Chapter 2
Planning and Scoping
EXAM OBJECTIVES
- Understanding key legal concepts
- Scoping the project and identifying the rules of engagement
- Defining targets and ensuring acceptance to risk
- Scheduling and handling scope creep
Good penetration testers know that before starting a penetration test, they must spend time with the customer scoping out the project and setting the rules of engagement. Planning and scoping is a critical phase of the pentest process, as too often penetration testers dive right into trying to compromise systems without giving any thought to the ramifications of their actions. Not planning the penetration test properly can result in crashing the customer’s systems or network (causing loss in production and revenue) and triggering intrusion detection systems. A lack of planning can also create legal problems due to a failure to obtain proper authorization to perform the penetration test.
In this chapter, you learn the importance of planning for the penetration test by jumping into the first phase of the CompTIA penetration testing process: planning and scoping.
Understanding Key Legal Concepts
The CompTIA PenTest+ certification exam is sure to have a few questions regarding the legal concepts surrounding a penetration test that come into play during the planning and scoping phase. The following sections outline the three most important concepts you should be aware of: obtaining written authorization, contract types, and the importance of disclaimers.
Written authorization
It is illegal to hack into systems without proper authorization from the owner of the asset being compromised. As a penetration tester, you have to remember this. Before any pentest can start, you must first get written permission in the form of a signed contract from the customer in order to conduct the work. Once the contract is signed, you then schedule a planning and scoping meeting with the customer so that you can identify the goals for the penetration test, identify what should be tested, and understand how far the testing should go.
It is important to understand that often this authorization cannot come from an office manager, IT manager, or local network administrator, as they are not the owners of the assets being tested. It is critical you get authorization from the owners of the assets, such as the company owner, or from a member of upper-level management who has signing authority.
In addition, virtualization technology in the cloud has become a huge resource for companies to leverage, as it allows a company to get high availability and access to resources from anywhere. During pre-engagement activities and discussions, verify if there are any resources that are in the cloud, because you will need to get authorization from the cloud provider to perform a pentest on the cloud resources.
Contracts
Before starting the penetration test and typically before you start scoping out the project, you will receive a signed contract that is essentially hiring you for the service. These contracts are designed to protect the contractor from liability if something goes wrong with the penetration test, and protect the customer from sensitive data leakage on the part of the contractor.
The CompTIA PenTest+ certification exam refers to three main types of contracts:
- SOW: A statement of work (SOW) is a contract created by the penetration testing company that specifies the type of work its pentesters are providing, the timeline for performing the work, the cost of the work, the payment schedule, and any terms and conditions covering the work.
- MSA: A master service agreement (MSA) is a useful contract if you are performing repeat work for a company. The MSA acts as a standard boiler plate contract for the business relationship between the contractor and customer saving time when repeat work is needed from the contractor. With the MSA, you can define the terms of the work in the MSA and then refer to that from the SOW for each reoccurring engagement. Examples of terms in the MSA include payment terms, working conditions, remediation processes, and ownership of intellectual property.
- NDA: A non-disclosure agreement (NDA) is a common document outlining the importance of confidentiality in regard to the relationship of the two parties and the work performed. It identifies what information should be kept confidential and how confidential information should be handled. The NDA is created by the customer and given to the contractor to sign. The NDA is designed to protect the confidentiality of sensitive information that the contractor may come across while doing the penetration test.
Disclaimers
During the pre-engagement discussions and in the SOW, it is important to include two disclaimers that outline two important points about the penetration test.
First, you should have a disclaimer that states that the penetration test is a point-in-time assessment — meaning you have tested against known vulnerabilities and exploits as of the current date. As time goes on and new software and systems are installed on the network, your assessment would not have tested those new items.
Second, you should have a disclaimer that indicates that the comprehensiveness of the penetration test is based on the types of tests authorized by the customer and the known vulnerabilities at the time. For example, if the customer requests that no denial of service (DoS) attacks are performed (which is common), your penetration test would not have tested how the company stands up against a DoS attack. This disclaimer will help protect you if the customer is hit with a DoS attack after the penetration test is performed.
Scoping the Project
During the pre-engagement activities, it is important to have an initial meeting with the customer that allows you to discuss the scope of the project and get an understanding of what the customer’s goals are for the penetration test.
