Chapter 7
Security Operations (Domain 7)
-
Referring to the following figure, what technology is shown that provides fault tolerance for the database servers?
- Failover cluster
- UPS
- Tape backup
- Cold site

-
Joe is the security administrator for an ERP system. He is preparing to create accounts for several new employees. What default access should he give to all of the new employees as he creates the accounts?
- Read only
- Editor
- Administrator
- No access
-
Which one of the following is not a privileged administrative activity that should be automatically sent to a log of superuser actions?
- Purging log entries
- Restoring a system from backup
- Logging into a workstation
- Managing user accounts
-
Which one of the following individuals is most likely to lead a regulatory investigation?
- CISO
- CIO
- Government agent
- Private detective
-
What type of evidence consists entirely of tangible items that may be brought into a court of law?
- Documentary evidence
- Parol evidence
- Testimonial evidence
- Real evidence
-
Which one of the following trusted recovery types does not fail into a secure operating state?
- Manual recovery
- Automated recovery
- Automated recovery without undue loss
- Function recovery
-
Which one of the following might a security team use on a honeypot system to consume an attacker’s time while alerting administrators?
- Honeynet
- Pseudoflaw
- Warning banner
- Darknet
-
Toni responds to the desk of a user who reports slow system activity. Upon checking outbound network connections from that system, Toni notices a large amount of social media traffic originating from the system. The user does not use social media, and when Toni checks the accounts in question, they contain strange messages that appear encrypted. What is the most likely cause of this traffic?
- Other users are relaying social media requests through Toni’s computer.
- Toni’s computer is part of a botnet.
- Toni is lying about her use of social media.
- Someone else is using Toni’s computer when she is not present.
-
Under what virtualization model does the virtualization platform separate the network control plane from the data plane and replace complex network devices with simpler devices that simply receive instructions from the controller?
- Virtual machines
- VSAN
- VLAN
- SDN
-
Jim would like to identify compromised systems on his network that may be participating in a botnet. He plans to do this by watching for connections made to known command-and-control servers. Which one of the following techniques would be most likely to provide this information if Jim has access to a list of known servers?
- Netflow records
- IDS logs
- Authentication logs
- RFC logs
- For questions 11–14, please refer to the following scenario:
- Gary was recently hired as the first chief information security officer (CISO) for a local government agency. The agency recently suffered a security breach and is attempting to build a new information security program. Gary would like to apply some best practices for security operations as he is designing this program.
-
As Gary decides what access permissions he should grant to each user, what principle should guide his decisions about default permissions?
- Separation of duties
- Least privilege
- Aggregation
- Separation of privileges
-
As Gary designs the program, he uses the matrix shown here. What principle of information security does this matrix most directly help enforce?
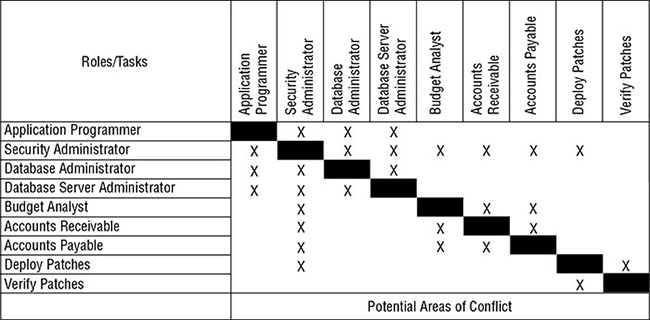
- Segregation of duties
- Aggregation
- Two-person control
- Defense in depth
-
Gary is preparing to create an account for a new user and assign privileges to the HR database. What two elements of information must Gary verify before granting this access?
- Credentials and need to know
- Clearance and need to know
- Password and clearance
- Password and biometric scan
-
Gary is preparing to develop controls around access to root encryption keys and would like to apply a principle of security designed specifically for very sensitive operations. Which principle should he apply?
- Least privilege
- Defense in depth
- Security through obscurity
- Two-person control
-
When should an organization conduct a review of the privileged access that a user has to sensitive systems?
- On a periodic basis
- When a user leaves the organization
- When a user changes roles
- All of the above
-
Which one of the following terms is often used to describe a collection of unrelated patches released in a large collection?
- Hotfix
- Update
- Security fix
- Service pack
-
Which one of the following tasks is performed by a forensic disk controller?
