6 ◾ Official (ISC)
2
® Guide to the ISSMP® CBK®
© 2011 by Taylor & Francis Group, LLC
Within the same organization, DHS, internal groups with dierent goals and
objectives exist; thus their systems will have dierent security requirements.
Organizational goals are very specic to each internal element of an organiza-
tion. Goals are statements that tell what the system is intended to accomplish.
Goals can dene the system’s purpose and include timelines and metrics. Examples
of goals are the following:
◾ Provide information to a specic group or everyone.
◾ Share research information with other researchers.
◾ Pass sensitive or classied information only to authorized systems.
◾ Sell a product to the healthcare organizations or everyone.
◾ Allow gamblers to gamble over the Internet from their PCs.
◾ Connect people who need organs to newly harvested organs.
◾ Command the release of a nuclear weapon onto a specic target.
Because the types of security needed for a specic system vary depending on the
organization’s mission, goals, and objectives, it is critical for the ISSMP to identify
these from the very beginning of the eorts in building the systems information
system security plan.
Business Functions
In commercial businesses, both for prot and not for prot, there are internal
groups that support dierent business functions, i.e., accounting, sales, produc-
tion, marketing, research and development (R&D), human resources (HR), legal,
and so forth. Each function’s requirements have dierent security requirements
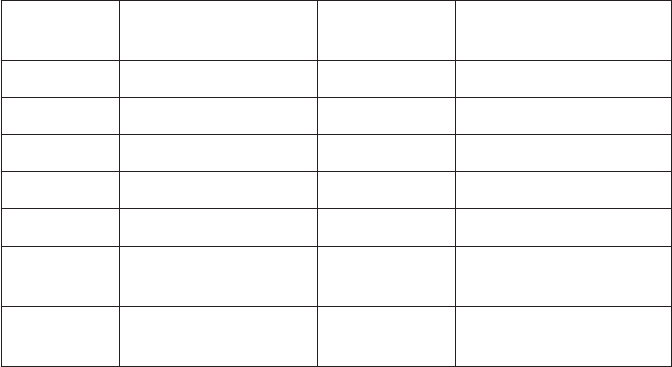
because each has dierent goals and objectives. Table1.1 provides an example of
Table1.1 Business Function Impact on Security Requirements
Functional
Group
Internet Access
Requirement
Security
Requirements
Security Requirement
Justification
Accounting Customers/banks Strong Payroll/privacy/financial
Sales Everyone Little Sensitive client lists
Production Suppliers None Ordering parts
Marketing Everyone None Promotional activities
R&D Everyone Moderate Intellectual property
HR Recruiters, recruits,
insurance companies
Moderate Privacy information
Legal Other lawyers Moderate Corporate sensitive
information
Enterprise Security Management Practices ◾ 7
© 2011 by Taylor & Francis Group, LLC
how a functional group’s system security requirements change just by the group’s
need to access the Internet.
Group Business Processes
Also, within each of these functions the ISSMP must be aware of the specic busi-
ness processes and types of information that support and are produced by the sys-
tem. e things that the ISSMP needs to understand about business processes are
as follows:
Who is in charge and manages the business?
Who is responsible overall for controlling the system’s operations and resources?
How does the business work?
What is the determination of success: input, output, prot, number of customers,
and so forth?
How is the information entered?
Who receives or reviews it?
Who does what with it (change, consolidate, delete, store, transmit, etc.)?
To whom is information transmitted and from where and why?
Are there any product or service providers?
Are there any external or internal customers or buyers?
Are there any management reviews and approvals required in the processes?
Who does the review and approvals and what is approved?
How fast do these actions need to happen?
What is the impact if they do not happen?
Who provides oversight and how often?
e above list is not a complete list, but it is an excellent start. As the review is
conducted, more questions will become obvious as the ISSMP tries to gain solid
insight into the business the system supports or will be supporting. With a full
understanding of the business process, the ISSMP can determine things such as
◾ What is the ow of the information?
◾ Who communicates what and with whom?