When preparing for the initial meeting with the customer, you should plan out scoping questions that will help you understand the magnitude of the project. Some common questions to ask when determining the scope of the pentest are:
- What is the goal of the penetration test? (Why is it being done?)
- Is the penetration test going to test internal systems, external systems, or both?
- What are the Internet Protocol (IP) ranges of the internal and external systems that are being tested?
- What are the internal and external domain names of the systems to be tested?
- Does the company own the systems using those IP addresses?
- Are there any systems hosted by third-party companies such as an ISP or a cloud provider?
- What applications and services will be tested?
- What types of tests are to be performed? For example, are you testing physical security and/or social engineering, and are DoS attacks allowed?
If performing a black box test, which is discussed in Chapter 1, the penetration tester is typically responsible for discovering target services, and some would say the target IP addresses. The important point here to remember is that you want the customer to give you the target IP addresses and domain names so that you can be sure you have proper authorization to perform testing on those systems. If it is up to the pentester to discover the IP addresses, especially external IP addresses, the tester runs the risk of performing the penetration test on an unauthorized IP address or system owned by someone else.
Depending on the type of testing being performed, there are a number of other questions you can ask during the scoping of the project. The Penetration Testing Execution Standard (PTES) website found at www.pentest-standard.org has an extensive list of questions you can ask. The following sections list example questions for each different type of test.
General questions
- What is the goal of the penetration test? (Why is it being done?)
- Is the pentest being performed for compliance reasons?
- What hours of the day can the penetration test be performed (business hours/non-business hours)?
- What are the internal and external target IP addresses?
- Are security controls in place such as firewalls and intrusion detection systems?
- If a system is compromised, what actions should be taken next (for example, no action, elevate privileges, and so on)?
Web application testing questions
- How many web applications/sites are being tested?
- How many of those require authentication?
- How many static pages are in those sites?
- How many dynamic pages are in those sites?
- Is the source code available for review?
- Is authentication testing to be performed?
Wireless network testing questions
- How many wireless networks are there?
- What wireless encryption protocol(s) are being used?
- What is the area covered by wireless?
- Should detection of rogue devices be performed?
- Should wireless attacks against clients be performed (or just focus on the access point)?
- How many wireless clients are there?
Physical security testing questions
- Is physical security testing part of the pentest?
- How many locations are there?
- Are the locations shared with other businesses? If so, what floors do you occupy?
- Are lock picks and bump keys allowed to bypass a locked door?
- Are video cameras being used? If so, does the customer own those devices?
Social engineering testing questions
- Is social engineer testing part of the pentest?
- Does the customer have email addresses for social engineering?
- Does the customer have phone numbers for social engineering?
Testing questions for IT staff
- Are there fragile systems that are easy to crash?
- What is the mean time to repair from a system outage?
- What are the business-critical servers and applications?
- Are backups tested regularly?
- Is there a disaster recovery procedure in place for devices and systems being tested?
- When was the last backup performed?
Identifying the Rules of Engagement
As part of the planning and scoping phase of the CompTIA penetration testing process, it is important to define the rules of engagement for the penetration test. The “rules of engagement” refer to any restrictions and details in regard to how the customer wants the penetration test performed. Following are some points covered by the rules of engagement:
- The timeline for the penetration test: Determine the start date and the end date of the penetration test based on a schedule for each task and phases being performed.
- When testing is to be performed: Define the hours of the day testing is permitted. This could be during work hours, non-work hours, or on weekends.
- What to test — locations, targets, services, and applications: Identify what resources or targets will be tested. This includes the office locations, target systems, target services and applications, and the accounts to be targeted.
- How the results should be reported: The details and results of the penetration tests, such as the vulnerabilities associated with each system, are highly sensitive. Define what method of communication is acceptable to communicate the pentest details and results. Communication should be encrypted, whether it is sent via email or on a disk.
- Who should contact the pentest team: Define who is allowed to communicate with the pentest team during the penetration test.
- How frequently updates should be communicated: Define who the pentest team is to go to with updates on the progress of the penetration test and how often updates should be communicated.
- Authorization to perform the pentest: Verify that you have signed authorization to perform the penetration test.
- Legal considerations with third parties: Verify whether any of the systems or services are hosted by a third party such as an ISP or cloud provider. If a third party is used to host services, verify that you have authorization from the third party to perform the pentest.
- Security controls that could shun the pentest: Verify whether the pentest team can expect to be blocked or shunned by security controls such as firewalls, intrusion prevention systems, and blacklisting on the network. These controls can limit the pentest and increase the time to perform the penetration test.