- Masking error conditions reported by the storage device
- Transmitting write commands to the storage device
- Intercepting and modifying or discarding commands sent to the storage device
- Preventing data from being returned by a read operation sent to the device
-
Lydia is processing access control requests for her organization. She comes across a request where the user does have the required security clearance, but there is no business justification for the access. Lydia denies this request. What security principle is she following?
- Need to know
- Least privilege
- Separation of duties
- Two-person control
-
Match each of the numbered terms with its correct lettered definition:
Terms
- Honeypot
- Honeynet
- Pseudoflaw
- Darknet
Definitions
- An intentionally designed vulnerability used to lure in an attacker
- A network set up with intentional vulnerabilities
- A system set up with intentional vulnerabilities
- A monitored network without any hosts
-
Which one of the following mechanisms is not commonly seen as a deterrent to fraud?
- Job rotation
- Mandatory vacations
- Incident response
- Two-person control
-
Brian recently joined an organization that runs the majority of its services on a virtualization platform located in its own data center but also leverages an IaaS provider for hosting its web services and a SaaS email system. What term best describes the type of cloud environment this organization uses?
- Public cloud
- Dedicated cloud
- Private cloud
- Hybrid cloud
-
Tom is responding to a recent security incident and is seeking information on the approval process for a recent modification to a system’s security settings. Where would he most likely find this information?
- Change log
- System log
- Security log
- Application log
-
Mark is considering replacing his organization’s customer relationship management (CRM) solution with a new product that is available in the cloud. This new solution is completely managed by the vendor, and Mark’s company will not have to write any code or manage any physical resources. What type of cloud solution is Mark considering?
- IaaS
- CaaS
- PaaS
- SaaS
-
Which one of the following information sources is useful to security administrators seeking a list of information security vulnerabilities in applications, devices, and operating systems?
- OWASP
- Bugtraq
- Microsoft Security Bulletins
- CVE
-
Which of the following would normally be considered an example of a disaster when performing disaster recovery planning?
- Hacking incident
- Flood
- Fire
- Terrorism
- II and III only
- I and IV only
- II, III, and IV only
- I, II, III, and IV
-
Glenda would like to conduct a disaster recovery test and is seeking a test that will allow a review of the plan with no disruption to normal information system activities and as minimal a commitment of time as possible. What type of test should she choose?
- Tabletop exercise
- Parallel test
- Full interruption test
- Checklist review
-
Which one of the following is not an example of a backup tape rotation scheme?
- Grandfather/Father/Son
- Meet in the middle
- Tower of Hanoi
- Six Cartridge Weekly
-
Helen is implementing a new security mechanism for granting employees administrative privileges in the accounting system. She designs the process so that both the employee’s manager and the accounting manager must approve the request before the access is granted. What information security principle is Helen enforcing?
- Least privilege
- Two-person control
- Job rotation
- Separation of duties
-
Which one of the following is not a requirement for evidence to be admissible in court?
- The evidence must be relevant.
- The evidence must be material.
- The evidence must be tangible.
- The evidence must be competent.
-
In which cloud computing model does a customer share computing infrastructure with other customers of the cloud vendor where one customer may not know the other’s identity?
- Public cloud
- Private cloud
- Community cloud
- Shared cloud
-
Which of the following organizations would be likely to have a representative on a CSIRT?
- Information security
- Legal counsel
- Senior management
- Engineering
- I, III, and IV
- I, II, and III
- I, II, and IV
- All of the above
-
Sam is responsible for backing up his company’s primary file server. He configured a backup schedule that performs full backups every Monday evening at 9 p.m. and differential backups on other days of the week at that same time. Files change according to the information shown in the following figure. How many files will be copied in Wednesday’s backup?
- 2
- 3
- 5
- 6

-
Which one of the following security tools is not capable of generating an active response to a security event?
- IPS
- Firewall
- IDS
- Antivirus software
-
In virtualization platforms, what name is given to the module that is responsible for controlling access to physical resources by virtual resources?
- Guest machine
- SDN
- Kernel
- Hypervisor
-
What term is used to describe the default set of privileges assigned to a user when a new account is created?
- Aggregation
- Transitivity
- Baseline
- Entitlement
-
Which one of the following types of agreements is the most formal document that contains expectations about availability and other performance parameters between a service provider and a customer?
