CHAPTER 10
Physical Security and Authentication Models
This chapter covers the following subjects:
![]() Physical Security: An organization’s building is one of its greatest assets and as such it should be properly protected. This section details door access, biometric readers, access logs, and video surveillance to teach you some of the ways to protect the building, its contents, and its inhabitants and to ensure proper authentication when a person enters a building.
Physical Security: An organization’s building is one of its greatest assets and as such it should be properly protected. This section details door access, biometric readers, access logs, and video surveillance to teach you some of the ways to protect the building, its contents, and its inhabitants and to ensure proper authentication when a person enters a building.
![]() Authentication Models and Components: You can use various methods and models to authenticate a person who wants to access computer networks and resources. This section delves into local authentication technologies such as Kerberos, LDAP, and 802.1X, and remote authentication types such as VPN and RADIUS.
Authentication Models and Components: You can use various methods and models to authenticate a person who wants to access computer networks and resources. This section delves into local authentication technologies such as Kerberos, LDAP, and 802.1X, and remote authentication types such as VPN and RADIUS.
I suppose that at times life on this planet is all about proving oneself. The world of security is no different. To gain access to an organization’s building and ultimately to its resources, you must first prove yourself in a physical manner, providing indisputable evidence of your identity. Then, perhaps you can gain access by being authenticated, as long as the system authenticating you accepts your identification. Finally, if all this goes through properly, you should be authorized to specific resources such as data files, printers, and so on.
Some people use the terms identification, authentication, and authorization synonymously. Although this might be somewhat acceptable in everyday conversation, we need to delve a bit deeper and attempt to make some distinctions among the three.
![]() Identification: When a person is in a state of being identified. It can also be described as something that identifies a person such as an ID card.
Identification: When a person is in a state of being identified. It can also be described as something that identifies a person such as an ID card.
![]() Authentication: When a person’s identity is confirmed or verified through the use of a specific system. Authorization to specific resources cannot be accomplished without previous authentication of the user. This might also be referred to as access control, but generally authentication is considered to be a component of access control.
Authentication: When a person’s identity is confirmed or verified through the use of a specific system. Authorization to specific resources cannot be accomplished without previous authentication of the user. This might also be referred to as access control, but generally authentication is considered to be a component of access control.
![]() Authorization: When a user is given permission to access certain re-sources. This can be accomplished only when authentication is complete.
Authorization: When a user is given permission to access certain re-sources. This can be accomplished only when authentication is complete.
The CompTIA Security+ exam concentrates most on the terms authentication and access control. This chapter focuses mostly on the authentication portion of access control. The rest of access control is covered in Chapter 11, “Access Control Methods and Models."
First, we cover the physical ways that a person can be authenticated. Then, we move on to ways that a person can be authenticated to a computer network, whether that person is attempting to connect locally (for example, on the LAN) or attempting to connect remotely (for example, via a VPN).
Authentication is required to gain access to a secure area of the building or to gain access to secure data. People might identify themselves in several ways depending on the authentication scheme used, by presenting one or more of the following:

![]() Something the user knows: Such as a password or personal identification number (PIN). These are also known as knowledge factors.
Something the user knows: Such as a password or personal identification number (PIN). These are also known as knowledge factors.
![]() Something the user has: Such as a smart card or ID card. These are also known as possession factors.
Something the user has: Such as a smart card or ID card. These are also known as possession factors.
![]() Something the user does: Such as a signature or gesture.
Something the user does: Such as a signature or gesture.
![]() Something the user is: Such as a thumbprint or retina scan or other biometric. These are also known as inherence factors.
Something the user is: Such as a thumbprint or retina scan or other biometric. These are also known as inherence factors.
![]() Somewhere the user is: Such as “at work,” “at the home office,” or “on the road.”
Somewhere the user is: Such as “at work,” “at the home office,” or “on the road.”
Another term you might hear in your travels is identity proofing, which is an initial validation of an identity. For example, when employees working for a government agency want to enter a restricted building, the first thing they must do is show their ID. A guard or similar person then does an initial check of that ID. Additional authentication systems would undoubtedly ensue. Identity proofing is also when an entity validates the identity of a person applying for a certain credential with that entity. It could be used for anonymous access as well.
As you go through this chapter and read about the following physical and logical authentication technologies, try to remember this introduction and apply these concepts to each of those authentication types.
Foundation Topics
Physical Security
To control access, physical security can be considered the first line of defense, sort of like a firewall is the first line of defense for a network. Implementing physical access security methods should be a top priority for an organization. Unfortunately, securing physical access to the organization’s building sometimes slumps to the bottom of the list. Or a system is employed, but it fails to mitigate risk properly. In some cases, the system is not maintained well. Proper building entrance access and secure access to physical equipment are vital. And anyone coming and going should be logged and surveyed. Let’s discuss a few of the ways that we can secure physical access to an organization’s building.
General Building and Server Room Security
Protecting an organization’s building is an important step in general security. The more security a building has, the less you have to depend on your authentication system. A building’s perimeter should be surveyed for possible breaches; this includes all doors, windows, loading docks, and even the roof. The area around the building should be scanned for hiding places; if there are any they should be removed. The area surrounding the building should be well lit at night. Some companies may opt to use security guards and guard dogs. It is important that these are trained properly; usually an organization will enlist the services of a third-party security company. Video surveillance can also be employed to track an individual’s movements. Video cameras should be placed on the exterior perimeter of the building in an area hard to access; for example, 12 feet or higher with no lateral or climbing access. The more well-hidden the cameras are the better. Video cameras can also be placed inside the building, especially in secure areas such as executive offices, wiring closets, server rooms, and research and development areas. Many organizations use closed-circuit television (CCTV), but some opt for a wired/wireless IP-based solution. Either way, the video stream may be watched and recorded, but it should not be broadcast. Video cameras are an excellent way of tracking user identities. However, proper lighting is necessary inside and outside in order for the cameras to capture images well. Also, video cameras must be properly secured as they are prime targets for reverse-engineering techniques where the attacker attempts to gain access to the pan-tilt-zoom (PTZ) controls and redirect the video feed. Motion detectors and other sensors are also common as part of a total alarm system. They are often infrared-based (set off by heat) or ultrasonic-based (set off by certain higher frequencies). We could go on and on about general building security, but this chapter focuses on authentication. Besides, I think you get the idea. If your organization is extremely concerned about building security, and doubts that it has the knowledge to protect the building and its contents properly, consider hiring a professional.
The server room is the lifeblood in today’s organizations. If anything happens to the server room, the company could be in for a disaster. We talk more about how an organization can recover from disasters in Chapter 16, “Redundancy and Disaster Recovery,” but the best policy is to try to avoid disasters before they happen. So, there are some things you should think about when it comes to server room security. First, where is the server room to be placed? It’s wise to avoid basements or any other areas that might be prone to water damage. Second, the room should be accessible only to authorized IT persons. This can be accomplished by using one of many door access systems. The room should also have video surveillance saved to a hard drive located in a different room of the building or stored offsite. All devices and servers in the server room should have complex passwords that only the authorized IT personnel have knowledge of. Devices and servers should be physically locked down with cable locks to prevent theft. If necessary, network cabling to each server should be approved circuits and meet the requirements for protected distribution systems. We discuss wired security in Chapter 9, “Securing Network Media and Devices,” and talk more about server room security and building security in Chapter 16 and Chapter 18, “Policies and Procedures."
Note
Security doesn’t just mean securing data; it also means user safety—keeping an organization’s employees secure. To this end, properly planned fire drills, exit signs, escape plans, and escape routes are all vital. We’ll discuss this more in Chapter 18.
For now, let’s focus on how to impede unauthorized access. Secure door access is the number one way to stop intruders from getting into the building or server room. If the system is set up properly, then the intruder cannot be authenticated. Let’s talk about door access in a little more depth.
Door Access
Lock the door! Sounds so simple, yet it is often overlooked. As a person in charge of security for a small business or even a midsized business, you must think about all types of security, including entrances to the building. Door locks are essential. When deciding on a locking system to use, you should take into account the type of area your building is in and the crime rate, and who will have authorized access to the building. If you purchase regular door locks that work with a key, it is recommended that you get two or three of them. The first one should be tested. Can you break in to it with a credit card, jeweler’s screwdriver, or other tools? And a backup should always be on hand in case the current door lock gets jimmied in an attempt to force a break-in. Cipher locks are a decent solution when regular key locks are not enough but you don’t want to implement an electronic system. The cipher lock uses a punch code to lock the door and unlock it. Though it will have a relatively low number of combinations, the fact that they have to be attempted manually makes it difficult to get past them.
