Chapter 8
Operating System Hardening
Chapter Objectives
After reading this chapter and completing the exercises, you will be able to do the following:
![]() Properly configure a Windows system for secure operations.
Properly configure a Windows system for secure operations.
![]() Properly configure a Linux system for secure operations.
Properly configure a Linux system for secure operations.
![]() Apply appropriate operating system patches to Windows.
Apply appropriate operating system patches to Windows.
![]() Apply application patches.
Apply application patches.
![]() Securely configure a web browser.
Securely configure a web browser.
Introduction
Protecting the system’s perimeters and subnets via firewalls, proxy servers (or NAT-enabled machines), intrusion-detection systems, honeypots, and other devices is only one part of securing a network. Even installing antivirus software and anti-spyware does not complete a network’s security. To achieve a more secure network, you must perform operating system hardening. This is the process of properly configuring each machine, and especially servers, for the optimum security settings. The word optimum rather than maximum is used for a reason. Maximum security is also the least usable. Optimum security strikes a balance between ease of use and security.
In this chapter you will learn how to properly configure Windows 7, Windows 8/8.1, Windows 10, Linux, and various web browsers. Securely configuring the operating system and its software is a critical step in system security that is frequently ignored. Even relatively naive security administrators often think of installing a firewall or antivirus software, but many fail to harden the individual machines against attacks. Discovering the presence of vulnerabilities allows you to close “open” ports and further restrict “input/output” operations. All of these techniques and procedures are in the overarching area of Risk Management Systems and Information Assurance.
It should be noted that application security is just as important as operating system security. However, there are so many different applications that it is impossible to address secure configuration here, other than to say that you should consult the application documentation and ensure it is securely configured and stays patched/updated. Secure programming is also an important topic, but a completely separate topic outside the scope of this book.
Configuring Windows Properly
Properly configuring Windows (with a focus on Windows 7, 8, and 10) consists of many facets. You must disable unnecessary services, properly configure the registry, enable the firewall, properly configure the browser, and more. Chapter 4, “Firewall Practical Applications,” discussed the Internet connection firewall and the processes of both stateful packet inspection and stateless packet inspection, and a later section of this chapter discusses browser security. For now, let’s go over the other important factors in Windows security configuration.
FYI: What About Windows Server?
Throughout this chapter the examples use Windows 7, 8, and 10. You might wonder whether these issues apply to Windows Server (2008, 2012, and 2016). First and foremost, Windows 10 is the desktop operating system currently supported by Microsoft; Windows 2016 is the current server version. We include Windows 7 because many businesses are still using it.
The second reason for not discussing Windows Server 2016 is that from an operating system hardening perspective, it is virtually identical to Windows 10. Thus most of the recommendations in this chapter will also apply to Windows Server (2008, 2012, or 2016). It is also the case that Microsoft ships its server versions already more securely configured than the desktop versions.
Accounts, Users, Groups, and Passwords
Any Windows system comes with certain default user accounts and groups. These can frequently be a starting point for intruders who want to crack passwords for those accounts and thereby gain entrance onto a server or network. Simply renaming or disabling some of these default accounts can improve your security.
Note
Windows has a tendency to move things in the control panel with each version. Your version (7, 8, 8.1, 10, etc.) might have things in a different location. If you have not already done so, I suggest you pause and take some time to familiarize yourself with the location of utilities in your version of Windows.
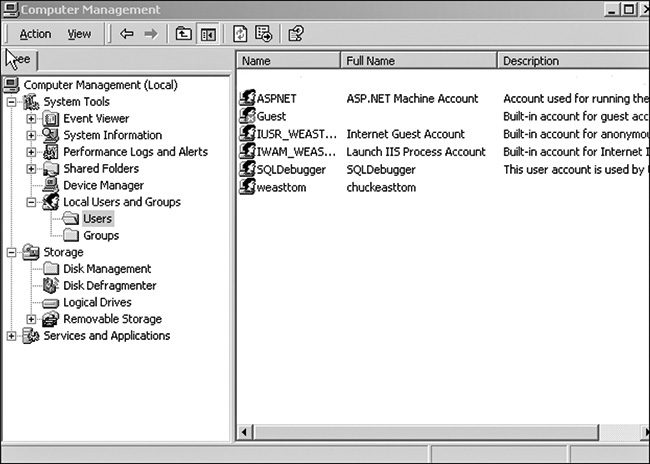
In Windows 7 or Windows 8 you find user accounts by going to Start, Settings, Control Panel, Users and Groups. In Windows 10 go to Start, Settings, and Accounts. Figure 8-1 shows a screen similar to the one you will see.
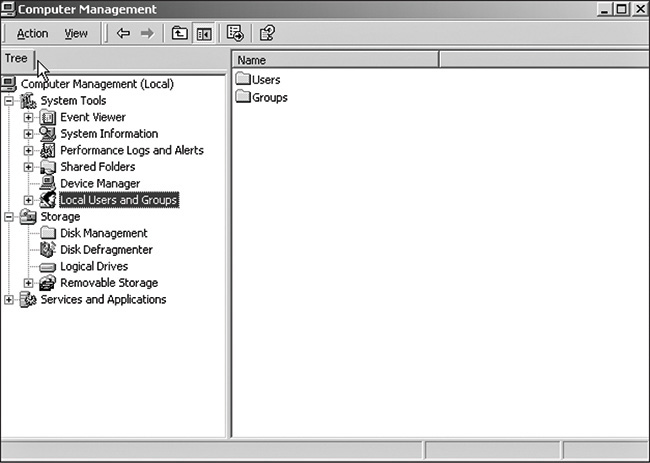
Select the Advanced tab, which takes you to the screen shown in Figure 8-2. Click the Advanced button, which opens the screen shown in Figure 8-3.
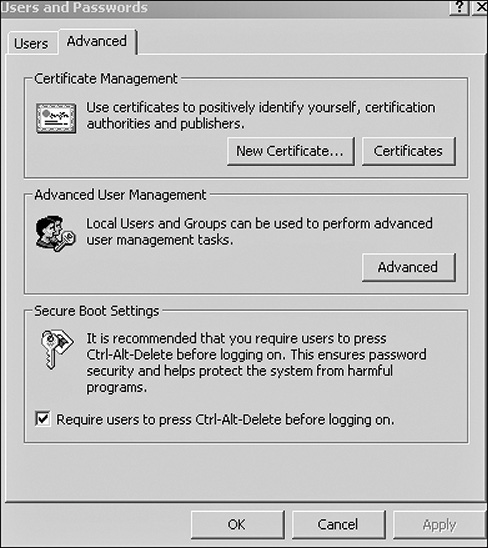
FIGURE 8-2 Manage users and passwords from this dialog box
From here you can alter, disable, or add accounts. The following paragraphs demonstrate how to use this utility to adjust various default accounts.
The Windows 10 Accounts screen is shown in Figure 8-4. From here, you can add accounts, delete accounts, or change accounts.
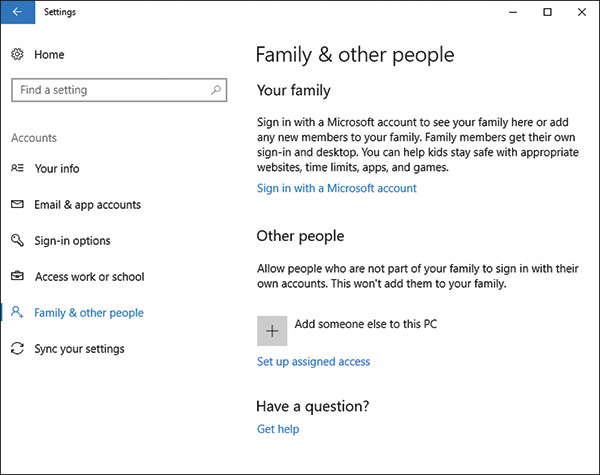
FIGURE 8-4 Accounts in Windows 10
Administrator Accounts
The default administrator account has administrative privileges, and hackers frequently seek to obtain the logon information for an administrator account. Guessing a logon is a two-fold process of first identifying the username, and then the password. Default accounts allow the hacker to bypass the first half of this process.