- Service-level agreement (SLA)
- Operational-level agreement (OLA)
- Memorandum of understanding (MOU)
- Statement of work (SOW)
-
Which one of the following frameworks focuses on IT service management and includes topics such as change management, configuration management, and service level agreements?
- ITIL
- PMBOK
- PCI DSS
- TOGAF
-
Richard is experiencing issues with the quality of network service on his organization’s network. The primary symptom is that packets are consistently taking too long to travel from their source to their destination. What term describes the issue Richard is facing?
- Jitter
- Packet loss
- Interference
- Latency
-
Joe wants to test a program he suspects may contain malware. What technology can he use to isolate the program while it runs?
- ASLR
- Sandboxing
- Clipping
- Process isolation
-
Which one of the following is an example of a manmade disaster?
- Hurricane
- Flood
- Mudslide
- Transformer failure
-
Which of the following is not true about the (ISC)2 code of ethics?
- Adherence to the code is a condition of certification.
- Failure to comply with the code may result in revocation of certification.
- The code applies to all members of the information security profession.
- Members who observe a breach of the code are required to report the possible violation.
-
Javier is verifying that only IT system administrators have the ability to log on to servers used for administrative purposes. What principle of information security is he enforcing?
- Need to know
- Least privilege
- Two-person control
- Transitive trust
-
Which one of the following is not a basic preventative measure that you can take to protect your systems and applications against attack?
- Implement intrusion detection and prevention systems.
- Maintain current patch levels on all operating systems and applications.
- Remove unnecessary accounts and services.
- Conduct forensic imaging of all systems.
-
Tim is a forensic analyst who is attempting to retrieve information from a hard drive. It appears that the user attempted to erase the data, and Tim is trying to reconstruct it. What type of forensic analysis is Tim performing?
- Software analysis
- Media analysis
- Embedded device analysis
- Network analysis
-
Which one of the following is an example of a computer security incident?
- Completion of a backup schedule
- System access recorded in a log
- Unauthorized vulnerability scan of a file server
- Update of antivirus signatures
-
Which one of the following technologies would provide the most automation of an inventory control process in a cost-effective manner?
- IPS
- WiFi
- RFID
- Ethernet
-
Connor’s company recently experienced a denial of service attack that Connor believes came from an inside source. If true, what type of event has the company experienced?
- Espionage
- Confidentiality breach
- Sabotage
- Integrity breach
-
What type of attack is shown in the following figure?

- SYN flood
- Ping flood
- Smurf
- Fraggle
-
Florian is building a disaster recovery plan for his organization and would like to determine the amount of time that a particular IT service may be down without causing serious damage to business operations. What variable is Florian calculating?
- RTO
- MTD
- RPO
- SLA
-
Which one of the following statements best describes a zero-day vulnerability?
- An attacker who is new to the world of hacking
- A database attack that places the date 00/00/0000 in data tables in an attempt to exploit flaws in business logic
- An attack previously unknown to the security community
- An attack that sets the operating system date and time to 00/00/0000 and 00:00:00
-
Which one of the following is not a canon of the (ISC)2 code of ethics?
- Protect society, the common good, necessary public trust and confidence, and the infrastructure.
- Promptly report security vulnerabilities to relevant authorities.
- Act honorably, honestly, justly, responsibly, and legally.
- Provide diligent and competent service to principals.
-
During an incident investigation, investigators meet with a system administrator who may have information about the incident but is not a suspect. What type of conversation is taking place during this meeting?
- Interview
- Interrogation
- Both an interview and an interrogation
- Neither an interview nor an interrogation
-
Match each of the numbered types of recovery capabilities to their correct lettered definition:
Terms
- Hot site
- Cold site
- Warm site
- Service bureau
Definitions
- An organization that can provide onsite or offsite IT services in the event of a disaster
- A site with dedicated storage and real-time data replication, often with shared equipment that allows restoration of service in a very short time
- A site that relies on shared storage and backups for recovery
- A rented space with power, cooling, and connectivity that can accept equipment as part of a recovery effort
-
What technique has been used to protect the intellectual property in the following image?

- Steganography
- Clipping
- Sampling
- Watermarking
-
You are working to evaluate the risk of flood to an area and consult the flood maps from the Federal Emergency Management Agency (FEMA). According to those maps, the area lies within a 200-year flood plain. What is the annualized rate of occurrence (ARO) of a flood in that region?
- 200
- 0.01
- 0.02
- 0.005
-
Which one of the following individuals poses the greatest risk to security in most well-defended organizations?