- Whether security controls should be tested: Discuss whether you should be testing the effectiveness of the security controls in place. For example, should you report on whether the company security team was able to detect and respond to information gathering, footprinting attempts, scanning and enumeration, and attacks on systems?
Target audience and reason for the pentest
During the pre-engagement activities, it is important to determine the target audience for the penetration test and the reason the pentest is being performed. Many companies state that the primary goal of the penetration test is to verify that their systems are secure by seeing how they hold up to real-world attacks. Another goal may be to see how the security team (known as the blue team) defends against the attacks, and to verify the effectiveness of the security controls in place (such as intrusion detection systems and firewalls). As a secondary goal, the company may need to be compliant to regulations stating that the company must have a penetration test performed regularly.
It is important to know why the pentest is being performed, but also who it is being performed for. The pentest report will need to be written to satisfy the goals of the pentest and be written to include information for the intended audience. For example, upper-level management may just want an executive summary that states how the company held up to the pentest, while the network administrators and security team may want more details on the vulnerabilities that still exist within their systems.
Communication escalation path
In addition to determining the target audience for the penetration test and the reason the pentest is being performed, it is also important to determine who the penetration testing team is to communicate with during the pentest. This includes determining when updates are delivered to the contact person and also who to contact when there is an emergency (such as a system or network crashes due to the pentest).
Following are some common questions you can ask during the pre-engagement phase to determine communication paths:
- How frequently should updates on the progress of the penetration test be communicated?
- Who is the main point of contact in the company for communication updates?
- Are the penetration testers allowed to talk to network administrators and the security team, or is this a silent pentest?
- Who should be the point of contact in case of emergency?
As a pentester you also want to be sure you have collected proper contact information in case there is an emergency, such as a system goes down or an entire network segment goes down. Following is the key information you should collect about the customer in case of emergency:
- Name of the company contact
- Job title and responsibility of the contact
- Does the contact have authorization to discuss details of the pentest activities?
- Office phone number, mobile phone number, and home phone number of the contact
Resources and requirements
When defining the rules of engagement for the pentest, you also want to ensure that you discuss key points surrounding the company’s different resources such as the targets to focus on and who to communicate the results with. You learn earlier in this chapter about a few questions you should ask in relation to resources, but let’s discuss a bit more about resources and requirements.
Confidentiality of findings
A key point to discuss is the confidentiality of the updates given and the results of the penetration test. Determine with the customer who are the authorized persons to receive updates on the progress of the penetration test, who to go to in case of emergency, and who the penetration results (the report) should go to. Be clear that you will be unable to communicate details of the penetration test to anyone not on this authorized list.
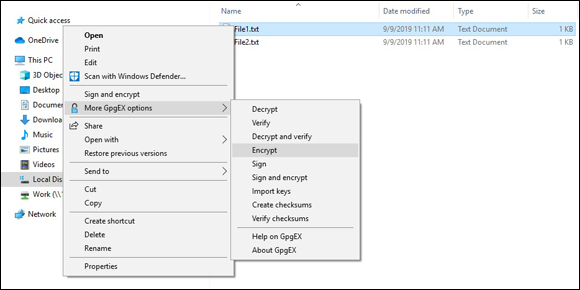
FIGURE 2-1: Encrypting a file in Windows Explorer with Gpg4win.
Known versus unknown
During the pre-engagement phase, discuss the targets for the penetration test and how to handle the discovery of an unknown device on the network. An unknown device is a device not on the target list, or an unauthorized access point connected to the network, VPN server, or router. If any non-targeted device that makes the client network and security vulnerable is discovered, you should stop the penetration test to discuss with authorized persons on how they want to proceed.
Support for the pentester
When planning for the penetration test, be sure to request all potential resources available to help you determine the number of targets and to learn a bit more detail about the targets. The first important resource to request is documentation: ask for network diagrams identifying servers, routers, switches, and network segments to help you better prepare for the penetration test.
You can request a number of other support resources from the customer:
- WSDL/WADL files: You can obtain detailed information such as the methods or functions and their parameter data types supported by a web service by looking at the Web Services Definition Language (WSDL) or the Web Application Description Language (WADL) files. These are XML-based files that describe the web service.
- SOAP project file: You can use the SOAP project file to view details about the functionality of a web service.