Of course, many organizations (and especially government) get more technical with their door access systems. Electronic access control systems such as cardkey systems are common. These use scanning devices on each door used for access to the building. They read the cardkeys that you give out to employees and visitors. These cardkeys should be logged; it should be known exactly who has which key at all times. The whole system is guided by a cardkey controller. This controller should be placed in a wiring closet or in a server room, and that room should be locked as well (and protected by the cardkey system). Some companies implement separate cardkey systems for the server room and for the main entrances. Some systems use photo ID badges for identification and authentication to a building’s entrance. They might have a magnetic stripe similar to a credit card, or they might have a barcode or use an RFID chip. A key card door access system is another good practice for tracking user identities.
Note
Hardware-based security tokens are physical devices given to authorized users to help with authentication. These devices might be attached to a keychain or might be part of a card system. Hardware-based tokens might be used as part of the door access system or as something that gives access to an individual computer. As one example, RSA tokens carry and generate rolling one-time passwords (OTPs), each of which is valid for only one login session or transaction.
Another possibility is the smart card. The smart card falls into the category of “something a person has” and is known as a token. It’s the size of a credit card and has an embedded chip that stores and transacts data for use in secure applications such as hotel guest room access, prepaid phone services, and more. Smart cards have multiple applications, one of which is to authenticate users by swiping the card against a scanner, thus securing a computer or a computer room. The smart card might have a photo ID as well. Examples of smart cards include the PIV card (Personal Identity Verification), which is required for all U.S. government employees and contractors, and the Common Access Card (CAC), which is used to identify Department of Defense (DoD) military personnel, other DoD civilian government employees, and so on. These cards not only identify the person and are responsible for authentication to buildings and systems, but can also encrypt and digitally sign e-mails. These cards might be used as part of a multifactor authentication scheme in which there is a combination of username/password (or PIN) and a smart card. Advanced smart cards have specialized cryptographic hardware that can use algorithms such as RSA and 3DES but generally use private keys to encrypt data. (More on encryption and these encryption types is provided in Chapter 14, “Encryption and Hashing Concepts.") A smart card might incorporate a microprocessor (as is the case with the PIV and CAC cards). A smart card security system usually is composed of the smart card itself, smart card readers, and a back-office database that stores all the smart card access control lists and history.
Older technologies use proximity sensors, but this is not considered very secure today. However, the more complex the technology, the more it costs. Often, in these situations, budgeting becomes more important to organizations than mitigating risk; and generally, the amount of acceptable risk increases as the budget decreases. So, you will probably see proximity-based door access systems. HID (also known as HID Global) is an example of a company that offers various levels of door access control systems.
To increase security of the entrances of the building, some organizations implement mantraps, which are areas between two doorways, meant to hold people until they are identified and authenticated. This might be coupled with security guards, video surveillance, multifactor authentication, and sign-in logs. The main purpose of a physical access log or sign-in log is to show who entered the facility and when.
Door access systems are considered by many to be the weakest link in an enterprise. This can be taken to the next level by also incorporating biometrics, thus creating a different type of multifactor authentication scheme.
Biometric Readers
Biometrics is the science of recognizing humans based on one or more physical characteristics. Biometrics is used as a form of authentication and access control. It is also used to identify persons who might be under surveillance.
Biometrics falls into the category of “something a person is.” Examples of bodily characteristics that are measured include fingerprints, retinal patterns, iris patterns, voice patterns, and even facial/bone structure. Biometric readers (for example, fingerprint scanners) are becoming more common in door access systems and on laptops or as USB devices. Biometric information can also be incorporated into smart card technology. An example of a biometric door access system provider is Suprema, which has various levels of access systems, including some that incorporate smart cards and biometrics, together forming a multifactor authentication system. There are lots of providers of fingerprint scanners (also called fingerprint readers) for desktops and laptops also; these fingerprint recognition systems are usually USB-based.
Sometimes there are failures in which a biometric authentication system will improperly categorize people. These include the following:
![]() False acceptance: This is when a biometric system authenticates a user who should not be allowed access to the system.
False acceptance: This is when a biometric system authenticates a user who should not be allowed access to the system.
![]() False rejection: This is when a biometric system denies a user who should actually be allowed access to the system.
False rejection: This is when a biometric system denies a user who should actually be allowed access to the system.
A security admin should monitor the biometric system for errors. Generally, if either the false acceptance rate (FAR) or the false rejection rate (FRR) goes above 1%, it should be investigated further—perhaps .1% for some organizations. More importantly, the two should be collectively analyzed with the crossover error rate (CER). This is also known as the equal error rate (EER) because the goal is to keep both the FAR and FRR errors at a common value, or as close as possible. The lower the CER, the better the biometric system in general. This is one of the main metrics to use when analyzing biometric system performance.
Biometrics can be seen in many movies and TV shows. However, many biometric systems historically have been easily compromised. It has only been of late that readily available biometric systems have started to live up to the hype. Thorough investigation and testing of a biometric system is necessary before purchase and installation. In addition, it should be used in a multifactor authentication scheme. The more factors the better, as long as your users can handle it. (You would be surprised what a little bit of training can do.) Voice recognition software has made great leaps and bounds since the turn of the millennium. A combination of biometrics, voice recognition, and PIN access would make for an excellent three-factor authentication system. But as always, only if you can get it through budgeting!
Authentication Models and Components
Now that we’ve covered some physical authentication methods, let’s move into authentication models, components, and technologies used to grant or deny access to operating systems and computer networks.
The first thing a security administrator should do is plan what type of authentication model to use. Then, consider what type of authentication technology and how many factors of authentication will be implemented. Also for consideration is how the authentication system will be monitored and logged. Getting more into the specifics, will only local authentication be necessary? Or will remote authentication also be needed? And which type of technology should be utilized? Will it be Windows-based or a third-party solution? Let’s discuss these concepts now and give some different examples of the possible solutions you can implement.
Authentication Models
Many small businesses and even some midsized businesses often have one type of authentication to gain access to a computer network—the username and password. In today’s security-conscious world, this is not enough for the average organization. Some companies share passwords or fail to enforce password complexity. In addition, password-cracking programs are becoming more and more powerful and work much more quickly than they did just five years ago, making the username and password authentication scheme limiting. Not to say that it shouldn’t be used, but perhaps it should be enforced, enhanced, and integrated with other technologies.
Because of the limitations of a single type of authentication such as username and password, organizations sometimes use multiple factors of authentication. Multifactor authentication (MFA) is when two or more types of authentication are used for user access control. An example of multifactor authentication would be when a user needs to sign in with a username and password and swipe some type of smart card or use some other type of physical token at the same time. Adding factors of authentication makes it more difficult for a malicious person to gain access to a computer network or an individual computer system. Sometimes an organization uses three factors of authentication—perhaps a smart card, biometrics, and a username/password. The disadvantages of a multifactor authentication scheme are that users need to remember more information and remember to bring more identification with them, and more IT costs and more administration will be involved. Another disadvantage of some MFA environments is that they are static—rules and whitelists/blacklists are usually configured manually. A more dynamic way of authenticating individuals is to utilize context-aware authentication (also known as context-sensitive access). It is an adaptive way of authenticating users based on their usage of resources, and the confidence that the system has in the user. It can automatically increase the level of identification required and/or increase or decrease the level of access to resources based on constant analysis of the user.
Some organizations have several computer systems that an individual user might need access to. By default, each of these systems will have a separate login. It can be difficult for users to remember the various logins. Single sign-on (SSO) is when a user can log in once but gain access to multiple systems without being asked to log in again. This is complemented by single sign-off, which is basically the reverse; logging off signs off a person from multiple systems. Single sign-on is meant to reduce password fatigue, or password chaos, which is when a person can become confused and possibly even disoriented when having to log in with several different usernames and passwords. It is also meant to reduce IT help desk calls and password resets. By implementing a more centralized authentication scheme such as single sign-on, many companies have reduced IT costs significantly. If implemented properly, single sign-on can also reduce phishing. In large networks and enterprise scenarios, it might not be possible for users to have a single sign-on, and in these cases, it might be referred to as reduced sign-on. Single sign-on can be Kerberos-based, integrated with Windows authentication, or token- or smart card-based.
