Chapter 11. It’s a Network
Objectives
Upon completion of this chapter, you will be able to answer the following questions:
![]() What are the devices and protocols used in a small network?
What are the devices and protocols used in a small network?
![]() How does a small network serve as the basis of larger networks?
How does a small network serve as the basis of larger networks?
![]() Why are basic security measures needed on network devices?
Why are basic security measures needed on network devices?
![]() What are security vulnerabilities and general mitigation techniques?
What are security vulnerabilities and general mitigation techniques?
![]() How do you configure network devices with device-hardening features to mitigate security threats?
How do you configure network devices with device-hardening features to mitigate security threats?
![]() How do you use the output of the ping and tracert commands to establish relative network performance?
How do you use the output of the ping and tracert commands to establish relative network performance?
![]() How do you use the basic show commands to verify the configuration and status of a device interface?
How do you use the basic show commands to verify the configuration and status of a device interface?
![]() Which file systems are present on routers and switches?
Which file systems are present on routers and switches?
![]() How do you apply the commands to back up and restore an IOS configuration file?
How do you apply the commands to back up and restore an IOS configuration file?
Key Terms
This chapter uses the following key terms. You can find the definitions in the Glossary.
operating system features and services page 550
Real-Time Transport Protocol (RTP) page 557
Real-Time Transport Control Protocol (RTCP) page 557
data loss/manipulation page 560
disruption of service page 560
reconnaissance attacks page 565
denial of service attacks page 565
appliance-based firewalls page 570
server-based firewalls page 570
Introduction (11.0.1.1)
Up to this point in the course, we have considered the services that a data network can provide to the human network, examined the features of each layer of the OSI model and the operations of TCP/IP protocols, and looked in detail at Ethernet, a universal LAN technology. The next step is to learn how to assemble these elements in a functioning network that can be maintained.
Class Activity 11.0.1.2: Did You Notice?
In this activity you will compare and contrast two different networks.
Note
Students can work singularly, in pairs, or in a full-classroom learning environment.
Go to the online course to perform the network compare and contrast practice activity.
Create and Grow (11.1)
This section takes a look at devices and protocols used in a small network, and what it takes to grow from a smaller to a larger network.
Devices in a Small Network (11.1.1)
Let’s start by examining the different devices in a small network and how they are connected.
Small Network Topologies (11.1.1.1)
The majority of businesses are small businesses. It is not surprising then that the majority of networks are small networks.
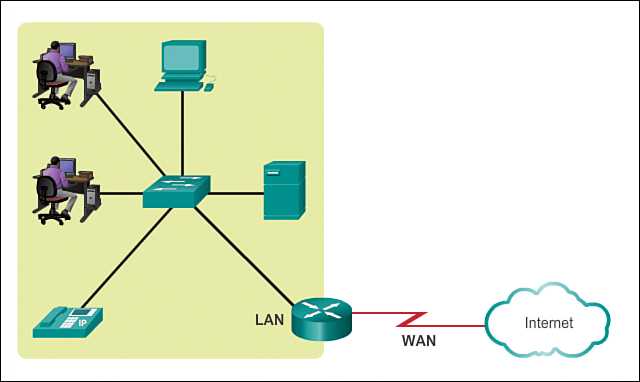
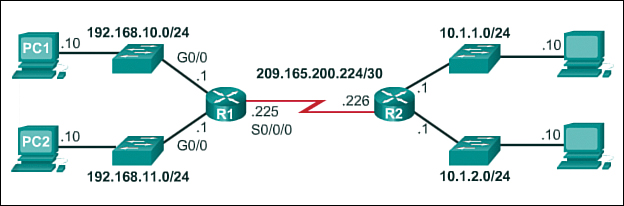
With small networks, the design of the network is usually simple. The number and types of devices on the network are significantly reduced compared to that of a larger network, as shown in Figure 11-1. The network topologies for small networks typically involve a single router and one or more switches. Small networks may also have wireless access points (possibly built into the router) and IP phones. As for connection to the Internet, normally a small network has a single WAN connection provided by DSL, cable, or an Ethernet connection.
Managing a small network requires many of the same skills as those required for managing a larger one. The majority of work is focused on maintenance and troubleshooting of existing equipment, as well as securing devices and information on the network. The management of a small network is done either by an employee of the company or by a person contracted by the company, depending on the size of the business and the type of business.
Device Selection for a Small Network (11.1.1.2)
In order to meet user requirements, even small networks require planning and design. Planning ensures that all requirements, cost factors, and deployment options are given due consideration.
One of the first design considerations when implementing a small network is the type of intermediate devices to use to support the network. When selecting the type of intermediate devices, there are a number of factors that need to be considered, as shown in Figure 11-2.
Cost
Cost is typically one of the most important factors when selecting equipment for a small business network. The cost of a switch or router is determined by its capacity and features. The device capacity includes the number and types of ports available and the backplane speed. Other factors that affect the cost are network management capabilities, embedded security technologies, and optional advanced switching technologies. The expense of cable runs required to connect every device on the network must also be considered. Another key element affecting cost consideration is how much redundancy to incorporate into the network—this includes devices, ports per device, and copper or fiber-optic cabling.
Speed and Types of Ports/Interfaces
Choosing the number and types of ports on a router or switch is a critical decision. Questions to be asked include
![]() Do we order just enough ports for today’s needs, or do we consider growth requirements?
Do we order just enough ports for today’s needs, or do we consider growth requirements?
![]() Do we require a mixture of UTP speeds?
Do we require a mixture of UTP speeds?
![]() Do we require both UTP and fiber ports?
Do we require both UTP and fiber ports?
Newer computers have built-in 1-Gbps NICs. 10-Gbps ports are already included with some workstations and servers. Although it is more expensive, choosing Layer 2 devices that can accommodate increased speeds makes it possible for the network to evolve without replacing central devices.
Expandability
Networking devices come in both fixed and modular physical configurations. Fixed configurations have a specific number and type of ports or interfaces, making them a poor choice for expandability of the network. Modular devices have expansion slots that provide the flexibility to add new modules as requirements evolve. Most modular devices come with a basic number of fixed ports and expansion slots. Switches are available with special additional ports for optional high-speed uplinks. Also, because routers can be used for connecting different numbers and types of networks, care must be taken to select the appropriate modules and interfaces for the specific media. Questions to be considered include
![]() Do we order devices with upgradable modules?
Do we order devices with upgradable modules?
![]() What type of WAN interfaces, if any, are required on the router(s)?
What type of WAN interfaces, if any, are required on the router(s)?
Operating System Features and Services
Depending on the version of the operating system, a network device can support certain operating system features and services, such as
![]() Security
Security
![]() Quality of service (QoS)
Quality of service (QoS)
![]() Voice over IP (VoIP)
Voice over IP (VoIP)
![]() Layer 3 switching
Layer 3 switching
![]() Network address translation (NAT)
Network address translation (NAT)
![]() Dynamic Host Control Protocol (DHCP)
Dynamic Host Control Protocol (DHCP)
Routers can be expensive, depending on the interfaces and features needed. Additional modules, such as fiber optics, increase the cost of the network devices.
IP Addressing for a Small Network (11.1.1.3)
When implementing a small network, it is necessary to plan the IP addressing space. All hosts within an internetwork must have a unique address. Even on a small network, address assignment within the network should not be random. Rather, the IP addressing scheme should be planned, documented, and maintained based on the type of device receiving the address.
Examples of different types of devices that will factor into the IP design are
![]() End devices for users
End devices for users
![]() Servers and peripherals
Servers and peripherals
![]() Hosts that are accessible from the Internet
Hosts that are accessible from the Internet
![]() Intermediary devices
Intermediary devices
Planning and documenting the IP addressing scheme helps the administrator to track device types. For example, if all servers are assigned a host address in the range 50 to 100, it is easy to identify server traffic by IP address. This can be very useful when troubleshooting network traffic issues using a protocol analyzer.
Additionally, administrators are better able to control access to resources on the network based on IP address when a deterministic IP addressing scheme is used. This can be especially important for hosts that provide resources both to the internal network and to the external network. Web servers or e-commerce servers play such a role. If the addresses for these resources are not planned and documented, the security and accessibility of the devices are not easily controlled. If a server has a random address assigned, blocking access to this address is difficult and clients may not be able to locate this resource.
Each of these different device types should be allocated to a logical block of addresses within the address range of the network.
Click the buttons in Activity 11.1.1.3 to see the method for assignment.

Activity 11.1.1.3: IPv4 Address Planning and Assignment
Go to the online course and click through the buttons in the figure to see the method for IPv4 address planning and assignment.
Redundancy in a Small Network (11.1.1.4)
Another important part of network design is reliability. Even small businesses often rely on their network heavily for business operation. A failure of the network can be very costly. To maintain a high degree of reliability, redundancy is required in the network design. Redundancy helps to eliminate single points of failure. There are many ways to accomplish redundancy in a network. Redundancy can be accomplished by installing duplicate equipment, but it can also be accomplished by supplying duplicate network links for critical areas, as shown in Activity 11.1.1.4.
Activity 11.1.1.4: Redundancy to a Server Farm
Go to the online course and click the blue-highlighted devices and connections for additional information.
The smaller the network, the less the chance that redundancy of equipment will be affordable. Therefore, a common way to introduce redundancy is through the use of redundant switch connections between multiple switches on the network and between switches and routers.
Also, servers often have multiple NIC ports that enable redundant connections to one or more switches. In a small network, servers typically are deployed as web servers, file servers, or email servers.
Small networks typically provide a single exit point toward the Internet via one or more default gateways. With one router in the topology, the only redundancy in terms of Layer 3 paths is enabled by utilizing more than one inside Ethernet interface on the router. However, if the router fails, the entire network loses connectivity to the Internet. For this reason, it may be advisable for a small business to pay for a least-cost option account with a second service provider for backup.
Design Considerations for a Small Network (11.1.1.5)
Users expect immediate access to their emails and to the files that they are sharing or updating. To help ensure this availability, the network designer should take the following steps:
Step 1. Secure file and mail servers in a centralized location.
Step 2. Protect the location from unauthorized access by implementing physical and logical security measures.
Step 3. Create redundancy in the server farm that ensures if one device fails, files are not lost.
Step 4. Configure redundant paths to the servers.
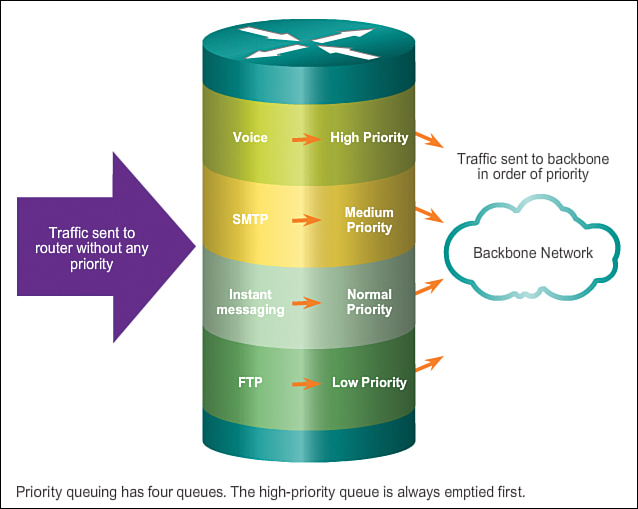
In addition, modern networks often use some form of voice or video over IP for communication with customers and business partners. This type of converged network is implemented as an integrated solution or as an additional form of raw data overlaid onto the IP network. The network administrator should consider the various types of traffic and their treatment in the network design. The router(s) and switch(es) in a small network should be configured to support real-time traffic, such as voice and video, in a distinct manner relative to other data traffic. In fact, a good network design will classify traffic carefully according to priority, as shown in Figure 11-3. Traffic classes could be as specific as
![]() Email
Email
![]() Voice
Voice
![]() Video
Video
![]() Messaging
Messaging
![]() Transactional
Transactional
In the end, the goal for a good network design, even for a small network, is to enhance productivity of the employees and minimize network downtime.

Activity 11.1.1.6: Network Planning and Design
Go to the online course and perform the drag-and-drop exercise.
Protocols in a Small Network (11.1.2)
Several protocols are utilized in small networks, as described in this section.
Common Applications in a Small Network (11.1.2.1)
The network is only as useful as the applications that are on it. As shown in Figure 11-4, within the application layer, there are two forms of software programs or processes that provide access to the network: network applications and application layer services.
Network Applications
Network applications are the software programs used to communicate over the network. Some end-user applications are network-aware, meaning that they implement application layer protocols and are able to communicate directly with the lower layers of the protocol stack. Email clients and web browsers are examples of this type of application.
Application Layer Services
Other programs may need the assistance of application layer services to use network resources, such as file transfer or network print spooling. Though transparent to an employee, these services are the programs that interface with the network and prepare the data for transfer. Different types of data, whether text, graphics, or video, require different network services to ensure that they are properly prepared for processing by the functions occurring at the lower layers of the OSI model.
Each application or network service uses protocols, which define the standards and data formats to be used. Without protocols, the data network would not have a common way to format and direct data. In order to understand the function of various network services, it is necessary to become familiar with the underlying protocols that govern their operation.
Common Protocols in a Small Network (11.1.2.2)
Most of a technician’s work, in either a small network or a large network, will in some way be involved with network protocols. Network protocols support the applications and services used by employees in a small network. Common network protocols include
![]() DNS
DNS
![]() Telnet
Telnet
![]() IMAP, SMTP, POP (email)
IMAP, SMTP, POP (email)
![]() DHCP
DHCP
![]() HTTP
HTTP
![]() FTP
FTP
Click the servers in the figure in Activity 11.1.2.2 for a brief description of the network services each provides.

