedures. A common SQL Server account that is fruitful for attackers to gain access to and leverage is the prebuilt administrator account that is named System Administrator or “sa” by default. This account is created as part of the initial installation for SQL Server; however, any account with appropriate permissions will do.
alt1 Warning
“sa” is the legacy account that acts as an administrator-level account for managing SQL Server tasks and also provides full control over the database instance and its data. The “sysadmin” fixed server role is designed to provide accounts assigned to the role full control over all aspects of the SQL Server instance it is a part of. By default, the sa account is assigned to the sysadmin role, making it a prime target for attackers.
Access to a valid account can be accomplished through several methods depending on the access an attacker already has to the network or the database instance. One of the most common methods for gaining access to a sysadmin fixed server role account is to perform password guessing or dictionary attacks against the default sa account. All too often, administrators fail to configure accounts with strong passwords (or any password at all for that matter). Depending on what version of SQL Server is implemented and what password policies are implemented, account lockouts may or may not be enabled to limit these attacks. Finally, DBAs may have turned off auditing for failed logon attempts because of “performance” reasons or the events are created, but there is no monitoring of the logs. This type of configuration will allow attackers to conduct password attacks against the SQL Server that may go unnoticed.
In SQL Server 2008, the sa account is present whether mixed mode authentication or Windows authentication is selected as the authentication mode. However, in the case of Windows authentication mode, the sa account is left disabled. In order to ensure compatibility with legacy applications and database interaction, many administrators will configure servers to use mixed mode authentication and enable the sa account.
In SQL Server 2005 and 2008, administrators are forced to provide a password for the account; however, this was not the case with earlier versions. After the initial configuration of these early versions, sysadmins are able to set a password with a null value. In a security-conscious world, the ability to leave the password blank wouldn't be a big deal, because anybody who cares about security would never set it that way. Unfortunately, in most cases, it is actually DBAs who handle the security within an SQL Server, and that means it is possible that the convenience of a blank password will trump security (this situation almost always means that performance trumps security, which has its own implications).
Accessing Stored Procedures
Once an attacker has administrative control over the SQL Server instance, attacks can be leveraged against the stored procedures implemented on the server. Stored procedures come in different flavors and provide different functionalities. For Microsoft's SQL Server, three main categories of stored procedures exist:
- User-defined stored procedures are implemented to maximize code reuse and user-defined operations via Transact-SQL (T-SQL) statements or using the .NET framework Common Language Runtime (CLR).
- Extended stored procedures allow database developers to create reusable code in languages such as C. This is a legacy method and will be removed at some point in the future.[B]
- System-stored procedures provide administrative interfaces for some of the administrative management of the SQL Server instance.
Bhttp://msdn.microsoft.com/en-us/library/ms164716.aspx
Accessibility of stored procedures will depend on the version of SQL Server installed and the configuration of the server. In the last several versions of SQL Server, Microsoft has slowly implemented controls and configuration changes to the default implementation of SQL Server in an attempt to reduce the exploitation of some of the more well-known vulnerabilities associated with SQL Server.
alt1 Tip
The sqlcmd utility is new as of SQL Server 2005 and provides additional features and options as compared to the osql utility. In some cases, the osql utility may not be compatible with all of the features found in SQL Server 2005 and 2008. Microsoft recommends using the sqlcmd utility to ensure compatibility with the new features found in these versions. In this chapter, we will be using the sqlcmdC utility for our examples, as many of the commands are identical in comparison to the legacy osql utility.D
C Usage information for the sqlcmd utility can be found at http://msdn.microsoft.com/en-us/library/ms162773.aspx
D For information on using the osql utility reference the MSDN pages located at http://msdn.microsoft.com/en-us/library/aa214012(SQL.80).aspx
Executing stored procedures interactively using the sqlcmd utility is a fairly straightforward task. Once a valid account is obtained, an administrator may use the sqlcmd utility to connect to the SQL Server and execute command to access data or perform functions. Successful connection to the SQL Server with the sqlcmd utility will enable you to execute commands in a command-line environment.
Depending on the SQL Server version and the implemented configuration, stored procedures may or may not be enabled. Figure 3.1 provides an example of an administrator connecting to the SQL Server and attempting to leverage the functionality of the xp_cmdshell extended stored procedure. The initial error message indicates that the requested stored procedure is disabled and the administrator is not able to successfully complete the command as requested; however, if the stored procedure has not been fully removed, the administrator can reenable the stored procedure with a few simple commands, assuming that the administrator has appropriate permissions to do so.
FIGURE 3.1. Enabling xp_cmdshell Stored Procedure
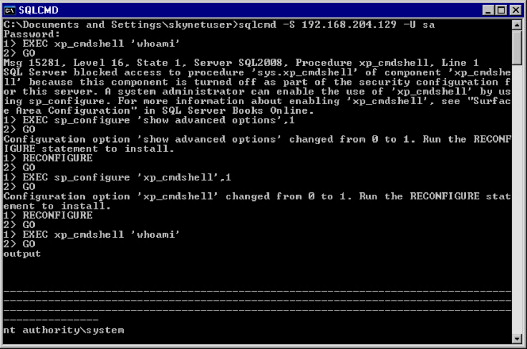
The database engine stored procedure “sp_configure” allows configuration of many options globally on the SQL Server instance. Using sp_configure to reenable the stored procedure will allow the administrator to continue on with the task at hand.
1>EXEC sp_configure 'show advanced options',1