SSO is a derivative of federated identity management (also called FIM or FIdM). This is when a user’s identity, as well as the user’s attributes, is shared across multiple identity management systems. These various systems can be owned by one organization; for example, Microsoft offers the Forefront Identity Manager software, which can control user accounts across local and cloud environments. Also, Google, Yahoo!, and Amazon are examples of companies that utilize this federation approach. But, some providers join forces so that information can be shared across multiple services and environments between the companies, yet still allow the user a single login. Shibboleth is an example of an SSO system that allows people to sign in with a single digital identity and connect to various systems run by federations of different organizations. SSO systems—and federated systems in general—will often incorporate the concept of transitive trust where two networks (or more) have a relationship such that users logging in to one network get access to data on the other.
While an SSO is easier for the user to remember, it acts as a single point of failure as well. In addition, sometimes a company might not be watching out for the user’s best interests—either unwittingly or otherwise—and might fail to realize that multiple systems have been configured as a transitive trust. We mentioned the transitive trust concept in Chapter 7, “Networking Protocols and Threats." When it comes to authentication, it can be especially damaging. Let’s say that a user has an account with Company A, and has a separate account with Company B. Imagine that Companies A and B have a two-way trust. Now, let’s say there is a third organization, Company C, that has a two-way trust with Company B. At this point, the user’s account information from Companies A and B could be shared with Company C, even though the user never signed up with that company. This kind of activity is frowned upon, but the user might not even know when it happens—two companies might merge, or a company might be bought out or otherwise absorbed by another. So, when it comes to authentication, it is sometimes wise to avoid trust relationships, and strongly consider whether single sign-on will ultimately be more beneficial or costly to your organization.
Another concern is web-based SSO. Web-based SSO can be problematic due to disparate proprietary technologies. To help alleviate this problem, the XML-based Security Assertion Markup Language (SAML) and the OpenID Connect protocol were developed. OpenID Connect is an interoperable authentication protocol based on the OAuth 2.0 family of specifications. It uses straightforward REST/JSON message flows with a design goal of “making simple things simple and complicated things possible.” Both OpenID Connect and SAML specify separate roles for the user, the service provider, and the identity provider. Shibboleth is also based on SAML.
Whatever the type of authentication scheme used, it needs to be monitored periodically to make sure that it’s working properly. The authentication system should block people who cannot furnish proper identification, and should allow access to people who do have proper identification. Let’s talk about some of those authentication technologies now.
Localized Authentication Technologies
There are several types of technologies for authenticating a user to a local area network. Examples that are software-based include LDAP and Kerberos, whereas an example that includes physical characteristics would be 802.1X. Keep in mind that there is a gray area between localized and remote authentication technologies. I’ve placed each technology in the category in which it is used the most commonly.
During this section and the next one, we mention several encryption concepts that work with the various authentication technologies. These encryption concepts and protocols are covered in detail in Chapter 14 and Chapter 15, “PKI and Encryption Protocols.”
802.1X and EAP
802.1X is an IEEE standard that defines port-based network access control (PNAC). Not to be confused with 802.11x WLAN standards, 802.1X is a data link layer authentication technology used to connect hosts to a LAN or WLAN. 802.1X allows you to apply a security control that ties physical ports to end-device MAC addresses, and prevents additional devices from being connected to the network. It is a good way of implementing port security, much better than simply setting up MAC filtering.
It all starts with the central connecting device such as a switch or wireless access point. These devices must first enable 802.1X connections; they must have the 802.1X protocol (and supporting protocols) installed. Vendors that offer 802.1X-compliant devices (for example, switches and wireless access points) include Cisco, Symbol Technologies, and Intel. Next, the client computer needs to have an operating system, or additional software, that supports 802.1X. The client computer is known as the supplicant. All recent Windows versions support 802.1X. macOS/OS X offers support as well, and Linux computers can use Open1X to enable client access to networks that require 802.1X authentication.
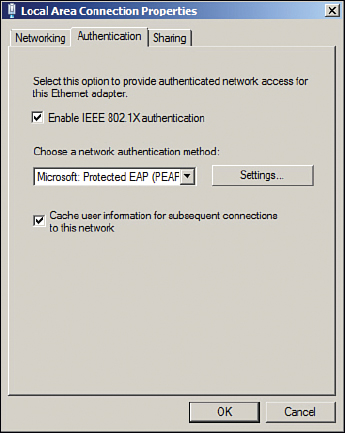
802.1X encapsulates the Extensible Authentication Protocol (EAP) over wired or wireless connections. EAP is not an authentication mechanism in itself, but instead defines message formats. 802.1X is the authentication mechanism and defines how EAP is encapsulated within messages. An example of an 802.1X-enabled network adapter is shown in Figure 10-1. In the figure, you can see that the box for enabling 802.1X has been checked, and that the type of network authentication method for 802.1X is EAP— specifically, Protected EAP (PEAP).

Note
802.1X can be enabled in Windows by accessing the Local Area Connection Properties page.
Following are three components to an 802.1X connection:
![]() Supplicant: A software client running on a workstation. This is also known as an authentication agent.
Supplicant: A software client running on a workstation. This is also known as an authentication agent.
![]() Authenticator: A wireless access point or switch.
Authenticator: A wireless access point or switch.
![]() Authentication server: An authentication database, most likely a RADIUS server.
Authentication server: An authentication database, most likely a RADIUS server.
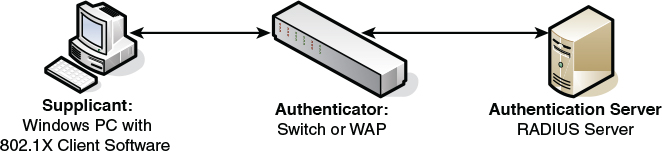
The typical 802.1X authentication procedure has four steps. The components used in these steps are illustrated in Figure 10-2.

Step 1. Initialization: If a switch or wireless access point detects a new supplicant, the port connection enables port 802.1X traffic; other types of traffic are dropped.
Step 2. Initiation: The authenticator (switch or wireless access point) periodically sends EAP requests to a MAC address on the network. The supplicant listens for this address and sends an EAP response that might include a user ID or other similar information. The authenticator encapsulates this response and sends it to the authentication server.
Step 3. Negotiation: The authentication server then sends a reply to the authenticator. The authentication server specifies which EAP method to use. (These are listed next.) Then the authenticator transmits that request to the supplicant.
Step 4. Authentication: If the supplicant and the authentication server agree on an EAP method, the two transmit until there is either success or failure to authenticate the supplicant computer.
Following are several types of EAP authentication:
![]() EAP-MD5: This is a challenge-based authentication providing basic EAP support. It enables only one-way authentication and not mutual authentication.
EAP-MD5: This is a challenge-based authentication providing basic EAP support. It enables only one-way authentication and not mutual authentication.
![]() EAP-TLS: This version uses Transport Layer Security, which is a certificate-based system that does enable mutual authentication. This does not work well in enterprise scenarios because certificates must be configured or managed on the client side and server side.
EAP-TLS: This version uses Transport Layer Security, which is a certificate-based system that does enable mutual authentication. This does not work well in enterprise scenarios because certificates must be configured or managed on the client side and server side.
![]() EAP-TTLS: This version is Tunneled Transport Layer Security and is basically the same as TLS except that it is done through an encrypted channel, and it requires only server-side certificates.
EAP-TTLS: This version is Tunneled Transport Layer Security and is basically the same as TLS except that it is done through an encrypted channel, and it requires only server-side certificates.
![]() EAP-FAST: This uses a protected access credential instead of a certificate to achieve mutual authentication. FAST stands for Flexible Authentication via Secure Tunneling.
EAP-FAST: This uses a protected access credential instead of a certificate to achieve mutual authentication. FAST stands for Flexible Authentication via Secure Tunneling.
![]() PEAP: This is the Protected Extensible Authentication Protocol (also known as Protected EAP). This uses MS-CHAPv2, which supports authentication via Microsoft Active Directory databases. It competes with EAP-TTLS and includes legacy password-based protocols. It creates a TLS tunnel by acquiring a public key infrastructure (PKI) certificate from a server known as a certificate authority (CA). The TLS tunnel protects user authentication much like EAP-TTLS. More information on PKI and CAs can be found in Chapter 15.
PEAP: This is the Protected Extensible Authentication Protocol (also known as Protected EAP). This uses MS-CHAPv2, which supports authentication via Microsoft Active Directory databases. It competes with EAP-TTLS and includes legacy password-based protocols. It creates a TLS tunnel by acquiring a public key infrastructure (PKI) certificate from a server known as a certificate authority (CA). The TLS tunnel protects user authentication much like EAP-TTLS. More information on PKI and CAs can be found in Chapter 15.