Activity 11.1.2.2: Network Services
Go to the online course and click each server for a brief description of network services provided.
These network protocols comprise the fundamental tool set of a network professional. Each of these network protocols defines
![]() Processes on either end of a communication session
Processes on either end of a communication session
![]() Types of messages
Types of messages
![]() Syntax of the messages
Syntax of the messages
![]() Meaning of informational fields
Meaning of informational fields
![]() How messages are sent and the expected response
How messages are sent and the expected response
![]() Interaction with the next lower layer
Interaction with the next lower layer
Many companies have established a policy of using secure versions of HTTP, FTP, and Telnet protocols whenever possible. These protocols are HTTPS, SFTP, and SSH.
Real-Time Applications for a Small Network (11.1.2.3)
In addition to the common network protocols described previously, modern businesses, even small ones, typically utilize real-time applications for communicating with customers and business partners. Although a small company may not be able to justify the cost of an enterprise Cisco TelePresence solution, there are other real-time applications that are affordable and justifiable for small business organizations. Real-time applications require more planning and dedicated services (relative to other types of data) to ensure priority delivery of voice and video traffic. This means that the network administrator must ensure that the proper equipment is installed in the network and that the network devices are configured to ensure priority delivery. Figure 11-5 shows elements of a small network that support real-time applications.
Infrastructure
To support the existing and proposed real-time applications, the infrastructure must accommodate the characteristics of each type of traffic. The network designer must determine whether the existing switches and cabling can support the traffic that will be added to the network. Cabling that can support gigabit transmissions should be able to carry the traffic generated and not require any changes to the infrastructure. Older switches may not support Power over Ethernet (PoE). Obsolete cabling may not support the bandwidth requirements. The switches and cabling would need to be upgraded to support these applications.
VoIP
Voice over IP (VoIP) is implemented in organizations that still use traditional telephones. VoIP uses voice-enabled routers. These routers convert analog voice from traditional telephone signals into IP packets. After the signals are converted into IP packets, the router sends those packets between corresponding locations. VoIP is much less expensive than an integrated IP telephony solution, but the quality of communications does not meet the same standards. Voice and video over IP solutions for small businesses can be realized, for example, with Skype and non-enterprise versions of Cisco WebEx.
IP Telephony
In IP telephony, the IP phone itself performs voice-to-IP conversion. Voice-enabled routers are not required within a network with an integrated IP telephony solution. IP phones use a dedicated server for call control and signaling. There are now many vendors with dedicated IP telephony solutions for small networks.
Real-time Applications
To transport streaming media effectively, the network must be able to support applications that require delay-sensitive delivery. Real-Time Transport Protocol (RTP) and Real-Time Transport Control Protocol (RTCP) are two protocols that support this requirement. RTP and RTCP enable control and scalability of the network resources by allowing QoS mechanisms to be incorporated. These QoS mechanisms provide valuable tools for minimizing latency issues for real-time streaming applications.
Growing to Larger Networks (11.1.3)
Growth is a natural process for many small businesses, and their networks must grow accordingly. A network administrator for a small network will work either reactively or proactively, depending on the leaders of the company, which often include the network administrator. Ideally, the network administrator has enough lead time to make intelligent decisions about growing the network in line with the growth of the company.
Scaling a Small Network (11.1.3.1)
To scale a network, several elements are required:
![]() Network documentation: Physical and logical topology
Network documentation: Physical and logical topology
![]() Device inventory: List of devices that use or comprise the network
Device inventory: List of devices that use or comprise the network
![]() Budget: Itemized IT budget, including fiscal year equipment purchasing budget
Budget: Itemized IT budget, including fiscal year equipment purchasing budget
![]() Traffic analysis: Documentation of protocols, applications, and services and their respective traffic requirements
Traffic analysis: Documentation of protocols, applications, and services and their respective traffic requirements
These elements are used to inform the decision making that accompanies the scaling of a small network.
Protocol Analysis of a Small Network (11.1.3.2)
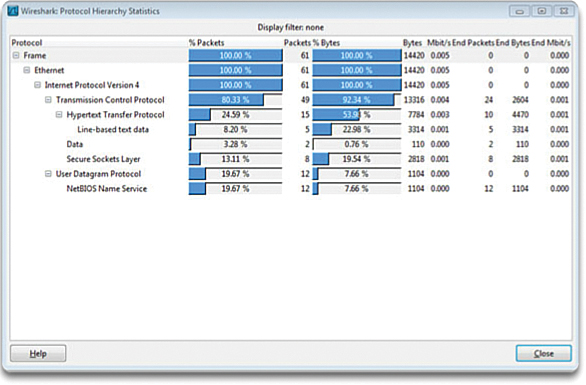
Supporting and growing a small network requires being familiar with the protocols and network applications running over the network. Although the network administrator will have more time in a small network environment to individually analyze network utilization for each network-enabled device, a more holistic approach with some type of software- or hardware-based protocol analyzer is recommended.
As shown in Figure 11-6, protocol analyzers enable a network professional to quickly compile statistical information about traffic flows on a network.
When trying to determine how to manage network traffic, especially as the network grows, it is important to understand the type of traffic that is crossing the network as well as the current traffic flow. If the types of traffic are unknown, the protocol analyzer will help identify the traffic and its source.
To determine traffic flow patterns, it is important to do the following:
![]() Capture traffic during peak utilization times to get a good representation of the different traffic types.
Capture traffic during peak utilization times to get a good representation of the different traffic types.
![]() Perform the capture on different network segments because some traffic will be local to a particular segment.
Perform the capture on different network segments because some traffic will be local to a particular segment.
Information gathered by the protocol analyzer is analyzed based on the source and destination of the traffic as well as the type of traffic being sent. This analysis can be used to make decisions on how to manage the traffic more efficiently. This can be done by reducing unnecessary traffic flows or changing flow patterns altogether by moving a server, for example.
Sometimes, simply relocating a server or service to another network segment improves network performance and accommodates the growing traffic needs. At other times, optimizing the network performance requires major network redesign and intervention.
Evolving Protocol Requirements (11.1.3.3)
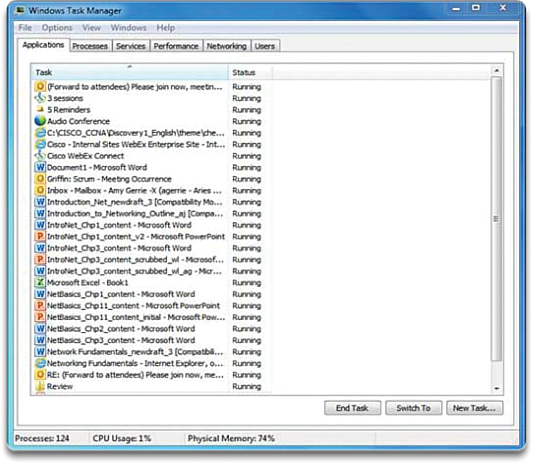
In addition to understanding changing traffic trends, a network administrator must also be aware of how network use is changing. As shown in Activity 11.1.3.3, a network administrator in a small network has the ability to obtain in-person IT “snapshots” of employee application utilization for a significant portion of the employee workforce over time.

Activity 11.1.3.3: Software Processes
Go to the online course and click each process button for examples of processes running in the Windows operating system.
These snapshots typically include information such as
![]() OS and OS version
OS and OS version
![]() Non-network applications
Non-network applications
![]() Network applications
Network applications
![]() CPU utilization
CPU utilization
![]() Drive utilization
Drive utilization
![]() RAM utilization
RAM utilization
Documenting snapshots for employees in a small network over a period of time will go a long way toward informing the network administrator of evolving protocol requirements and associated traffic flows. For example, it may be that some employees are using offsite resources such as social media in order to better position a company with respect to marketing. When they began working for the company, these employees may have focused less on Internet-based advertising. This shift in resource utilization may require the network administrator to shift network resource allocations accordingly.
It is the responsibility of the network administrator to track network utilization and traffic flow requirements, and implement network modifications in order to optimize employee productivity as the network and business grow.
Keeping the Network Safe (11.2)
![]()
Lesson 1: Securing Device Access
Keeping the network safe involves many aspects. This section looks at network device security measures; vulnerabilities and network attacks and how to mitigate them; and how to secure devices.
Network Device Security Measures (11.2.1)
This section looks at some of the categories of security threats as well as the concern of physical security and security vulnerabilities.
Categories of Threats to Network Security (11.2.1.1)
Whether wired or wireless, computer networks are essential to everyday activities. Individuals and organizations alike depend on their computers and networks. Intrusion by an unauthorized person can result in costly network outages and loss of work. Attacks to a network can be devastating and can result in a loss of time and money due to damage or theft of important information or assets.
Intruders can gain access to a network through software vulnerabilities, through hardware attacks, or by guessing someone’s username and password. Intruders who gain access by modifying software or exploiting software vulnerabilities are often called hackers.
After the hacker gains access to the network, four types of threats may arise:
![]() Information theft: Breaking into a computer to obtain confidential information
Information theft: Breaking into a computer to obtain confidential information
![]() Identity theft: A form of information theft where personal information is stolen for the purpose of taking over someone’s identity
Identity theft: A form of information theft where personal information is stolen for the purpose of taking over someone’s identity
![]() Data loss/manipulation: Breaking into a computer to destroy or alter data records
Data loss/manipulation: Breaking into a computer to destroy or alter data records
![]() Disruption of service: Preventing legitimate users from accessing services to which they should be entitled.
Disruption of service: Preventing legitimate users from accessing services to which they should be entitled.
Click the images in Activity 11.2.1.1 to see more information.
Activity 11.2.1.1: Categories of Threats
Go to the online course and click each blue-highlighted image for additional information.
Even in small networks, it is necessary to consider security threats and vulnerabilities when planning a network implementation.
Physical Security (11.2.1.2)
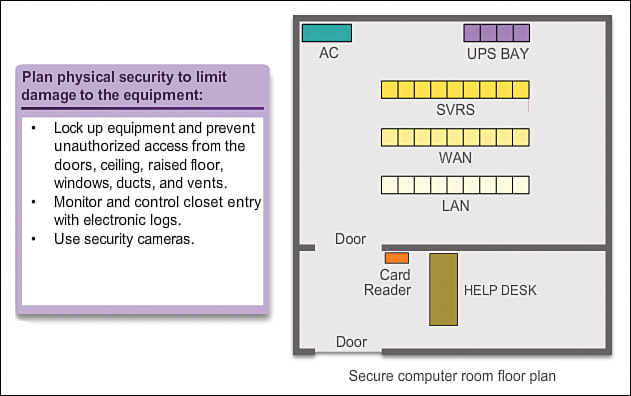
When you think of network security, or even computer security, you may imagine attackers exploiting software vulnerabilities. An equally important vulnerability is the physical security of devices, as shown in Figure 11-7. An attacker can deny the use of network resources if those resources can be physically compromised.
The four classes of physical threats are
![]() Hardware threats: Physical damage to servers, routers, switches, cabling plant, and workstations
Hardware threats: Physical damage to servers, routers, switches, cabling plant, and workstations
![]() Environmental threats: Temperature extremes (too hot or too cold) or humidity extremes (too wet or too dry)
Environmental threats: Temperature extremes (too hot or too cold) or humidity extremes (too wet or too dry)
![]() Electrical threats: Voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss
Electrical threats: Voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss
![]() Maintenance threats: Poor handling of key electrical components (electrostatic discharge), lack of critical spare parts, poor cabling, and poor labeling
Maintenance threats: Poor handling of key electrical components (electrostatic discharge), lack of critical spare parts, poor cabling, and poor labeling
Some of these issues must be dealt with in an organizational policy. Some of them are subject to good leadership and management in the organization.
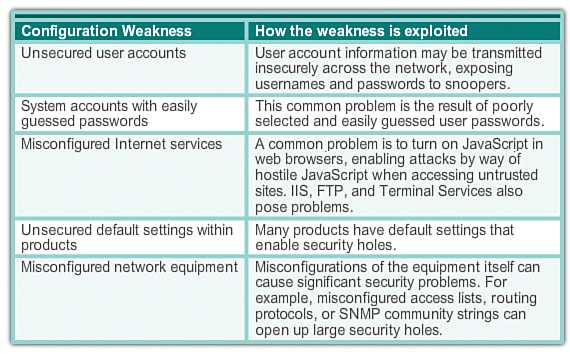
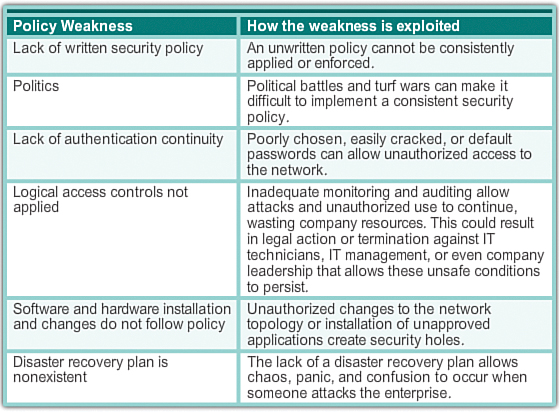
Types of Security Vulnerabilities (11.2.1.3)
Three network security factors are vulnerability, threat, and attack.
Vulnerability is the degree of weakness which is inherent in every network and device. This includes routers, switches, desktops, servers, and even security devices.
Threats include the people interested and qualified in taking advantage of each security weakness. Such individuals can be expected to continually search for new exploits and weaknesses.
Threats are realized by a variety of tools, scripts, and programs to launch attacks against networks and network devices. Typically, the network devices under attack are the endpoints, such as servers and desktop computers.
There are three primary vulnerabilities or weaknesses:
![]() Technology, as shown in Figure 11-8
Technology, as shown in Figure 11-8
![]() Configuration, as shown in Figure 11-9
Configuration, as shown in Figure 11-9
![]() Security policy, as shown in Figure 11-10
Security policy, as shown in Figure 11-10
All three of these vulnerabilities or weaknesses can lead to various attacks, including malicious code attacks and network attacks.

