Chapter 8: Software Development Security Domain 8 Practice Questions
Questions from the following topics are included in this domain:
- Understanding and integrating security into the software development life cycle
- Identifying and applying security controls to software development
- Assessing the effectiveness of software security
- Assessing the security of acquired software
- Defining and applying secure coding guidelines and standards
To pass the CISSP exam, you must score high in the Software Development Security domain. Domain 8 has an 11% weighting on the exam and requires you to understand details regarding the software development life cycle (SDLC), development methodologies such as Agile and Waterfall, and change management.
A thorough understanding of security controls, as well as when and where to apply them, is critical to passing the CISSP exam. Such controls include software configuration management, security orchestration, and repositories. You must also understand the difference between dynamic and static testing.
Finally, understanding the importance of securing software from outside vendors is critical. Acquired software includes application programming interfaces (APIs), commercial-off-the-shelf, and even open source. By default, these must go through normal security evaluations.
Questions
- Several software developers are invited to review each other's source code. This is an example of which type of activity?
A. Passive testing
B. Fuzzing
C. Static analysis
D. Dynamic analysis
- Mal, a system administrator, insists that she did not send an email threatening a co-worker. Further analysis shows that the public key of the letter directly relates to Mal's private key. What is this an example of?
A. Certificates
B. Non-repudiation
C. Defense in depth
D. Repudiation
- The security approach of complete mediation has which of the following features?
A. A security design that preserves data integrity
B. A security design where all access is verified
C. A security design where a kernel protects the hardware
D. A security design that uses defense in depth
- Which organization is responsible for maintaining the top 10 list of web application vulnerabilities?
A. OSSTMM
B. OWASP
C. OEC
D. OCTAVE
- The software development team at Flat Ground Mountain Bank is planning to test their production application using real customer data. Which process should they use to ensure the privacy of their customers?
A. Data anonymization
B. Data protection
C. Depersonalization
D. Safe harbor
- Reference monitors must have all the following features Except for which one?
A. Speed
B. Verifiable
C. Tamperproof
D. Complete mediation
- Which of the following are foundations of privacy?
A. Choice, data integrity, security
B. Verifiable, diverse, transferable
C. Openness, complexity, nonrepudiation
D. Encryption, availability, storage
- All the following are phases of the software development life cycle (SDLC) except for which of the following?
A. Planning
B. Fuzzing
C. Design
D. Maintenance
- Which software development model is based on manufacturing design, where work proceeds through steps in a linear, sequential process?
A. Spiral
B. Scrum
C. Waterfall
D. Agile
- From the following options, which cannot be used as a shared secret?
A. Something you have
B. Something you are
C. Something you know
D. Something you need
- Delphine is a security analyst classifying human resources and payroll data for the organization's employees and contractors. Which of the following is her BEST classification methodology?
A. Impact
B. Privacy
C. Sensitivity
D. Likelihood
- Which of the following is NOT considered structured data?
A. MySQL database of cybersecurity books
B. LibreOffice spreadsheet of course authors
C. Log file of SCSI drive errors
D. XML file of customer names and phone numbers
- When creating functional requirements for a software application, modeling how software should be used properly by customers helps build software that meets expectations. What are these models called?
A. Behavioral diagrams
B. Use cases
C. Application modeling
D. Misuse cases
- Darlene is the CISO of YRF Charities, and her team of software developers creates applications for churches. She follows organizational secure coding standards. What does this guarantee?
A. Error-free code
B. Complete security functionality
C. Code is economical
D. Code sans change orders
- When not properly handled, overly complex conditional logic can result in which condition?
A. Infinite loops
B. Input attacks
C. Race conditions
D. Memory leaks
- Nathan, a software engineer, has developed an application in the C language that allows users to enter their tax identification number. Which of the following is his primary concern?
A. Users entering an incorrect tax identification number
B. Lack of library support
C. Buffer overflows
D. Malware
- Owen is a software manager who's leading a team of developers that are making sales marketing software. He tracks and manages the project requirements with a grid. This grid is known as what?
A. A requirements traceability matrix
B. A Gantt chart
C. A Pareto chart
D. A PERT chart
- When prioritizing use cases, at a minimum, the use cases must be designed for which of the following?
A. All requirements
B. Poorly defined business requirements
C. Input validation
D. Security-related requirements
- Which tool should you use to decompose systems so that you can understand threats better?
A. UML
B. NVD
C. DFD
D. CVE
- What is the primary purpose of security reviews within the software development life cycle (SDLC)?
A. Ensure that threat models are updated at each phase
B. Ensure the quality of security actions
C. Ensure the attack models are updated
D. Ensure all steps of the SDLC are followed
- Matthew manages the software development of a website with a paywall, and they are running behind schedule. The threat model documentation is mostly complete. What should be their next step?
A. Complete the threat model documentation in the next phase.
B. The documentation can be skipped because development has tested positive.
C. Delay the process until the documentation is complete.
D. Apply for a waiver from the security team.
- The characteristics of a trust boundary are found in which of the following?
A. Cannot be observed
B. Items share the same rights, access, and identifiers
C. Items have the same access control list access
D. Items share identical user accounts
- The critical security details for the design phase of a new software product are contained in which document?
A. Security control model
B. Threat model
C. Bug database
D. Configuration file
- Reducing risk by reusing source code, libraries, and application programming interfaces is an example of which model?
A. Separation of duties
B. Leveraging existing components
C. Least common mechanism
D. Weakest link
- Hernan is designing an application that would work great within a single sign-on (SSO) system. What is the BEST way for him to manage authentication in the system?
A. Utilize the existing SSO management system.
B. Log exception data.
C. Implement exception management systems.
D. Create a management interface within the application.
- Complete mediation can be BEST described by which of the following approaches to security?
A. An approach that minimizes the opportunity to be circumvented.
B. Layered security.
C. Integrates authentication and authorization.
D. An approach that uses defense in depth and least privilege.
- Which of the following is the BEST example of exception management?
A. Logging and audit data
B. Psychological acceptability
C. Separation of duties
D. Integrity and availability
- Hash functions are commonly deployed for what purpose?