- Political activist
- Malicious insider
- Script kiddie
- Thrill attacker
-
Veronica is considering the implementation of a database recovery mechanism recommended by a consultant. In the recommended approach, an automated process will move database backups from the primary facility to an offsite location each night. What type of database recovery technique is the consultant describing?
- Remote journaling
- Remote mirroring
- Electronic vaulting
- Transaction logging
-
When designing an access control scheme, Hilda set up roles so that the same person does not have the ability to provision a new user account and assign superuser privileges to an account. What information security principle is Hilda following?
- Least privilege
- Separation of duties
- Job rotation
- Security through obscurity
-
Reggie recently received a letter from his company’s internal auditors scheduling the kickoff meeting for an assessment of his group. Which of the following should Reggie not expect to learn during that meeting?
- Scope of the audit
- Purpose of the audit
- Expected timeframe
- Expected findings
-
Which one of the following events marks the completion of a disaster recovery process?
- Securing property and life safety
- Restoring operations in an alternate facility
- Restoring operations in the primary facility
- Standing down first responders
-
Melanie suspects that someone is using malicious software to steal computing cycles from her company. Which one of the following security tools would be in the best position to detect this type of incident?
- NIDS
- Firewall
- HIDS
- DLP
-
Brandon observes that an authorized user of a system on his network recently misused his account to exploit a system vulnerability against a shared server that allowed him to gain root access to that server. What type of attack took place?
- Denial of service
- Privilege escalation
- Reconnaissance
- Brute force
-
Carla has worked for her company for 15 years and has held a variety of different positions. Each time she changed positions, she gained new privileges associated with that position, but no privileges were ever taken away. What concept describes the sets of privileges she has accumulated?
- Entitlement
- Aggregation
- Transitivity
- Isolation
-
During what phase of the incident response process do administrators take action to limit the effect or scope of an incident?
- Detection
- Response
- Mitigation
- Recovery
- For questions 65–68, please refer to the following scenario:
- Ann is a security professional for a midsized business and typically handles log analysis and security monitoring tasks for her organization. One of her roles is to monitor alerts originating from the organization’s intrusion detection system. The system typically generates several dozen alerts each day, and many of those alerts turn out to be false alarms after her investigation.
- This morning, the intrusion detection system alerted because the network began to receive an unusually high volume of inbound traffic. Ann received this alert and began looking into the origin of the traffic.
-
At this point in the incident response process, what term best describes what has occurred in Ann’s organization?
- Security occurrence
- Security incident
- Security event
- Security intrusion
-
Ann continues her investigation and realizes that the traffic generating the alert is abnormally high volumes of inbound UDP traffic on port 53. What service typically uses this port?
- DNS
- SSH/SCP
- SSL/TLS
- HTTP
-
As Ann analyzes the traffic further, she realizes that the traffic is coming from many different sources and has overwhelmed the network, preventing legitimate uses. The inbound packets are responses to queries that she does not see in outbound traffic. The responses are abnormally large for their type. What type of attack should Ann suspect?
- Reconnaissance
- Malicious code
- System penetration
- Denial of service
-
Now that Ann understands that an attack has taken place that violates her organization’s security policy, what term best describes what has occurred in Ann’s organization?
- Security occurrence
- Security incident
- Security event
- Security intrusion
-
Frank is seeking to introduce a hacker’s laptop in court as evidence against the hacker. The laptop does contain logs that indicate the hacker committed the crime, but the court ruled that the search of the apartment that resulted in police finding the laptop was unconstitutional. What admissibility criteria prevents Frank from introducing the laptop as evidence?
- Materiality
- Relevance
- Hearsay
- Competence
-
Gordon suspects that a hacker has penetrated a system belonging to his company. The system does not contain any regulated information, and Gordon wishes to conduct an investigation on behalf of his company. He has permission from his supervisor to conduct the investigation. Which of the following statements is true?
- Gordon is legally required to contact law enforcement before beginning the investigation.
- Gordon may not conduct his own investigation.
- Gordon’s investigation may include examining the contents of hard disks, network traffic, and any other systems or information belonging to the company.
- Gordon may ethically perform “hack back” activities after identifying the perpetrator.
-
Which one of the following tools provides an organization with the greatest level of protection against a software vendor going out of business?