Activity 11.2.1.4: Security Threats and Vulnerabilities (Part 1 and Part 2)
Go to the online course and read the security threats and vulnerabilities scenarios. Drag each scenario to its corresponding type of security threat.
Vulnerabilities and Network Attacks (11.2.2)
This section looks at several network vulnerabilities and attacks.
Viruses, Worms, and Trojan Horses (11.2.2.1)
Malicious code attacks include a number of types of computer programs that were created with the intention of causing data loss or damage. The three main types of malicious code attacks are viruses, Trojan horses, and worms.
A virus is malicious software that is attached to another program to execute a particular unwanted function on a workstation. An example is a program that is attached to command.com (the primary interpreter for Windows systems) and deletes certain files and infects any other versions of command.com that it can find.
A Trojan horse is different only in that the entire application was written to look like something else, when in fact it is an attack tool. An example of a Trojan horse is a software application that runs a simple game on a workstation. While the user is occupied with the game, the Trojan horse mails a copy of itself to every address in the user’s address book. The other users receive the game and play it, thereby spreading the Trojan horse to the addresses in each address book.
Viruses normally require a delivery mechanism, a vector, such as a zip file or some other executable file attached to an email, to carry the virus code from one system to another. The key element that distinguishes a computer worm from a computer virus is that human interaction is required to facilitate the spread of a virus.
Worms are self-contained programs that attack a system and try to exploit a specific vulnerability in the target. Upon successful exploitation of the vulnerability, the worm copies its program from the attacking host to the newly exploited system to begin the cycle again. The anatomy of a worm attack is as follows:
![]() The enabling vulnerability: A worm installs itself by exploiting known vulnerabilities in systems, such as naive end users who open unverified executable attachments in emails.
The enabling vulnerability: A worm installs itself by exploiting known vulnerabilities in systems, such as naive end users who open unverified executable attachments in emails.
![]() Propagation mechanism: After gaining access to a host, a worm copies itself to that host and then selects new targets.
Propagation mechanism: After gaining access to a host, a worm copies itself to that host and then selects new targets.
![]() Payload: After a host is infected with a worm, the attacker has access to the host, often as a privileged user. Attackers could use a local exploit to escalate their privilege level to administrator.
Payload: After a host is infected with a worm, the attacker has access to the host, often as a privileged user. Attackers could use a local exploit to escalate their privilege level to administrator.
Video 11.2.2.1: Malicious Code Attacks
This video demonstrates how malicious code attacks include a number of types of computer programs that were designed to attack the network. Go to the online course to view the animation.
Network Attacks (11.2.2.2)
In addition to malicious code attacks, it is also possible for networks to fall prey to various network attacks. Network attacks can be classified into three major categories:
![]() Reconnaissance attacks: The unauthorized discovery and mapping of systems, services, or vulnerabilities
Reconnaissance attacks: The unauthorized discovery and mapping of systems, services, or vulnerabilities
![]() Access attacks: The unauthorized manipulation of data, system access, or user privileges
Access attacks: The unauthorized manipulation of data, system access, or user privileges
![]() Denial of service (DoS) attacks: The disabling or corruption of networks, systems, or services
Denial of service (DoS) attacks: The disabling or corruption of networks, systems, or services
Reconnaissance Attacks
External attackers can use Internet tools, such as the nslookup and whois utilities, to easily determine the IP address space assigned to a given corporation or entity. After the IP address space is determined, an attacker can then ping the publicly available IP addresses to identify the addresses that are active. To help automate this step, an attacker may use a ping sweep tool, such as fping or gping, which systematically pings all network addresses in a given range or subnet. This is similar to going through a section of a telephone book and calling each number to see who answers.

Activity 11.2.2.2: Reconnaissance Attacks
Go to the online course and click each type of reconnaissance attack tool to see an animation of the attack.
Access Attacks (11.2.2.3)
Access attacks exploit known vulnerabilities in authentication services, FTP services, and web services to gain entry to web accounts, confidential databases, and other sensitive information. An access attack allows an individual to gain unauthorized access to information that they have no right to view. Access attacks can be classified into four types. One of the most common types of access attack is the password attack. Password attacks can be implemented using a packet sniffer to yield user accounts and passwords that are transmitted as clear text. Password attacks can also refer to repeated attempts to log in to a shared resource, such as a server or router, to identify a user account, password, or both. These repeated attempts are called dictionary attacks or brute-force attacks. The other three access attacks are trust exploitation, port redirection and man in the middle.

Video 11.2.2.3 (Section 2): Trust Exploitation
This video demonstrates how an attacker can access one system to then access another. Go to the online course to perform this practice activity.
DoS Attacks (11.2.2.4)
Denial of service (DoS) attacks are the most publicized form of attack and also among the most difficult to eliminate. Even within the attacker community, DoS attacks are regarded as trivial and considered bad form because they require so little effort to execute. But because of their ease of implementation and potentially significant damage, DoS attacks deserve special attention from security administrators.
DoS attacks take many forms. Ultimately, they prevent authorized people from using a service by consuming system resources.

Video 11.2.2.4 (Section 2): Ping of Death
This video demonstrates how an attacker can launch DoS and distributed DoS (DDoS) attacks. Go to the online course to view the animation.