Administrators should disable this account. If you double-click on any account (recall the Users and Groups utility previously shown in Figure 8-3) you will see a screen much like that shown in Figure 8-5. From here you can disable the default administrator account.
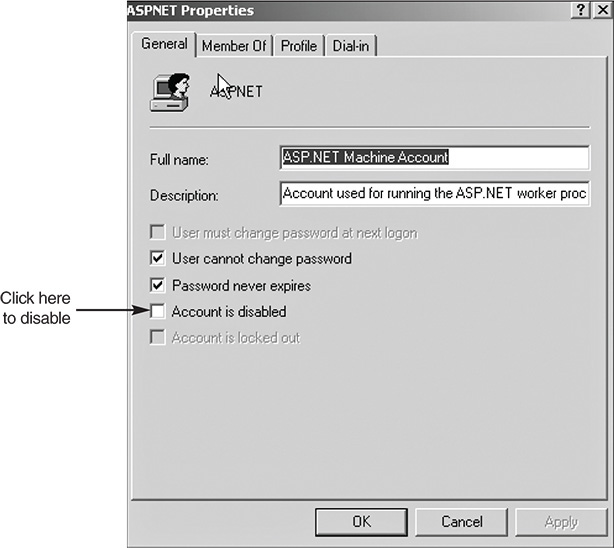
FIGURE 8-5 Disabling the default administrator account
Obviously, having an account with administrative privileges is necessary for maintaining your server. The next step is adding a new account, one with an innocuous name (for example, temp_clerk, receptionist, etc.), and giving that account administrative privileges. Doing so makes a hacker’s task more difficult, as he must first ascertain what account actually has administrative privileges before he can even attempt to compromise that account.
Some experts suggest simply renaming the administrator account, or using an administrator account that has a username that indicates its purpose. That is not the recommendation of this book for the following reasons:
![]() The whole point is that a hacker should not be able to readily tell which username has administrative privileges.
The whole point is that a hacker should not be able to readily tell which username has administrative privileges.
![]() Simply renaming the administrator account to a different name, but one that still indicates its administrative rights, will not help this situation.
Simply renaming the administrator account to a different name, but one that still indicates its administrative rights, will not help this situation.
Other Accounts
We have concentrated on the administrator account because it is the one most often targeted by hackers, but Windows also includes other default user accounts. Applying an equally rigorous treatment to all default accounts is a good idea. Any default account can be a gateway for a hacker to compromise a system. A few accounts that you should pay particular attention to include:
![]() IUSR_Machine name: When you are running IIS, a default user account is created for IIS. Its name is IUSR_ and the name of your machine. This is a common account for a hacker to attempt to compromise. Altering this one in the manner suggested for the administrator account is advisable.
IUSR_Machine name: When you are running IIS, a default user account is created for IIS. Its name is IUSR_ and the name of your machine. This is a common account for a hacker to attempt to compromise. Altering this one in the manner suggested for the administrator account is advisable.
![]() ASP.NET: If your machine is running ASP.NET, a default account is created for web applications. A hacker that is familiar with .NET could target this account.
ASP.NET: If your machine is running ASP.NET, a default account is created for web applications. A hacker that is familiar with .NET could target this account.
![]() Database accounts: Many relational database management systems, such as SQL Server, create default user accounts. An intruder, particularly one who wants to get at your data, could target these accounts.
Database accounts: Many relational database management systems, such as SQL Server, create default user accounts. An intruder, particularly one who wants to get at your data, could target these accounts.
FYI: Alternatives to Disabling the Administrative Account
Another secure option is to leave the default administrator account enabled, but to change it from being a member of the administrator’s group to being a very restricted user account. You must then make sure that none of your administrators use this account. At this point you can simply monitor server logs for attempts to log on to this account. Repeated attempts in a short period of time could mean someone is attempting to breach your system’s security.
Leaving the administrator account enabled with significantly reduced access and monitoring any attempts to use that account provides you with a virtual trap for hackers.
Of course, you must have accounts for all of these and other services. The suggestion here is to ensure that the names of these accounts are not obvious and that default accounts are not used.
When adding any new account, always give the new account’s user or group the least number and type of privileges needed to perform their job, even accounts for IT staff members. Here are a few examples of places to restrict user access/privileges that you might not think of:
![]() A PC technician does not need administrative rights on the database server. Even though she is in the IT department, she does not need access to everything in that department.
A PC technician does not need administrative rights on the database server. Even though she is in the IT department, she does not need access to everything in that department.
![]() Managers may use applications that reside on a web server, but they certainly should not have rights on that server.
Managers may use applications that reside on a web server, but they certainly should not have rights on that server.
![]() Just because a programmer develops applications that run on a server does not mean that he should have full rights on that server.
Just because a programmer develops applications that run on a server does not mean that he should have full rights on that server.
![]() Perhaps this might be another position to reinforce the procedures of RBAC (Role Based Access Control), DAC (Discretionary Access Control), and MAC (Mandatory Access Control).
Perhaps this might be another position to reinforce the procedures of RBAC (Role Based Access Control), DAC (Discretionary Access Control), and MAC (Mandatory Access Control).
These are just a few examples of things to consider when setting up user rights. Remember: Always give the least access necessary for that person to do her job. This concept is often termed least privileges, and is a cornerstone of security.
Setting Security Policies
Setting appropriate security policies is the next step in hardening a Windows server. This does not refer to written policies an organization might have regarding security standards and procedures. In this case the term security policies refers to the individual machines’ policies. When you select Start, Settings, Control Panel, Administrative Tools, you will also note the Local Security Policy. Double-clicking this and selecting Account Policies takes you to the screen shown in Figure 8-6. The various subfolders in the dialog box shown in Figure 8-6 are expanded. Normally when you open this utility they will not be. Note that in Windows 10 you can access this same screen by going to the Run menu and typing gpedit (this is the Local Group Policy Editor utility).
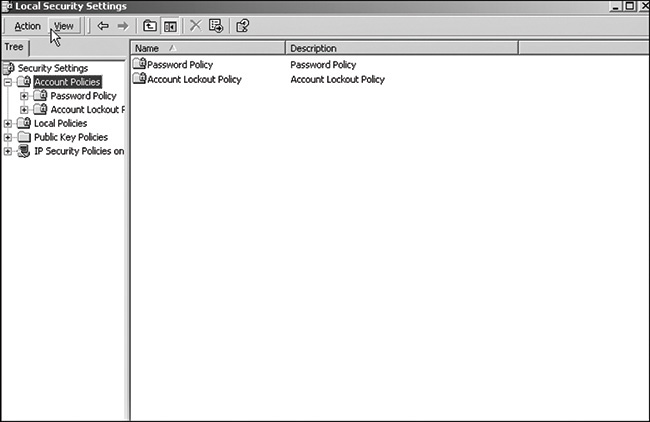
FIGURE 8-6 Local security policies
The first matter of concern is setting secure password policies. The default settings for Windows passwords are not secure. Table 8-1 shows the default password policies. Maximum password age refers to how long a password is effective before the user is forced to change that password. Enforce password history refers to how many previous passwords the system remembers, thus preventing the user from reusing passwords. Minimum password length defines the minimum number of characters allowed in a password. Password complexity means that the user must use a password that combines numbers, letters, and other characters. These are the default security settings for all Windows versions from Windows NT 4.0 forward. If your system is protected within a business environment, the settings at Local Security will be grayed out, indicating you do not have permissions to make changes.