- SDK documentation: You can view the documentation for a software development kit (SDK) to get a better understanding of the functionality provided by the SDK and types of calls that can be made by applications using it.
- Swagger document: A swagger document is a document that describes the functionality of an application programming interface (API). Swagger is a technology that helps automate the creation of the API documentation. This documentation could be quite useful to the pentester to help him or her understand the functionality offered by an API.
- XSD: An XML schema document (XSD) is used to describe the structure of an XML document and is a great tool to help understand the data stored in XML.
- Sample application requests: You could view a sample application request message sent to an application to obtain detailed information about the structure of the request.
- Architectural diagrams: A key piece of documentation that can help with application testing is an architectural diagram of the application and all of its components. For example, a web application may communicate with some middleware software, which then communicates with a database. Having a diagram that shows the communication channels for all components is a great tool to help you understand the architecture of an application.
Budget
A big part of the pre-engagement activities is determining the cost of the penetration test. Once you have an idea of the size of the organization and the target resources for the penetration test, you can then work on calculating the cost of the pentest based on the man-hours you expect it to take and the cost per hour for the consultants. As the Penetration Testing Execution Standard (PTES) recommends, you should add 20 percent additional time to the estimated man-hours to accommodate any incidents that may slow down the penetration test. This will help the customer better understand the budget for the penetration test, and you can always lower the cost if you like once the job is complete. Customers are usually okay with the final cost ending up lower than what was quoted, but not happy if the cost goes up.
You also need to determine how payments are going to be scheduled. For smaller projects, you could do a net 30 days after the final report has been delivered, or for medium-sized and larger projects, you could go with a regular ongoing payment schedule that has the customer paying quarterly throughout the duration of the project. For larger jobs, some consultants ask for half of the payment upfront and then additional payments later on.
Impact analysis and remediation timelines
As discussed in “Disclaimers” earlier in this chapter, during the pre-engagement phase, it is critical that you communicate to the customer the risk or impact a penetration test can have on the company’s systems and the network. It is important that you try not to crash systems, and that you test all tools and techniques before using them on your customer’s systems, but in the end, the tools you are using are hacking tools, and they may have unexpected results in different environments. You must state that there is a risk to crashing a system or network in your contract, but stress during your discussions with the customer that you have tested the tools and will not intentionally try to crash systems.
The penetration test report will include remediation steps that the customer needs to take to better secure their assets. It is critical that after the customer implements these fixes that the assets are retested to make sure the penetration test is not successful. Make sure you accommodate for this retesting in your budget estimate. It is also important to make sure you give a deadline on when the remediation steps need to be completed — and how long after report delivery retesting is covered in the price.
Defining Targets for the Pentest
During the planning and scoping phase, you need to define the targets for the penetration test. The contract agreement should have a section on target selection that specifies the systems that are the targets of the pentest. Let’s take a look at common targets for a penetration test.
Internal and external targets
When performing a penetration test, you will be working with internal targets, external targets, or both. An internal target is a system that exists inside the corporate network and is not accessible from the Internet because it is behind firewalls. An external target is a system that is reachable from the Internet and resides in the demilitarized zone (DMZ) network or in the cloud.
You will need to determine what internal systems (targets) should be tested and obtain the internal IP addresses or domain names for these assets. For example, you’ll need to obtain the internal addresses of the intranet servers, mail servers, file servers, or network-attached storage (NAS) devices, to name just a few. When identifying the internal assets and IP ranges, it is important to identify if those assets are on-site or off-site. On-site resources are systems and devices that exist on the network at the location being assessed, while off-site resources could be systems in the cloud, at an alternate site, or maybe resources that are mobile like a network on a boat or other vehicle. When conducting a pentest of the internal network, you may have to visit different locations to perform the penetration test, which should be reflected in the budget.
You will also want to be sure to determine the external IP addresses and domain names of systems to pentest. This is critical to verify as you do not want to try to exploit an external address not owned by the customer.
First-party versus third-party hosted
As I mention earlier in this chapter, you need to verify where the targets are being hosted, whether by the customer (first party) or by an outside company (third party). If systems are hosted by a third-party company such as an ISP or cloud provider, you need to get authorization from the third party to perform the pentest on those assets.
