Microsoft provides three automated tools for locking down Windows and IIS:
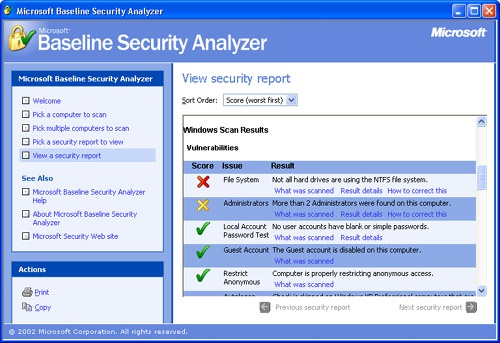
Microsoft Baseline Security Analyzer (MBSA). This tool detects a large number of common security issues, such as blank passwords and missing security patches. MBSA alerts you to the cause of the issue and recommends steps for fixing them. It’s available as a free download from http://www.microsoft.com/technet/security/tools/Tools/MBSAhome.asp. MBSA requires Windows 2000 or Windows XP, with Internet Explorer 5.01 or later. The tool is shown in Figure 11-1.
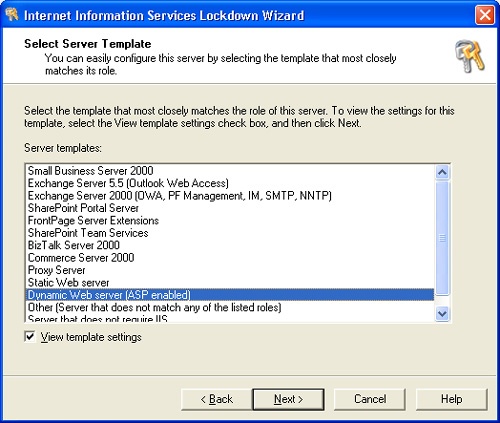
IIS Lockdown tool. This application, shown in Figure 11-2, detects a large number of IIS security holes. Unlike MBSA, the IIS Lockdown tool makes the configuration changes for you. The utility also has an undo facility, so it can be run at a future time to restore the previous configuration.
The IIS Lockdown tool is available as a free download from http://www.microsoft.com/technet/security/tools/tools/locktool.asp. It requires Windows NT 4.0, Windows 2000, or Windows XP and IIS 4.0 or later.
URLScan. This application runs in conjunction with IIS and will filter requests to IIS that are
Extremely long
Requesting an unusual action
Encoded by using an alternate character set, or that include character sequences rarely seen in legitimate requests.
It’s available as a free download from http://support.microsoft.com/default.aspx?scid=KB;en-us;307608. It can also be installed from the IIS Lockdown tool.
MBSA should be run regularly because it detects missing patches and configuration issues that might change from time to time. The IIS Lockdown tool should be run once, after running MBSA, and then again any time you need to reconfigure IIS. After running MBSA and the IIS Lockdown tool, URLScan should be installed and allowed to run continuously in the background.
The following sections explain the configurations for locking down Windows, IIS, and .NET and which configurations MBSA and the IIS Lockdown tool will detect.