A. Confidentiality
B. Integrity checking
C. Authentication
D. Authorization
- Which of the following technologies is a set of standards that uses radio frequencies over very short distances?
A. Yagi
B. Zigbee
C. NFC
D. Omni-directional
- Which architecture mimics desktop applications in terms of functionality and usability?
A. REST
B. SOAP
C. RPC
D. RIA
- Which architectural component acts as a communication translator between protocols such as XML, REST, DCOM, and others?
A. JSON
B. CORBA
C. ESB
D. EDI
- Which of the following is NOT a feature of digital rights management (DRM) that controls the use, modification, and distribution of copyrighted works?
A. Persistence
B. Integrity checking
C. Encryption
D. Copy restriction
- The approach of linking to shared libraries when a program executes and loading them into memory is known as what?
A. Interpreting
B. Dynamic linking
C. Early linking
D. Static linking
- Which of the following both has compile features and acts as an interpreted language?
A. Lenovo
B. Java virtual machine (JVM)
C. Pascal
D. Android
- Isolating test code from direct contact with in-production data and systems goes by the name of which process?
A. Automation
B. Revision control
C. Isolation
D. Sandboxing
- What are two of the MOST important advantages managed code has over unmanaged code? (Choose 2)
A. Garbage collection
B. Runs faster
C. Security
D. Error-free
- Hashing values return the same result for identical inputs. How can you resolve this vulnerability?
A. Salt the hash.
B. Revert to MD5 hashing.
C. Use longer hash functions.
D. Triple hashing.
- What are the BEST methods for examining and selecting code when you're using disallowed functions (for example, routines prone to buffer overflows)? (Choose 2)
A. Static code analysis
B. Misuse case testing
C. Dynamic code analysis
D. Code review
- Attacking memory locations where applications had once run goes by which name?
A. Buffer overflow
B. Memory relocation
C. Data remanence
D. ASLR
- One of the important differences between a SIEM platform and a SOAR platform is what?
A. SIEMs rank threats and generate alerts.
B. SOARs identify deviations from the baseline.
C. SIEMs aggregate data from multiple sources.
D. SOARs use automation to respond to threats.
- The process that considers decision making from a variety of skill sets, for a specific product, within a specific timeframe, and uses consensus building techniques is considered which of the following?
A. TCB
B. SDLC
C. IPT
D. CMMI
- A popular source code repository tool that archives, tracks the history, and maintains revisions of an application is called what?
A. Pascal
B. Git
C. Fortran
D. Java
- The goals of software configuration management (SCM) include all the following Except which one?
A. Managing processes and tools for software builds
B. Conducting source code reviews
C. Defect-tracking back to the source
D. Ensuring that the configurations meet all your requirements
- Edson is a software developer creating applications for the automotive industry. He uses a system called DevOps that allows continuous development, testing, and delivery of new code. This activity is also known as what? (Choose 2)
A. Continuous development
B. Continuous delivery
C. Continuous integration
D. Continuous installation
- What is an organization's largest security risk when it comes to using third-party or commercial-off-the-shelf applications?
A. The application is written in a language prone to buffer overflows.
B. The developers are slow at releasing security patches.
C. The application has not been tested for input attacks.
D. The creator(s) has/ve poor security software design policies.
- Security tools built into continuous delivery process are known as what?
A. Security as code
B. Software-defined security
C. Commercial-off-the-shelf (COTS)
D. Open source
- Marie-Antoinette is a security manager concerned with the amount of entry point sources into the application being developed. What is her number one priority?
A. APIs
B. Software versioning
C. Type-safe code
D. Cryptographic abilities
- Khadija is a software developer that just downloaded a signed API from LYI Corp. Code signing provides all the following information about the API Except for what?
A. API is authentic
B. API is free of errors
C. API is published by LYI Corp
D. API integrity
- Jacques has just finished writing an application for computer-aided engineering. After running the application, he notices that the output results are incorrect, and now he needs to debug the application even further. What kind of test did he run?
A. Static analysis
B. Code review
C. Dynamic analysis
D. Code walkthrough
- When running a functional test, the examiner will conduct all the following tests Except for which one?
A. Unit testing
B. Performance testing
C. Dynamic testing
D. Attack surface area testing
- Maren is a software development manager, and her team is at the final testing for the software before releasing it to production. The final test will simulate the production environment. What is this test called?
A. Penetration testing
B. Sandbox testing
C. Simulation testing
D. Production testing
- An important part of customer service for those that use an organization's software product includes which of the following?
A. Creating new features
B. Responding to requests
C. Training
D. Getting the latest software development and testing tools
- Jackson tests security for applications, including those that encrypt data. To validate the encryption functions, he runs all of the following Except for what?
A. RNG
B. Secret encryption techniques
C. Encryption algorithms
D. Key distribution
- Veronica leads the software development team at TTC Corp and uses a tool to prioritize which errors must be resolved before releasing the application. What is this tool called?
A. SDLC process requirements
B. Bug bar
C. Trust boundaries
D. Security gates
- Applications that are written to restore themselves after a security breach are known to have which functionality?
A. Recoverability
B. Reliability
C. Restorability
D. Resilience
- When coding in .NET on a Microsoft system, compiling with the /GS flag enables which feature?
A. Buffer security check
B. Graphics speedup
C. Enable input validation
D. Graphics security
- Robbie is the manager of software development and is at a crossroad regarding whether the new application should use managed or unmanaged code. Which of the following are advantages of managed code? (Choose 2)
A. Type-safe code
B. Runs on one operating system
C. Faster execution
D. Improved memory management
- Which of the following is NOT true regarding declarative security programming and imperative (programmatic) security programming?
A. Declarative programming describes which security principles to apply, but not how to do it.
B. Imperative programming techniques create applications with high portability.
C. Declarative programming uses a container-based approach to aid in security.
D. Imperative programming programs specific security features into an application.
- What is the technology called that virtualizes security functions into software that enables simpler remote management and simpler deployments?
A. Continuous integration and continuous delivery
B. Honeypot
C. Software-defined security
D. DevSecOps
- TVM Corp's team of software developers inspects each programmer's source code for proper data sanitation regarding inputs, backdoors, and buffer overflow mitigations. This is an example of which activity? (Choose 2)
A. Code review
B. Dynamic code analysis
C. Code identification
D. Static code analysis
- What is an organization's largest security risk when it comes to using open source applications?