Other targets
When performing a penetration test, in addition to identifying the IP addresses of the hosts you are going to perform the penetration test on, you should also identify the following resources:
- Applications: Determine what applications and services are in scope of the penetration test. Some common applications and services may be the intranet site, Internet site, email services, remote desktop services, file transfer protocol (FTP) service, internal websites, and external websites.
- Physical security controls: Determine if testing the physical security controls is in scope of the pentest. This includes social engineering attacks on security guards, exploiting surveillance equipment, and testing locking systems with a lock pick or bump key.
- SSIDs: Determine if there are wireless networks that you are authorized to exploit. Make sure you find out what wireless networks, or SSIDs, are owned by the company that are in scope of the pentest.
- Users: Determine what user accounts are in scope for password cracking. Be sure to determine if you are allowed to attempt to compromise administrative accounts as well.
Target considerations
When working on exploiting target systems, applications, and services, you must make different considerations when conducting a white box test versus a black box test. With a white box test, the company will grant the pentester access to the system by allowing the pentester to pass through any security controls, but with a black box test, the pentester will need to figure out how to bypass the security controls as part of the test.
Here are some considerations to keep in mind when performing the pentest on the identified targets:
- Whitelisted versus blacklisted: As a pentester you can seek to have your system whitelisted by security controls so that the system is not blocked when performing the assessment. A blacklisted system, which is a system that is blocked by a security control, can slow down the assessment dramatically.
- Security exceptions: You can add the pentester’s IP address or account to security exceptions within security controls so that the pentester is not blocked. For example, on a firewall you can add the pentester’s IP address to the firewall exception list so that the pentester’s traffic can pass through the firewall.
- IPS/WAF whitelist: You can add the pentester’s IP address to the whitelist on the intrusion prevention system (IPS) and the web application firewall (WAF) so that it is not blocked and the pentester can test the web application.
- NAC: The customer may have network access control (NAC) features implemented that only allow devices in a secure state to connect to the network. As a pentester, this could affect your capabilities to connect to the network and perform the pentest. You may have to be placed on an exception list so that you can access the network from your pentest system.
- Certificate pinning: Certificate pinning refers to the process of associating a host with the expected server it will receive certificates from. If the certificate comes from a different system, the communication session will not occur. You may need to disable certificate pinning on the network to allow communication.
- Company’s policies: You should review the company security policy to determine if there are any policies in place that would put limits on the actions the penetration testers can take.
- Technical constraints: Be aware of any technical constraints that may limit your capabilities to perform the penetration test. For example, there may be firewalls blocking your scans during discovery of targets or there may be network segments controlling communication.
- Environmental differences: When performing the penetration test, it is important to be aware of any differences in the environment, as any differences could change how the pentest tools respond. Be aware of export restrictions when it comes to crossing borders with any encrypted content and any other local and national government restrictions that may be in place with regard to encryption and penetration testing tools. When performing a pentest on large global companies, know that the laws are different in these different companies with regard to using pentest tools. Also, review any corporate policies so that you are aware of the pentesting rules.
- Special scoping considerations: There may be other special scoping considerations that may arise during the pre-engagement phase, such as premerger testing and supply chain testing considerations. Premerger testing refers to assessing the security of a business the company is going to acquire. Supply chain testing refers to assessing the security of a supplying company, or multiple supplying companies, before the customer does business with those companies.
Verifying Acceptance to Risk
Earlier in this chapter, I discuss the importance of including a disclaimer in the SOW, and I want to stress again that as the penetration tester, you need to make the risk of performing a penetration test clear to the customer (in discussion and in the contract). Make sure the customer accepts those risks before starting the penetration test, as risk acceptance is critical to protecting yourself from legal action.
Some key points to communicate with the customer in relation to the acceptance of risk of the penetration test are:
- Tools are used to try to compromise the security of the company’s systems.
- Although you have tested the tools and are using tools that have not crashed your test systems, the tools could have unpredictable results in different environments due to different software and configurations that you may not have had in your test environment.
- Stress that although you will not try to crash systems, the risk is there that systems may crash.
- Verify that the customer has recent backups of the systems being assessed.
It is also important to verify the customer’s tolerance to the impact the assessment will have on the company’s systems. Here are some questions you can ask to verify the customer’s acceptance of the impact of the assessment:
- Is the customer aware and okay with the fact that you are hacking into the company’s systems when performing the penetration test?
