A TCP connection usually goes through a series of states during its lifetime. The state signifies the status of the TCP connection. In order to determine the connection state, execute the netstat command:
$ sudo netstat --tcp --all --numeric Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:3306 0.0.0.0:* LISTEN tcp 0 0 0.0.0.0:139 0.0.0.0:* LISTEN tcp 0 0 192.168.2.111:39551 182.19.89.106:80 ESTABLISHED tcp 396 0 192.168.2.111:18358 173.194.36.70:443 TIME_WAIT tcp 0 0 127.0.0.1:80 127.0.0.1:48234 TIME_WAIT
The states can contain any of the following values:
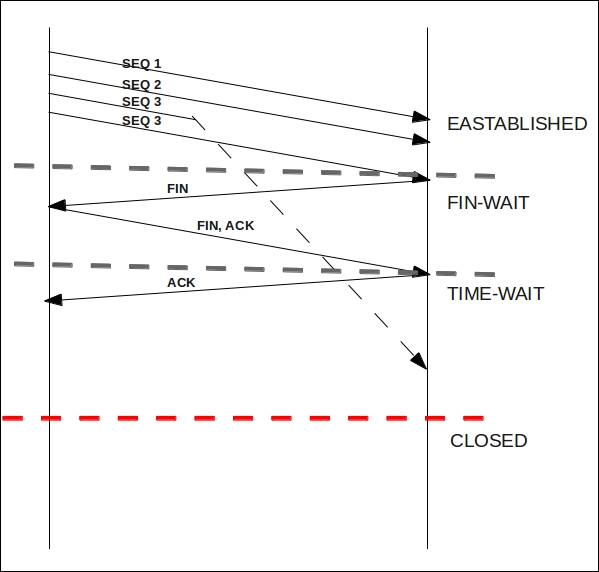
LISTEN: This indicates that the socket is ready for incoming connectionsSYN_SENT: This indicates that the socket is attempting to establish a connectionSYN_RECV: This indicates that the server has received a connection requestESTABLISHED: This indicates that the server has established a connectionLAST_ACK: This indicates that the server is waiting for ACK as the socket is closedCLOSE_WAIT: This indicates that the server is waiting for the socket to close as the client has closed the connectionTIME_WAIT: This indicates that the server has closed the socket but is waiting for packets in the networkFIN_WAIT1: This indicates that the connection is shutting down as the socket is closedFIN_WAIT2: This indicates that the connection is closed and the socket is waiting for shutdown from clientCLOSED: This indicates that the socket is not being used
When a TCP connection closes, the connection moves to the TIME_WAIT state. The connection remains in this state for a long period of time, usually twice the maximum segment life (msl). The reason for waiting is that packets may arrive out of order or be retransmitted after the connection has been closed. Thus, the connection is being kept around so that these delayed packets can be handled appropriately.
The long TIME_WAIT state results in the memory and ports getting blocked by closed connections. Thus, a heavily loaded server can run out of resources, which can be caused by a large number of connections in the TIME_WAIT state.
The default MSL is 60 seconds, thus making the TIME_WAIT state last for 2 minutes for each closed socket. The MSL can be listed for the net.ipv4.tcp_fin_timeout key:
$ sysctl net.ipv4.tcp_fin_timeout net.ipv4.tcp_fin_timeout = 60
To make the TIME_WAIT state last for 40 seconds, decrease the value of net.ipv4.tcp_fin_timeout to 20 seconds:
$ sudo sysctl -w net.ipv4.tcp_fin_timeout = 20 net.ipv4.tcp_fin_timeout = 20
Another way of improving the utilization of TCP sockets is to configure the TCP behavior using tcp_tw_reuse. The property allows TCP to reuse the TIME_WAIT socket when it is safe from the protocol viewpoint. The configuration is disabled by default; enable it by setting the net.ipv4.tcp_rw_reuse key:
$ sysctl net.ipv4.tcp_tw_reuse net.ipv4.tcp_tw_reuse = 0 $ sudo sysctl -w net.ipv4.tcp_tw_reuse = 1 net.ipv4.tcp_tw_reuse = 1
Note
The kernel also presents the tcp_tw_recycle option as an alternative to tcp_tw_reuse. The tcp_tw_recycle option is a more aggressive version of tcp_tw_reuse and enables fast recycling of TIME_WAIT connections:
$ sysctl net.ipv4.tcp_tw_recycle net.ipv4.tcp_tw_recycle = 0
It is not recommended that you enable this option as the kernel makes assumptions before determining whether to reuse a socket. These assumptions can pose problems when working with a NAT, stateful firewall.