Activity 11.2.2.5: Types of Attacks (Part 1, Part 2, and Part 3)
Go to the online course and read the type of security attack scenarios. Drag each attack type to its corresponding attack scenario.
Lab 11.2.2.6: Researching Network Security Threats
In this lab you will complete the following objectives:
![]() Part 1: Explore the SANS Website
Part 1: Explore the SANS Website
![]() Part 2: Identify Recent Network Security Threats
Part 2: Identify Recent Network Security Threats
![]() Part 3: Detail a Specific Network Security Threat
Part 3: Detail a Specific Network Security Threat
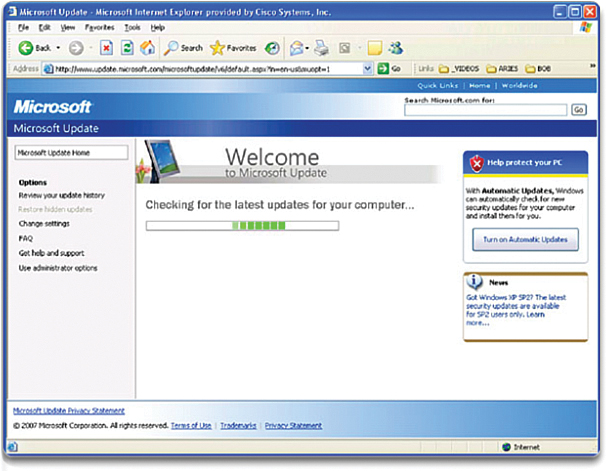
Backup, Upgrade, Update, and Patch (11.2.3.1)
Antivirus software can detect most viruses and many Trojan horse applications and prevent them from spreading in the network. Antivirus software can be deployed at the user level and at the network level.
Keeping up to date with the latest developments in these sorts of attacks can also lead to a more effective defense against these attacks. As new virus or Trojan applications are released, enterprises need to keep current with the latest versions of antivirus software as well.
Worm attack mitigation requires diligence on the part of system and network administration staff. The following are the recommended steps for worm attack mitigation:
![]() Containment: Contain the spread of the worm within the network. Compartmentalize uninfected parts of the network.
Containment: Contain the spread of the worm within the network. Compartmentalize uninfected parts of the network.
![]() Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems.
Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems.
![]() Quarantine: Track down each infected machine inside the network. Disconnect, remove, or block infected machines from the network.
Quarantine: Track down each infected machine inside the network. Disconnect, remove, or block infected machines from the network.
![]() Treatment: Clean and patch each infected system. Some worms may require complete core system reinstallations to clean the system.
Treatment: Clean and patch each infected system. Some worms may require complete core system reinstallations to clean the system.
The most effective way to mitigate a worm attack is to download security updates from the operating system vendor and patch all vulnerable systems. This is difficult with uncontrolled user systems in the local network. Administering numerous systems involves the creation of a standard software image (operating system and accredited applications that are authorized for use on client systems) that is deployed on new or upgraded systems. However, security requirements change, so already-deployed systems may need to have updated security patches installed.
One solution to the management of critical security patches is to create a central patch server that all systems must communicate with after a set period of time, as shown in Figure 11-11. Any patches that are not applied to a host are automatically downloaded from the patch server and installed without user intervention.
Authentication, Authorization, and Accounting (11.2.3.2)
Authentication, authorization, and accounting (AAA, or “triple A”) network security services provide the primary framework to set up access control on a network device. AAA is a way to control who is permitted to access a network (authenticate), control what they can do while they are there (authorize), and watch the actions they perform while accessing the network (accounting). AAA provides a higher degree of scalability than the console, aux, vty, and privileged EXEC authentication commands alone.
Authentication
Users and administrators must prove that they are who they say they are. Authentication can be established using username and password combinations, challenge and response questions, token cards, and other methods. For example: “I am user ‘student.’ I know the password to prove that I am user ‘student.’”
In a small network, local authentication is often used. With local authentication, each device maintains its own database of username/password combinations. However, when there are more than a few user accounts in a local device database, managing those user accounts becomes complex. Additionally, as the network grows and more devices are added to the network, local authentication becomes difficult to maintain and does not scale. For example, if there are 100 network devices, all user accounts must be added to all 100 devices.
For larger networks, a more scalable solution is external authentication. External authentication allows all users to be authenticated through an external network server. The two most popular options for external authentication of users are RADIUS and TACACS+:
![]() RADIUS is an open standard with low use of CPU resources and memory. It is used by a range of network devices, such as switches, routers, and wireless devices.
RADIUS is an open standard with low use of CPU resources and memory. It is used by a range of network devices, such as switches, routers, and wireless devices.
![]() TACACS+ is a security mechanism that enables modular AAA services. It uses a TACACS+ daemon running on a security server.
TACACS+ is a security mechanism that enables modular AAA services. It uses a TACACS+ daemon running on a security server.
Authorization
After the user is authenticated, authorization services determine which resources the user can access and which operations the user is allowed to perform. An example is, “User ‘student’ can access host serverXYZ using Telnet only.”
Accounting
Accounting records what the user does, including what is accessed, the amount of time the resource is accessed, and any changes that were made. Accounting keeps track of how network resources are used. An example is, “User ‘student’ accessed host serverXYZ using Telnet for 15 minutes.”
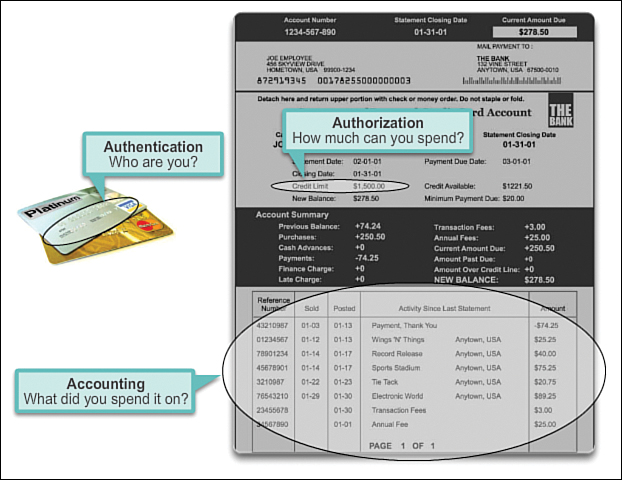
The concept of AAA is similar to the use of a credit card. The credit card identifies who can use it, identifies how much that user can spend, and keeps account of what items the user spent money on, as shown in Figure 11-12.
Firewalls (11.2.3.3)
In addition to protecting individual computers and servers attached to the network, it is important to control traffic traveling to and from the network.
A firewall is one of the most effective security tools available for protecting internal network users from external threats. A firewall resides between two or more networks and controls the traffic between them. It also helps to prevent unauthorized access. Firewall products use various techniques for determining what is permitted or denied access to a network. These techniques are
![]() Packet filtering: Prevents or allows access based on IP or MAC addresses.
Packet filtering: Prevents or allows access based on IP or MAC addresses.
![]() Application filtering: Prevents or allows access by specific application types based on port numbers.
Application filtering: Prevents or allows access by specific application types based on port numbers.
![]() URL filtering: Prevents or allows access to websites based on specific URLs or keywords.
URL filtering: Prevents or allows access to websites based on specific URLs or keywords.
![]() Stateful packet inspection (SPI): Incoming packets must be legitimate responses to requests from internal hosts. Unsolicited packets are blocked unless permitted specifically. SPI can also include the capability to recognize and filter out specific types of attacks such as DoS attacks.
Stateful packet inspection (SPI): Incoming packets must be legitimate responses to requests from internal hosts. Unsolicited packets are blocked unless permitted specifically. SPI can also include the capability to recognize and filter out specific types of attacks such as DoS attacks.
Firewall products may support one or more of these filtering capabilities. Additionally, firewalls often perform network address translation (NAT). NAT translates an internal IP address or group of IP addresses into an outside, public IP address that is sent across the network. This allows internal IP addresses to be concealed from outside users.
Firewall products come packaged in various forms, as shown in Figure 11-13 and described here:
![]() Appliance-based firewalls: An appliance-based firewall is a firewall that is built-in to a dedicated hardware device known as a security appliance.
Appliance-based firewalls: An appliance-based firewall is a firewall that is built-in to a dedicated hardware device known as a security appliance.
![]() Server-based firewalls: A server-based firewall consists of a firewall application that runs on a network operating system (NOS) such as Linux or Windows.
Server-based firewalls: A server-based firewall consists of a firewall application that runs on a network operating system (NOS) such as Linux or Windows.
![]() Integrated firewalls: An integrated firewall is implemented by adding firewall functionality to an existing device, such as a router.
Integrated firewalls: An integrated firewall is implemented by adding firewall functionality to an existing device, such as a router.
![]() Personal firewalls: Personal firewalls reside on host computers and are not designed for LAN implementations. They may be available by default from the OS or may come from an outside vendor.
Personal firewalls: Personal firewalls reside on host computers and are not designed for LAN implementations. They may be available by default from the OS or may come from an outside vendor.
Endpoint Security (11.2.3.4)
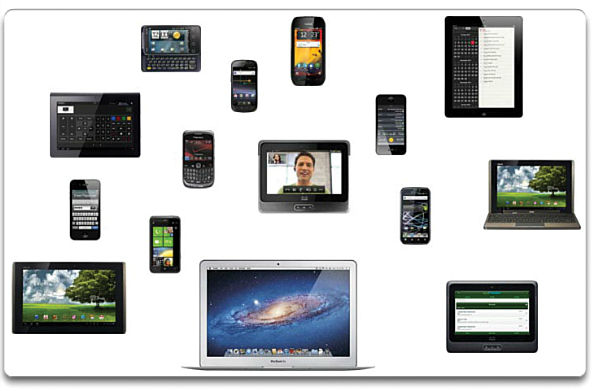
A secure network is only as strong as its weakest link. The high-profile threats most often discussed in the media are external threats, such as Internet worms and DoS attacks. But securing the internal network is just as important as securing the perimeter of a network. The internal network is made up of network endpoints, some of which are shown in Figure 11-14. An endpoint, or host, is an individual computer system or device that acts as a network client. Common endpoints are laptops, desktops, servers, smartphones, and tablets. If users are not practicing security with their endpoint devices, no amount of security precautions will guarantee a secure network.
Securing endpoint devices is one of the most challenging jobs of a network administrator because it involves human nature. A company must have well-documented policies in place, and employees must be aware of and follow those policies. Employees need to be trained on proper use of the network. Policies often include the use of antivirus software and host intrusion prevention. More comprehensive endpoint security solutions rely on network access control.
Endpoint security also requires securing Layer 2 devices in the network infrastructure to prevent against Layer 2 attacks such as MAC address spoofing, MAC address table overflow attacks, and LAN storm attacks. This is known as attack mitigation.
Securing Devices (11.2.4)
One method of mitigating security issues is to secure the different network devices. This section looks at several methods of doing that.
Introduction to Securing Devices (11.2.4.1)
Part of network security is securing actual devices, including end devices and intermediate devices such as network devices.
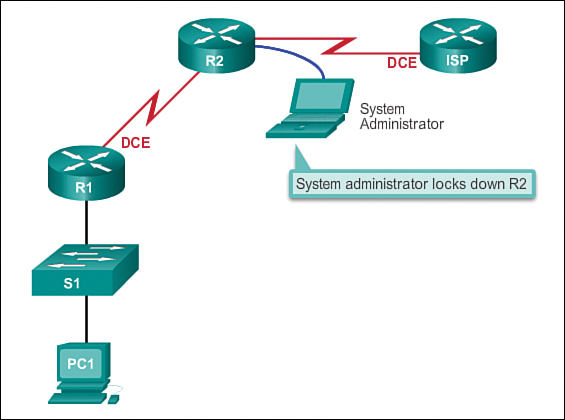
When a new operating system is installed on a device, the security settings are set to the default values. In most cases, this level of security is inadequate. For Cisco routers, the Cisco AutoSecure feature can be used to assist securing the system. Figure 11-15 shows a typical network with devices that need to be secured. There are some simple steps that should be taken that apply to most operating systems:
![]() Change default usernames and passwords immediately.
Change default usernames and passwords immediately.
![]() Restrict access to system resources to only the individuals that are authorized to use those resources.
Restrict access to system resources to only the individuals that are authorized to use those resources.
![]() Turn off and uninstall, when possible, any unnecessary services and applications.
Turn off and uninstall, when possible, any unnecessary services and applications.
All devices should be updated with security patches as they become available. Often, devices shipped from the manufacturer have been sitting in a warehouse for a period of time and do not have the most up-to-date patches installed. It is important, prior to implementation, to update any software and install any security patches.
Passwords (11.2.4.2)
To protect network devices, it is important to use strong passwords. Here are standard guidelines to follow:
![]() Use a password length of at least 8 characters, preferably 10 or more characters. A longer password is a better password.
Use a password length of at least 8 characters, preferably 10 or more characters. A longer password is a better password.
![]() Make passwords complex. Include a mix of uppercase and lowercase letters, numbers, symbols, and spaces, if allowed.
Make passwords complex. Include a mix of uppercase and lowercase letters, numbers, symbols, and spaces, if allowed.
![]() Avoid passwords based on repetition, common dictionary words, letter or number sequences, usernames, relative or pet names, biographical information (such as birthdates, ID numbers, and ancestor names), or other easily identifiable pieces of information.
Avoid passwords based on repetition, common dictionary words, letter or number sequences, usernames, relative or pet names, biographical information (such as birthdates, ID numbers, and ancestor names), or other easily identifiable pieces of information.
![]() Deliberately misspell a password. For example, Smith = Smyth = 5mYth or Security = 5ecur1ty.
Deliberately misspell a password. For example, Smith = Smyth = 5mYth or Security = 5ecur1ty.
![]() Change passwords often. If a password is unknowingly compromised, the window of opportunity for the attacker to use the password is limited.
Change passwords often. If a password is unknowingly compromised, the window of opportunity for the attacker to use the password is limited.
![]() Do not write passwords down and leave them in obvious places such as on the desk or monitor.
Do not write passwords down and leave them in obvious places such as on the desk or monitor.
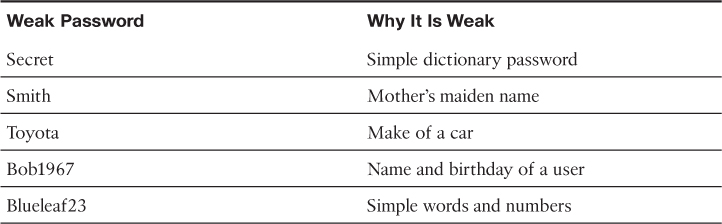
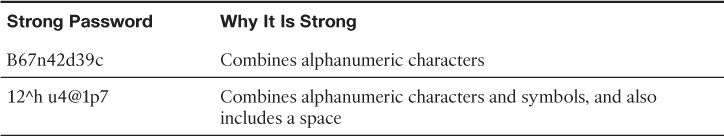
Tables 11-1 and 11-2 provide examples of weak and strong passwords, respectively.
On Cisco routers, leading spaces are ignored for passwords, but spaces after the first character are not ignored. Therefore, one method to create a strong password is to use a space in the password and create a phrase made of many words. This is called a pass phrase. A pass phrase is often easier to remember than a simple password. It is also longer and harder to guess.
Administrators should ensure that strong passwords are used across the network. One way to accomplish this is to use the same “brute force” attack tools that attackers use as a way to verify password strength.
Basic Security Practices (11.2.4.3)
When implementing devices, it is important to follow all security guidelines set by the organization. This includes naming devices in a fashion that allows for easy documentation and tracking but also maintains some form of security. It is not wise to provide too much information about the use of the device in the hostname. There are many other basic security measures that should be taken.
Additional Password Security
Strong passwords are only as useful as they are secret. There are several steps that can be taken to help ensure that passwords remain secret. Using the global configuration command service password-encryption prevents unauthorized individuals from viewing passwords in plaintext in the configuration file, as shown Figure 11-16. This command causes the encryption of all passwords that are unencrypted.
Additionally, to ensure that all configured passwords are a minimum of a specified length, use the security passwords min-length command in global configuration mode.
Another way hackers learn passwords is simply by brute-force attacks, trying multiple passwords until one works. It is possible to prevent this type of attack by blocking login attempts to the device if a set number of failures occurs within a specific amount of time. The following command will block login attempts for 120 seconds if three failed login attempts occur within 60 seconds:
Router(config)# login block-for 120 attempts 3 within 60
Banners
A banner message is similar to a no-trespassing sign. Banners are important in order to be able to prosecute, in a court of law, anyone who accesses the system inappropriately. Banners serve as a means of letting intruders know that they are entering unauthorized areas of the network. Be sure banner messages comply with security policies for the organization. The following line of code shows how you would configure the message of the day banner.
Router(config)# banner motd #message#
Exec Timeout
Another recommendation is to set executive (exec) timeouts. By setting the exec timeout, you are telling the Cisco device to automatically disconnect users on a line after they have been idle for the duration of the exec timeout value. Exec timeouts can be configured on console, vty, and aux ports. The following command will disconnect users after 10 minutes of inactivity on a router:
Router(config)# line vty 0 4
Router(config-vty)# exec-timeout 10
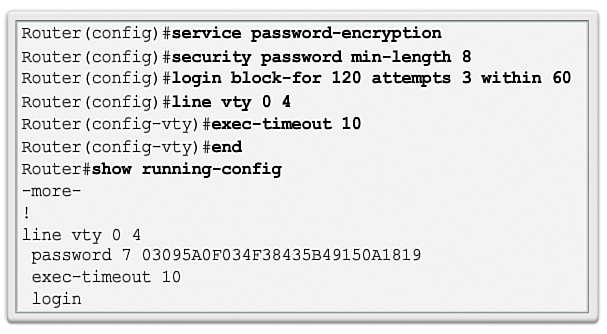
Enable SSH (11.2.4.4)
This section looks at the function of SSH and explains how to enable SSH.
Remote Access via SSH
The legacy protocol to manage devices remotely is Telnet. Telnet is not secure. Data contained within a Telnet packet is transmitted unencrypted. Using a tool like Wireshark, it is possible for someone to “sniff” a Telnet session and obtain password information. For this reason, it is highly recommended to enable Secure Shell (SSH) on devices for secure remote access. It is possible to configure a Cisco device to support SSH using the following four steps, also shown in Figure 11-17:
Step 1. Ensure that the router has a unique hostname, and then configure the IP domain name of the network using the ip domain-name domain-name command in global configuration mode.
Step 2. Generate one-way secret keys for a router to encrypt SSH traffic. The key is what is actually used to encrypt and decrypt data. To create an encryption key, use the crypto key generate rsa general-keys modulus modulus-size command in global configuration mode, as shown next. The specific meaning of the various parts of this command are complex and out of scope for this course, but for now, just note that the modulus determines the size of the key and can be configured from 360 bits to 2,048 bits. The larger the modulus, the more secure the key, but the longer it takes to encrypt and decrypt information. The minimum recommended modulus length is 1,024 bits.
Router(config)# crypto key generate rsa general-keys modulus 1024
Step 3. Create a local database username entry using the username name secret secret global configuration command.
Step 4. Enable vty inbound SSH sessions using the line vty commands login local and transport input ssh.
The router SSH service can now be accessed using SSH client software.
Lab 11.2.4.5: Accessing Network Devices with SSH
In this lab you will complete the following objectives:
![]() Part 1: Configure Basic Device Settings
Part 1: Configure Basic Device Settings
![]() Part 2: Configure the Router for SSH Access
Part 2: Configure the Router for SSH Access
![]() Part 3: Examine a Telnet Session with Wireshark
Part 3: Examine a Telnet Session with Wireshark
![]() Part 4: Examine a SSH Session with Wireshark
Part 4: Examine a SSH Session with Wireshark
![]() Part 5: Configure the Switch for SSH Access
Part 5: Configure the Switch for SSH Access
![]() Part 6: SSH from the CLI on the Switch
Part 6: SSH from the CLI on the Switch
Lab 11.2.4.6: Securing Network Devices
In this lab you will complete the following objectives:
![]() Part 1: Configure Basic Device Settings
Part 1: Configure Basic Device Settings
![]() Part 2: Configure Basic Security Measures on the Router
Part 2: Configure Basic Security Measures on the Router
![]() Part 3: Configure Basic Security Measures on the Switch
Part 3: Configure Basic Security Measures on the Switch
Basic Network Performance (11.3)
There are several ways of monitoring network performance; this section looks at several means of doing that.
Ping (11.3.1)
![]()
Checking for Connectivity with Ping
The ping protocol is often the first tool used to check network connectivity.
Interpreting Ping Results (11.3.1.1)
After the network has been implemented, a network administrator must be able to test the network connectivity to ensure that it is operating appropriately. Additionally, it is a good idea for the network administrator to document the network.
The ping Command
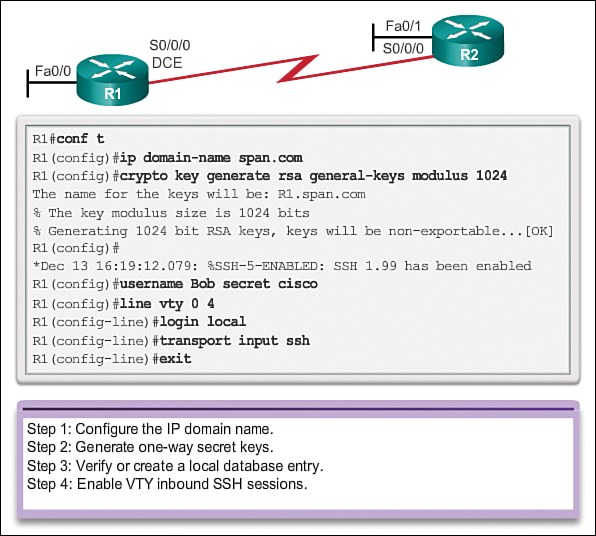
Using the ping command is an effective way to test connectivity. The test is often referred to as testing the protocol stack, because the ping command moves from Layer 3 of the OSI model to Layer 2 and then Layer 1. Ping uses the ICMP protocol to check for connectivity.
The ping command will not always pinpoint the nature of a problem, but it can help to identify the source of the problem, an important first step in troubleshooting a network failure.
The ping command provides a method for checking the protocol stack and IPv4 address configuration on a host as well as testing connectivity to local or remote destination hosts, as shown in Figure 11-18. There are additional tools that can provide more information than ping, such as telnet or trace, which will be discussed in more detail later.
IOS Ping Indicators
A ping issued from the IOS will yield one of several indications for each ICMP Echo Request message that was sent. The most common indicators are
![]() ! (exclamation mark) indicates receipt of an ICMP Echo Reply message. This indicates that the ping completed successfully and verifies Layer 3 connectivity.
! (exclamation mark) indicates receipt of an ICMP Echo Reply message. This indicates that the ping completed successfully and verifies Layer 3 connectivity.
![]() . (period) indicates a time expired while waiting for an ICMP Echo Reply message. This may indicate problems in the communication or that a connectivity problem occurred somewhere along the path. It may also indicate that a router along the path did not have a route to the destination and did not send an ICMP Destination Unreachable message. It also may indicate that ping was blocked by device security.
. (period) indicates a time expired while waiting for an ICMP Echo Reply message. This may indicate problems in the communication or that a connectivity problem occurred somewhere along the path. It may also indicate that a router along the path did not have a route to the destination and did not send an ICMP Destination Unreachable message. It also may indicate that ping was blocked by device security.
![]() U indicates an ICMP Destination Unreachable message was received. This indicates that a router along the path did not have a route to the destination address or that the ping request was blocked and responded with an ICMP Destination Unreachable message.
U indicates an ICMP Destination Unreachable message was received. This indicates that a router along the path did not have a route to the destination address or that the ping request was blocked and responded with an ICMP Destination Unreachable message.
Testing the Loopback
The ping command is used to verify the internal IP configuration on the local host. Recall that this test is accomplished by using the ping command on a reserved address called the loopback (127.0.0.1). This verifies the proper operation of the protocol stack from the network layer to the physical layer—and back—without actually putting a signal on the media.
You enter ping commands at a command line. Enter the ping loopback command with this syntax:
C:> ping 127.0.0.1
The reply from this command would look something like this:
Reply from 127.0.0.1: bytes=32 time<1ms TTL=128
Reply from 127.0.0.1: bytes=32 time<1ms TTL=128
Reply from 127.0.0.1: bytes=32 time<1ms TTL=128
Reply from 127.0.0.1: bytes=32 time<1ms TTL=128
Ping statistics for 127.0.0.1:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milliseconds:
Minimum = 0ms, Maximum = 0ms, Average = 0ms
The result indicates that four 32-byte test packets were sent and were returned from host 127.0.0.1 in a time of less than 1 ms. TTL stands for Time-to-Live and defines the number of hops that the ping packet has remaining before it will be dropped.
Extended Ping (11.3.1.2)
The Cisco IOS offers an “extended” mode of the ping command. This mode is entered by typing ping in privileged EXEC mode, without a destination IP address. A series of prompts are then presented, as shown in the following example. Pressing Enter accepts the indicated default values. The example illustrates how to force the source address for a ping to be 10.1.1.1 (see R2 in Figure 11-19); the source address for a standard ping would be 209.165.200.226. By doing this, the network administrator can verify remotely (from R2) that R1 has the route 10.1.1.0/24 in its routing table.
R2# ping
Protocol [ip]:
Target IP address: 192.168.10.1
Repeat count [5]:
Datagram size [100]:
Timeout in seconds [2]:
Extended commands [n]: y
Source address or interface: 10.1.1.1
Type of service [0]:
Set DF bit in IP header? [no]:
Validate reply data? [no]:
Data pattern [0xABCD]:
Loose, Strict, Record, Timestamp, Verbose[none]:
Sweep range of sizes [n]:
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.10.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 36/97/132 ms
Entering a longer timeout period than the default allows for possible latency issues to be detected. If the ping test is successful with a longer value, a connection exists between the hosts, but latency may be an issue on the network.
Note that entering “y” to the “Extended commands” prompt provides more options that are useful in troubleshooting.
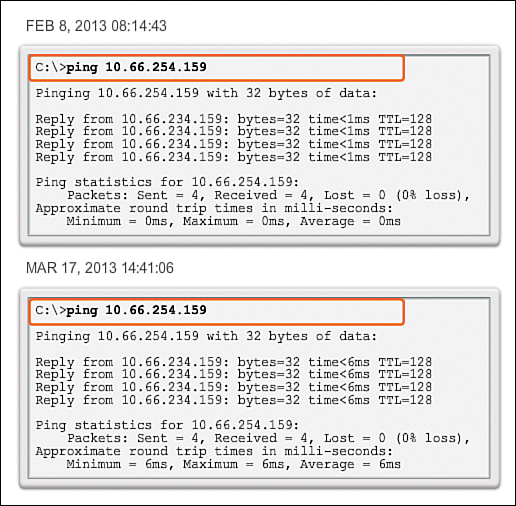
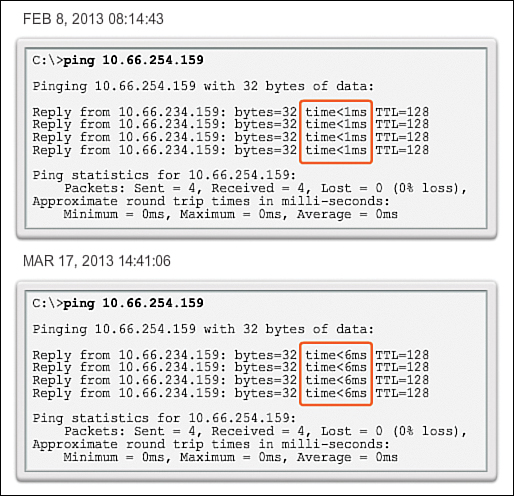
Network Baseline (11.3.1.3)
One of the most effective tools for monitoring and troubleshooting network performance is to establish a network baseline. A baseline is a process for studying the network at regular intervals to ensure that the network is working as designed. A network baseline is more than a single report detailing the health of the network at a certain point in time. Creating an effective network performance baseline is accomplished over a period of time. Measuring performance at varying times (as shown in Figure 11-20 and Figure 11-21) and varying loads will assist in creating a better picture of overall network performance.
The output derived from network commands can contribute data to the network baseline.
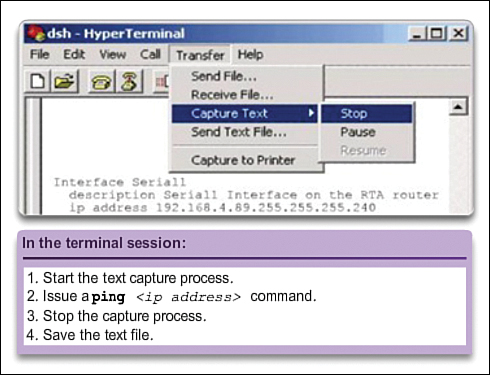
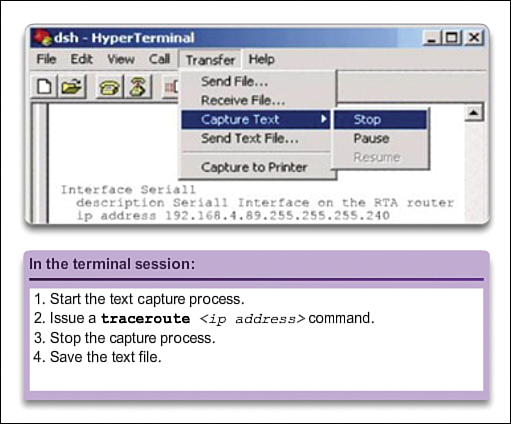
One method for starting a baseline is to copy and paste the results from an executed ping, trace, or other relevant command into a text file. These text files can be time stamped with the date and saved into an archive for later retrieval.
An effective use of the stored information is to compare the results over time (see Figure 11-22). Among items to consider are error messages and the response times from host to host. If there is a considerable increase in response times, there may be a latency issue to address.
The importance of creating documentation cannot be emphasized enough. Verification of host-to-host connectivity, latency issues, and resolutions of identified problems can assist a network administrator in keeping a network running as efficiently as possible.
Corporate networks should have extensive baselines...more extensive than we can describe in this course. Professional-grade software tools are available for storing and maintaining baseline information. In this course, we only cover some basic techniques and discuss the purpose of baselines.
You can find best practices for baseline processes here: http://www.cisco.com/en/US/tech/tk869/tk769/technologies_white_paper09186a008014fb3b.shtml.
Capturing ping command output can also be completed from the IOS prompt, as shown in Figure 11-23.
Tracert (11.3.2)
Another well-known tool is tracert. This section looks at how to use tracert.
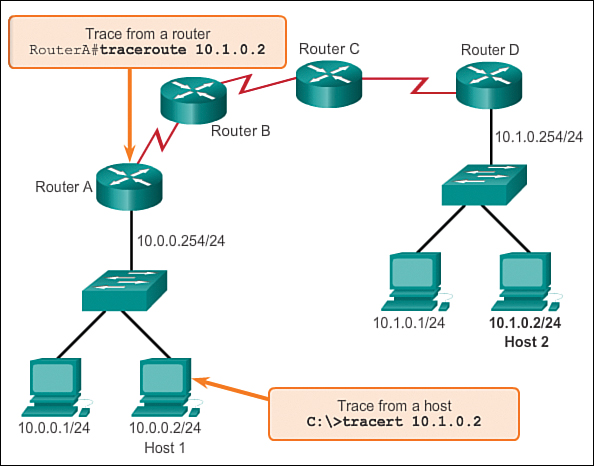
Interpreting Tracert Messages (11.3.2.1)
A trace returns a list of hops as a packet is routed through a network. The form of the command depends on where the command is issued. When performing the trace from a Windows computer, use tracert, and when performing the trace from a router CLI, use traceroute, as shown in Figure 11-24.
Like ping commands, trace commands are entered in the command line and take an IP address as the argument.
Assuming that the command will be issued from a Windows computer, we use the tracert form:
C:> tracert 10.1.0.2
Tracing route to 10.1.0.2 over a maximum of 30 hops
1 2 ms 2 ms 2 ms 10.0.0.254
2 * * * Request timed out.
3 * * * Request timed out.
4 ^C
The only successful response was from the gateway on Router A. Trace requests to the next hop timed out, meaning that the next hop router did not respond. The trace results indicate that the failure is therefore in the internetwork beyond the LAN.
Capturing the traceroute output can also be done from the router prompt, as shown in Figure 11-25.