A. The source code is visible by anyone in the world.
B. The operations department does not install version updates and patches in a timely manner.
C. The creator(s) of the application may not have used secure software development procedures.
D. The creator(s) decide to discontinue further development of the application.
- Which of the following is the biggest risk for an organization converting from a Waterfall development to continuous integration and continuous delivery?
A. The risk that management cannot track project activity
B. The risk that developers will reuse metrics before they are reassessed by management
C. The risk that developers do not understand the sprint process
D. The risk that high-priority bugs will go unresolved
- What technique is used to detect buffer overflows?
A. Fairy
B. Canary
C. Sparrow
D. Gnome
- What is the primary difference between software configuration management (SCM) and a revision control system (RCS)?
A. RCS manages the software and the hardware hosting system.
B. SCM primarily focuses on application configurations, not source code.
C. RCS primarily focuses on application configurations, not source code.
D. SCM performs defect tracking, whereas RCS does not.
- Source code repositories that archive, track history, and maintain revisions of applications have all the following features Except for what?
A. Compilers
B. Bug tracking
C. Code review
D. Personal repository
- Which system uses customized playbooks to automate the mitigation of cybersecurity incidents, thus resulting in faster incident response and system operations being streamlined?
A. SOAR
B. IDS
C. IPS
D. Firewall
- Which of the following is NOT a key difference between standard work groups and integrated product teams (IPTs)?
A. Work products are created collectively in standard work groups.
B. Consensus is essential in IPTs.
C. Work products are individually focused on standard work groups.
D. Teams delegate work in IPTs.
- Ingrid is an ethical hacker attempting to exploit a victim by running a string that includes %252E%252E%255C within her browser. What type of attack is she attempting to run?
A. SQL injection
B. Directory traversal
C. Percentage injection
D. Buffer overflow
- The trusted platform module (TPM) resides on the computer's motherboard and manages at least which two features for system users?
A. Availability
B. Encryption
C. Hashing
D. Software platforms
- Which of the following describes the infrastructure of using certificates and asymmetric keys for mutual verification?
A. OSCP
B. GPG
C. PGP
D. X.509
- Which of the following provides a system for websites to grant access by using a relying party, allowing users to log into unrelated websites without having to create separate identities?
A. MySQL
B. SAML
C. OpenID
D. OSCP
- Which process creates machine language-based object files from source code?
A. Linking
B. Compiling
C. GUI
D. Interpreting
- The service-oriented architecture (SOA), which allows disparate applications to communicate across a network, has all the following features Except for which one?
A. Interoperability
B. Uniform testing framework
C. Modularity
D. Platform neutrality
- Which of the following is NOT a characteristic of cloud computing?
A. Resource pooling
B. Provisionable
C. Broad network access
D. Measured service
- Which of the following is NOT one of the cloud deployment models?
A. Personal
B. Private
C. Hybrid
D. Community
- Designing a simpler system that makes it easier for the team and others to understand design objectives is an example of which principle?
A. Open design
B. Single point of failure
C. Least common mechanism
D. Fail safe
- The Open Web Application Security Project Software Assurance Maturity Model (OWASP SAMM), which provides a vendor-neutral, measurable, and effective secure development life cycle, contains which five business functions?
A. Governance, design, implementation, verification, operations
B. Governance, threat assessment, implementation, verification, operations
C. Strategy, threat assessment, secure build, architecture, incident management
D. Policy, secure requirements, deployment, testing, operations
- Creating standardized designs, and running standardized code for similar or repeatable functionalities, goes by which design philosophy?
A. Open design
B. Economy of mechanism
C. Complete mediation
D. Psychological acceptability
- Mapi is part of a development team creating a smartphone gaming application. She can reuse source code from previous video games to simplify her task. How should the development manager respond?
A. Never reuse code because it is poor practice.
B. Never reuse code because it brings bugs into the application.
C. Test and validate the reused code as if it were new code.
D. Never reuse code because it is inherently insecure.
- Pamela is leading a software development team in a modeling exercise that lists the appropriate security mitigations for various threats. Which mitigations are preferred?
A. Acceptance of the vulnerability
B. Encryption
C. Novel, state-of-the-art security controls
D. Commonly used standard corporate security controls
- Which of the following is NOT an appropriate mitigation method for threat management?
A. Accept the vulnerability.
B. Redesign to avoid vulnerabilities.
C. Modify the security requirement to disregard the threat.
D. Apply normal mitigation.
- Malesa is a software developer that commonly works with multithreaded applications. As a result, she must create controls to mitigate race conditions. What are these controls called?
A. Single threading
B. Race windows
C. Atomic actions
D. Mutual exclusion
- Kenneth is a software manager that is implementing mitigations for common attacks for his new application. This will be represented with which types of diagrams? (Choose 2)
A. Security
B. Misuse case
C. Abuse case
D. Use case
- Cle leads the software development team at TRY Corp and uses the software development life cycle for his projects. He always starts with the planning and business requirements. These requirements get converted into what for the software developers?
A. JavaScript
B. Functional requirements
C. Security concerns
D. White box testing
- Which of the following is NOT a type of data on a web server?
A. Preserved
B. Personally identifiable information
C. Personal health information
D. Classified
- Data in any organization has a life cycle so that it can be managed and disposed of properly. Which of the following is NOT a stage of the data life cycle?
A. Degaussing
B. Generation
C. Retention
D. Disposal
- What is a specific risk called that is NOT found during an audit?
A. Audit risk
B. Control risk
C. Inherent risk
D. Detection risk
- Reggie is a security director and analyzes whether software meets legal and regulatory policies. These policies are examples of which type of requirements?
A. Internal requirements
B. External requirements
C. Customer requirements
D. Job requirements
- Policy elements related to integrity include which of the following?
A. Systems that control risk
B. Determine who is authorized to see specific data segments
C. Obtain error detection and correction
D. Ensure systems are available for authorized users
- Which tool can be BEST used to examine the vulnerabilities of input interfaces?