TABLE 8-1 Default Windows Password Policies
Policy |
Recommendation |
Enforce password history |
1 password remembered |
Maximum password age |
42 days |
Minimum password age |
0 days |
Minimum password length |
0 characters |
Passwords must meet complexity requirements |
Disabled |
Store password using reversible encryption for all users in the domain |
Disabled |
The default password policies are not secure enough, but what policies should you use instead? Different experts answer that question differently. Table 8-2 shows the recommendations of Microsoft, the National Security Agency, and the author’s personal recommendations (along with an explanation when they differ significantly from the Microsoft or NSA recommendations).
TABLE 8-2 Password Setting Recommendations
Policy |
Microsoft |
NSA |
Author |
Enforce password history |
3 passwords |
5 passwords |
3 passwords |
Maximum password age |
42 days |
42 days |
60 days |
Minimum password age |
2 days |
2 days |
2 days |
Minimum password length |
8 characters |
12 characters |
A minimum of 12 characters. Longer passwords, in fact pass phrases, are best. |
Passwords must meet complexity requirements |
No recommendation (left to user discretion) |
Yes |
Yes |
Store password using reversible encryption for all users in the domain |
No recommendation (left to user discretion) |
No recommendation |
No recommendation (left to user discretion) |
Developing appropriate password policies depends largely on the requirements of your network environment. If your network stores and processes highly sensitive data and is an attractive target to hackers, you must always skew your policies and settings toward greater security. However, bear in mind that if security measures are too complex, your users will find complying difficult. For example, very long, complex passwords (such as $%Tbx38T@_FgR$$) make your network quite secure, but such passwords are virtually impossible for users to remember. Many users will simply write the password on a note and keep it in a handy but insecure location, such as the top drawer of their desks, a major security problem.
Account Lockout Policies
When you open the Local Security Settings dialog, your options are not limited to setting password policies. You can also set account lockout policies. These policies determine how many times a user can attempt to log in before being locked out, and for how long to lock them out. The default Windows settings are shown in Table 8-3.
These default policies are not secure. Essentially they allow for an infinite number of log-in attempts, making the use of password crackers very easy and virtually guaranteeing that someone will eventually crack one or more passwords and gain access to your system. Table 8-4 provides the recommendations from Microsoft, National Security Agency, and the author.
TABLE 8-3 Windows Default Account Lockout Policy Settings
Policy |
Default Settings |
Account lockout duration |
Not defined |
Account lockout threshold |
0 invalid logon attempts |
Reset account lockout counter after |
Not defined |
TABLE 8-4 Recommended Account Lockout Policies
Policy |
Microsoft |
NSA |
Author |
Account lockout duration |
0, indefinite |
15 hours |
48 hours. If someone is attempting to crack passwords on weekends/holidays, you want the account locked until an administrator is aware of the attempt. |
Account lockout threshold |
5 attempts |
3 attempts |
3 attempts |
Reset account after |
15 minutes |
30 minutes |
30 minutes |
FYI: More Guidelines
Guidelines for Windows Security are available on the following websites. These guidelines apply to all versions of Windows.
![]() National Security Agency: https://www.iad.gov/iad/library/ia-guidance/security-configuration/index.cfm
National Security Agency: https://www.iad.gov/iad/library/ia-guidance/security-configuration/index.cfm
![]() Microsoft Guidelines: https://technet.microsoft.com/en-us/library/cc184906.aspx
Microsoft Guidelines: https://technet.microsoft.com/en-us/library/cc184906.aspx
Some of the links in this chapter are rather long because they take you directly to the item in question. You can always go to the root domain (such as www.microsoft.com) and search for the item in question.
All of these sites provide other perspectives on securing a Windows client or server.
Other Issues
Some account and password issues cannot be handled with computer settings. These involve setting organizational policies regarding user and administrator behavior. Chapter 11, “Security Policies,” discusses such organizational policies in greater depth. For now, simply consider this basic list of the most important organizational security policies:
![]() Users must never write down passwords.
Users must never write down passwords.
![]() Users must never share passwords.
Users must never share passwords.
![]() Administrators must use the least required access rule. That means most users should not have administrative privileges even on their own desktops.
Administrators must use the least required access rule. That means most users should not have administrative privileges even on their own desktops.
FYI: Registry Settings
Incorrect editing of your registry can render parts of your operating system unusable. It can even keep your machine from booting at all. Being careful when you make any changes to the registry and documenting such changes are important. If you are new to registry manipulation it is recommended that you use a lab machine that does not contain any critical data or applications. Misconfiguring the registry so severely that the entire operating system must be reinstalled is possible.
Registry Settings
Secure registry settings are critical to securing a network. Unfortunately, my experience has been that this area is often overlooked by otherwise secure practices. One thing to keep in mind is that if you don’t know what you are doing in the registry, you can cause serious problems. So, if you are not very comfortable with the registry, don’t touch it. Even if you are comfortable making registry changes, always back up the registry before any change.
The Windows Registry is a database used to store settings and options for Microsoft Windows operating systems. This database contains critical information and settings for all the hardware, software, users, and preferences on a particular computer. Whenever users are added, software is installed, or any other change is made to the system (including security policies), that information is stored in the registry.
Registry Basics
The physical files that make up the registry are stored differently depending on which version of Windows you are using. Older versions of Windows (that is, Windows 95 and 98) kept the registry in two hidden files in your Windows directory, called USER.DAT and SYSTEM.DAT. In all versions of Windows since XP, the physical files that make up the registry are stored in %SystemRoot%System32Config. Since Windows 8, the file has been named ntuser.dat. Regardless of the version of Windows you are using, you cannot edit the registry directly by opening and editing these files. Instead you must use a tool, regedit.exe, to make any changes. There are newer tools like regedit32. However, many users find that the older regedit has a more user friendly “find” option for searching the registry. Either one will work.
Although the registry is referred to as a “database,” it does not actually have a relational database structure (like a table in MS SQL Server or Oracle). The registry has a hierarchical structure similar to the directory structure on the hard disk. In fact, when you use regedit, you will note it is organized like Windows Explorer. To view the registry, go to Start, Run, and type regedit. You should see the Registry Editor dialog box, shown in Figure 8-7. Some of the folders in your dialog box might be expanded. If so, simply collapse them so that your registry looks like the one shown in Figure 8-7.
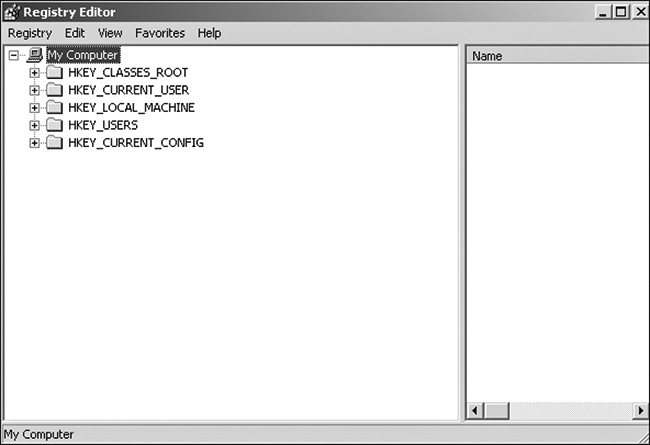
FIGURE 8-7 The Windows Registry hive
Your Registry Editor dialog box will likely have the same five main folders as the one shown in Figure 8-7. Each of these main branches of the registry is briefly described in the following list. These five main folders are the core registry folders. A system might have additions, but these are the primary folders containing information necessary for your system to run.