- Does the customer accept that the system may fail if you run exploits against the system? If the customer is not willing to accept the crashing of a system, you may want to do a vulnerability assessment instead of a penetration test. The vulnerability assessment will review the configuration of the systems and run a vulnerability scan to determine how exposed the system is, but not actually try to hack the system.
- If a system fails due to the penetration test, how long will it take to recover a failed system?
- How long can the business survive without the asset or system in question? How much downtime is the customer willing to accept if it does occur?
Scheduling the Pentest and Managing Scope Creep
Scheduling and scope creep are two important points to remember for the CompTIA PenTest+ certification exam as well as when you conduct a penetration test in the real world.
Scheduling
When discussing the details of the pentest with the customer during the pre-engagement phase, be sure to determine when the penetration test is to occur. Generally, pentests are scheduled to occur during any of the following timeframes:
- During work hours (for example, 8 a.m. to 5 p.m.)
- After work hours (for example, 6 p.m. to 6 a.m.)
- On weekends (for example, 8 a.m. to 12 a.m.)
When preparing the budget, be sure to have a schedule set up for how long it will take to perform the penetration test. Table 2-1 illustrates a sample schedule, but know that the schedule will vary depending on the size of the organization being assessed and the number of resources you have available to perform the penetration test.
TABLE 2-1 A Sample Pentest Schedule
Activity |
Activity Name |
Duration |
|---|---|---|
|
1 |
Initial preparation |
3 |
|
2 |
Planning and scoping |
3 |
|
3 |
Kick-off meeting |
1 |
|
4 |
Initial assessment of environment |
3 |
|
5 |
Information gathering |
5 |
|
6 |
Vulnerability assessment |
5 |
|
7 |
Exploitation of systems |
5 |
|
8 |
Physical security assessment |
3 |
|
9 |
Wireless security assessment |
3 |
|
10 |
Post-exploitation |
3 |
|
11 |
Clean-up |
3 |
|
12 |
Report preparation |
5 |
|
13 |
Report delivery and project closing |
1 |
Scope creep
An important discussion to have during the planning and scoping phase of the penetration test is how to handle scope creep. Scope creep occurs when the size of the project — in this case the penetration test — continues to change or grow as the project continues. As the consulting pentester, scope creep is a nightmare, as you have given a quote to the customer on the cost to perform the penetration test based on how long you estimate the pentest will take. The length of time is dependent on the number of targets defined for the project, and if that changes while the penetration test is occurring, the cost will go up! Increased costs typically do not sit well with the customer, so be very clear at the start that the cost is for the targets that have been defined within the scope of the project and that any newly discovered targets that arise while the penetration test is occurring will be an additional cost. Make sure the pentest team knows who to contact when a new target has been discovered during the pentest that was not specified in the scope of the project so that you can determine how to continue.
Conducting Compliance-based Assessments
If the organization for which you are performing a penetration test is conducting a pentest to be in compliance with industry regulations, you may need to meet strict requirements when performing the assessment. It is important as a penetration tester to become familiar with the requirements of a compliance-based assessment. Know that the requirements are different in every industry, as they depend on the laws or regulations that govern each industry. Following are examples of industry-specific laws or regulations an organization must follow based on the industry the organization operates in:
- Health Insurance Portability and Accountability Act (HIPAA), which controls the handling of health records.
- Family Educational Rights and Privacy Act (FERPA), which allows parents access to educational records of their child.
- Payment Card Industry Data Security Standard (PCI DSS), which secures debit and credit card information.
Following are some limitations and caveats to keep in mind with regard to compliance-based assessments:
- Rules to complete the assessment: Each regulation or standard has strict rules on how the penetration test is to be performed and what to look for in the assessment. For example, the PCI DSS includes strict requirements on the use of firewalls to restrict communication with data-holder equipment, and encryption requirements for transferring credit card data across public networks.
- Password policies: To be compliant, an organization may have to follow strict requirements on passwords and password policies. For example, you may need to assess the company’s password policy and ensure that the company employees use strong passwords, change passwords frequently, and cannot use a password they used previously.
- Data isolation: Due to laws or regulations you may need to ensure that certain types of data are separated from other types of data. For example, with PCI DSS, a company must ensure that credit and debit card data is isolated from the rest of the company data. As another example, in a bring-your-own-device (BYOD) environment, you may need to ensure that mobile devices partition personal data from business data so that business data can be remotely wiped if needed.
- Key management: You may need to assess the use and storage of encryption keys as well as assess the company’s backup policies or the archival of encryption keys to allow recovery of sensitive data.