A. Bug bar
B. Attack surface analysis
C. Threat model
D. Fuzz testing framework
- Microsoft has put which system together that helps users analyze common software threats?
A. SMART
B. DREAD
C. STRIDE
D. Waterfall
- Which of the following are NOT phases of the Microsoft SDL process? (Choose 2)
A. Requirements
B. Security
C. Validation
D. Training
- HITECH and HIPAA are frameworks that have been designed to protect which of the following?
A. PII
B. PHI
C. PCI
D. PFI
- What is the fifth level of the CMMI maturity model?
A. Incomplete
B. Initial
C. Defined
D. Optimizing
- Glue Corp is based in the US, while Horse Ltd. is based in the UK. Which of the following principles needs be invoked to facilitate data sharing?
A. GDPR
B. Safe harbor
C. FISMA
D. UNTC
- Of the following, which is NOT a technological risk?
A. Regulatory
B. Privacy
C. Encryption
D. Change management
- The software design principle of keeping things simple is related to which other security principle?
A. Economy of mechanism
B. Simple security rule
C. Layered security
D. Least privilege
- Users that create passwords with multiple characters using uppercase characters, lowercase characters, special characters, and a minimum of 12 characters are using which type of security model?
A. Defense in depth
B. Security through obscurity
C. Mutual authentication
D. Implicit deny
- A system approach where the separation of elements mitigates accidental sharing of information is called what?
A. Weakest link
B. Leverage existing components
C. Separation of duties
D. Least common mechanism
- Static code analysis would fit BEST in which testing model?
A. Black box testing
B. Gray box testing
C. White box testing
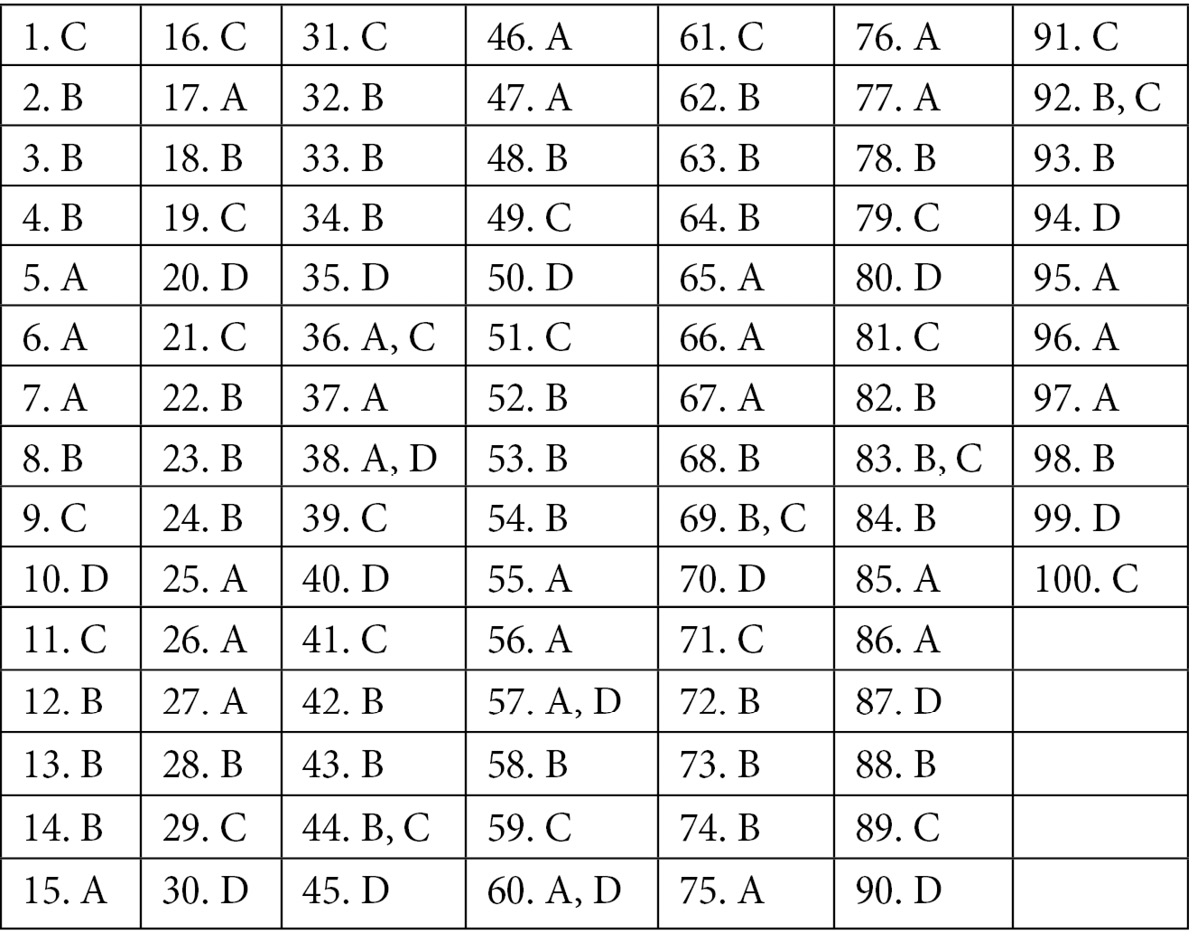
Quick answer key
Answers with explanations
- Answer: C Code reviews, or static analysis, are used to help others write more efficient code and watch for security vulnerabilities such as buffer overflows or backdoors. Dynamic analysis tests how the code operates when it runs. Fuzzing tests user input into applications, while passive testing monitors software as it runs.
- Answer: B Since her private key matches the public key of the letter, she cannot repudiate that she sent the email. It is still possible that someone sent the email from her account when she stepped away from her computer, and that could be determined through video analysis or other investigations.
- Answer: B Complete mediation designs ensure that access to an object is checked for authority. Whenever a subject accesses an object, the action must be mediated to ensure the subject has the required privilege.
- Answer: B The Open Web Application Security Project (OWASP) provides tools to mitigate web application vulnerabilities. The Open Source Security Testing Methodology Manual (OSSTMM) provides a penetration testing security model. The Open Education Consortium (OEC) advocates for free and open university-level educational materials. Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE) is an approach to managing general information security risks.