![]() HKEY_CLASSES_ROOT: This branch contains all of your file association types, OLE information, and shortcut data.
HKEY_CLASSES_ROOT: This branch contains all of your file association types, OLE information, and shortcut data.
![]() HKEY_CURRENT_USER: This branch links to the section of HKEY_USERS appropriate for the user currently logged on to the PC.
HKEY_CURRENT_USER: This branch links to the section of HKEY_USERS appropriate for the user currently logged on to the PC.
![]() HKEY_LOCAL_MACHINE: This branch contains computer-specific information about the type of hardware, software, and other preferences on a given PC.
HKEY_LOCAL_MACHINE: This branch contains computer-specific information about the type of hardware, software, and other preferences on a given PC.
![]() HKEY_USERS: This branch contains individual preferences for each user of the computer.
HKEY_USERS: This branch contains individual preferences for each user of the computer.
![]() HKEY_CURRENT_CONFIG: This branch links to the section of HKEY_LOCAL_MACHINE appropriate for the current hardware configuration.
HKEY_CURRENT_CONFIG: This branch links to the section of HKEY_LOCAL_MACHINE appropriate for the current hardware configuration.
If you expand a branch, you will see its subfolders. Many of these have, in turn, more subfolders, possibly as many as four or more before you get to a specific entry. A specific entry in the Windows Registry is referred to as a key. A key is an entry that contains settings for some particular aspect of your system. If you alter the registry, you are actually changing the settings of particular keys.
This is just a brief overview of the registry. If you intend to do more extensive work with the registry than setting the proper security, you can use the following sources:
![]() 50 Best Windows Registry Hacks: https://www.howtogeek.com/howto/37920/the-50-best-registry-hacks-that-make-windows-better/
50 Best Windows Registry Hacks: https://www.howtogeek.com/howto/37920/the-50-best-registry-hacks-that-make-windows-better/
![]() Windows Registry Tips: http://techtweek.com/windows/all-important-windows-registry-tips-and-tweaks
Windows Registry Tips: http://techtweek.com/windows/all-important-windows-registry-tips-and-tweaks
![]() Microsoft’s Windows Registry support page: https://support.microsoft.com/en-us/help/256986/windows-registry-information-for-advanced-users
Microsoft’s Windows Registry support page: https://support.microsoft.com/en-us/help/256986/windows-registry-information-for-advanced-users
FYI: Secure Registry Settings
Remember that the Windows Registry controls everything about Windows. Therefore, to truly secure Windows, you must configure the registry securely. Unfortunately, the registry’s default settings are not secure. This section describes how to apply secure registry settings on your machines. Chapter 12, “Assessing System Security,” provides more information about secure registry settings in the section on assessing a system. There you will learn about software products available online that notify you of any insecure registry settings on your machine. These tools are sold by third-party vendors and are not part of Windows.
Keep in mind that registry settings can change in different versions of Windows, so it is possible that you might not find one or more of the following settings, or they might be in a slightly different location. To find and check your registry settings for any of these keys, simply expand the appropriate node and work your way down to the specific key. For example, the first one on our list is HKLMSYSTEMCurrentControlSetServicesLanmanServer. You could first expand the LOCAL_MACHINE node, then the SYSTEM node, then the CurrentControlSet node, then the Services node. You should then be able to find the specific registry key you are looking for; in this example, we found LanmanServer. The same process can be applied to find any key; the LanmanServer key was randomly chosen for this example.
Restrict Null Session Access
Null sessions are a significant weakness that can be exploited through the various shares that are on the computer. A null session is Windows’ way of designating anonymous connections. Any time you allow anonymous connections to any server, you are inviting significant security risks. Modify null session access to shares on the computer by adding RestrictNullSessAccess, a registry value that toggles null session shares on or off to determine whether the Server service restricts access to clients logged on to the system account without username and password authentication. Setting the value to 1 restricts null session access for unauthenticated users to all server pipes and shares except those listed in the NullSessionPipes and NullSessionShares entries.
Key Path: HKLMSYSTEMCurrentControlSetServicesLanmanServer
Action: Ensure that it is set to: Value = 1
Restrict Null Session Access Over Named Pipes
The null session access over named pipes registry setting should be changed for much the same reason as the preceding null session registry setting. Restricting such access helps prevent unauthorized access over the network. To restrict null session access over named pipes and shared directories, edit the registry and delete the values, as shown in Table 8-5.
Key Path: HKLMSYSTEMCurrentControlSetServicesLanmanServer
Action: Delete all values
TABLE 8-5 TCP/IP Stack Registry Settings
Key Path |
Recommended Value |
DisableIPSourceRouting |
2 |
EnableDeadGWDetect |
0 |
EnableICMPRedirect |
0 |
EnablePMTUDiscovery |
0 |
EnableSecurityFilters |
1 |
KeepAliveTime |
300,000 |
NoNameReleaseOnDemand |
1 |
PerformRouterDiscovery |
0 |
SynAttackProtect |
2 |
TcpMaxConnectResponseRetransmissions |
2 |
TcpMaxConnectRetransmissions |
3 |
TCPMaxPortsExhausted |
5 |
Restrict Anonymous Access
The anonymous access registry setting allows anonymous users to list domain user names and enumerate share names. It should be shut off. The possible settings for this key are:
![]() 0—Allow anonymous users
0—Allow anonymous users
![]() 1—Restrict anonymous users
1—Restrict anonymous users
![]() 2—Allow users with explicit anonymous permissions
2—Allow users with explicit anonymous permissions
Key Path: HKLMSYSTEMCurrentControlSetControlLsa
Action: Set Value = 2
TCP/IP Stack Settings
A number of registry settings affect how the TCP/IP stack handles incoming packets. Setting these properly can help reduce your vulnerability to DoS attacks. This process, stack tweaking, is described in Chapter 2, “Types of Attacks.” Because these settings are all related and are found in the same key path, they are shown together in Table 8-5.
As Table 8-5 shows, most of these settings prevent the redirection of packets, change the timeout on connections, and generally alter how Windows handles TCP/IP connections. You can find more details about Microsoft’s recommendations for setting the TCP/IP stack registry settings at its website: https://msdn.microsoft.com/en-us/library/ff648853.aspx.
FYI: Default Shares
The Windows operating system opens default shared folders on each installation for use by the system account. Because they are default shares, they are identical for all Windows machines, with identical permissions. These default shares can be used by a skilled hacker as a starting point for intruding upon your machine. You can disable the default Administrative shares two ways:
1. Stop or disable the Server service, which removes the ability to share folders on your computer. (However, you can still access shared folders on other computers.)
2. Edit the registry.
To change the default share folders setting in the registry, go to HKEY_Local_MachineSYSTEMCurrentControlSetServicesLanmanServerParameters. For servers, edit AutoShareServer witha value of 0. For workstations, edit the key AutoShareWks. If for some reason, your WindowsRegistry does not have it, just add it: https://social.technet.microsoft.com/Forums/windows/en-US/c9d6b1c2-1059-4a8a-a6bd-56cc34104faa/disable-administrator-share?forum=w7itpronetworking.