Cisco also created a proprietary protocol called LEAP (Lightweight EAP), and it is just that—proprietary. To use LEAP, you must have a Cisco device such as an Aironet WAP or Catalyst switch, or another vendor’s device that complies with the Cisco Compatible Extensions program. Then you must download a third-party client on Windows computers to connect to the Cisco device. Most WLAN vendors offer an 802.1X LEAP download for their wireless network adapters.
Although 802.1X is often used for port-based network access control on the LAN, especially VLANs, it can also be used with VPNs as a way of remote authentication. Central connecting devices such as switches and wireless access points remain the same, but on the client side 802.1X would need to be configured on a VPN adapter, instead of a network adapter.
Many vendors, such as Intel and Cisco, refer to 802.1X with a lowercase x; however, the IEEE displays this on its website with an uppercase X, as does the IETF. The protocol was originally defined in 2001 (802.1X-2001) and has been redefined in 2004 and 2010 (802.1X-2004 and 802.1X-2010, respectively). There are several links to more information about 802.1X in the “View Recommended Resources” document on this book’s companion website.
LDAP
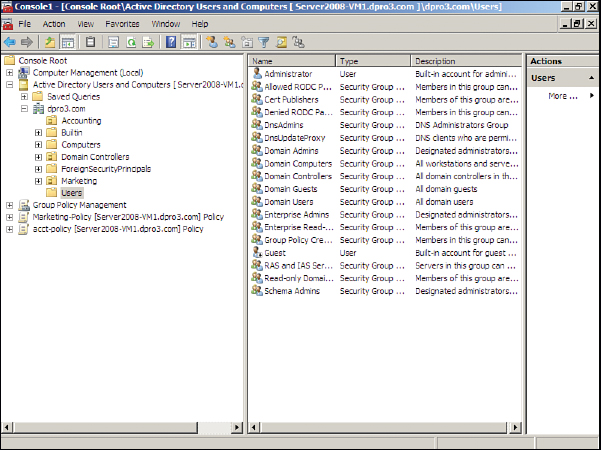
The Lightweight Directory Access Protocol (LDAP) is an application layer protocol used for accessing and modifying directory services data. It is part of the TCP/IP suite. Originally used in WAN connections, it has developed over time into a protocol commonly used by services such as Microsoft Active Directory on Windows Server domain controllers. LDAP acts as the protocol that controls the directory service. This is the service that organizes the users, computers, and other objects within the Active Directory. An example of the Active Directory is shown in Figure 10-3. Take note of the list of users (known as objects of the Active Directory) from the Users folder that is highlighted. Also observe other folders such as Computers that house other objects (such as Windows client computers).

Note
Windows servers running Active Directory use parameters and variables when querying the names of objects. For example, CN=dprowse, where CN stands for common name and dprowse is the username. Taking it to the next level: DC=ServerName. DC stands for domain component. ServerName is the variable and is the name of the server. Microsoft is famous for using the name “fabrikam” as its test name, but it would be whatever your server name is. In the case of fabrikam, an entire LDAP query might look something like this:
<LDAP://DC=Fabrikam, DC=COM>
A Microsoft server that has Active Directory and LDAP running will have inbound port 389 open by default. To protect Active Directory from being tampered with, Secure LDAP can be used—also known as LDAPS. This brings into play SSL (Secure Sockets Layer) on top of LDAP and uses inbound port 636 by default. Other implementations of LDAP use TLS (Transport Layer Security) over LDAP.
Kerberos and Mutual Authentication
Kerberos is an authentication protocol designed at MIT that enables computers to prove their identity to each other in a secure manner. It is used most often in a client-server environment; the client and the server both verify each other’s identity. This is known as two-way authentication or mutual authentication. Often, Kerberos protects a network server from illegitimate login attempts, just as the mythological three-headed guard dog of the same name (also known as Cerberus) guards Hades.
A common implementation of Kerberos occurs when a user logs on to a Microsoft domain. (Of course, I am not saying that Microsoft domains are analogous to Hades!) The domain controller in the Microsoft domain is known as the key distribution center (KDC). This server works with tickets that prove the identity of users. The KDC is composed of two logical parts: the authentication server and the ticket-granting server. Basically, a client computer attempts to authenticate itself to the authentication server portion of the KDC. When it does so successfully, the client receives a ticket. This is actually a ticket to get other tickets—known as a ticket granting ticket (TGT). The client uses this preliminary ticket to demonstrate its identity to a ticket-granting server in the hopes of ultimately getting access to a service—for example, making a connection to the Active Directory of a domain controller.
The domain controller running Kerberos will have inbound port 88 open to the service logon requests from clients. Figure 10-4 shows a netstat -an command run on a Windows Server that has been promoted to a domain controller. It points out port 88 (used by Kerberos) and port 389 (used by LDAP) on the same domain controller.

Kerberos is designed to protect against replay attacks and eavesdropping. One of the drawbacks of Kerberos is that it relies on a centralized server such as a domain controller. This can be a single point of failure. To alleviate this problem, secondary and tertiary domain controllers can be installed that keep a copy of the Active Directory and are available with no downtime in case the first domain controller fails. Another possible issue is one of synchronicity. Time between the clients and the domain controller must be synchronized for Kerberos to work properly. If for some reason a client attempting to connect to a domain controller becomes desynchronized, it cannot complete the Kerberos authentication, and as an end result the user cannot log on to the domain. This can be fixed by logging on to the affected client locally and synchronizing the client’s time to the domain controller by using the net time command. For example, to synchronize to the domain controller in Figure 10-4, the command would be
net time \10.254.254.252 /set
Afterward, the client should be able to connect to the domain. We revisit Kerberos and how it makes use of encryption keys in Chapter 14.
Kerberos—like any authentication system—is vulnerable to attack. Older Windows operating systems that run, or connect to, Kerberos are vulnerable to privilege escalation attacks; and newer Windows operating systems are vulnerable to spoofing. Of course, Microsoft will quickly release updates for these kinds of vulnerabilities (as they are found), but for the security administrator who does not allow Windows Update to automatically update, it’s important to review the CVEs for the Microsoft systems often.
Note
In a Red Hat Enterprise environment that uses an SSO such as Kerberos, pluggable authentication modules (PAMs) can be instrumental in providing the systems admin/security admin flexibility and control over authentication, as well as fully documented libraries for the developer.
Remote Desktop Services
Remote Desktop Services enables the remote control of Windows computers (most importantly for this section, Windows servers) from a client computer. This client computer could be on the LAN or out on the Internet, so the term “remote” is used loosely. It can also be used to enable client access to specific applications.
In Windows Server 2008, it is configured within Remote Desktop Management Server, and in Windows Server 2012 R2 and higher it is configured via the Remote Desktop Services server role. This application is in charge of authenticating remote users and will do so if the user has been configured properly. For example, users in question must have Remote Access permissions enabled within the properties of their account. Remote Desktop Services authentication integrates directly with standard Windows Server authentication. The remote desktop will have inbound port 3389 open to accept connections from remote clients. Client sessions are stored at the Windows Server running Remote Desktop Services, which allows for disconnections and later reuse.
Note
Remote Desktop Services is still often referred to as its original name, Terminal Services. In fact, the underlying service name is actually still called “TermService.”
Some of the vulnerabilities to Remote Desktop Services—and the Remote Desktop Protocol in general, otherwise known as RDP—include an extremely well-known port, comparatively weak encryption, and a lack of multifactor authentication. Because of this, you might choose to utilize another remote control application. At this point, security is relative, and your decision on what tool to use will be based on the type of data you are protecting.
As mentioned, the port is 3389 by default, and is extremely well known. But it can be modified within the inbound computer’s Registry at the following path:
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTerminal Server
WinStationsRDP-Tcp
Third-party applications such as VNC, TeamViewer, and so on can be more secure in this respect because they can use web-based connections via HTTPS on port 443. Out-of-the-box, RDP is generally limited to SSL (TLS 1.0) with a 128-bit key based on the RC4 algorithm (which is considered crackable, though difficult to do so). However, RDP can also comply with Federal Information Processing Standard (FIPS) 140 encryption methods, but additional hardware and software modules are required, which might incur an unacceptable expense. On the other hand, third-party remote control applications such as the ones mentioned earlier will often use RSA encryption for the HTTPS connection, and the Advanced Encryption Standard (AES) with up to 256-bit keys for session security. Some third-party applications also offer multifactor authentication; for example, a passcode in combination with the standard username/password login. However, multifactor authentication could always be added to RDP as a separate module (at a price). Your final decision of what application to use will be based on cost, the number of remote connections required, the platforms you need to support, and, of course, the level of security you desire.