- Answer: A Test data management utilizes data anonymization to strip the data of any personally identifiable information (PII). Skipping the anonymization step could leak customer PII unintentionally. Safe harbor, data protection, and depersonalization all protect the data, but the PII could still potentially be leaked because customer information has not been removed.
- Answer: A Reference monitors keep systems secure by constructing and assessing the effectiveness and assurance of security policy enforcement in automated systems.
Learn more here: https://web.ecs.syr.edu/~wedu/seed/Labs/Reference-Monitor/.
- Answer: A The fundamental privacy elements are access, choice, enforcement, data integrity, notice, onward transfer, and security. Learn more here: https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5124066/.
- Answer: B The phases of the SDLC are Planning and Requirements, Design, Build, Test, Deploy, and Maintenance. Fuzzing is a component of the test phase to ensure that input validation is taking place and done properly. Learn more here: http://www.austincc.edu/skumpati/BCIS1305/CC06.ppt.
- Answer: C Waterfall is the model that's used in the automotive, road construction, and bridge building industries. It makes it very difficult to return to a previous step in the process because the expense would be huge. Because of the flexibility of software, processes such as spiral, Agile, and Scrum create opportunities to improve software by revisiting earlier steps in the process.
- Answer: D Possible methods of authenticating identities for application use include something you have, something you are, and something you know. Identities can be further proven using the something you do and somewhere you are factors. Learn more here: https://dojowithrenan.medium.com/the-5-factors-of-authentication-bcb79d354c13.
- Answer: C Privacy is not a methodology, but a goal. The privacy risk assessment methodology (PRAM) helps organizations respond to privacy risks; one way is to label data according to its sensitivity. Impact and likelihood are part of the PRAM approach. Learn more here: https://www.nist.gov/system/files/documents/2020/01/16/NIST%20Privacy%20Framework_V1.0.pdf.
- Answer: B When LibreOffice, Google Chrome Office, Microsoft Office, IBM Lotus, and other files are saved, they are preserved in the binary format of that vendor, which disrupts the format of the spreadsheet. The others are structured, and their formats are understood by a multitude of applications.
- Answer: B Use case diagrams display what an authenticated user can and cannot do depending on their role as a user. Misuse case diagrams display what unauthenticated users cannot do. The others are distractors.
- Answer: B Examples of secure coding standards are published by the Software Engineering Institute/CERT at Carnegie Mellon University. This includes recommendations for secure programming that resolve vulnerabilities that are found within typical source code. Sans means without.
- Answer: A When complex conditionals aren't checked properly, infinite loops can occur because a statement seen as true when it was last checked may now be false. It now remains in the loop, even though it shouldn't.
- Answer: C C language development is prone to buffer overflow attacks, especially when users can enter input. When successfully exploited, a buffer overflow can allow attackers to exfiltrate data or power off the system. Malware and library support are concerns, but more so to system administrators.
- Answer: A The requirements traceability matrix (RTM) is designed specifically for the software industry to track and verify requirements. Gantt, Pareto, and Program Evaluation and Review Technique (PERT) are generic project management tools that are used to coordinate specific events and tasks for a project.
- Answer: B Use cases are helpful in describing unusually complex and confusing circumstances between the user and the system, which results in better software design. The other options are generally issues that are normally handled in software development; therefore, developing use cases for such events would be redundant.
- Answer: C Data flow diagrams (DFDs) provide the system with the processes, data stores, and data flows between elements so that developers can examine trust between the boundaries that are most vulnerable to attacks. The Unified Modeling Language (UML) does not go into this level of detail. The National Vulnerability Database (NVD) and Common Vulnerabilities and Exposures (CVE) are both tools that can be used during the DFD process as these provide lists of known vulnerabilities.
- Answer: D The primary goal of security reviews is to assure the development team that the SDLC process and the desired security mitigations are effective so that the process can be trusted and tuned for future projects.
- Answer: C Each phase of the software development life cycle (SDLC) must be approved by security before advancing to the next phase, which means completing that phase before continuing.
- Answer: B Trust boundaries are areas where systems have equal trust, such as identical rights, privileges, identifiers, and access. Trust boundary violations refers to vulnerabilities where code trusts unvalidated data. Learn more here: https://owasp.org/www-project-web-security-testing-guide/assets/archive/OWASP_Testing_Guide_v3.pdf.
Reference:"OWASP Testing Guide", OWASP Foundation, p. 155, 2008 v3.0.
- Answer: B Threat modeling is a process by which potential threats, such as structural vulnerabilities or the absence of appropriate safeguards, can be identified and enumerated, and mitigations can be prioritized. The purpose of threat modeling is to provide defenders with systematic analysis of what controls or defenses need to be included, given the nature of the system, the probable attacker's profile, the most likely attack vectors, and the assets most desired by an attacker. Learn more here: https://owasp.org/www-community/Threat_Modeling.
- Answer: B Risk is reduced by using proven components. When each component performs one task, and performs it well, it is considered separation of duties. The least common mechanism states that code that's used to access resources should not be shared; sharing mechanisms creates vulnerabilities. Where the vulnerabilities are highly exploitable is considered the weakest link.
- Answer: A Utilizing the existing SSO system provides many operational advantages as systems administrators can maintain a system they understand. The other options are reinventing the wheel, so thorough security testing would be required to ensure their long-term success.
- Answer: A Authority is verified before use in complete mediation system; for example, verifying that the user has the rights to modify a file before making changes.
- Answer: A When systems crash or fail, detailing when and why these errors occur is important and saved in log files. This is also known as auditing. This aids in proper diagnoses and correction. The others have little to do with exception management.
- Answer: B Hashing functions are also used as part of authentication, but hashing is more commonly used for integrity checking to determine whether files have been altered accidentally or intentionally. File alterations could be as simple as an entry made by a user, or due to malware added by an attacker.
- Answer: C Near-field communication (NFC) communicates over very short distances, making it less vulnerable to man-in-the-middle attacks versus Yagi systems, which are very long range, and Wi-Fi, which uses omni-directional antennas. Many home security systems use Zigbee wireless networks.