Packet Tracer Activity 11.3.2.2: Test Connectivity with Traceroute
This activity is designed to help you troubleshoot network connectivity issues using commands to trace the route from source to destination. You are required to examine the output of tracert (the Windows command) and traceroute (the IOS command) as packets traverse the network and determine the cause of a network issue. After the issue is corrected, use the tracert and traceroute commands to verify the completion.
Lab 11.3.2.3: Testing Network Latency with Ping and Traceroute
In this lab you will complete the following objectives:
![]() Part 1: Use Ping to Document Network Latency
Part 1: Use Ping to Document Network Latency
![]() Part 2: Use Traceroute to Document Network Latency
Part 2: Use Traceroute to Document Network Latency
show Commands (11.3.3)
There are numerous Cisco IOS show commands that can be used to test network connectivity; this section looks at some of those commands.
Common show Commands Revisited (11.3.3.1)
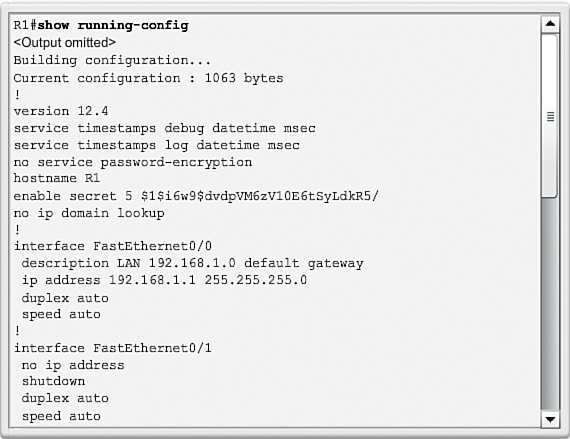
The Cisco IOS CLI show commands display relevant information about the configuration and operation of the device.
Network technicians use show commands extensively for viewing configuration files, checking the status of device interfaces and processes, and verifying the device operational status.
The status of nearly every process or function of the router can be displayed using a show command. The following are some of the more popular show commands:
![]() show running-config (see Figure 11-26)
show running-config (see Figure 11-26)
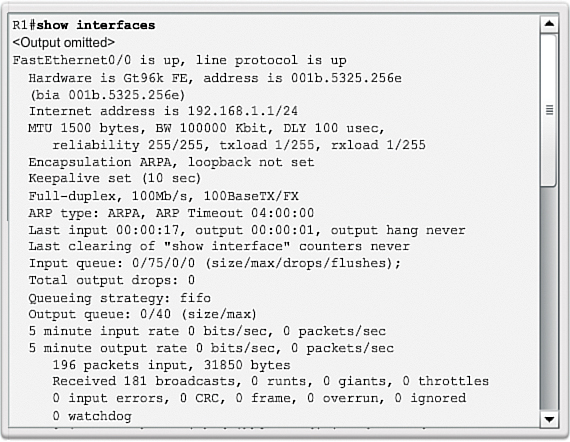
![]() show interfaces (see Figure 11-27)
show interfaces (see Figure 11-27)
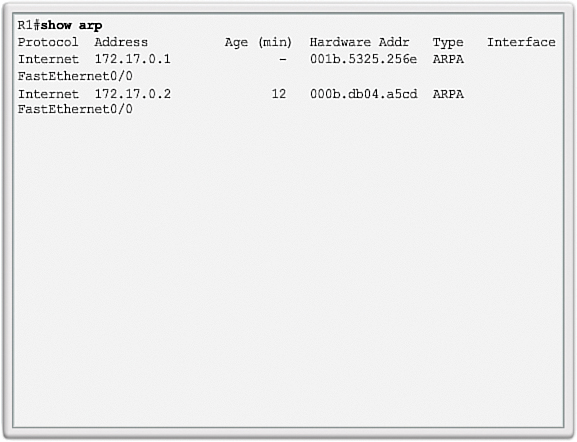
![]() show arp (see Figure 11-28)
show arp (see Figure 11-28)
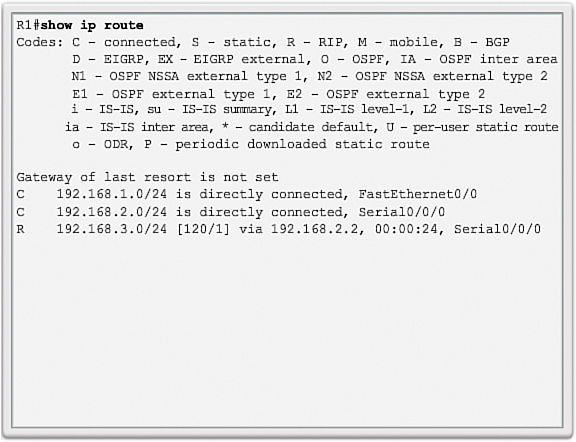
![]() show ip route (see Figure 11-29)
show ip route (see Figure 11-29)
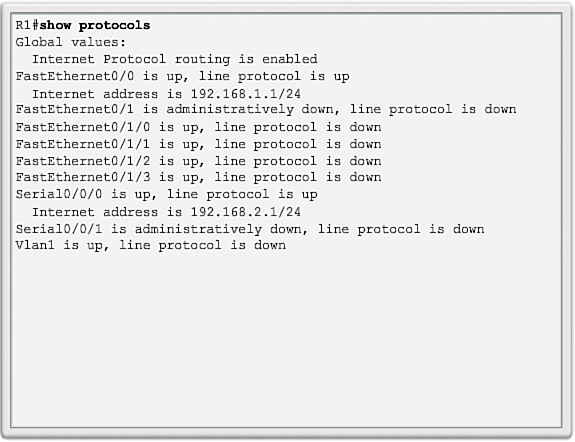
![]() show protocols (see Figure 11-30)
show protocols (see Figure 11-30)
![]() show version (see Figure 11-31)
show version (see Figure 11-31)
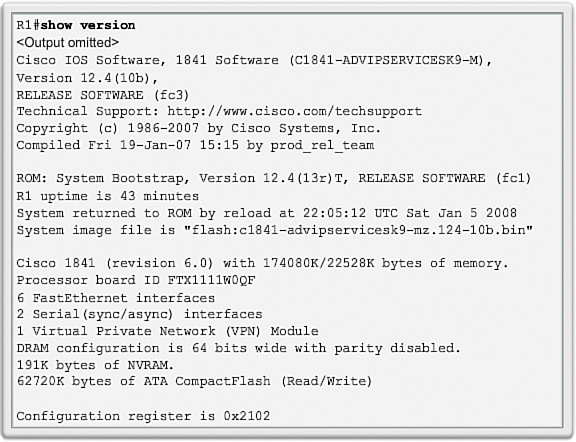
Viewing Router Settings with the show version Command (11.3.3.2)
After the startup configuration file is loaded and the router boots successfully, the show version command can be used to verify and troubleshoot some of the basic hardware and software components used during the bootup process. The output from the show version command includes
![]() The Cisco IOS Software version being used.
The Cisco IOS Software version being used.
![]() The version of the system bootstrap software, stored in ROM memory, that was initially used to boot the router.
The version of the system bootstrap software, stored in ROM memory, that was initially used to boot the router.
![]() The complete filename of the Cisco IOS image and where the bootstrap program located it.
The complete filename of the Cisco IOS image and where the bootstrap program located it.
![]() Type of CPU on the router and amount of RAM. It may be necessary to upgrade the amount of RAM when upgrading the Cisco IOS Software.
Type of CPU on the router and amount of RAM. It may be necessary to upgrade the amount of RAM when upgrading the Cisco IOS Software.
![]() The number and type of physical interfaces on the router.
The number and type of physical interfaces on the router.
![]() The amount of NVRAM. NVRAM is used to store the startup-config file.
The amount of NVRAM. NVRAM is used to store the startup-config file.
![]() The amount of flash memory on the router. It may be necessary to upgrade the amount of flash when upgrading the Cisco IOS Software.
The amount of flash memory on the router. It may be necessary to upgrade the amount of flash when upgrading the Cisco IOS Software.
![]() The currently configured value of the software configuration register in hexadecimal.
The currently configured value of the software configuration register in hexadecimal.