Remote Authentication Technologies
Even more important than authenticating local users is authenticating remote users. The chances of illegitimate connections increase when you allow remote users to connect to your network. Examples of remote authentication technologies include RAS, VPN, RADIUS, TACACS+, and CHAP. Let’s discuss these now.
Remote Access Service
Remote Access Service (RAS) began as a service that enabled dial-up connections from remote clients. Nowadays, more and more remote connections are made with high-speed Internet technologies such as cable Internet, DSL, and fiber-optic connections. But we can’t discount the dial-up connection. It is used in certain areas where other Internet connections are not available, and is still used as a fail-safe in many network operation centers and server rooms to take control of networking equipment.
One of the best things you can do to secure a RAS server is to deny access to individuals who don’t require it. Even if the user or user group is set to “not configured,” it is wise to specifically deny them access. Allow access to only those users who need it, and monitor on a daily basis the logs that list who connected. If there are any unknowns, investigate immediately. Be sure to update the permissions list often in the case that a remote user is terminated or otherwise leaves the organization.
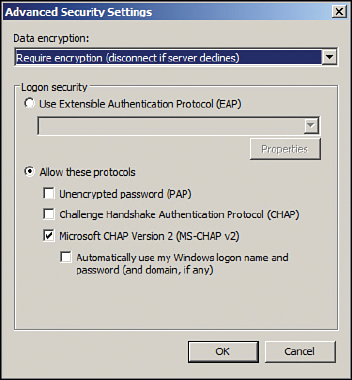
The next most important security precaution is to set up RAS authentication. One secure way is to use the Challenge-Handshake Authentication Protocol (CHAP), which is an authentication scheme used by the Point-to-Point Protocol (PPP), which in turn is the standard for dial-up connections. It uses a challenge-response mechanism with one-way encryption. Due to this, it is not capable of mutual authentication in the way that Kerberos is, for example. CHAP uses DES and MD5 encryption types, which we cover in Chapter 14. Microsoft developed its own version of CHAP known as MS-CHAP; an example of this is shown in Figure 10-5. The figure shows the Advanced Security Settings dialog box of a dial-up connection. Notice that this particular configuration shows that encryption is required, and that the only protocol allowed is MS-CHAPv2. It’s important to use version 2 of MS-CHAP because it provides for mutual authentication between the client and the authenticator. Of course, the RAS server has to be configured to accept MS-CHAP connections as well. You also have the option to enable EAP for the dial-up connection. Other RAS authentication protocols include SPAP, which is of lesser security, and PAP, which sends usernames and passwords in clear text—obviously insecure and to be avoided.

Note
Use CHAP, MS-CHAP, or EAP for dial-up connections. Verify that it is configured properly on the RAS server and dial-up client to ensure a proper handshake.
The CHAP authentication scheme consists of several steps. It authenticates a user or a network host to entities such as Internet access providers. CHAP periodically verifies the identity of the client by using a three-way handshake. The verification is based on a shared secret. After the link has been established, the authenticator sends a challenge message to the peer. The encrypted results are compared, and finally the client is either authorized or denied access.
The actual data transmitted in these RAS connections is encrypted as well. By default, Microsoft RAS connections are encrypted by the RSA RC4 algorithm. More information on this can also be found in Chapter 14.
Now you might say, “But Dave, who cares about dial-up connections?” Well, there are two reasons that they are important. First, the supporting protocols, authentication types, and encryption types are used in other technologies; this is the basis for those systems. Second, as I mentioned before, some organizations still use the dial-up connection—for remote users or for administrative purposes. And hey, don’t downplay the dial-up connection. Old-school dial-up guys used to tweak the connection to the point where it was as fast as some DSL versions and as reliable. So, there are going to be die-hards out there as well. Plus, there are some areas of the United States, and the rest of the world, that have no other option than dial-up.
However, RAS now has morphed into something that goes beyond just dial-up. VPN connections that use dial-up, cable Internet, DSL, and so on are all considered remote access.
Virtual Private Networks
A virtual private network (VPN) is a connection between two or more computers or devices not on the same private network. Generally, VPNs use the Internet to connect one host to another. It is desirable that only proper users and data sessions make their way to a VPN device; because of this, data encapsulation and encryption are used. A “tunnel’ is created through any LANs and WANs that might intervene; this tunnel connects the two VPN devices together. Every time a new session is initiated, a new tunnel is created, which makes the connection secure.
PPTP and L2TP are common VPN connections that can cause a lot of havoc if the security settings are not configured properly on the client side and the server side. This can cause errors; you can find a link to the list of these error codes in the “View Recommended Resources” document online. We cover PPTP and L2TP encryption methods in Chapter 15.
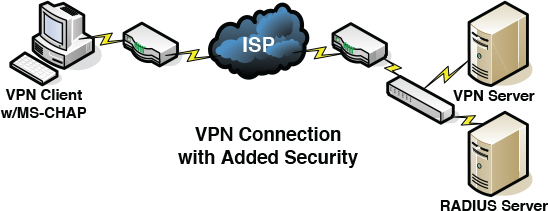
Figure 10-6 shows an illustration of a VPN. Note that the VPN server is on one side of the cloud, and the VPN client is on the other. It should be known that the VPN client will have a standard IP address to connect to its own LAN. However, it will receive a second IP address from the VPN server or a DHCP device. This second IP address works “inside” the original IP address. So, the client computer will have two IP addresses; in essence, the VPN address is encapsulated within the logical IP address. As previously mentioned, dial-up authentication protocols such as CHAP are also used in other technologies; this is one of those examples. VPN adapters, regardless of the Internet connection used, can use MS-CHAP, as shown in Figure 10-6. To further increase authentication security, a separate RADIUS server can be used with the VPN server—we talk more about RADIUS in the next section.

Figure 10-6 illustrates a single computer connecting to a VPN server at an office, which is typical and is known as VPN remote access. However, organizations sometimes need to connect multiple offices to each other. This is done with a site-to-site configuration, where each site has a VPN device (SOHO router, concentrator, or server) that takes care of VPN connections for each network of computers. Site-to-site VPNs are generally more secure because an admin can specify that only specific networks can connect—and can do it in a private intranet fashion. If a company is growing, site-to-site is the way to go, whether the company is flourishing geographically or is simply inhabiting a separate space of the same building. When separate networks are connected in the same building, it is often wise to use a VPN, because the physical wiring might pass through a public area.
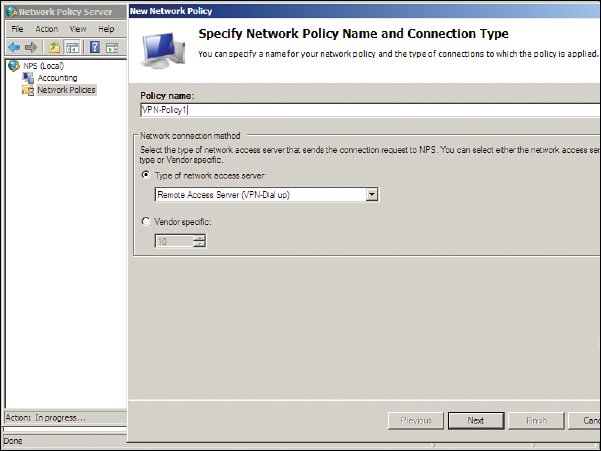
A Microsoft VPN can be set up on a standard Windows Server by configuring Routing and Remote Access Service (RRAS). Remote access policies can be created from here that permit or deny access to groups of users for dial-in or VPN connections. In a typical Windows Server you would need to set up RRAS as part of the Network Policy and Access Services role. Then you would right-click the Remote Access Logging & Policies node and access the Network Policy Server (NPS) window to create a new RRAS policy. Figure 10-7 displays the initiation of a RRAS VPN policy.
Note
You could also configure DirectAccess if you have Windows Server 2008 R2 (or higher) and Windows 7 clients (or higher) to implement a Microsoft-based VPN.
You don’t have to use a server for incoming VPN sessions. Hardware appliances are offered by several vendors. Larger organizations that need hundreds of simultaneous connections should opt for a VPN concentrator as their solution. Or, it might be part of your unified threat management (UTM) solution.
Older VPNs use either PPTP (port 1723) or L2TP (port 1701) with IPsec. They can also incorporate CHAP on the client side and RADIUS servers for authentication. Newer VPNs protect traffic by using SSL or TLS. For example, OpenVPN uses this type of encryption (https://openvpn.net/). SSL/TLS solutions for VPN improve on endpoint security and enable always-on VPN functionality—where a user can always have access via the VPN without the need to periodically disconnect and reconnect.