- Answer: D Rich internet applications (RIAs) use the internet to transfer data and use the client to process the data, typically to display graphics, with, for example, JavaScript or Flash. Remote procedure calls (RPCs) create remote instructions, put them into a message, send them to the server to execute, and return the results to the client. The Simple Object Access Protocol (SOAP) allows enterprises to integrate messaging with their partners using different programming languages. Representational State Transfer (REST) makes server-side data available to website administrators.
Learn more here: https://www.altexsoft.com/blog/soap-vs-rest-vs-graphql-vs-rpc/.
- Answer: C An enterprise service bus (ESB) provides seamless communication between XML, DCOM, REST, CORBA, WSDL, EDI, and others.
- Answer: B The Digital Millennium Copyright Act (DMCA) defines the copyright laws that DRM enforces. Persistence ensures that rights persist, regardless of where the document is moved. Copy restriction doesn't allow you to make duplicates of the medium. Other features include installation limits, anti-tampering, regional lockouts, and watermarking. Learn more here: https://www.locklizard.com/rights-management/.
- Answer: B Dynamic links, also known as late links, are resolved at runtime, where static or early links are built into the compiled application. Interpreted languages may read dynamically linked libraries when they're executed.
- Answer: B Compiled JVM byte code runs universally on any JVM offering the capability to write once and run anywhere, as long as the system runs a JVM. JVMs run on smartphones, computers, tablets, and web browsers.
- Answer: D Sandboxing protects live, in-production systems from changes that could damage critical systems. Revision control systems provide branches to isolate experimental changes from trusted branches. Many automation systems have sandboxing utilities built in as part of their service, allowing developers to segment an experimental area from the trusted environment.
- Answer: A, C Managed code works within a virtual machine; for example, the Common Language Runtime (CLR) on Windows. The CLR provides secure features, such as sandboxing, garbage collection, type safety, and memory management. Unmanaged code provides better performance because it runs on the target system it was designed for, but the developer must add their own security features.
- Answer: A Salting creates stronger hashes by making them more random so that a hash is different for identical inputs. The salt is added to the input so that the hash varies. Linux systems salt hashes by default as part of authentication. (Windows systems do not salt their hashes.)
- Answer: A, D Code review and static analysis is where other members of the team review each other's source code within the application. Misuse case testing evaluates software by abusing its intended purpose. Dynamic testing analyzes an application at runtime.
- Answer: C Attackers attempt to get copies of data where applications had once run on memory. This can happen if garbage collection is not done, which overwrites unused memory locations with zeroes. Another mitigation is address space layout randomization (ASLR), which places applications in different areas of memory each time they are executed, making it harder for hackers to find where the data is located.
- Answer: D Security orchestration, automation, and response (SOAR) systems use automation, machine learning, and artificial intelligence to respond to threats. Security information and event management (SIEM) systems are similar to SOAR systems, but without the automation.
- Answer: C Integrated product teams (IPTs) bring people together from diverse backgrounds, such as engineering, marketing, manufacturing, software developers, and so on, using consensus to develop an application that best meets the needs of the user. Neither the trusted computing base (TCB), the software development life cycle (SDLC), or the Capability Maturity Model Integration (CMMI) fit the model for IPT. Learn more here: https://www.mitre.org/publications/technical-papers/integrated-project-team-ipt-startup-guide.
- Answer: B Git is a revision control system that was developed by Linus Torvalds, the founder of the Linux operating system. Source code hosting facilities that use Git include GitHub, GitLab, Launchpad, and others. The other options are computer languages whose source code can be utilized in a repository.
- Answer: B SCM provides a bigger picture than code management. Code reviews are completed by separate teams outside of SCM. The SCM ensures that the software meets the needs of the environment, including interactions with other applications and disparate hardware.
Reference: Software Configuration Management, Coordination for Team Productivity, W. A. Babich, Addison-Wesley, 1986.
- Answer: B, C Continuous integration and continuous delivery (CI/CD) are important for successful software development and operations (DevOps). CI involves developers and testers working together to validate new code. CD is the straightforward release of this new code to users without servers needing to be shut down. Learn more here: https://www.infoworld.com/article/3113680/5-common-pitfalls-of-cicd-and-how-to-avoid-them.html.
- Answer: D Any software development not using secure software development practices leaves organizations open to vulnerabilities. The other options are the result of poor software development policies.
- Answer: A Continuous delivery provides an automated framework for software changes, releasing software upgrades, patches, and configuration changes in a predictable format. Security-as-code controls automatically where testing is done, who has access to repositories, manages changes, and more. Learn more here: https://www.oreilly.com/library/view/devopssec/9781491971413/. Reference: DevOpsSec, Jim Bird, O'Reilly Media, Inc, June 2016.
- Answer: A Application programming interfaces (APIs) are generally black boxes that provide additional features for applications. Since static code analysis cannot be performed, other security measures must be performed to ensure the APIs do not bring insecurities into the application.
- Answer: B Code signing provides authenticity and integrity checking, but not defects within the code.
- Answer: C Jacques is performing dynamic analysis. The others are all types of static analysis where reviewers examine the source code. Debugging his application takes him back to the code review stage since he will be examining the source code again.
- Answer: D Attack surface area testing is part of the software development life cycle (SDLC) process. Functional tests are concerned with how the application functions.
- Answer: C A simulation test simulates the production environment the software will be released to. Production testing occurs once the software has been released to a live production environment. Sandboxing and penetration testing occur before simulation testing.
- Answer: B Organizations that respond to customer requests are successful because the voice of the customer leads to features they are seeking, and they feel as if they are part of the process. The others are important, but if the customer feels ignored, the firm will eventually lack business.
- Answer: B Random number generators (RNGs) are tested for robustness. Side-channel attacks are tested against key distribution systems. Encryption algorithms are analyzed, ensuring the correct versions are used for the needs of the data. Custom-made, secret encryption techniques are not tested because they are inherently insecure. Learn more here: https://resources.infosecinstitute.com/topic/the-dangers-of-rolling-your-own-encryption/.
- Answer: B Bug bars are a measure of the minimal level of quality, or bar, before software is released to production. If errors exceed the bar, they must be fixed before the software is released into production.