- Limitations: You may need to assess for limitations placed on resources such as systems, devices, and data. For example, there may be strict limitations on certain types of systems not being accessible from the Internet.
- Limited network access: You may need to ensure that the network is segmented to allow control of a specific type of system that can only access a particular network segment. For example, with PCI DSS, the credit card processing system must be on a separate network segment than regular company systems.
- Limited storage access: You may need to assess that the company is controlling access to data and that one specified person has access to sensitive data. Again, looking at PCI DSS, the pentester would validate that access to card data is limited and protected.
It is important to stress that there are clearly defined objectives based on regulations. For example, if the organization is processing credit cards, the organization must be compliant with PCI DSS by following the objectives and requirements set by PCI DSS. (You can view the Requirements and Security Assessment Procedures document at https://www.pcisecuritystandards.org/document_library.)
Reviewing Key Concepts
This chapter highlights a number of important points to remember when planning and scoping the penetration test. Following is a quick review of some of the key points from this chapter:
- Ensure you receive written authorization to perform the penetration test by a signing authority for the company.
- Know the different types of contracts you may encounter, such as a SOW, NDA, and MSA.
- Ensure you include a disclaimer in the contract with the customer that states the risk of performing a penetration test. It is possible that the tools used could crash a system or network and cause downtime with the company asset.
- Ensure you have a clear scope for the penetration test. Include the target IP addresses (both internal and external), a list of the wired and wireless networks and applications to test, and determine whether social engineering is to be performed and whether you are performing an assessment of physical security.
- Clearly define the communication path to follow when performing the assessment. Who is the pentest team allowed to communicate the details of the pentest with? Also, be clear that additional assets discovered during the assessment may increase the time and cost of the assessment if the newly discovered asset is to be evaluated as well.
- If the organization is performing the assessment for compliance reasons, read up on the requirements of the compliance-based assessment to ensure you follow all goals and requirements.
Prep Test
1. What type of contract outlines the requirements of confidentiality between the two parties and the work being performed?
(A) SOW
(B) NDA
(C) MSA
(D) SLA
2. Bob is performing a penetration test for Company XYZ. During the planning and scoping phase, the company identified two web servers as targets for the penetration test. While scanning the network, Bob identified a third web server. When discussing this new finding with the customer, the customer states that the third server runs critical web applications and needs to be assessed as well. What is this an example of?
(A) Statement of work
(B) Master service agreement
(C) Disclaimer
(D) Scope creep
3. You are drafting the agreement for the penetration test and working on the disclaimer section. What two key points should be covered by the disclaimer? (Choose two.)
(A) Compliance-based
(B) Point-in-time
(C) WSDL document
(D) Comprehensiveness
4. What type of contract is a description of the type of job being performed, the timeline, and the cost of the job?
(A) SOW
(B) NDA
(C) MSA
(D) SLA
5. You have been hired to do the pentest for Company XYZ. You acquired proper written authorization, performed the planning and scoping phase, and are ready to start discovery. You connect your laptop to the customer network and are unable to obtain an IP address from the company DHCP server. Which of the following could be the problem?
(A) MSA
(B) SSID
(C) SOW
(D) NAC
6. You are performing the penetration test for a company and have completed the planning and scoping phase. You wish to do the pentest on the wireless networks. What scoping element would you need?
(A) MSA
(B) NDA
(C) SSID
(D) NAC
7. What type of contract is used to define the terms of the repeat work performed?
(A) MSA
(B) NDA
(C) SOW
(D) NAC
8. You drafted the agreement to perform the penetration test, and you are now looking to have the agreement signed by the customer. Who should sign the agreement on behalf of the customer?
(A) Office manager
(B) IT manager
(C) Security manager
(D) Signing authority
9. You are working on the planning and scoping of the penetration test, and you are concerned that the consultants performing the pentest will be blocked by security controls on the network. What security feature would you look to leverage to allow the pentesters’ systems to communicate on the network?
(A) Blacklisting
(B) Whitelisting
(C) NAC
(D) Certificate pinning
10. You are performing a penetration test for a company that has requested the pentest because it is processing credit card payments from customers. What type of assessment is being performed?
(A) Goal-based assessment
(B) Security-based assessment
(C) Compliance-based assessment
(D) Credit card–based assessment
Answers
- B. A non-disclosure agreement (NDA) is designed to outline the requirements of confidentiality between two parties and the work performed. See “Understanding Key Legal Concepts.”