- Service level agreement
- Escrow agreement
- Mutual assistance agreement
- PCI DSS compliance agreement
-
Fran is considering new human resources policies for her bank that will deter fraud. She plans to implement a mandatory vacation policy. What is typically considered the shortest effective length of a mandatory vacation?
- Two days
- Four days
- One week
- One month
-
Which of the following events would constitute a security incident?
- An attempted network intrusion
- A successful database intrusion
- A malware infection
- A violation of a confidentiality policy
- An unsuccessful attempt to remove information from a secured area
- 2, 3, and 4
- 1, 2, and 3
- 4 and 5
- All of the above
-
Which one of the following traffic types should not be blocked by an organization’s egress filtering policy?
- Traffic destined to a private IP address
- Traffic with a broadcast destination
- Traffic with a source address from an external network
- Traffic with a destination address on an external network
-
Allie is responsible for reviewing authentication logs on her organization’s network. She does not have the time to review all logs, so she decides to choose only records where there have been four or more invalid authentication attempts. What technique is Allie using to reduce the size of the pool?
- Sampling
- Random selection
- Clipping
- Statistical analysis
-
You are performing an investigation into a potential bot infection on your network and wish to perform a forensic analysis of the information that passed between different systems on your network and those on the Internet. You believe that the information was likely encrypted. You are beginning your investigation after the activity concluded. What would be the best and easiest way to obtain the source of this information?
- Packet captures
- Netflow data
- Intrusion detection system logs
- Centralized authentication records
-
Which one of the following tools helps system administrators by providing a standard, secure template of configuration settings for operating systems and applications?
- Security guidelines
- Security policy
- Baseline configuration
- Running configuration
-
What type of disaster recovery test activates the alternate processing facility and uses it to conduct transactions but leaves the primary site up and running?
- Full interruption test
- Parallel test
- Checklist review
- Tabletop exercise
-
During which phase of the incident response process would an analyst receive an intrusion detection system alert and verify its accuracy?
- Response
- Mitigation
- Detection
- Reporting
-
In what virtualization model do full guest operating systems run on top of a virtualization platform?
- Virtual machines
- Software-defined networking
- Virtual SAN
- Application virtualization
-
What level of RAID is also known as disk mirroring?
- RAID-0
- RAID-1
- RAID-5
- RAID-10
-
Bruce is seeing quite a bit of suspicious activity on his network. It appears that an outside entity is attempting to connect to all of his systems using a TCP connection on port 22. What type of scanning is the outsider likely engaging in?
- FTP scanning
- Telnet scanning
- SSH scanning
- HTTP scanning
-
The historic ping of death attack is most similar to which of the following modern attack types?
- SQL injection
- Cross-site scripting
- Buffer overflow
- Brute-force password cracking
-
Roger recently accepted a new position as a security professional at a company that runs its entire IT infrastructure within an IaaS environment. Which one of the following would most likely be the responsibility of Roger’s firm?
- Configuring the network firewall
- Applying hypervisor updates
- Patching operating systems
- Wiping drives prior to disposal
-
What technique can application developers use to test applications in an isolated virtualized environment before allowing them on a production network?
- Penetration testing
- Sandboxing
- White box testing
- Black box testing
-
Gina is the firewall administrator for a small business and recently installed a new firewall. After seeing signs of unusually heavy network traffic, she checked the intrusion detection system, which reported that a SYN flood attack was under way. What firewall configuration change can Gina make to most effectively prevent this attack?
- Block SYN from known IPs.
- Block SYN from unknown IPs.
- Enable SYN-ACK spoofing at the firewall.
- Disable TCP.
-
What type of trust relationship extends beyond the two domains participating in the trust to one or more of their subdomains?
- Transitive trust
- Inheritable trust
- Nontransitive trust
- Noninheritable trust
-
Renee is a software developer who writes code in Node.js for her organization. The company is considering moving from a self-hosted Node.js environment to one where Renee will run her code on application servers managed by a cloud vendor. What type of cloud solution is Renee’s company considering?
- IaaS
- CaaS
- PaaS
- SaaS
-
Timber Industries recently got into a dispute with a customer. During a meeting with his account representative, the customer stood up and declared, “There is no other solution. We will have to take this matter to court.” He then left the room. When does Timber Industries have an obligation to begin preserving evidence?
- Immediately
- Upon receipt of a notice of litigation from opposing attorneys
- Upon receipt of a subpoena
- Upon receipt of a court order
-
What legal protection prevents law enforcement agencies from searching a facility or electronic system without either probable cause or consent?