- Answer: A Recovery testing is part of a non-functional process, and developers study how quickly it recovers, as well as with what functionalities. The other options are improper terminology. Learn more here: https://www.guru99.com/recovery-testing.html.
- Answer: A The /GS compiler switch enables stack overflow protection using a cookie. This cookie is treated as a canary to determine whether its value changes when the program reaches the end of a function. Learn more here: https://docs.microsoft.com/en-us/cpp/build/reference/gs-buffer-security-check.
- Answer: A, D Managed code such as applications that use Java or .NET provide more security by default because the applications run in a Common Language Runtime (CLR) environment. This provides sandboxing, index checking, and multi-platform capabilities.
- Answer: B Declarative programs use a container-based approach to manage their applications so that security is managed by operational personnel, not development. An imperative programming approach reduces the portability of the applications because of their built-in customization. Learn more here: https://www.csm.ornl.gov/SOS20/documents/McCormick-SOS20.pdf.
Reference: Imperative, Declarative, Functional and Domain-Specific Programming… Oh My!, Patrick McCormick, SOS 20 Workshop, Los Alamos National Laboratory, March 2016.
- Answer: C Virtualizing security functions provides many of the same benefits as virtualization in general, including reducing capital and operational expenses (CapEx/OpEx), smaller device footprints, and easier updating. Learn more here: https://www.sdxcentral.com/security/definitions/what-is-software-defined-security/.
- Answer: A, D Dynamic code analysis is the process of validating results when users run the application. Code identification is a distractor.
- Answer: C Any software development not using secure software development practices leaves organizations open to a plethora of vulnerabilities, including malware, backdoors, and hijacking. Many view the visibility of open source software as an advantage because many more developers can spot vulnerabilities via static analysis, and if the creator(s) decide not to develop any further, it is straightforward for someone to take over and continue the effort. The operations department needs to keep all the software updated. Learn more here: https://devops.com/the-risks-and-potential-impacts-associated-with-open-source/.
- Answer: B Software managers and developers must understand that although many segments of continuous integration and continuous delivery (CI/CD) follow the software development life cycle (SDLC), it does not drive the SDLC. Software and security managers must ensure that the SDLC drives the CI/CD process and define the requirements before design, as in this example. The CI/CD process makes it easier to track project activity, manage bugs, and explain the sprint process.
- Answer: B The canary technique sets a parameter to a known value between the buffer and control data on the stack. If the value changes, it's likely the buffer overflowed and overwrote the canary value, and the application should terminate. The other options are distractors.
- Answer: B Software configuration management (SCM) is primarily concerned with how software operates in the environment, not standalone like revision control systems (RCSes). SCM's goals include configuration management, environment management, and facilitating team interactions.
- Answer: A Source code repositories offer many services, including web hosting, wikis, translation systems, shell server support, mailing lists, forums, and more. Software developers need to provide their own compilers. Learn more here: https://github.com/features/.
- Answer: A Security orchestration, automation, and response (SOAR) systems aid in cybersecurity by using machine learning to help resolve security events or incidents. Intrusion detection systems (IDSes), intrusion prevention systems (IPSes), and firewalls do not use playbooks. Learn more here: https://searchsecurity.techtarget.com/definition/SOAR.
- Answer: A Work products are more individually focused on standard work groups. Learn more here: https://www.mitre.org/publications/technical-papers/integrated-project-team-ipt-startup-guide.
Reference: "Integrated Project Team (IPT) Start-up Guide", Creekmore, Muscella, and Petrun, The MITRE Corporation, October 2008.
- Answer: B Ingrid is using URL encoding to defeat intrusion detection or prevention systems so that her attack goes unnoticed. %252 represents ".," while %255C represents "," which, when decoded, becomes "..." This means "change directory." The goal is for the attacker to reach the folder where her exploit resides so that she can execute it and compromise the server.
- Answer: B, C Trusted platform modules (TPMs) contain processors to generate and store asymmetric and symmetric keys. They also have hash generators to assist with integrity checking. Other features include a hardware-based random number generator and platform integrity, so that they can detect whether any network cards or hard drives have been replaced.
- Answer: D X.509 certificates contain details about the vendor, such as their name, address, expiration date for the certificate, and more. The Online Certificate Status Protocol (OCSP) is used to obtain the status of X.509 digital certificates. GNU Privacy Guard (GPG) is the free, open source version of Pretty Good Privacy (PGP), which provides tools for building X.509 certificates.
- Answer: C OpenID is used by Google, Facebook, Microsoft, and others so that users can use those credentials to access other services. Security Assertion Markup Language (SAML) is similar to OpenID in functionality but does not use a relying party. The Online Certificate Status Protocol (OCSP) is used to obtain the status of X.509 digital certificates. MySQL is an open source relational database management system.
- Answer: B Compiling creates object files that usually end in <filename>.o or <filename>.obj, but can't be executed by the operating system yet. The next stage is linking, which combines the functions, libraries, and dependencies into a single file that can be executed by the operating system. Interpreted languages don't need to be compiled; for example, Python and Bash. Graphical user interfaces (GUIs) allow users to run programs using a mouse.
- Answer: B Features of the service-oriented architecture (SOA) include platform neutrality, modularity, reusability, a contract-based interface, discoverability, and interoperability. Because of the heterogeneity and complexity of SOA and its large number of testing possibilities, multiple tools are required to validate SOA services.
- Answer: B The characteristics of cloud computing include on-demand self-service, broad network access, resource pooling, rapid elasticity, and measured service. Learn more here: http://blog.mesa.org/2017/08/manufacturing-in-cloud-part-ii-5.html.
- Answer: A The four cloud deployment models are public, private, community, and hybrid, which is a combination of the first three.
- Answer: A Open design is all about clear communications. The simpler the communications to the design team, the better the design and the better the security of the application. Single point of failure is similar to weakest link in that if there is no backup, the system fails. A fail safe is designed so that if the system fails, it fails in a secure manner.
- Answer: A The OWASP Software Assurance Maturity Model (SAMM) provides an effective and measurable way to analyze and improve the secure development life cycle. SAMM was built to be evolutive and risk-driven. The five business functions – governance, design, implementation, verification, and operations – are built on top of more than a dozen practices, including strategy and metrics, threat assessment, secure build, architecture assessment, and incident management. Learn more here: https://owasp.org/www-project-samm.