Watch out for split tunneling. This is when a client system (for example, a mobile device) can access a public network and a LAN at the same time using one or more network connections. For example, a remote user might connect to the Internet through a hotel’s Wi-Fi network. If the user needs to access resources on the company LAN, the VPN software will take control. But if the user needs to connect to websites on the Internet, the hotel’s gateway will provide those sessions. While this can provide for bandwidth conservation and increase efficiency, it can also bypass upper-layer security in place within the company infrastructure. While it is common, split tunneling should be tested thoroughly before being allowed by administrators. For example, simulate the split tunnel from a remote location, then perform vulnerability scans and capture packets. Analyze the session in depth and log your findings.
Cisco systems use the Generic Routing Encapsulation (GRE) protocol to encapsulate a lot of different data, namely, routing information that passes between VPN-enabled connected networks that use PPTP or IPsec. GRE might also make use of Multiprotocol Label Switching (MPLS), a packet-forwarding technology that uses labels to make data forwarding decisions. With MPLS, the Layer 3 header analysis is done just once (when the packet enters the MPLS domain). Label inspection drives subsequent packet forwarding. It is a natural evolution for networks that provide predictable IP services.
There is a minor amount of risk when using MPLS due to its open-ended nature, and when connecting from MPLS to non-MPLS networks. To mitigate this, the MPLS over GRE feature provides a mechanism for tunneling MPLS packets over a non-MPLS network. This feature utilizes MPLS over Generic Routing Encapsulation (MPLSoGRE) to encapsulate MPLS packets inside IP tunnels. The encapsulation of MPLS packets inside IP tunnels creates a virtual point-to-point link across non-MPLS networks.
RADIUS Versus TACACS
We mentioned RADIUS previously in this chapter and in Chapter 9, and said that it could be used in combination with a SOHO router in order to provide strong authentication. Let’s define it further: The Remote Authentication Dial-In User Service (RADIUS) provides centralized administration of dial-up, VPN, and wireless authentication and can be used with EAP and 802.1X. To set this up on a Windows Server, the Internet Authentication Service must be loaded; it is usually set up on a separate physical server. RADIUS is a client-server protocol that runs on the application layer of the OSI model.
RADIUS works within the AAA concept: It is used to authenticate users, authorize them to services, and account for the usage of those services. RADIUS checks whether the correct authentication scheme such as CHAP or EAP is used when clients attempt to connect. It commonly uses port 1812 for authentication messages and port 1813 for accounting messages (both of which use UDP as the transport mechanism). In some proprietary cases, it uses ports 1645 and 1646 for these messages, respectively. Memorize these four ports for the exam!
Another concept you will encounter is that of RADIUS federation. This is when an organization has multiple RADIUS servers—possibly on different networks—that need to communicate with each other in a safe way. It is accomplished by creating trust relationships and developing a core to manage those relationships as well as the routing of authentication requests. It is often implemented in conjunction with 802.1X. This federated network authentication could also span between multiple organizations.
Note
Another protocol similar to RADIUS—though not as commonly used—is the Diameter protocol. Once again, it’s an AAA protocol. It evolves from RADIUS by supporting TCP or SCTP, but not UDP. It uses port 3868.
Moving on, the Terminal Access Controller Access-Control System (TACACS) is one of the most confusing-sounding acronyms ever. Now that we have reached the pinnacle of computer acronyms, let’s really discuss what it is. TACACS is another remote authentication protocol that was used more often in Unix networks. In Unix, the TACACS service is known as the TACACS daemon. The newer and more commonly used implementation of TACACS is called Terminal Access Controller Access-Control System Plus (TACACS+). It is not backward compatible with TACACS. TACACS+, and its predecessor XTACACS, were developed by Cisco. TACACS+ uses inbound port 49 like its forerunners; however, it uses TCP as the transport mechanism instead of UDP. Let’s clarify: the older TACACS and XTACACS technologies are not commonly seen anymore. The two common protocols for remote authentication used today are RADIUS and TACACS+.
There are a few differences between RADIUS and TACACS+. Whereas RADIUS uses UDP as its transport layer protocol, TACACS+ uses TCP as its transport layer protocol, which is usually seen as a more reliable transport protocol (though each will have its own unique set of advantages). Also, RADIUS combines the authentication and authorization functions when dealing with users; however, TACACS+ separates these two functions into two separate operations that introduce another layer of security. It also separates the accounting portion of AAA into its own operation.
RADIUS encrypts only the password in the access-request packet, from the client to the server. The remainder of the packet is unencrypted. Other information such as the username can be easily captured, without need of decryption, by a third party. However, TACACS+ encrypts the entire body of the access-request packet. So, effectively TACACS+ encrypts entire client-server dialogues, whereas RADIUS does not. Finally, TACACS+ provides for more types of authentication requests than RADIUS.
Table 10-1 summarizes the local and remote authentication technologies we have covered thus far.

Table 10-1 Summary of Authentication Technologies
Authentication Type |
Description |
802.1X |
An IEEE standard that defines Port-based Network Access Control (PNAC). 802.1X is a data link layer authentication technology used to connect devices to a LAN or WLAN. Defines EAP. |
LDAP |
An application layer protocol used for accessing and modifying directory services data. It is part of the TCP/IP suite. Originally used in WAN connections, it has morphed into a protocol commonly used by services such as Microsoft Active Directory. |
Kerberos |
An authentication protocol designed at MIT that enables computers to prove their identity to each other in a secure manner. It is used most often in a client-server environment; the client and the server both verify each other’s identity. |
RAS |
A service that enables dial-up and various types of VPN connections from remote clients. |
CHAP |
An authentication scheme used by the Point-to-Point Protocol (PPP) that is the standard for dial-up connections. It utilizes a challenge-response mechanism with one-way encryption. Derivatives include MS-CHAP and MS-CHAPv2. |
RADIUS |
Used to provide centralized administration of dial-up, VPN, and wireless authentication. It can be used with EAP and 802.1X. Uses ports 1812 and 1813, or 1645 and 1646, over a UDP transport. |
TACACS+ |
Remote authentication developed by Cisco, similar to RADIUS but separates authentication and authorization into two separate processes. Uses port 49 over a TCP transport. |
Chapter Summary
Users must constantly prove themselves to the world of technology. It’s amazing how many times a person can be authenticated during a typical day. An authentication method could be as simple as typing an e-mail address and password; for example, when logging into a web-based e-mail system. Or, it could be as complex as a multifactor authentication system; where a user is required to enter a password, then a PIN, then swipe a smart card, and finally scan a thumb!
The complexity of the authentication system will be based on the confidentiality level of an organization’s data and resources. If a person can supply the necessary identification and credentials, and the system is configured properly, that person should be authenticated to the system, and finally authorized to access data, or enter a server room, or whatever the case may be. The authentication system can include methods such as: something the user knows, something the user has, something the user does, something the user is, and somewhere the user is. These systems span from the physical (door access systems and biometrics) to the logical (localized and remote authentication software/hardware). In some cases, to make things easier for the end user, an SSO is utilized where the user need only remember one password. Sometimes it’s not even the user who is authenticated, but the computer itself; for example, when a network adapter adheres to the 802.1X protocol.
Authentication systems can fail. For example, in biometric systems, the most common failures are false acceptance—when a system authenticates a user who should not be allowed access to the system, and false rejection—when a system denies a user who should be allowed access to the system. A system that has too many failures will cause user distress, and should be reconfigured and tested carefully. One of the best metrics to analyze this failure rate is the crossover error rate (CER), which compares the false acceptance rate (FAR) to the false rejection rate (FRR).
Examples of localized authentication systems include 802.1X, LDAP, Kerberos, and RDP. Examples of remote authentication systems include RAS, VPNs, and RADIUS. However, there is a gray area here. Some local systems can be used for remote access, and vice versa. Remember: This is not a cut-and-dried technology in general; for example, RDP could be used locally or over the Internet. It all hinges on what your organization needs for its end users. Nowadays, more and more people work from home or on the road, making remote authentication vital to the organization’s efficiency and overall production.
One thing to keep in mind is that attackers (and con artists) are very smart. In fact, the sad truth is that they are sometimes smarter than IT people. A poorly designed authentication system is tantamount to leaving the physical key in the door. However, a well-planned authentication system can save an organization millions of dollars and untold man hours in the long run.
Chapter Review Activities
Use the features in this section to study and review the topics in this chapter.
Review Key Topics
Review the most important topics in the chapter, noted with the Key Topic icon in the outer margin of the page. Table 10-2 lists a reference of these key topics and the page number on which each is found.