For more information on default shares or to view security advisories about them, consult the following websites:
Remote Access to the Registry
Remote access to the registry is another potential opening for hackers. The Windows XP registry editing tools support remote access by default, but only administrators should have remote access to the registry. Fortunately, later versions of Windows turned this off by default. In fact some experts advise that there should be no remote access to the registry for any person. This point is certainly debatable. If your administrators frequently need to remotely alter registry settings, then completely blocking remote access to them will cause a reduction in productivity of those administrators. However, completely blocking remote access to the registry is certainly more secure. To restrict network access to the registry:
1. Add the following key to the registry: HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecurePipeServerswinreg.
2. Select winreg, click the Security menu, and then click Permissions.
3. Set the Administrator’s permission to Full Control, make sure no other users or groups are listed, and then click OK.
Recommended Value = 0
Other Registry Settings
Adjusting the previously discussed registry settings will help you avoid some of the most common security flaws in the default Windows Registry settings and will certainly increase the security of any server. However, for maximum security an administrator must take the time to carefully study the Windows Registry for any additional areas that can be made more secure. A few of the additional settings you might want to look into include:
![]() Restricting anonymous access to the registry
Restricting anonymous access to the registry
![]() NTLMv2 Security (affects security of passwords being sent to the server)
NTLMv2 Security (affects security of passwords being sent to the server)
![]() KeepAlive (affects how long to keep a connection active)
KeepAlive (affects how long to keep a connection active)
![]() SynAttackProtect (protects against a very specific type of SYN attack)
SynAttackProtect (protects against a very specific type of SYN attack)
Services
A service is a program that runs without direct intervention by the computer user. In Unix/Linux environments, these are referred to as daemons. Many items on your computer are run as services. Internet Information Services, FTP Service, and many system services are good examples. Any running service is a potential starting point for a hacker. Obviously, you must have some services running for your computer to perform its required functions. However, there are services your machine does not use. If you are not using a service, it should be shut down.
You should be cautious when shutting down services so that you do not inadvertently shut down a service that you need. Always check with your operating system documentation. The rule of thumb is that if you are not sure, do not touch it.
Shutting Down a Service in Windows
Shutting down a service in Windows is relatively easy. In our example we will shut down the FTP service on a machine that does not require FTP.
Go to Start, select Settings, and choose Control Panel. Double-click Administrative Tools, and then double-click Services. You should see the Services dialog box, which looks similar to the one shown in Figure 8-8.
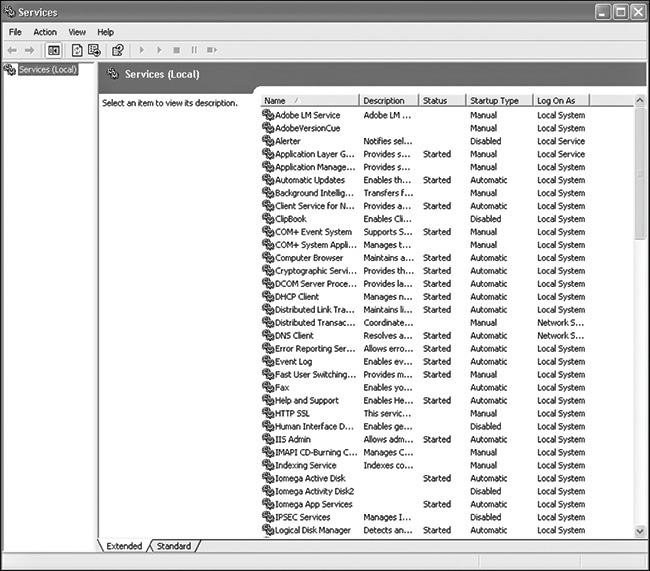
FIGURE 8-8 Services
The Services dialog box shows all services installed on your machine, whether they are running or not. Notice that the dialog box also displays information about whether a service is running, whether it starts up automatically, and so forth. In Windows 7 and beyond, more information can be seen by selecting an individual service. When you double-click on an individual service, you see a dialog box similar to Figure 8-8, which gives you detailed information about the service and enables you to change the service’s settings. In Figure 8-9, we are examining the FTP service on a machine that does not require it.
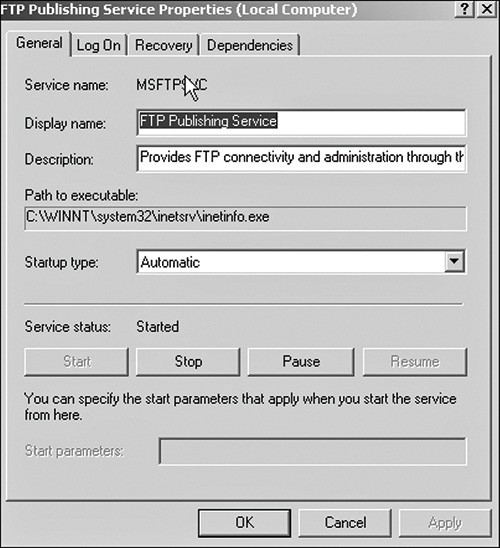
FIGURE 8-9 FTP services
FYI: Dependencies
We are going to turn off the FTP service; but before you ever turn off any service, click on the Dependencies tab to see whether other services depend on the one you are about to shut off. If other services depend on that service, you will then be causing them to malfunction by shutting it down.
In this particular case there are no other dependencies, so you can go to the General tab and do two things: Change the Startup type option to Disabled, and then click the Stop button. When you’re done, the screen will show the status as disabled. The service is now shut down.
Shutting down unneeded services is an essential and very basic part of hardening an operating system. Every running service is a possible avenue for a hacker or a virus to get to your machine, so the rule for services is: If you don’t need it, shut it down. Chapter 12 discusses utilities that scan systems for vulnerabilities. Many of these utilities will point out running services and open ports.
Starting and stopping services from the command prompt is also possible. Many administrators prefer command prompts because it is often faster than going through several layers of the Windows graphical user interface. The syntax is quite simple:
net start servicename
or
net stop servicename
For example:
net stop messenger net start messenger
FYI: Erroneous Information on Net Stop
When writing this book I actually found more than one website that stated that you could not start or stop a service from the command prompt. This is inaccurate, but has somehow become somewhat of an urban legend among some Windows users. The following documentation from Microsoft’s own website confirms that you can indeed start and stop a service from the command prompt:
Port Filtering and Firewalls in Windows
Chapters 4 and 5 discuss the Windows Firewall. Turning on the Windows port filters is a basic part of operating system hardening. The instructions for doing this have been previously given in Chapters 4 and 5 and will be explored again in exercises at the end of this chapter.
Encrypting File System
Beginning with Windows 2000, the Windows operating system has offered the Encrypting File System (EFS), which is based on public key encryption and takes advantage of the CryptoAPI architecture in Windows 2000. This still exists in Windows 7, 8, and 10; however, with the later versions of Windows, EFS is only available in the upper-end editions of Windows such as Windows Professional. With this system, each file is encrypted using a randomly generated file encryption key, which is independent of a user’s public/private key pair; this method makes the encryption resistant to many forms of cryptoanalysis-based attacks. For our purposes the exact details of how EFS encryption works are not as important as the practical aspects of using it.
User Interaction
The default configuration of EFS enables users to start encrypting files with no administrator effort. EFS automatically generates a public key pair and file encryption certificate for file encryption the first time a user encrypts a file.
File encryption and decryption is supported per file or for an entire folder. Folder encryption is transparently enforced. All files and folders created in a folder marked for encryption are automatically encrypted. Each file has a unique file encryption key, making it safe to rename. If you move a file from an encrypted folder to an unencrypted folder on the same volume, the file remains encrypted. However, if you copy an unencrypted file into an encrypted folder, the file state will change. The file becomes encrypted. Command-line tools and administrative interfaces are provided for advanced users and recovery agents.
FYI: What If a User Leaves?
Users might encrypt a file and then be unavailable to decrypt it. They might become unavailable due to leaving the company, illness, or other reasons. Fortunately, EFS does give administrators a method by which they can recover the encryption key used to encrypt files, and thereby decrypt them. EFS allows recovery agents to configure public keys that are used to recover encrypted data if a user leaves the company. Only the file encryption key is available using the recovery key, not a user’s private key. This ensures that no other private information is revealed to the recovery agent.