◾ What privileges will each person require?
◾ Who drafts requests and who approves them?
◾ How critical are the individual system components and their capabilities to
supporting the success of the organization?
◾ What information types and sensitivities are being processed in the system?
◾ Who are the providers and what agreements are in place or are needed?
◾ Who are the customers and what are their capabilities and expectations?
◾ Who is the owner of the system?
◾ Who will be the ultimate person to accept any residual risk and authorize the
system to become operational or continue to operate?
8 ◾ Official (ISC)
2
® Guide to the ISSMP® CBK®
© 2011 by Taylor & Francis Group, LLC
e above are all key pieces of information required for the ISSMP to ensure that
the most eective security is applied to the system. Some people may say that this
is the job of a systems analyst and they would be right, but it is recommended that
the ISSMP work closely with the systems analysts and designers to ensure that secu-
rity is considered during the entire development process.
Identity Management
e information collected has a major impact on the security needs of the system,
specically in the area of identity management, by identifying where the concepts
of “least privileges” and “role-based security” can be applied. Both of these concepts
are demonstrated in the following example:
There are three individuals who work in the payments section of a major corpora-
tion. Mary is the supervisor, who oversees the efforts of Sally and John. Sally and
John draft fund transfers from banks to pay corporate bills. Mary is the only one
who can authorize and make the transfers online. Each bank has a unique method
of authenticating Mary prior to her making a money transfer, i.e., one-time pass-
words and challenge-and-response tokens.
To make the transfers, Sally and John review the vendor invoices using a word-
processing program, and using that data they use a standard Funds Transfer Form
to create a Draft Funds Transfer, which they submit to Mary. Mary reviews the
Draft Funds Transfer and creates a Final Funds Transfer, using the word- processing
program. Mary then connects to the bank via the Internet using an Internet
browser program. With the connection to the bank, she authenticates to the bank
using the book or token authentication processes, which are secured in a safe that
only Mary has access to, and uploads the Final Funds Transfer to the bank. Upon
acceptance of the funds transfer the bank forwards a Transfer Confirmation Notice
to the system. At any time during this process any individual can print a copy of
any file. To ensure that proper oversight is conducted, the corporate auditors must
have access to all of the files that are created during this process.
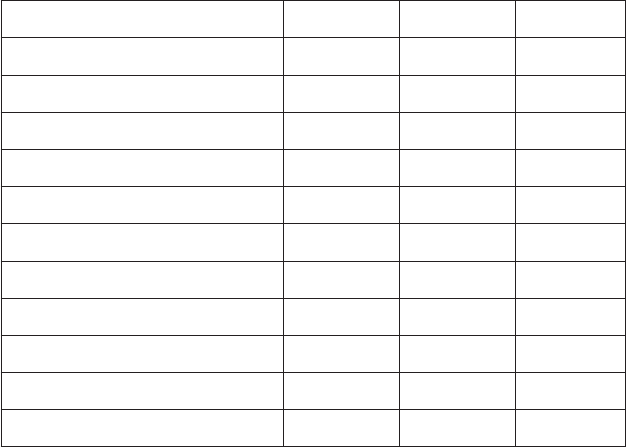
Knowing all of this, the ISSMP can now recommend the “role-based” security
solutions that can be used to implement the concept of “least privilege.” Table1.2
provides a summary of the privileges that each role (“Drafter” [Sally and John],
“Approver” [Mary], and Auditor [senior management, auditing staff, or third-party
auditors]) will be granted in the system to support this scenario.
Note that in this example, Mary, although she is in the role of supervisor,
does not have full privileges in the system. Specifically, she cannot change the
Submitted Draft Funds Transfer or the Transfer Confirmation Notice. This is to
ensure that she cannot modify key documents required by the auditors to ensure
that the process and the actions of the employees are in full compliance with
standard accounting procedures.