Video 11.3.3.2: show version Output
This video demonstrates how to identify the different features of the show version command output. Go to the online course to view this animation.
The configuration register tells the router how to boot up. For example, the factory default setting for the configuration register is 0x2102. This value indicates that the router attempts to load a Cisco IOS Software image from flash and loads the startup configuration file from NVRAM. It is possible to change the configuration register and, therefore, change where the router looks for the Cisco IOS image and the startup configuration file during the bootup process. If there is a second value in parentheses, it denotes the configuration register value to be used during the next reload of the router.
Click the Note icon at the bottom-right corner of the video 11.3.3.2 to obtain more information about the configuration register.
Viewing Switch Settings with the show version Command (11.3.3.3)
The show version command on a switch displays information about the currently loaded software version, along with hardware and device information. Some of the information displayed by this command includes
![]() Software version: IOS software version
Software version: IOS software version
![]() Bootstrap version: Bootstrap version
Bootstrap version: Bootstrap version
![]() System up-time: Time since last reboot
System up-time: Time since last reboot
![]() System restart info: Method of restart (e.g., power cycle, crash)
System restart info: Method of restart (e.g., power cycle, crash)
![]() Software image name: IOS filename
Software image name: IOS filename
![]() Switch platform and processor type: Model number and processor type
Switch platform and processor type: Model number and processor type
![]() Memory type (shared/main): Main processor RAM and shared packet I/O buffering
Memory type (shared/main): Main processor RAM and shared packet I/O buffering
![]() Hardware interfaces: Interfaces available on the switch
Hardware interfaces: Interfaces available on the switch
![]() Configuration register: Sets bootup specifications, console speed setting, and related parameters
Configuration register: Sets bootup specifications, console speed setting, and related parameters

Packet Tracer Activity 11.3.3.4: Using show Commands
This activity is designed to reinforce the use of router show commands. You are not required to configure, but rather examine the output of several show commands.
Host and IOS Commands (11.3.4)
This section looks at several commands that you can use on the host to test connectivity.
ipconfig Command Options (11.3.4.1)
![]()
Lesson 2: Verifying Host Configuration
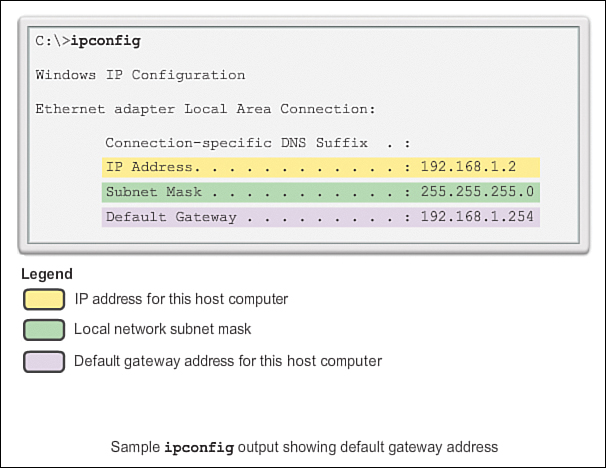
As shown in Figure 11-32, the IP address of the default gateway of a host can be viewed by issuing the ipconfig command at the command line of a Windows computer.
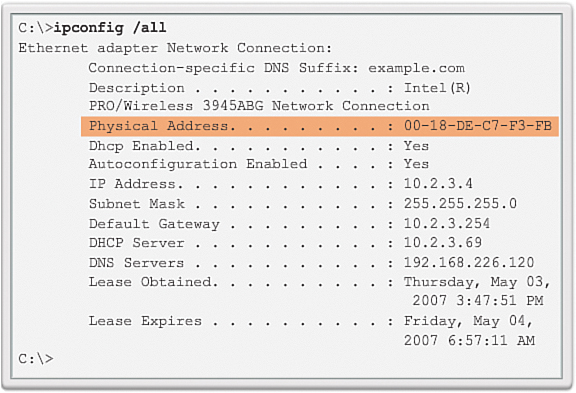
A tool to examine the MAC address of our computer is ipconfig /all. Note that in Figure 11-33, the MAC address of the computer is now displayed along with a number of details regarding the Layer 3 addressing of the device.
In addition, the manufacturer of the network interface in the computer can be identified through the OUI portion of the MAC address. This can be researched on the Internet.
The DNS Client service on Windows PCs optimizes the performance of DNS name resolution by storing previously resolved names in memory. The ipconfig /displaydns command displays all of the cached DNS entries on a Windows computer system.
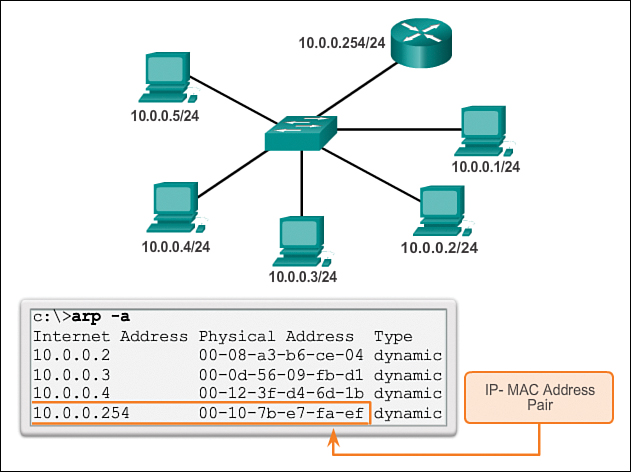
arp Command Options (11.3.4.2)
The arp command enables the creation, editing, and display of mappings of physical addresses to known IPv4 addresses. The arp command is executed from the Windows command prompt.
To execute an arp command, at the command prompt of a host, enter
C:host1> arp -a
As shown in Figure 11-34, the arp –a command lists all devices currently in the ARP cache of the host, which includes the IPv4 address, physical address, and the type of addressing (static/dynamic), for each device.
The cache can be cleared by using the arp –d command in the event the network administrator wants to repopulate the cache with updated information.
Note
The ARP cache only contains information from devices that have been recently accessed. To ensure that the ARP cache is populated, ping a device so that it will have an entry in the ARP table.
show cdp neighbors Command Options (11.3.4.3)
![]()
Lesson 4: Discovering Neighbors
![]()
Lesson 6: Discovering Neighbors
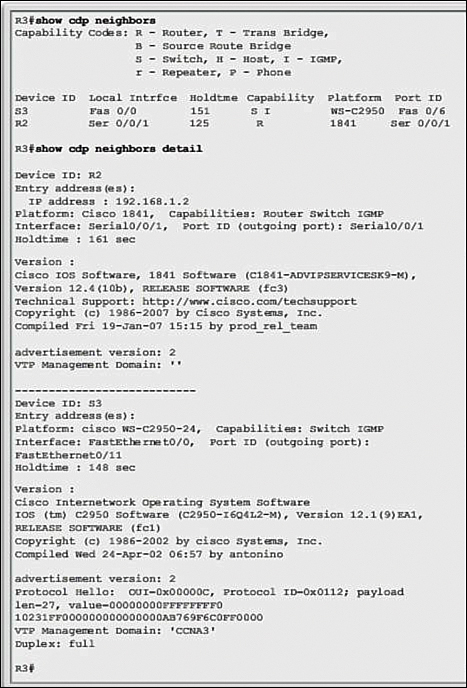
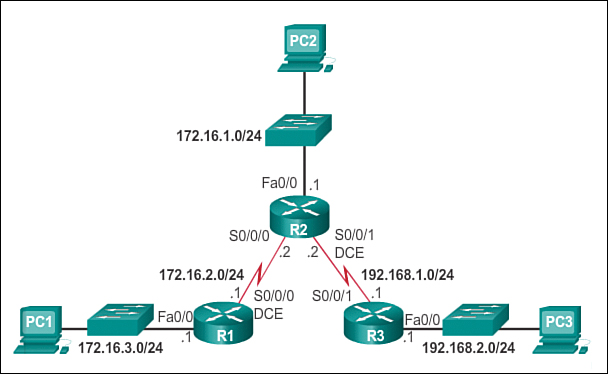
Examine the output from the show cdp neighbors (and show cd neighbor details) command in Figure 11-35, with the topology in Figure 11-36. Notice that R3 has gathered some detailed information about R2 and the switch connected to the Fast Ethernet interface on R3.
CDP is a Cisco-proprietary protocol that runs at the data link layer (Layer 2). Because CDP operates at the data link layer, two or more Cisco network devices, such as routers that support different network layer protocols, can learn about each other even if Layer 3 connectivity does not exist.
When a Cisco device boots up, CDP starts up by default. CDP automatically discovers neighboring Cisco devices running CDP, regardless of which Layer 3 protocol or suites are running. CDP exchanges hardware and software device information with its directly connected CDP neighbors.
CDP provides the following information about each CDP neighbor device:
![]() Device identifiers: For example, the configured hostname of a switch
Device identifiers: For example, the configured hostname of a switch
![]() Address list: Up to one network layer address for each protocol supported
Address list: Up to one network layer address for each protocol supported
![]() Port identifier: The name of the local and remote port, in the form of an ASCII character string such as ethernet0
Port identifier: The name of the local and remote port, in the form of an ASCII character string such as ethernet0
![]() Capabilities list: For example, whether this device is a router or a switch
Capabilities list: For example, whether this device is a router or a switch
![]() Platform: The hardware platform of the device; for example, a Cisco 1841 series router
Platform: The hardware platform of the device; for example, a Cisco 1841 series router
The show cdp neighbors detail command reveals the IP address of a neighboring device. CDP will reveal the neighbor’s IP address regardless of whether or not you can ping the neighbor. This command is very helpful when two Cisco routers cannot route across their shared data link. The show cdp neighbors detail command will help determine if one of the CDP neighbors has an IP configuration error.
For network discovery situations, knowing the IP address of the CDP neighbor is often all the information needed to telnet into that device. For obvious reasons, CDP can be a security risk. Because some IOS versions send out CDP advertisements by default, it is important to know how to disable CDP. To disable CDP globally, use the global configuration command no cdp run. To disable CDP on an interface, use the interface command no cdp enable.
Using the show ip interface brief Command (11.3.4.4)
In the same way that commands and utilities are used to verify a host configuration, commands can be used to verify the interfaces of intermediate devices. The Cisco IOS provides commands to verify the operation of router and switch interfaces.
Verifying Router Interfaces
One of the most frequently used commands is the show ip interface brief command. This command provides a more abbreviated output than the show ip interface command. It provides a summary of the key information for all the network interfaces on a router.
Figure 11-37 shows the topology that is being used in this example.
In Activity 11.3.4.4 Part 2, click the R1 button. The show ip interface brief output displays all interfaces on the router, the IP address assigned to each interface, if any, and the operational status of the interface.