- Answer: B Reusing components is a representation of economy of mechanism. When applications are written with mild learning curves, they are more likely to be used. This is known as psychological acceptability. Where there is open and constructive communication, you have a system of open design. Conducting authorization checks before an operation proceeds is known as complete mediation.
- Answer: C When reusing code, make sure it goes through the normal SDLC security process. Reusing code can help save time and can often be more secure than writing new code because it is heavily tested.
- Answer: D Organizations that utilize known, tested, and commonly used security controls use systems that they are familiar with and allow staff to compare the results against their past benchmarks. The other options are useful, but the best practice is to use security controls validated by the organization, as well as going through configuration management.
- Answer: C Ignoring the threat does not mitigate the threat and still leaves the application vulnerable. The others are appropriate risk mitigations.
- Answer: B Race windows interpret the environment, which can cause a race condition. This is where an object can be altered by concurrent threads. These are commonly resolved using mutual exclusion and atomic actions. Single threading is a distractor.
- Answer: B, C Misuse and abuse case diagrams display what attackers should not be able to do, so that proper mitigations can be put in place during the design and development phases of software development. Misuse case diagrams are slightly more detailed than abuse case diagrams, but both are great at making software more secure. Learn more here: https://www.cs.auckland.ac.nz/courses/compsci725s2c/archive/termpapers/csia.pdf.
Reference: "Misuse Cases and Abuse Cases in Eliciting Security Requirements", Chin Wei, Department of Computer Science, University of Auckland, October 25, 2005.
- Answer: B The business requirements are converted into functional requirements, which are like blueprints for which software will be securely designed and tested. At this stage, it is too early to conduct any JavaScript coding because the requirements may call for a different computer language entirely. Security is part of every stage of the SDLC, and white box testing occurs much later in the testing phase.
- Answer: A All data is saved or preserved on a hard drive. The others can all be labeled as PII, PHI, classified, or unclassified.
- Answer: A Degaussing uses a magnet to securely dispose of data. The proper stages of the data life cycle are generation, retention, and disposal.
- Answer: D Detection risk occurs when an auditor fails to find a vulnerability. Inherent risks are risks that are present in source code by default. Control risks are those that the software developer cannot prevent or detect. An audit risk is a distractor. Learn more here: https://www.investopedia.com/terms/d/detection-risk.asp.
- Answer: B Laws and regulations are detailed and enforced by outside organizations, making them external requirements. Internal requirements include those that are created and enforced by the organization Reggie belongs to. Customer requirements are product functions that appeal to the client. Job requirements come with a task list for completing an assignment.
- Answer: C Integrity controls log errors and detect items outside a baseline. Availability controls determine who is allowed to access specific data segments, or whether systems are available for authorized users. Risk is analyzed as part of business impact analysis.
- Answer: D Fuzz testing is a process where random inputs are sent to an interface seeking exploitable failures. Bug bars prioritize bugs as to whether they need to be fixed in current or future releases. One way to accomplish this is with the DREAD model (damage, reproducibility, exploitability, affected users, and discoverability). Threat models define and describe threats to the entire software system; one such model is Microsoft's STRIDE model. Attack surface analysis measures software vulnerabilities.
- Answer: C The Microsoft STRIDE model reminds developers to out watch for Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, and Elevation of privilege, all of which are common threats. This helps users build better quality and lower cost software.
Learn more here: https://www.microsoft.com/security/blog/2007/09/11/stride-chart/.
- Answer: B, C The Microsoft security development life cycle (SDLC) consists of the following phases: 1) Training, 2) Requirements, 3) Design, 4) Implementation, 5) Verification, 6) Release, 7) Response. Security is reviewed in each phase of the SDL. Validation is part of the Release phase.
- Answer: B If personal health information (PHI) is compromised, patients could end up with the wrong prescriptions or procedures. Also, leaked information could affect the patient's employment or employment opportunities.
- Answer: D The maturity levels represent an organization's path toward performance and process improvement. The Capability Maturity Model Integration (CMMI) maturity levels are Level 0: Incomplete, Level 1: Initial, Level 2: Managed, Level 3: Defined, Level 4: Quantitatively Managed, and Level 5: Optimizing. Optimizing organizations focuses on continuous improvement.
Learn more here: https://cmmiinstitute.com/learning/appraisals/levels.
- Answer: A When working with firms in the European Union, General Data Protection Regulation (GDPR) principles must apply to all data, no longer Safe Harbor, which allowed for looser relationships regarding data exchange, especially with regards to personally identifiable information (PII). The Federal Information Security Management Act (FISMA) is a federal law that requires federal agencies to implement security programs. The United Nations Treaty Collection is a depository of over 500 multilateral treaties.
- Answer: A Regulatory would be an example of a business risk because there is no technical utility to manage such risk, where privacy, change management, and encryption all contain a technical control to manage their risk.
- Answer: A The simple security rule is defined for use within the Bell-LaPadula confidentiality model and states that the user must have the correct rights to view an item. Economy of mechanism states that code complexity leads to security vulnerabilities because of the larger attack surface.
Learn more here:
https://us-cert.cisa.gov/bsi/articles/knowledge/principles/economy-of-mechanism.
- Answer: B One way security through obscurity protects passwords is that they are different from any dictionary word, making them very difficult to crack.
Learn more here: https://us-cert.cisa.gov/ncas/tips/ST04-002.
- Answer: D Prevention of accidental sharing is the point here. The least common mechanism states that any mechanisms that are used to access resources should not be shared. Separation of duties reduces fraud by ensuring that each individual does one small piece of the entire work. Leveraging existing components allows you to reuse low-risk coding elements. Weakest link states that the least secure component harms security for the entire system.
- Answer: C With static code analysis, each participant has a full view of the source code. Since everyone has knowledge of the internals, this best fits with white box testing. Black box testing would best fit dynamic code analysis for code that's been purchased from a vendor that does not provide source code. Gray box testing means that the reviewers have some knowledge of the internals. Opaque box testing is a distractor.