Compliance
In addition to the mission, business, and operating requirements, the ISSMP must
understand the legal and regulatory restrictions and demands that are imposed on
Enterprise Security Management Practices ◾ 9
© 2011 by Taylor & Francis Group, LLC
each group in the organization. ese are critical, because deploying security that
fails to make the system compliant with one of these can result in major nes or
negatively impact the reputation of the organization. e following are some of the
more common legal and regulatory compliance needs:
Privacy Act of 1974: e purpose of this act is to protect the rights of individu-
als by placing restrictions on government agencies as to what they can do with
personal information (i.e., transferring, matching, etc.) and mandates secu-
rity requirements to prevent the unauthorized release of the information.
Computer Security Act of 1987: e U.S. Congress declared that improving
the security and privacy of sensitive information in federal computer sys-
tems was in the public interest and established the means to create minimum
acceptable security practices for such systems.
European Union (EU) Directive of 1995 (95/46/EC): e EU issued this
directive to protect individuals with regard to the processing and free move-
ment of their personal data.
Health Insurance Portability and Accountability Act of 1996 (HIPAA): e
purpose of HIPAA is to protect an individual’s healthcare information from
being used in an unethical and fraudulent manner. e act mandates that the
ocers and employees of organizations related to healthcare (i.e., hospitals,
healthcare providers, insurance companies, etc.) deploy safeguards to ensure
the integrity and condentiality of all individual healthcare information, and
violations are punishable by nes and jail time.
Table1.2 Roles and Privileges
Privileges Approver Drafter Auditor
Word processing program Execute Execute Execute
Vendor invoices Read Read Read
Funds transfer forms Read Read/Write Read
Draft funds transfers Read Read/Write Read
Submitted draft funds transfers Read Read Read
Final funds transfers Read/Write Read Read
Submitted draft funds transfers Read Read Read
Internet browser program Execute No Access No Access
Authentication books/tokens Access No Access No Access
Transfer confirmation notice Read Read Read
Printer Write Write Write
10 ◾ Official (ISC)
2
® Guide to the ISSMP® CBK®
© 2011 by Taylor & Francis Group, LLC
Personal Information Protection and Electronic Document Act of 2000
(PIPEDA): PIPEDA is a Canadian law supporting and promoting electronic
commerce by protecting personal information that is collected, used, or dis-
closed in certain circumstances by providing for the use of electronic means
to communicate or record information or transactions.
Sarbanes-Oxley Act of 2002 (SOX): e purpose of SOX is to protect inves-
tors by improving the accuracy and reliability of corporate disclosures made
pursuant to the securities laws, and for other purposes.
Federal Information Security Management Act of 2002 (FISMA): e pur-
poses of Title III of this act are to provide a comprehensive framework for
ensuring the eectiveness of information security controls over information
resources that support federal operations and assets, eective government-wide
management and oversight of the related information security risks, and a
mechanism for improved oversight of federal agency information security
programs (i.e., FISMA compliance reporting to the Oce of Management
and Budget [OMB], Congressional Federal Computer Security Grades identi-
fying Agency security status, linking deciencies with budget process, etc.).
Take note that under FISMA, Congress linked the reporting of IT secu-
rity deciencies to the government budget process. is connection is one of
the keys to gaining and maintaining IT security in the government and com-
mercial sectors. is will be further discussed later in this chapter.
Cultural Expectations
e ISSMP needs to be aware of each group’s cultural dierences regarding secu-
rity, including its perceptions and expectations. Here are some examples of the
cultural dierences and the basis for the dierences:
Accounting: It will be expecting and accepting of the need for security, because
the function is frequently audited, has very detail-oriented tasks, is subject to
many regulatory requirements, and so forth.
R&D: If researchers are from or in an academic community, they will want
very little security because they desire an environment that is open, sharing,
and allows the ability to seek inputs or reviews from their colleagues. On
the other hand, if they work for a product, defense, or intelligence research
group, they will be expecting a lot of security, because they are used to han-
dling intellectual property or classied information.
Production: It will understand physical and personnel security very well and
may be less condent in the use of computers, so the use of physical access
controls and strict screen scripts may be seen as more acceptable methods of
securing its systems.
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
