Developing an Authentication Provider is a fairly complex task with many concepts that need to be understood. Here, we will introduce the concepts regarding the composing parts of a provider and different kinds of authentication.
Authentication is completely delegated to entities called Authentication Providers, which are a set of classes and configuration files that incorporate an MBean and a LoginModule interface. Every time you request a protected resource, every configured Provider is requested to add the principals extracted from the credentials provided.
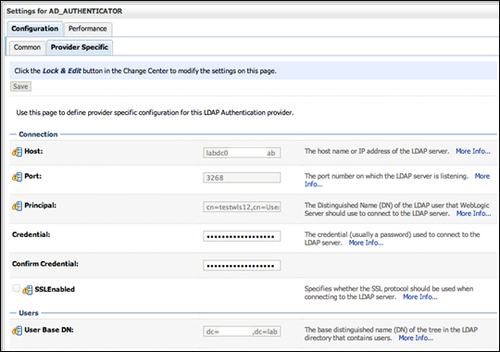
This mechanism is very similar to the one configurable on the client with only JAAS (and jaas.config); the main difference is that it's done with the administration console. This console allows us to configure parameters visually, through the automatically-generated JSP page, without touching any XML file, as shown in the following screenshot:
Under WebLogic Security Framework, everything is wrapped by MBeans. The standard JAAS security infrastructure is created and invoked using an MBean, which can be configured using the standard console. This makes sense because the console and every utility that runs under the WebLogic ecosystem has to be consistent and there are a lot of technologies around Java that have to be integrated.
So, if you need to implement your own LoginModule interface, remember that you need to "decorate" it with the correct MBean, which in turn is automatically generated for you by the WebLogic MBeanMaker tool.
Every Provider has only one chance to contribute to the authentication process: it receives Credentials and eventually adds Principals to the current Subject. This scenario of security has very limited potentialities if interaction with the user agent is required. For example, for negotiating an authentication mechanism, redirecting to a remote login site, or even implementing a challenge/response handshake, this is a suitable task for servlet filters, but if they are configured for a protected resource they are not called until you are authenticated.
WebLogic Security Framework gives developers a chance to return an array of filters that are executed on behalf of the standard Authentication mechanism, but not under the application component's security context.