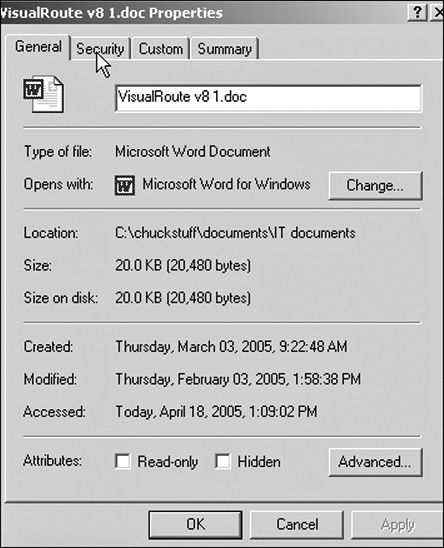
The best thing about EFS is that it is virtually transparent to the user. You don’t have to decrypt a file to open it and use it. EFS automatically detects an encrypted file and locates a user’s file encryption key from the system’s key store. However, if the file is moved from the originating computer to another computer, a user trying to open it will find it is encrypted. The following steps will allow you to encrypt any file you want:
1. Locate the file or folder you want to encrypt (using either Windows Explorer or My Computer/This PC). Right-click on that file and select Properties. The Properties dialog box, similar to the one shown in Figure 8-10, appears.
2. Click on the Advanced button to access an option that you can check to encrypt the file, as shown in Figure 8-11.

FIGURE 8-11 Encrypting a file
3. Click Encrypt Contents to Secure Data.
After you have done this, your file or folder is now encrypted. As long as the same user on the same machine opens the file, it will be decrypted automatically. A hacker who transfers the file to his or her own system (or an employee attempting industrial espionage, who takes the file home on a disk) will find it is encrypted. Because EFS is built into Windows, costs nothing extra, and is so easy to use, it is difficult to find any reason not to use it. If you want more details, the following websites should be helpful to you:
![]() ServerWatch review of EFS: www.serverwatch.com/tutorials/article.php/2106831
ServerWatch review of EFS: www.serverwatch.com/tutorials/article.php/2106831
![]() A utility for retrieving EFS encryption keys: www.lostpassword.com/efs.htm
A utility for retrieving EFS encryption keys: www.lostpassword.com/efs.htm
FYI: EFS in Windows Server
Encrypting File System was introduced in Windows 2000. However, it was continued in Windows 8, 8.1, and 10 as well as Windows Server 2008, Server 2012, and Server 2016.
Security Templates
We have been discussing a number of ways for making a Windows system more secure, but exploring services, password settings, registry keys, and other tools can be a daunting task for the administrator who is new to security. Applying such settings to a host of machines can be a tedious task for even the most experienced administrator. The best way to simplify this aspect of operating system hardening is to use security templates. A security template contains hundreds of possible settings that can control a single or multiple computers. Security templates can control areas such as user rights, permissions, and password policies, and they enable administrators to deploy these settings centrally by means of Group Policy Objects (GPOs).
Security templates can be customized to include almost any security setting on a target computer. A number of security templates are built into Windows. These templates are categorized for domain controllers, servers, and workstations. These security templates have default settings designed by Microsoft. All of these templates are located in the C:WindowsSecurityTemplates folder. The following is a partial list of the security templates that you will find in this folder:
![]() Hisecdc.inf: This template is designed to increase the security and communications with domain controllers.
Hisecdc.inf: This template is designed to increase the security and communications with domain controllers.
![]() Hisecws.inf: This template is designed to increase security and communications for client computers and member servers.
Hisecws.inf: This template is designed to increase security and communications for client computers and member servers.
![]() Securedc.inf: This template is designed to increase the security and communications with domain controllers, but not to the level of the High Security DC security template.
Securedc.inf: This template is designed to increase the security and communications with domain controllers, but not to the level of the High Security DC security template.
![]() Securews.inf: This template is designed to increase security and communications for client computers and member servers.
Securews.inf: This template is designed to increase security and communications for client computers and member servers.
![]() Setup security.inf: This template is designed to reapply the default security settings of a freshly installed computer. It can also be used to return a system that has been misconfigured to the default configuration.
Setup security.inf: This template is designed to reapply the default security settings of a freshly installed computer. It can also be used to return a system that has been misconfigured to the default configuration.
Installing security templates simplifies network security for the administrator. You will have the opportunity to walk through the process of installing a security template in one of the end-of-chapter exercises.
Configuring Linux Properly
An in-depth review of Linux security would be a lengthy task indeed. One reason is the diversity of Linux setups. Users could be using Debian, Red Hat, Ubuntu, or other Linux distributions. Some might be working from the shell, while others work from some graphical user interfaces such as KDE or GNOME (for Windows users not familiar with Linux you might want to consult my book Moving from Windows to Linux). Fortunately, many of the same security concepts that apply to Windows can be applied to Linux. The only differences lie in the implementation, as explained in the following list:
![]() User and account policies should be set up the same in Linux as they are in Windows, with only a few minor differences. These differences are more a matter of using different names in Linux than in Windows. For example, Linux does not have an administrator account; it has a root account.
User and account policies should be set up the same in Linux as they are in Windows, with only a few minor differences. These differences are more a matter of using different names in Linux than in Windows. For example, Linux does not have an administrator account; it has a root account.
![]() All services (called daemons in Linux) not in use should be shut down.
All services (called daemons in Linux) not in use should be shut down.
![]() The browser must be configured securely.
The browser must be configured securely.
![]() You must routinely patch the operating system.
You must routinely patch the operating system.
In addition to these tactics that are common to Windows and Linux, a few approaches are different for the two operating systems:
![]() No application should run as the root user unless absolutely necessary. Remember that the root user is equivalent to the administrator account in Windows. Also remember that all applications in Linux run as if started by a particular user, and therefore having an application run as root user would give it all administrative privileges.
No application should run as the root user unless absolutely necessary. Remember that the root user is equivalent to the administrator account in Windows. Also remember that all applications in Linux run as if started by a particular user, and therefore having an application run as root user would give it all administrative privileges.
![]() The root password must be complex and must be changed frequently. This is the same as with Windows administrator passwords.
The root password must be complex and must be changed frequently. This is the same as with Windows administrator passwords.
![]() Disable all console-equivalent access for regular users. This means blocking access to programs such as shutdown, reboot, and halt for regular users on your server. To do this, run the following command: [root@kapil /]# rm -f /etc/security/console.apps/<servicename>, where <servicename> is the name of the program to which you want to disable console-equivalent access.
Disable all console-equivalent access for regular users. This means blocking access to programs such as shutdown, reboot, and halt for regular users on your server. To do this, run the following command: [root@kapil /]# rm -f /etc/security/console.apps/<servicename>, where <servicename> is the name of the program to which you want to disable console-equivalent access.
![]() Hide your system information. When you log in to a Linux box, it displays by default the Linux distribution name, version, kernel version, and the name of the server. This information can be a starting point for intruders. You should just prompt users with a “Login:” prompt.
Hide your system information. When you log in to a Linux box, it displays by default the Linux distribution name, version, kernel version, and the name of the server. This information can be a starting point for intruders. You should just prompt users with a “Login:” prompt.
To do this, edit the /etc/rc.d/rc.local file and place # in front of the following lines, as shown:
# This will overwrite /etc/issue at every boot. So, make any changes you # want to make to /etc/issue here or you will lose them when you reboot. #echo "" > /etc/issue #echo "$R" >> /etc/issue #echo "Kernel $(uname -r) on $a $(uname -m)" >> /etc/issue # #cp -f /etc/issue /etc/issue.net #echo >> /etc/issue Remove the following files: "issue.net" and "issue" under "/etc" directory: [root@kapil /]# rm -f /etc/issue [root@kapil /]# rm -f /etc/issue.net
In general, security concepts apply regardless of operating system. However, truly hardening any operating system requires a certain level of expertise with that particular operating system.