Activity 11.3.4.4 Part 2: Interface Testing
Go to the online course and click the R1 button. The output of the ip interface brief command is displayed. Click the S1 button. The output of the switch is displayed.
According to the output, the Fast Ethernet 0/0 interface has an IP address of 192.168.254.254. The last two columns in this line show the Layer 1 and Layer 2 status of this interface. The up in the Status column shows that this interface is operational at Layer 1. The up in the Protocol column indicates that the Layer 2 protocol is operational.
Also notice that the Serial 0/0/1 interface has not been enabled. This is indicated by administratively down in the Status column.
As with any end device, we can verify Layer 3 connectivity with the ping and traceroute commands. In this example, both the ping and traceroute commands show successful connectivity.
Verifying the Switch Interfaces
Continuing in Activity 11.3.4.4 Part 2, click the S1 button. The show ip interface brief command can also be used to verify the status of the switch interfaces. The IP address for the switch is applied to a VLAN interface. In this case, the Vlan 1 interface is assigned an IP address of 192.168.254.250 and has been enabled and is operational.
The output also shows that the FastEthernet0/1 interface is down. This indicates either that no device is connected to the interface or that the device that is connected to this interface has a network interface that is not operational.
In contrast, the output shows that the FastEthernet0/2 and FastEthernet0/3 interfaces are operational. This is indicated by both the Status and Protocol being shown as up.
You can also test the Layer 3 connectivity of the switch with the show ip interface brief and traceroute commands. In this example, both the ping and trace commands show successful connectivity.
It is important to keep in mind that an IP address is not required for a switch to perform its job of frame forwarding at Layer 2. An IP address is only necessary if the switch will be managed over the network using Telnet or SSH. If the network administrator plans to remotely connect to the switch from a location outside of the local LAN, then a default gateway must also be configured.

Activity 11.3.4.5: show Commands
Go to the online course and read each of the types of show command scenarios. Drag each show command to the correct show command scenario.
Lab 11.3.4.6: Using the CLI to Gather Network Device Information
In this lab you will complete the following objectives:
![]() Part 1: Set Up Topology and Initialize Devices
Part 1: Set Up Topology and Initialize Devices
![]() Part 2: Configure Devices and Verify Connectivity
Part 2: Configure Devices and Verify Connectivity
![]() Part 3: Gather Network Device Information
Part 3: Gather Network Device Information
Managing IOS Configuration Files (11.4)
This section introduces both router and switch file systems and explains how to back them up and how to restore them.
Router and Switch File Systems (11.4.1)
Router and switch file systems are discussed in this section.
Router File Systems (11.4.1.1)
In addition to implementing and securing a small network, the job of the network administrator also includes managing configuration files. Managing the configuration files is important for purposes of backup and retrieval in the event of a device failure.
The Cisco IOS File System (IFS) provides a single interface to all the file systems a router uses, including
![]() Network file systems (TFTP and FTP)
Network file systems (TFTP and FTP)
![]() Any other endpoint for reading or writing data such as NVRAM, the running configuration, ROM, and others
Any other endpoint for reading or writing data such as NVRAM, the running configuration, ROM, and others
With Cisco IFS, all files can be viewed and classified (image, text file, and so forth), including files on remote servers. For example, it is possible to view a configuration file on a remote server to verify that it is the correct configuration file before loading the file on the router.
Cisco IFS allows the administrator to move around to different directories, list the files in a directory, and create subdirectories in flash memory or on a disk. The directories available depend on the device.
The Figure 11-38 displays the output of the show file systems command, which lists all of the available file systems on a Cisco 1941 router, in this example. This command provides useful information such as the amount of available and free memory, the type of file system, and its permissions. Permissions include read only (ro), write only (wo), and read and write (rw), shown in the Flags column of the command output.
Although there are several file systems listed in Figure 11-38, of interest to us are the flash and NVRAM file systems.
Notice that the flash file system also has an asterisk preceding it. This indicates that flash is the current default file system. The bootable IOS is located in flash; therefore, the pound symbol (#) is appended to the flash listing, indicating that it is a bootable disk.
Flash File System
Figure 11-39 lists the content of the current default file system, which in this case is flash, as was indicated by the asterisk preceding its listing in Figure 11-38. There are several files located in flash, but of specific interest is the last listing. This is the name of the current Cisco IOS file image that is running in RAM.
NVRAM File System
To view the contents of NVRAM, you must change the current default file system using the cd (change directory) command, as shown in Figure 11-40. The pwd (present working directory) command verifies that we are viewing the NVRAM directory. Finally, the dir (directory) command lists the contents of NVRAM. Although there are several configuration files listed, of specific interest is the startup-config file.
Switch File Systems (11.4.1.2)
With the Cisco 2960 switch flash file system, you can copy configuration files and archive (upload and download) software images.
The command to view the file systems on a Catalyst switch is the same as the command to view the file systems on a Cisco router: show file systems (as shown in Figure 11-41).
Many basic UNIX commands are supported on Cisco switches and routers: cd for changing to a file system or directory, dir to display directories on a file system, and pwd to display the working directory.
Back Up and Restore Configuration Files (11.4.2)
This section examines the several methods available to back up and restore IOS configuration files.
Backing Up and Restoring Using Text Files (11.4.2.1)
One of the methods of backing up and restoring IOS configuration files is to use text files.
Backing Up Configurations with Text Capture (Tera Term)
Configuration files can be saved/archived to a text file using Tera Term (see Figure 11-42).
As shown in Figure 11-42, the steps are as follows:
Step 1. On the File menu, click Log.
Step 2. Choose the location to save the file. Tera Term will begin capturing text.
Step 3. After capture has been started, execute the show running-config or show startup-config command at the privileged EXEC prompt. Text displayed in the terminal window will be directed into the chosen file.
Step 4. When the capture is complete, select Close in the Tera Term: Log window.
Step 5. View the file to verify that it was not corrupted.
Restoring Text Configurations
A configuration can be copied from a file to a device. When copied from a text file and pasted into a terminal window, the IOS executes each line of the configuration text as a command. This means that the file will require editing to ensure that encrypted passwords are in plaintext and that non-command text such as “--More--” and IOS messages are removed.
Further, at the CLI, the device must be set at the global configuration mode to receive the commands from the text file being pasted into the terminal window.
Note
To facilitate the restore of the configuration, you also need to add a line such as “no shutdown” after each interface configured with an active IP address.
When using Tera Term, the steps are as follows:
Step 1. On the File menu, click Send file.
Step 2. Locate the file to be copied into the device and click Open.
Step 3. Tera Term will paste the file into the device.
The text in the file will be applied as commands in the CLI and become the running configuration on the device. This is a convenient method for manually configuring a router.
Backing Up and Restoring Using TFTP (11.4.2.2)
Another method of backing up and restoring IOS files is through the use of Trivial File Transfer Protocol (TFTP).
Backing Up Configurations with TFTP
Copies of configuration files should be stored as backup files in the event of a problem. Configuration files can be stored on a TFTP server or a USB drive. A configuration file should also be included in the network documentation.
To save the running configuration or the startup configuration to a TFTP server, use either the copy running-config tftp command, as shown in Figure 11-43, or the copy startup-config tftp command. Follow these steps to back up the running configuration to a TFTP server:
Step 1. Enter the copy running-config tftp command.
Step 2. Enter the IP address of the host where the configuration file will be stored.
Step 3. Enter the name to assign to the configuration file, or press the Enter key to continue.
Step 4. Press Enter to confirm each choice.
Note
You need to have a TFTP server running on the network for this part of the TFTP process to work.
Restoring Configurations with TFTP
To restore the running configuration or the startup configuration from a TFTP server, use either the copy tftp running-config command or the copy tftp startup-config command. Use these steps to restore the running configuration from a TFTP server:
Note
To facilitate the restore of the configuration, you also need to add a line such as “no shutdown” after each interface configured with an active IP address.
Step 1. Enter the copy tftp running-config command.
Step 2. Enter the IP address of the host where the configuration file is stored.
Step 3. Enter the name to assign to the configuration file.
Step 4. Press Enter to confirm each choice.
Using USB Ports on a Cisco Router (11.4.2.3)
The Universal Serial Bus (USB) storage feature enables certain models of Cisco routers to support USB flash drives. The USB flash feature provides an optional, secondary storage capability and an additional boot device. Images, configurations, and other files can be copied to or from the Cisco USB flash memory with the same reliability as storing and retrieving files using the CompactFlash card. In addition, modular Cisco Integrated Services Routers can boot any Cisco IOS Software image saved on USB flash memory.
Cisco USB flash modules are available in 64 MB, 128 MB, and 256 MB versions.
To be compatible with a Cisco router, a USB flash drive must be formatted in a FAT16 format. If that is not the case, the show file systems command will display an error indicating an incompatible file system.
Here is an example of the use of the dir command on a USB file system:
Router# dir usbflash0:
Directory of usbflash0:/
1 -rw- 30125020 Dec 22 2032 05:31:32 +00:00 c3825-entservicesk9-mz.123-14.T
63158272 bytes total (33033216 bytes free)
Ideally, USB flash can hold multiple copies of the Cisco IOS and multiple router configurations. The USB flash allows an administrator to easily move and copy those IOS files and configurations from router to router, and many times, the copying process can take place several times faster than it would over a LAN or WAN feature enables certain models of Cisco routers to support USB flash drives. Note that the IOS may not recognize the proper size of the USB flash, but that does not necessarily mean that the flash is unsupported. Additionally, the USB ports on a router are usually USB 2.0, as shown in Figure 11-44.
Backing Up and Restoring Using a USB (11.4.2.4)
This section discusses backing up with a USB flash drive, as well as restoration from a USB flash drive.
Backing Up Configurations with a USB Flash Drive
When backing up to a USB port, it is a good idea to issue the show file systems command to verify that the USB drive is there and confirm its name, as shown in Figure 11-45.
Next, use the copy running-config usbflash0:/ command to copy the configuration file to the USB flash drive. Be sure to use the name of the flash drive, as indicated in the file system. The slash is optional but indicates the root directory of the USB flash drive.
The IOS will prompt for the filename. If the file already exists on the USB flash drive, the router will prompt for overwrite, as shown in Figure 11-46.
Use the dir command to see the file on the USB drive, and use the more command to see the contents, as shown in Figure 11-47.
Restoring Configurations with a USB Flash Drive
In order to copy the file back, it will be necessary to edit the USB R1-Config file with a text editor to make it a valid running-config file; otherwise, there are a lot of entries that are invalid commands and no interfaces will be brought up.
R1# copy usbflash0:/R1-Config running-config
Destination filename [running-config]?