- First Amendment
- Fourth Amendment
- Fifth Amendment
- Fifteenth Amendment
-
Darcy is a computer security specialist who is assisting with the prosecution of a hacker. The prosecutor requests that Darcy give testimony in court about whether, in her opinion, the logs and other records in a case are indicative of a hacking attempt. What type of evidence is Darcy being asked to provide?
- Expert opinion
- Direct evidence
- Real evidence
- Documentary evidence
-
Which one of the following techniques is not commonly used to remove unwanted remnant data from magnetic tapes?
- Physical destruction
- Degaussing
- Overwriting
- Reformatting
-
What is the minimum number of disks required to implement RAID level 1?
- One
- Two
- Three
- Five
-
Jerome is conducting a forensic investigation and is reviewing database server logs to investigate query contents for evidence of SQL injection attacks. What type of analysis is he performing?
- Hardware analysis
- Software analysis
- Network analysis
- Media analysis
-
Quantum Computing regularly ships tapes of backup data across the country to a secondary facility. These tapes contain confidential information. What is the most important security control that Quantum can use to protect these tapes?
- Locked shipping containers
- Private couriers
- Data encryption
- Media rotation
-
Carolyn is concerned that users on her network may be storing sensitive information, such as Social Security numbers, on their hard drives without proper authorization or security controls. What technology can she use to best detect this activity?
- IDS
- IPS
- DLP
- TLS
-
Under what type of software license does the recipient of software have an unlimited right to copy, modify, distribute, or resell a software package?
- GNU Public License
- Freeware
- Open source
- Public domain
-
In what type of attack do attackers manage to insert themselves into a connection between a user and a legitimate website?
- Man-in-the-middle
- Fraggle
- Wardriving
- Meet-in-the-middle
-
Which one of the following techniques uses statistical methods to select a small number of records from a large pool for further analysis with the goal of choosing a set of records that is representative of the entire pool?
- Clipping
- Randomization
- Sampling
- Selection
-
Which one of the following controls protects an organization in the event of a sustained period of power loss?
- Redundant servers
- Uninterruptible power supply (UPS)
- Generator
- RAID
-
What concept from the Federal Rules of Civil Procedure (FCRP) helps to ensure that additional time and expense are not incurred as part of electronic discovery when the benefits do not outweigh the costs?
- Tool-assisted review
- Cooperation
- Spoilation
- Proportionality
-
Anne wants to gather information about security settings as well as build an overall view of her organization’s assets by gathering data about a group of Windows 10 workstations spread throughout her company. What Windows tool is best suited to this type of configuration management task?
- SCCM
- Group Policy
- SCOM
- A custom PowerShell script
-
Scott is responsible for disposing of disk drives that have been pulled from his company’s SAN as they are retired. Which of the following options should he avoid if the data on the SAN is considered highly sensitive by his organization?
- Destroy them physically
- Sign a contract with the SAN vendor that requires appropriate disposal and provides a certification process
- Reformat each drive before it leaves the organization
- Use a secure wipe tool like DBAN
-
What documentation is typically prepared after a postmortem review of an incident has been completed?
- A lessons learned document
- A risk assessment
- A remediation list
- A mitigation checklist
-
Staff from Susan’s company often travel internationally. Susan believes that they may be targeted for corporate espionage activities because of the technologies that her company is developing. What practice should Susan recommend that they adopt for connecting to networks while they travel?
- Only connect to public Wi-Fi
- Use a VPN for all connections
- Only use websites that support TLS
- Do not connect to networks while traveling
-
Matt wants to ensure that critical network traffic from systems throughout his company is prioritized over web browsing and social media use at this company. What technology can he use to do this?
- VLANs
- QoS
- VPN
- ISDN
-
John deploys his website to multiple regions using load balancers around the world through his cloud infrastructure as a service provider. What availability concept is he using?
- Multiple processing sites
- Warm sites
- Cold sites
- A honeynet
-
Lauren wants to ensure that her users only run software that her organization has approved. What technology should she deploy?
- Blacklisting
- Configuration management
- Whitelisting
- Graylisting
-
When one of the employees of Alice’s company calls in for support, she uses a code word that the company agreed to use if employees were being forced to perform an action. What is this scenario called?
- Social engineering
- Duress
- Force majeure
- Stockholm syndrome