The following websites provide information useful for helping you secure your Linux server:
![]() Linux Security Administrators Guide: www.linuxsecurity.com/docs/SecurityAdminGuide/SecurityAdminGuide.html
Linux Security Administrators Guide: www.linuxsecurity.com/docs/SecurityAdminGuide/SecurityAdminGuide.html
FYI: Patch Conflicts
A patch could possibly conflict with some software or settings on your system. To avoid these conflicts, you should first apply patches to a test machine to ensure no conflicts exist before you apply them to production machines.
Patching the Operating System
From time to time, security flaws are found in operating systems. As software vendors become aware of flaws, they usually write corrections to their code, known as patches or updates. Whatever operating system you use, you must apply these patches as a matter of routine. Windows patches are probably the most well-known, but patches can be released for any operating system. You should patch your system any time a critical patch is released. You might consider scheduling a specific time simply to update patches. Some organizations find that updating once per quarter or even once per month is necessary.
For Windows you can go to www.microsoft.com. On the left-hand side you should notice a link that says Update Windows. If you click on it, you can scan your machine for missing patches and download them from the website. Red Hat offers a similar service for Red Hat Linux users. On the website www.redhat.com/security/, users can scan for updates.
Configuring Browsers
Most computers, including corporate workstations, are used to access the Internet. This means that proper browser configuration is absolutely essential for hardening a system. The Internet is probably the single greatest threat to an individual system or a corporate network. Safe use of the Internet is critical. This section describes how to set Internet Explorer for safe Internet use.
Securing Browser Settings for Microsoft Internet Explorer
Some experts claim that Internet Explorer simply is not a secure browser. We won’t spend time engaging in the Internet Explorer versus Chrome versus Mozilla debate. And Microsoft has since introduced the Edge Browser, though many users still use Internet Explorer. Because many people use Internet Explorer, you must understand how to make it as secure as possible.
1. Open Microsoft Internet Explorer.
2. Select Tools on the menu bar, and then select Internet Options. A screen like the one shown in Figure 8-12 appears.
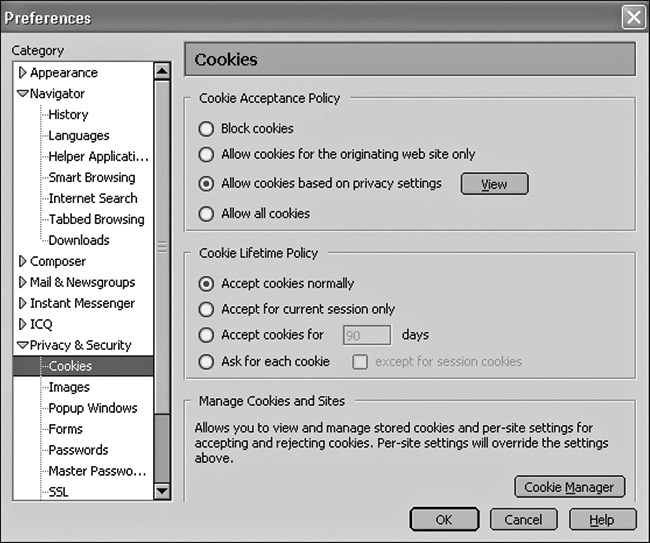
FIGURE 8-12 Internet Explorer options
The Internet Options window includes a Privacy tab and a Security tab. We will discuss both of these tabs and the settings you should select.
Privacy Settings
With spyware a growing problem, privacy settings are as important to operating system hardening as security settings. Clicking on the Advanced button allows you to alter how your browser handles cookies. Unfortunately, surfing the web without accepting some cookies is difficult. The following settings are recommended:
![]() Block third-party cookies
Block third-party cookies
![]() Prompt for first-party cookies
Prompt for first-party cookies
![]() Always allow session cookies
Always allow session cookies
These settings will help you avoid some of the problems associated with cookies. You might also want to click the Edit button and set up the browser to allow cookies from certain sites and to never allow cookies from others.
Security Settings
Security settings are more complex than privacy settings, and there are many more security options to select. You can simply choose the default levels of low, medium, high in your browser, but most security-conscious administrators use the Custom button to set up security specific to their organization. When you select Custom, a dialog box like the one shown in Figure 8-13 appears. We will not discuss every single setting, but will explain many of the more important ones.
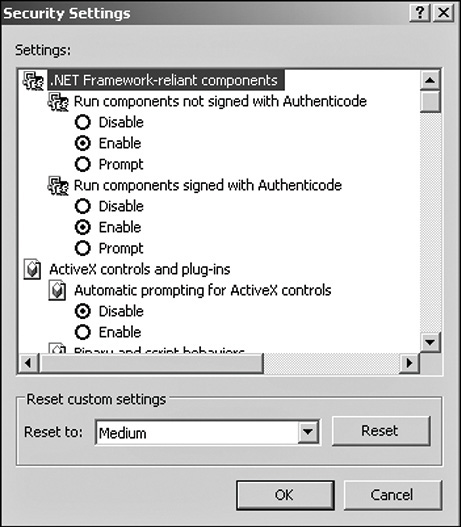
FIGURE 8-13 Internet Explorer custom security settings
As you can see, many different settings are available for you to work with. Table 8-6 summarizes the most important ones and the recommended settings for each.
TABLE 8-6 Internet Explorer Custom Security Settings
Setting |
Purpose |
Recommendation |
Run components not signed with Authenticode |
Allows unsigned software components to execute on your system. |
At a minimum set this to prompt you, but consider disabling it altogether. |
Run components signed with Authenticode |
Allows signed software components to execute on your system. |
Prompt. |
Download Signed ActiveX |
Allows ActiveX components that are signed to be downloaded automatically to your system. |
Prompt. |
Download Unsigned ActiveX |
Allows ActiveX components that are not signed to be automatically downloaded to your system. |
Prompt. You might think disable, but many Flash animations are not signed, and if you simply disable you will not be able to see those. |
Initialize and script ActiveX controls not marked as safe |
Allows ActiveX components to run scripts. |
Disable is recommended, but at least prompt. |
Script ActiveX controls marked safe |
Allows those ActiveX components to run scripts. |
Prompt. |
Downloads (font, file, etc.) |
Downloads files, fonts, etc. that a Web page needs. |
Prompt. |
Java permissions |
This setting simply allows you to determine what a Java applet can or cannot do on your system. Java applets can be a vehicle for malicious code, but all applets need to perform some actions on your system. |
High safety. |
All others |
This is the catchall for miscellaneous non-critical items that don’t fit in elsewhere. These various settings are not as critical to safety as the ones previously discussed. |
You can always have prompts if you do not want to outright disable something. In most cases simply disabling all settings will render some websites unviewable, so for practical purposes the “prompt before...” setting is preferred. |
Because the web is often the weakest part in an organization’s security, having secure browser settings is critical to operating system security and to network security in general.
Other Browsers
In addition to Internet Explorer and Edge, other browsers are available, including Mozilla Firefox, Opera, Safari (Mac OS X), Chrome, and IceWeasel (Linux only, default is Kali Linux). Each of these have different methods for setting up security, but the same principles that hold true for Explorer also apply to these browsers: Limit cookies, do not allow ActiveX components to run without your knowledge, and do not allow any scripts to execute without your knowledge. If you apply the same principles to other browsers, you should be able to achieve similar security to what you can have with Internet Explorer.