Packet Tracer Activity 11.4.2.5: Backing Up Configuration Files
This activity is designed to show how to restore a configuration from a backup and then perform a new backup. Due to an equipment failure, a new router has been put in place. Fortunately, backup configuration files have been saved to a TFTP server. You are required to restore the files from the TFTP server to get the router back online with as little downtime as possible.
Lab 11.4.2.6: Managing Router Configuration Files with Tera Term
In this lab you will complete the following objectives:
![]() Part 1: Configure Basic Device Settings
Part 1: Configure Basic Device Settings
![]() Part 2: Use Terminal Emulation Software to Create a Backup Configuration File
Part 2: Use Terminal Emulation Software to Create a Backup Configuration File
![]() Part 3: Use a Backup Configuration File to Restore a Router
Part 3: Use a Backup Configuration File to Restore a Router
Lab 11.4.2.7: Managing Device Configuration Files Using TFTP, Flash, and USB
In this lab you will complete the following objectives:
![]() Part 1: Build the Network and Configure Basic Device Settings
Part 1: Build the Network and Configure Basic Device Settings
![]() Part 2: (Optional) Download TFTP Server Software
Part 2: (Optional) Download TFTP Server Software
![]() Part 3: Use TFTP to Back Up and Restore the Switch Running Configuration
Part 3: Use TFTP to Back Up and Restore the Switch Running Configuration
![]() Part 4: Use TFTP to Back Up and Restore the Router Running Configuration
Part 4: Use TFTP to Back Up and Restore the Router Running Configuration
![]() Part 5: Back Up and Restore Running Configurations Using Router Flash Memory
Part 5: Back Up and Restore Running Configurations Using Router Flash Memory
![]() Part 6: (Optional) Use a USB Drive to Back Up and Restore the Running Configuration
Part 6: (Optional) Use a USB Drive to Back Up and Restore the Running Configuration
Lab 11.4.2.8: Researching Password Recovery Procedures
In this lab you will complete the following objectives:
![]() Part 1: Research the Configuration Register
Part 1: Research the Configuration Register
![]() Part 2: Document the Password Recovery Procedure for a Specific Cisco Router
Part 2: Document the Password Recovery Procedure for a Specific Cisco Router
Summary (11.5)
Class Activity 11.5.1.1: Capstone Project - Design and Build a Small Business Network
Go to the online course to perform the Capstone Project. You will use Packet Tracer and a word processing application to complete the activity. This activity works best with two to three students per group. In this Capstone Project you will build a network from scratch.

Packet Tracer Activity 11.5.1.2: Skills Integration Challenge
In this scenario the network administrator has asked you to prepare a router for deployment. Before it can be connected to the network, security measures must be enabled.
In order to meet user requirements, even small networks require planning and design. Planning ensures that all requirements, cost factors, and deployment options are given due consideration. An important part of network design is to ensure reliability, scalability, and availability.
Supporting and growing a small network requires being familiar with the protocols and network applications running over the network. Protocol analyzers enable a network professional to quickly compile statistical information about traffic flows on a network. Information gathered by the protocol analyzer is analyzed based on the source and destination of the traffic as well as the type of traffic being sent. This analysis can be used by a network technician to make decisions on how to manage the traffic more efficiently. Common network protocols include DNS, Telnet, SMTP, POP, DHCP, HTTP, and FTP.
It is a necessity to consider security threats and vulnerabilities when planning a network implementation. All network devices must be secured. This includes routers, switches, end-user devices, and even security devices. Networks need to be protected from malicious software, such as viruses, Trojan horses, and worms. Antivirus software can detect most viruses and many Trojan horse applications and prevent them from spreading in the network. The most effective way to mitigate a worm attack is to download security updates from the operating system vendor and patch all vulnerable systems.
Networks must also be protected from network attacks. Network attacks can be classified into three major categories: reconnaissance, access attacks, and denial of service. There are several ways to protect a network from network attacks:
![]() Authentication, authorization, and accounting (AAA, or “triple A”) network security services provide the primary framework to set up access control on a network device. AAA is a way to control who is permitted to access a network (authenticate), to control what they can do while they are there (authorize), and watch the actions they perform while accessing the network (accounting).
Authentication, authorization, and accounting (AAA, or “triple A”) network security services provide the primary framework to set up access control on a network device. AAA is a way to control who is permitted to access a network (authenticate), to control what they can do while they are there (authorize), and watch the actions they perform while accessing the network (accounting).
![]() A firewall is one of the most effective security tools available for protecting internal network users from external threats. A firewall resides between two or more networks and controls the traffic between them. It also helps to prevent unauthorized access.
A firewall is one of the most effective security tools available for protecting internal network users from external threats. A firewall resides between two or more networks and controls the traffic between them. It also helps to prevent unauthorized access.
![]() To protect network devices, it is important to use strong passwords. Also, when accessing network devices remotely, it is highly recommended to enable SSH instead of the unsecured Telnet.
To protect network devices, it is important to use strong passwords. Also, when accessing network devices remotely, it is highly recommended to enable SSH instead of the unsecured Telnet.
After the network has been implemented, a network administrator must be able to monitor and maintain network connectivity. There are several commands available toward this end. For testing network connectivity to local and remote destinations, commands such as ping, telnet, and traceroute are commonly used.
On Cisco IOS devices, the show version command can be used to verify and troubleshoot some of the basic hardware and software components used during the bootup process. To view information for all network interfaces on a router, the show ip interface command is used. The show ip interface brief command can also be used to view a more abbreviated output than is provided by the show ip interface command. CDP is a Cisco-proprietary protocol that runs at the data link layer. Because CDP operates at the data link layer, two or more Cisco network devices, such as routers that support different network layer protocols, can learn about each other even if Layer 3 connectivity does not exist.
Configuration files such as startup-config and running-config should be archived. These files can be saved to a text file or stored on a TFTP server. Some models of routers also have a USB port, in which case a file can be backed up to a USB drive. If needed, these files can be copied to the router and/or switch from the TFTP server or USB drive.
Practice
The following activities provide practice with the topics introduced in this chapter. The Labs and Class Activities are available in the companion Network Basics Lab Manual (978-1-58713-313-8). The Packet Tracer Activities PKA files are found in the online course.
Class Activities
Class Activity 11.0.1.2: Did You Notice?
Class Activity 11.5.1.1: Design and Build a Small Business Network
Labs
Lab 11.2.2.6: Researching Network Security Threats
Lab 11.2.4.5: Accessing Network Devices with SSH
Lab 11.2.4.6: Securing Network Devices
Lab 11.3.2.3: Testing Network Latency with Ping and Traceroute
Lab 11.3.4.6: Using the CLI to Gather Network Device Information
Lab 11.4.2.6: Managing Router Configuration Files with Tera Term
Lab 11.4.2.7: Managing Device Configuration Files Using TFTP, Flash, and USB
Lab 11.4.2.8: Researching Password Recovery Procedures

Packet Tracer Activities
Packet Tracer Activity 11.3.2.2: Troubleshooting IPv4 and IPv6 Addressing
Packet Tracer Activity 11.3.3.4: Using show Commands
Packet Tracer Activity 11.4.2.5: Backing Up Configuration Files
Packet Tracer Activity 11.5.1.2: Skills Integration Challenge
Check Your Understanding
Complete all the review questions listed here to test your understanding of the topics and concepts in this chapter. The appendix, “Answers to the ‘Check Your Understanding’ Questions” lists the answers.
1. A small accounting firm consists of 20 workstations and 3 servers. The company is assigned a network of 209.165.200.224/27. What is a Cisco-recommended approach for managing the IP addressing scheme for the network?
A. Assign static IP addresses for workstations and servers in a sequence of installation steps
B. Divide the network into two subnets, one for workstations and the other for servers
C. Add a DHCP server and assign dynamic IP addresses for workstations and servers via the DHCP server
D. Assign static IP addresses for servers in the upper block of the address pool and allow dynamic IP addresses for workstations
2. A small advertising company has a web server that provides critical business service. The company connects to the Internet through a leased line service to an ISP. Which approach best provides cost-effective redundancy for the Internet connection?
A. Add a second NIC to the web server
B. Add another web server to prepare failover support
C. Add another connection to the Internet via a DSL line to another ISP
D. Add multiple connections between the switches and the edge router
3. What are two examples of maintenance threats to a network? (Choose two.)
A. Poor labeling
B. Unconditioned power
C. Temperature extremes
D. Physical damage to routers
E. Lack of critical spare parts
4. Which statement is an example of a network security threat?
A. A router is configured with a weak password.
B. Telnet is used for all remote management of network devices.
C. A switch is running an old version of IOS with known security bugs.
D. A disgruntled employee has the administrator password to all of the network devices.
E. The company security policy does not specify how many characters must be in a password.
5. Which malicious code attack is self-contained and tries to exploit a specific vulnerability in a system being attacked?
A. Virus
B. Worm
C. Trojan horse
D. Social engineering
6. Which AAA component assigns varying levels of rights to users of network resources?
A. Auditing
B. Accounting
C. Authorization
D. Access control
E. Authentication
F. Acknowledgement
7. When configuring a switch for SSH access, what other command that is associated with the login local command is required to be entered on the switch?
A. enable secret password
B. password password
C. username username secret secret
D. login block-for seconds attempts number within seconds
8. A user complains that the workstation cannot access the network. The network technician asks the user to issue the ping 127.0.0.1 command. What is the purpose of using this command?
A. To test the reachability of a remote network
B. To verify that the NIC is configured with a static address
C. To verify that the TCP/IP stack is operational
D. To check that the workstation can reach a DHCP server
9. What conclusion can be drawn from the results of the following command issued by a user on the workstation?
C:Usersuser10> tracert www.cisco.com
Tracing route to e144.dscb.akamaiedge.net [184.50.224.170]
over a maximum of 30 hops:
1 15 ms 2 ms 3 ms 192.168.10.254
2 * * * Request timed out.
3 11 ms 12 ms 13 ms 173-219-253-70-link.sta.suddenlink.net [173.219.253.70]
4 13 ms 15 ms 21 ms 173-219-253-224-link.sta.suddenlink.net [173.219.253.224]
5 20 ms 19 ms 19 ms 173-219-253-234-link.sta.suddenlink.net [173.219.253.234]
6 29 ms 22 ms 21 ms xe-4-2-0.edge1.Washington1.Level3.net [4.79.20.57]
7 21 ms 22 ms 21 ms ae-4-90.edge2.Washington4.Level3.net [4.69.149.208]
8 31 ms 21 ms 22 ms xe-0-4-0-2.r04.asbnva02.us.bb.gin.ntt.net [129.250.9.153]
9 41 ms 38 ms 38 ms ae-7.r20.asbnva02.us.bb.gin.ntt.net [129.250.3.16]
10 98 ms 58 ms 60 ms ae-3.r20.dllstx09.us.bb.gin.ntt.net [129.250.3.51]
11 61 ms 58 ms 65 ms ae-2.r07.dllstx09.us.bb.gin.ntt.net [129.250.3.67]
12 65 ms 58 ms 66 ms a184-50-224-170.deploy.akamaitechnologies.com
[184.50.224.170]
Trace complete.
A. One of the routers in the path is not operational.
B. A ping to the website takes about 63 milliseconds.
C. The IP address of the workstation is 192.168.10.254.
D. There are 12 hops between the workstation and the website.
10. While downloading an IOS image from a TFTP server, an administrator sees long strings of exclamation marks (!) output to the console. What does this mean?
A. The transfer is working.
B. The TFTP server is not responding.
C. The IOS file is corrupt and is failing the checksum verification.
D. There is not enough space in flash to hold the image.