Table 10-2 Key Topics for Chapter 10
Key Topic Element |
Description |
Page Number |
Bulleted list |
Authentication methods |
|
Example of an 802.1X-enabled network adapter in Windows |
||
Components of a typical 802.1X authentication procedure |
||
Example of Active Directory showing user objects |
||
Results of the |
||
MS-CHAP enabled on a dial-up connection |
||
Illustration of a VPN |
||
Summary of authentication technologies |
Define Key Terms
Define the following key terms from this chapter, and check your answers in the glossary:
identification, authentication, authorization, identity proofing, closed-circuit television (CCTV), security tokens, mantrap, biometrics, false acceptance, false rejection, crossover error rate (CER), multifactor authentication (MFA), context-aware authentication, single sign-on (SSO), federated identity management, 802.1X, Extensible Authentication Protocol (EAP), Protected Extensible Authentication Protocol (PEAP), Lightweight Directory Access Protocol (LDAP), Kerberos, mutual authentication, tickets, Remote Access Service (RAS), Challenge-Handshake Authentication Protocol (CHAP), virtual private network (VPN), VPN concentrator, always-on VPN, Remote Authentication Dial-In User Service (RADIUS), Terminal Access Controller Access-Control System Plus (TACACS+)
Complete the Real-World Scenarios
Complete the Real-World Scenarios found on the companion website (www.pearsonitcertification.com/title/9780789758996). You will find a PDF containing the scenario and questions, and also supporting videos and simulations.
Review Questions
Answer the following review questions. Check your answers with the correct answers that follow.
1. Which of the following is the verification of a person’s identity?
A. Authorization
B. Accountability
C. Authentication
D. Password
2. Which of the following would fall into the category of “something a person is”?
A. Passwords
B. Passphrases
C. Fingerprints
D. Smart cards
3. Which of the following are good practices for tracking user identities? (Select the two best answers.)
A. Video cameras
B. Key card door access systems
C. Sign-in sheets
D. Security guards
4. What are two examples of common single sign-on authentication configurations? (Select the two best answers.)
A. Biometrics-based
B. Multifactor authentication
C. Kerberos-based
D. Smart card-based
5. Which of the following is an example of two-factor authentication?
A. L2TP and IPsec
B. Username and password
C. Thumbprint and key card
D. Client and server
6. What is the main purpose of a physical access log?
A. To enable authorized employee access
B. To show who exited the facility
C. To show who entered the facility
D. To prevent unauthorized employee access
7. Which of the following is not a common criteria when authenticating users?
A. Something you do
B. Something you are
C. Something you know
D. Something you like
8. Of the following, what two authentication mechanisms require something you physically possess? (Select the two best answers.)
A. Smart card
B. Certificate
C. USB flash drive
D. Username and password
9. Which of the following is the final step a user needs to take before that user can access domain resources?
A. Verification
B. Validation
C. Authorization
D. Authentication
10. To gain access to your network, users must provide a thumbprint and a username and password. What type of authentication model is this?
A. Biometrics
B. Domain logon
C. Multifactor
D. Single sign-on
11. The IT director has asked you to set up an authentication model in which users can enter their credentials one time, yet still access multiple server resources. What type of authentication model should you implement?
A. Smart card and biometrics
B. Three-factor authentication
C. SSO
D. VPN
12. Which of the following about authentication is false?
A. RADIUS is a client-server system that provides authentication, authorization, and accounting services.
B. PAP is insecure because usernames and passwords are sent as clear text.
C. MS-CHAPv2 is not capable of mutual authentication of the client and server.
D. CHAP is more secure than PAP because it encrypts usernames and passwords.
13. What types of technologies are used by external motion detectors? (Select the two best answers.)
A. Infrared
B. RFID
C. Gamma rays
D. Ultrasonic
14. In a secure environment, which authentication mechanism performs better?
A. RADIUS because it is a remote access authentication service.
B. RADIUS because it encrypts client-server passwords.
C. TACACS+ because it is a remote access authentication service.
D. TACACS+ because it encrypts client-server negotiation dialogues.
15. Which port number does the protocol LDAP use when it is secured?
A. 389
B. 443
C. 636
D. 3389
16. Which of the following results occurs when a biometric system identifies a legitimate user as unauthorized?
A. False rejection
B. FAR
C. False acceptance
D. CER
E. False exception
17. Of the following, which is not a logical method of access control?
A. Username/password
B. Access control lists
C. Biometrics
D. Software-based policy
18. Which of the following permits or denies access to resources through the use of ports?
A. Hub
B. 802.11n
C. 802.11x
D. 802.1X
19. Your data center has highly critical information. Because of this you want to improve upon physical security. The data center already has a video surveillance system. What else can you add to increase physical security? (Select the two best answers.)
A. A software-based token system
B. Access control lists
C. A mantrap
D. Biometrics
20. Which authentication method completes the following in order: logon request, encrypts value response, server, challenge, compare encrypted results, and authorize or fail referred to?
A. Security tokens
B. Certificates
C. Kerberos
D. CHAP
21. What does a virtual private network use to connect one remote host to another? (Select the best answer.)
A. Modem
B. Network adapter
C. Internet
D. Cell phone
22. Two items are needed before a user can be given access to the network. What are these two items?
A. Authentication and authorization
B. Authorization and identification
C. Identification and authentication
D. Password and authentication
23. Kerberos uses which of the following? (Select the two best answers.)
A. Ticket distribution service
B. The Faraday cage
C. Port 389
D. Authentication service
24. Which of the following authentication systems makes use of a Key Distribution Center?
A. Security tokens
B. CHAP
C. Kerberos
D. Certificates
25. Of the following, which best describes the difference between RADIUS and TACACS+?
A. RADIUS is a remote access authentication service.
B. RADIUS separates authentication, authorization, and auditing capabilities.
C. TACACS+ is a remote access authentication service.
D. TACACS+ separates authentication, authorization, and auditing capabilities.
26. Which of the following best describes the proper method and reason to implement port security?
A. Apply a security control that ties specific ports to end-device MAC addresses, and prevents additional devices from being connected to the network.
B. Apply a security control that ties specific ports to end-device IP addresses, and prevents additional devices from being connected to the network.
C. Apply a security control that ties specific ports to end-device MAC addresses, and prevents all devices from being connected to the network.
D. Apply a security control that ties specific ports to end-device IP addresses, and prevents all devices from being connected to the network.
27. You are tasked with setting up a wireless network that uses 802.1X for authentication. You set up the wireless network using WPA2 and CCMP; however, you don’t want to use a PSK for authentication. Which of the following options would support 802.1X authentication?
A. Kerberos
B. CAC card
C. Pre-shared key
D. RADIUS
28. Which two options can prevent unauthorized employees from entering a server room? (Select the two best answers.)
A. Bollards
B. CCTV
C. Security guard
D. 802.1X
E. Proximity reader
29. What is the most secure method of authentication and authorization in its default form?
A. TACACS
B. Kerberos
C. RADIUS
D. LDAP
30. When attempting to grant access to remote users, which protocol uses separate, multiple-challenge responses for each of the authentication, authorization, and audit processes?
A. RADIUS
B. TACACS
C. TACACS+
D. LDAP
31. Before gaining access to the data center, you must swipe your finger on a device. What type of authentication is this?
A. Biometrics
B. Single sign-on
C. Multifactor
D. Tokens
32. Which of the following is an authentication system that uses UDP as the transport mechanism?
A. LDAP
B. Kerberos
C. RADIUS
D. TACACS+
33. Your organization provides employee badges that are encoded with a private encryption key and specific personal information. The encoding is used to provide access to the organization’s network. What type of authentication method is being used?
A. Token
B. Biometrics
C. Kerberos
D. Smart card
34. You are in charge of training a group of technicians on the authentication method their organization uses. The organization currently runs an Active Directory infrastructure. Which of the following best correlates to the host authentication protocol used within that organization’s IT environment?
A. TACACS+
B. Kerberos
C. LDAP
D. 802.1X
35. Which of the following is an authentication and accounting service that uses TCP as its transport mechanism when connecting to routers and switches?
A. Kerberos
B. RADIUS
C. Captive portal
D. TACACS+
Answers and Explanations
1. C. Authentication is the verification of a person’s identity. Authorization to specific resources cannot be accomplished without previous authentication of the user.
2. C. Fingerprints are an example of something a person is. The process of measuring that characteristic is known as biometrics.
3. A and B. Video cameras enable a person to view and visually identify users as they enter and traverse a building. Key card access systems can be configured to identify a person as well, as long as the right person is carrying the key card!
