Digest authentication is one of the well known HTTP authentication schemes, which were introduced to overcome most of the drawbacks of basic authentication. This type of authentication makes use of user-ID and password just like Basic authentication, but the major difference comes in the picture, when the credentials get transferred to the server.
Digest authentication increases the security of the credentials by going an extra mile with the concept of cryptographic encryption. When the user submits the password for the sake of authentication, the browser will apply an MD5 hashing scheme on it. The crux of the process lies in using nonce values (pseudo-random numbers) while encrypting the password which decreases the replay attacks.
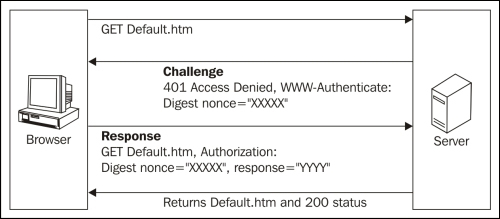
This type of authentication gains more strength, as the password in this encryption is not used in the form of plain text. The cracking of the password hashes becomes difficult in digest authentication with the use of a nonce, which counters the chosen plain text attacks.
Even though Digest authentication overcomes most of the drawbacks of Basic authentication, it does have some disadvantages. This scheme of authentication is vulnerable to man-in-the-middle attacks. It reduces the flexibility of storing the password in the password's database, as all the well designed password databases use other encryption methods to store them.
Using Digest authentication with requests is very simple. Let us see how it's done:
>>> from requests.auth import HTTPDigestAuth >>> requests.get('https://demo.example.com/resource/path', auth=HTTPDigestAuth('user-ID', 'password'))
In the preceding lines of code, we carried out digest authentication by creating an HTTPDigestAuth object and setting it to the 'auth' parameter which will be submitted to the server. If the submitted credentials gets authenticated successfully, the server returns a 200 response, otherwise, it will return a 401 response.