- D. Scope creep is when the scope of the project is modified as the project is being performed. Review “Scope creep.”
- B, D. The disclaimer should cover the fact that the pentest is a point-in-time assessment and stress that the comprehensiveness of the assessment is based on the scope. Check out “Understanding Key Legal Concepts.”
- A. The statement of work (SOW) is a description of the work being performed, includes the timeline for the project, and contains a breakdown of the cost for the project. Peruse “Understanding Key Legal Concepts.”
- D. Network access control (NAC) is a suite of technologies that limits connections to the network based on health criteria. Take a look at “Defining Targets for the PenTest.”
- C. The SSIDs of the wireless network should be identified during the planning and scoping phase so that you can be sure you have authorization to perform the assessment on the correct wireless networks. Peek at “Defining Targets for the PenTest.”
- A. The master service agreement (MSA) is used when repeat engagements occur. It contains the terms of the work being performed and is referenced from the statement of work (SOW). Look over “Understanding Key Legal Concepts.”
- D. The signing authority for the company, such as the business owner, should sign the agreement as proof of authorization. Study “Understanding Key Legal Concepts.”
- B. Whitelisting is a method to allow systems to access network resources and bypass the security controls. Whitelisted systems and applications are considered authorized systems and applications, as opposed to blacklisted systems, which are non-authorized components. Peek at “Defining Targets for the PenTest.”
- C. A compliance-based assessment is an assessment that is driven by the need to be compliant with laws and regulations that are governing an organization. See “Conducting Compliance-based Assessments.”
 The planning and scoping phase of the penetration testing process is also known as the pre-engagement phase. In this phase you want to be sure to get authorization that allows the organization’s systems to be tested and compromised.
The planning and scoping phase of the penetration testing process is also known as the pre-engagement phase. In this phase you want to be sure to get authorization that allows the organization’s systems to be tested and compromised. If some of the company resources are being hosted by a third-party company, you must get authorization from that third party as well. For example, if the company’s website is hosted on its ISP’s web server, or the ISP hosts the domain name system (DNS) service for the company, it is important to get authorization from the ISP if you are going to perform penetration testing on those resources. If you do not get authorization to perform the penetration test on those systems, you must ensure they are not in the scope of the penetration test.
If some of the company resources are being hosted by a third-party company, you must get authorization from that third party as well. For example, if the company’s website is hosted on its ISP’s web server, or the ISP hosts the domain name system (DNS) service for the company, it is important to get authorization from the ISP if you are going to perform penetration testing on those resources. If you do not get authorization to perform the penetration test on those systems, you must ensure they are not in the scope of the penetration test. For the PenTest+ certification exam, remember that you must obtain a signature from a proper signing authority to perform the penetration test. Also remember to check if any resources are hosted by third parties such as an ISP or cloud provider because you will need third-party provider authorization to test those resources.
For the PenTest+ certification exam, remember that you must obtain a signature from a proper signing authority to perform the penetration test. Also remember to check if any resources are hosted by third parties such as an ISP or cloud provider because you will need third-party provider authorization to test those resources. Your agreement should also make it clear that a penetration test uses hacking tools that a hacker would use, and although you have tested these tools, it is possible that they could have unpredictable results due to the additional software installed on the systems or the configuration of the systems. Unpredictable results in this case is referring to the fact that it is possible that the target systems could crash and be unavailable. For example, I have heard cases where performing a vulnerability scan of the network caused the print servers to drop off the network. This is not something that happens all the time, but the point is that different products from different vendors respond differently to the scanning and attack tools. One way to help prevent disruption on the network is to perform the penetration test on virtual machines within a test environment that are copies of the production systems.
Your agreement should also make it clear that a penetration test uses hacking tools that a hacker would use, and although you have tested these tools, it is possible that they could have unpredictable results due to the additional software installed on the systems or the configuration of the systems. Unpredictable results in this case is referring to the fact that it is possible that the target systems could crash and be unavailable. For example, I have heard cases where performing a vulnerability scan of the network caused the print servers to drop off the network. This is not something that happens all the time, but the point is that different products from different vendors respond differently to the scanning and attack tools. One way to help prevent disruption on the network is to perform the penetration test on virtual machines within a test environment that are copies of the production systems.