4. C and D. Kerberos and smart card setups are common single sign-on configurations.
5. C. Two-factor authentication (or dual-factor) means that two pieces of identity are needed prior to authentication. A thumbprint and key card would fall into this category. L2TP and IPsec are protocols used to connect through a VPN, which by default require only a username and password. Username and password is considered one-factor authentication. There is no client and server authentication model.
6. C. A physical access log’s main purpose is to show who entered the facility and when. Different access control and authentication models will be used to permit or prevent employee access.
7. D. Common criteria when authenticating users include something you do, something you are, something you know, something you have, and somewhere you are. A person’s likes and dislikes are not common criteria; although, they may be asked as secondary questions when logging in to a system.
8. A and C. Two of the authentication mechanisms that require something you physically possess include smart cards and USB flash drives. Key fobs and cardkeys would also be part of this category. Certificates are granted from a server and are stored on a computer as software. The username/password mechanism is a common authentication scheme, but it is something that you type and not something that you physically possess.
9. C. Before a user can gain access to domain resources, the final step is to be authorized to those resources. Previously the user should have provided identification to be authenticated.
10. C. Multifactor authentication means that the user must provide two different types of identification. The thumbprint is an example of biometrics. Username and password are examples of a domain logon. Single sign-on would only be one type of authentication that enables the user access to multiple resources.
11. C. SSO (single sign-on) enables users to access multiple servers and multiple resources while entering their credentials only once. The type of authentication can vary but will generally be a username and password. Smart cards and biometrics is an example of two-factor authentication. VPN is short for virtual private network.
12. C. MS-CHAPv2 is capable of mutual authentication of the client and server. However, MS-CHAPv1 is not. That’s why it is important to use MS-CHAPv2. Mutual authentication is accomplished with Kerberos. All the other statements are true.
13. A and D. Motion detectors often use infrared technology; heat would set them off. They also use ultrasonic technology; sounds in higher spectrums that humans cannot hear would set these detectors off.
14. D. Unlike RADIUS, TACACS+ (Terminal Access Controller Access-Control System Plus) encrypts client-server negotiation dialogues. Both protocols are remote authentication protocols.
15. C. Port 636 is the port used to secure LDAP (called LDAPS). Port 389 is the standard LDAP port number. Port 443 is used by HTTPS (SSL/TLS), and port 3389 is used by RDP.
16. A. If a biometric system identifies a legitimate user as unauthorized, and denies that user access, it is known as a false rejection. False acceptance on the other hand is when a biometric system authorizes an illegitimate user. FAR is the false acceptance rate—the lower the better. CER stands for crossover error rate, which is the comparison of the FAR and the FRR. False exceptions have to do with software that has failed and needs to be debugged.
17. C. The only answer that is not a logical method of access control is biometrics. Biometrics deals with the physical attributes of a person and is the most tangible of the answers. All the rest deal with software, so they are logical methods.
18. D. 802.1X permits or denies access to resources through the use of ports. It implements Port-based Network Access Control (PNAC). This is part of the 802.1 group of IEEE protocols. 802.1X should not be confused with 802.11x, which is an informal term used to denote any of the 802.11 standards including 802.11b, 802.11g, 802.11n, and 802.11ac. A hub connects computers by way of physical ports but does not permit or deny access to any particular resources; it is a simple physical connector of computers.
19. C and D. A mantrap is a device made to capture a person. It is usually an area with two doorways, the first of which leads to the outside and locks when the person enters, the second of which leads to the secure area and is locked until the person is granted access. Biometrics can help in the granting of this access by authenticating the user in a secure way, such as thumbprint, retina scan, and so on. Software-based token systems and access control lists are both logical and do not play into physical security.
20. D. CHAP, the Challenge Handshake Authentication Protocol, authenticates a user or a network host to entities like Internet access providers. CHAP periodically verifies the identity of the client by using a three-way handshake; the verification is based on a shared secret. After a link has been established, the authenticator sends a challenge message to the peer; this does not happen in the other three authentication methods listed.
21. C. The Internet is used to connect hosts to each other in virtual private networks. A particular computer will probably also use a VPN adapter and/or a network adapter. Modems generally are used in dial-up connections and are not used in VPNs.
22. C. Before users can be given access to the network, the network needs to identify them and authenticate them. Later, users may be authorized to use particular resources on the network. Part of the authentication scheme may include a username and password. This would be known as an access control method.
23. A and D. Kerberos uses a ticket distribution service and an authentication service. This is provided by the Key Distribution Center. A Faraday cage is used to block data emanations. Port 389 is used by LDAP. One of the more common ports that Kerberos uses is port 88.
24. C. Kerberos uses a KDC (key distribution center) to centralize the distribution of certificate keys and keep a list of revoked keys.
25. D. Unlike RADIUS, TACACS+ separates authentication, authorization, and auditing capabilities. The other three answers are incorrect and are not differences between RADIUS and TACACS+.
26. A. You can achieve port security by applying a security control (such as 802.1X), which ties specific physical ports to end-device MAC addresses and prevents additional devices from being connected to the network. Note that port security solutions such as 802.1X are data link layer technologies (layer 2) so they deal with MAC addresses, not IP addresses. You wouldn’t want to exclude all devices from being connected to the network as this would cause a severe problem with connectivity.
27. D. RADIUS is a common back-end authenticator for 802.1X. When setting up a wireless access point, the two security mode options are usually PSK (pre-shared key), which is stored on the WAP, and Enterprise, which usually refers authentication to an external RADIUS server. Kerberos deals with authentication to Microsoft domains. CAC cards are smart cards that are used for ID and authentication to systems.
28. C and E. If a person doesn’t have the proper proximity card, that person will be prevented from entering a server room or other protected room. Security guards can also prevent people from accessing unauthorized areas. However, bollards (short vertical posts) probably wouldn’t stop a person, besides they aren’t normally installed in front of a server room entrance. A barricade might stop a person, but again, would be out of place! CCTV video surveillance is a detective control, but not a preventive control. 802.1X deals with authentication, not with physical security.
29. B. Kerberos is the most secure method of authentication listed. It has a more complicated system of authentication than TACACS (which is outdated) and RADIUS (which is used in different scenarios than Kerberos). LDAP deals with directories (for example, the ones on a Microsoft domain controller), which Kerberos first needs to give access to.
30. C. TACACS+ is the only answer listed that uses separate processes for authentication, authorization, and auditing. That is one of the main differences between it and RADIUS. TACACS is deprecated and is not often seen in the field. LDAP deals with managing directories of information.
31. A. Fingerprint technology is part of the realm of biometrics. Single sign-on means that you can use one type of authentication to get access to more than one system. While that could be going on in this scenario, it is not explicit, so biometrics is the more accurate answer. Multifactor means that more than one type of authentication is needed; for example, a fingerprint and a PIN. Let’s say that users were expected to type a PIN into a keypad to gain access to the data center. You might find over time that some persons who enter don’t match the owner of the PIN. That uncertainty can be avoided by incorporating biometrics. Tokens are used to gain access to systems and networks, and might include rolling one-time passwords, but do not incorporate a person’s physical characteristics such as a fingerprint.
32. C. RADIUS is the authentication system that uses UDP as the transport mechanism. The others all use TCP. Remember, RADIUS uses ports 1812 and 1813 (or 1645 and 1646), LDAP uses 389 (or 636 for secure LDAP), Kerberos uses port 88, and TACACS+ uses port 49.
33. D. A badge encoded with a private encryption key would be an example of a smart card. Tokens are software-based and could be used with a USB flash drive or could be stored on a mobile device. An example of biometrics is a thumbprint scan or retina scan. Kerberos is an authentication technology used by operating systems such as Windows (often in domain scenarios).
34. B. If the organization runs Active Directory, that means it has a Windows Server that is acting as a domain controller. These use the Kerberos authentication system by default. TACACS+ is an example of a remote authentication system, but is owned by Cisco, and is not a part of Active Directory. LDAP is the protocol in Windows that controls Active Directory objects, and works in conjunction with Kerberos, but is not the actual authentication method used. 802.1X is an authentication method used by network adapters on the data link layer.
35. D. TACACS+ is an authentication, accounting, and authorization service. It uses TCP as its transport mechanism. Kerberos authenticates only, and can use TCP and UDP. RADIUS performs authentication and accounting but uses UDP as the transport mechanism. A captive portal redirects people in an effort to authenticate them. It will often do this within a web browser, and might use TCP (HTTPS), but does not perform accounting services.