Summary
Operating system hardening is a critical part of network security, and it has many facets. It involves securing the operating system, applying patches, using appropriate security settings, and securing your browser. All of these factors must be addressed in order to secure a machine.
Careful configuration of the operating system can make many hacking techniques more difficult. It can also make a system more resistant to DoS attacks. Setting up appropriate policies for users and accounts can make hacking into those accounts much more difficult. Policies should cover issues such as appropriate password length, password type, and password age/history.
With Windows you can also use the Encrypted File System to protect your data should it be moved off of your system. EFS was first introduced in Windows 2000 and has continued through to today. It is a valuable tool that can and should be used to protect any sensitive data.
With any version of Microsoft Windows, proper registry settings are key to security. The registry is the heart and soul of the Microsoft Windows operating system, and failure to address proper registry settings will leave gaping holes in security.
Proper configuration of the browser makes a system less susceptible to malware. Limiting cookies can help ensure that privacy is protected. Blocking browsers from executing scripts or any active code without your knowledge is a critical step for protecting a system from malware.
Test Your Skills
MULTIPLE CHOICE QUESTIONS
1. What does disabling the default administrator account and setting up an alternative account accomplish?
A. Makes it more difficult for someone to guess the log-on information
B. Keeps administrators conscious of security
C. Allows closer management of administrator access
D. Makes the password stronger
2. What level of privileges should all users have?
A. Administrator
B. Guest
C. Most privileges possible
D. Least possible
3. What minimum password length does the NSA recommend?
A. 6
B. 8
C. 10
D. 12
4. What maximum password age does Microsoft recommend?
A. 20 days
B. 3 months
C. 1 year
D. 42 days
5. What account lockout threshold does the NSA recommend?
A. 5 tries
B. 3 tries
C. 4 tries
D. 2 tries
6. Which of the following most accurately describes the registry?
A. A relational database containing system settings
B. A database containing system settings
C. A database where software is registered
D. A relational database where software is registered
7. What is changing the TCP/Settings in the registry called?
A. Stack tweaking
B. Stack altering
C. Stack compression
D. Stack building
8. What type of encryption does EFS utilize?
A. Single key
B. Multi-alphabet
C. Public key encryption
D. A secret algorithm proprietary to Microsoft
9. What happens if you copy an unencrypted file into an encrypted folder?
A. It remains unencrypted.
B. The folder becomes unencrypted.
C. Nothing happens.
D. The file becomes encrypted.
10. Which of the following templates is used to provide the most security for the domain controllers?
A. Hisecdc.inf
B. Securedc.inf
C. Hisecws.inf
D. Sectopdc.inf
11. Which of the following is a security recommendation for Linux not common to Windows?
A. Shut down all services that you are not using (called daemons in Linux).
B. Configure the browser securely.
C. Routinely patch the operating system.
D. Disable all console-equivalent access for regular users.
12. What is the rule for unused services on any computer?
A. Turn them off only if they are critical.
B. Turn them off.
C. Monitor them carefully.
D. Configure them for minimal privileges.
13. What operating systems require periodic patches?
A. Windows
B. Linux
C. All
D. Macintosh
14. What is the minimum secure setting in Internet Explorer for Run components not signed with Authenticode?
A. Disable
B. Enable
C. Forbid
D. Prompt
15. What is the recommended secure setting in Internet Explorer for Initialize and script ActiveX controls not marked as safe?
A. Disable
B. Enable
C. Forbid
D. Prompt
EXERCISES
EXERCISE 8.1: User Accounts and Password Policies
Note: This exercise is best done with a lab computer, not a machine actually in use. Following the guidelines given in this chapter, accomplish the following tasks:
1. Create a new account with administrative privileges.
2. Disable all default accounts, or if they cannot be disabled, change them to the lowest possible permissions.
3. Implement the NSA recommendations for password policies and account lockout policies.
EXERCISE 8.2: Secure Registry Settings
Note: This exercise should be done on a laboratory Windows machine, not on one in normal use. Using the guidelines given in the chapter, check your machine’s settings to see that the following recommendations are implemented:
![]() Restrict null session access.
Restrict null session access.
![]() Restrict anonymous access.
Restrict anonymous access.
![]() Change default shares.
Change default shares.
![]() Restrict null session access over named pipes.
Restrict null session access over named pipes.
Note: This exercise should be done on a laboratory machine, not one in normal use.
Following the guidelines given in the chapter, change the registry settings to make DoS attacks more difficult.
EXERCISE 8.4: Installing Security Templates
This exercise should be done on a laboratory Windows machine, not on one in normal use. By following the steps given here, you should be able to apply a security template to a Windows 7 or XP machine. You may use one of the default templates mentioned in the chapter or one you download from a website of your choice.
1. From the command prompt, or from Start, Run, type MMC. A screen like the one shown in Figure 8-14 appears.
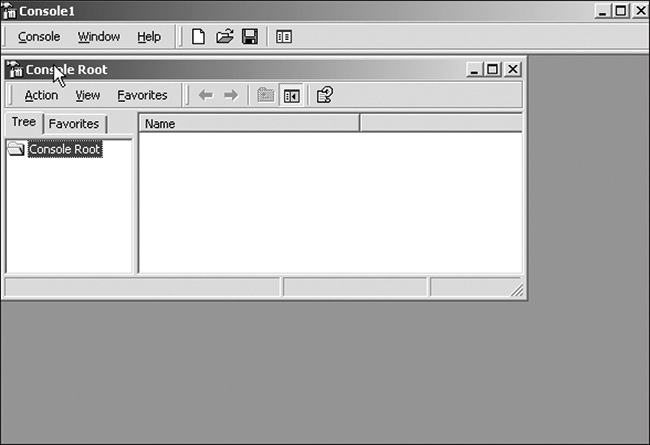
FIGURE 8-14 The MMC console
2. Go to the drop-down menu Console and choose Add/remove console.
3. When you click the Add/Remove snap-in you can select a number of consoles. Find and select Security Configuration and Analysis.
4. After you have added this to the console, you can right-click on it and choose Open Database. Then give the database any name you like. When you press Enter, your dialog will change to display a list of all templates. Select the one you want.
Using a laboratory Linux machine (any distribution will work) and the data presented in this chapter, accomplish the following:
1. Ensure that user accounts are set up securely.
2. Shut down unused and unneeded daemons.
3. Apply the Linux-specific settings given in this chapter.
EXERCISE 8.6: Securing Microsoft Internet Explorer
Using a laboratory computer, secure Microsoft Internet Explorer by following the steps given here:
1. Block all unsigned ActiveX components.
2. Limit cookies to only first-party and session cookies.
3. Block all scripting.
EXERCISE 8.7: Patching Windows
Using a laboratory computer, preferably one that has not been patched in quite some time:
1. Go to www.microsoft.com.
2. Scan for patches.
3. Update all patches, and document the patches you update.
PROJECTS
PROJECT 8.1: Account and Password Settings
This chapter provides recommendations on accounts and passwords from the NSA, Microsoft, and the author. Using the web (including but not limited to resources identified in this chapter), find recommendations from some other reliable source (CERT, SANS, any of the security certification vendors, etc.). Write a brief paper discussing those recommendations, paying particular attention to areas in which they differ from the recommendations given in this chapter.
PROJECT 8.2: Registry Settings
Note: This project is appropriate either for students with a strong understanding of the registry or perhaps as a group project.
Write about at least three additional registry settings you think should be modified to create a more secure Windows operating system. Explain your reasons fully.
PROJECT 8.3: Encrypted File System
Using the web or other resources, find out specifics about the Encrypted File System that is part of Windows. Describe this file system, and any strengths and any weaknesses you find.