Chapter 14. SSH
SSH, the Secure SHell, is an essential tool for many developers and administrators. SSH provides a way to establish encrypted, authenticated connections. The most common use of an SSH connection is to get a remote shell, but it’s possible to do many other things through SSH as well, including transferring files and tunneling other connections.
The twisted.conch package adds SSH support to Twisted. This
chapter shows how you can use the modules in twisted.conch to
build SSH servers and clients.
SSH Servers
The command line is an incredibly efficient interface for certain tasks. System administrators love the ability to manage applications by typing commands without having to click through a graphical user interface. An SSH shell is even better, as it’s accessible from anywhere on the Internet.
You can use twisted.conch to create an SSH server that
provides access to a custom shell with commands you define. This shell will even support some
extra features, like command history, so that you can scroll through the commands you’ve
already typed.
A Basic SSH Server
To write an SSH server, implement a subclass of twisted.conch.recvline.HistoricRecvLine that implements your shell
protocol. HistoricRecvLine is similar to twisted.protocols.basic.LineReceiver, but with higher-level
features for controlling the terminal.
To make your shell available through SSH, you need to implement a few different classes that
twisted.conch needs to build an SSH server. First, you
need the twisted.cred authentication classes: a portal,
credentials checkers, and a realm that returns avatars. Use twisted.conch.avatar.ConchUser as the base class for your
avatar. Your avatar class should also implement twisted.conch.interfaces.ISession, which includes an openShell method in which you create a Protocol to manage the user’s interactive session. Finally, create
a twisted.conch.ssh.factory.SSHFactory object and set its
portal attribute to an instance of your portal.
Example 14-1 demonstrates a custom SSH server that authenticates users by their username and password. It gives each user a shell that provides several commands.
To test this example, you’ll need to generate a public key with an empty passphrase. The OpenSSH SSH implementation that comes with most Linux distributions and Mac OS X includes a command-line utility called ssh-keygen that you can use to generate a new private/public key pair:
$ ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/home/jesstess/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/jesstess/.ssh/id_rsa.
Your public key has been saved in /home/jesstess/.ssh/id_rsa.pub.
The key fingerprint is:
6b:13:3a:6e:c3:76:50:c7:39:c2:e0:8b:06:68:b4:11 jesstess@kid-charlemagne Tip
Windows users that have installed Git Bash can also use ssh-keygen. You can also generate keys with PuTTYgen, which is distributed along with the popular free PuTTY SSH client.
fromtwisted.conchimportavatar,recvlinefromtwisted.conch.interfacesimportIConchUser,ISessionfromtwisted.conch.sshimportfactory,keys,sessionfromtwisted.conch.insultsimportinsultsfromtwisted.credimportportal,checkersfromtwisted.internetimportreactorfromzope.interfaceimportimplementsclassSSHDemoProtocol(recvline.HistoricRecvLine):def__init__(self,user):self.user=userdefconnectionMade(self):recvline.HistoricRecvLine.connectionMade(self)self.terminal.write("Welcome to my test SSH server.")self.terminal.nextLine()self.do_help()self.showPrompt()defshowPrompt(self):self.terminal.write("$ ")defgetCommandFunc(self,cmd):returngetattr(self,'do_'+cmd,None)deflineReceived(self,line):line=line.strip()ifline:cmdAndArgs=line.split()cmd=cmdAndArgs[0]args=cmdAndArgs[1:]func=self.getCommandFunc(cmd)iffunc:try:func(*args)exceptException,e:self.terminal.write("Error:%s"%e)self.terminal.nextLine()else:self.terminal.write("No such command.")self.terminal.nextLine()self.showPrompt()defdo_help(self):publicMethods=filter(lambdafuncname:funcname.startswith('do_'),dir(self))commands=[cmd.replace('do_','',1)forcmdinpublicMethods]self.terminal.write("Commands: "+" ".join(commands))self.terminal.nextLine()defdo_echo(self,*args):self.terminal.write(" ".join(args))self.terminal.nextLine()defdo_whoami(self):self.terminal.write(self.user.username)self.terminal.nextLine()defdo_quit(self):self.terminal.write("Thanks for playing!")self.terminal.nextLine()self.terminal.loseConnection()defdo_clear(self):self.terminal.reset()classSSHDemoAvatar(avatar.ConchUser):implements(ISession)def__init__(self,username):avatar.ConchUser.__init__(self)self.username=usernameself.channelLookup.update({'session':session.SSHSession})defopenShell(self,protocol):serverProtocol=insults.ServerProtocol(SSHDemoProtocol,self)serverProtocol.makeConnection(protocol)protocol.makeConnection(session.wrapProtocol(serverProtocol))defgetPty(self,terminal,windowSize,attrs):returnNonedefexecCommand(self,protocol,cmd):raiseNotImplementedError()defclosed(self):passclassSSHDemoRealm(object):implements(portal.IRealm)defrequestAvatar(self,avatarId,mind,*interfaces):ifIConchUserininterfaces:returninterfaces[0],SSHDemoAvatar(avatarId),lambda:Noneelse:raiseNotImplementedError("No supported interfaces found.")defgetRSAKeys():withopen('id_rsa')asprivateBlobFile:privateBlob=privateBlobFile.read()privateKey=keys.Key.fromString(data=privateBlob)withopen('id_rsa.pub')aspublicBlobFile:publicBlob=publicBlobFile.read()publicKey=keys.Key.fromString(data=publicBlob)returnpublicKey,privateKeyif__name__=="__main__":sshFactory=factory.SSHFactory()sshFactory.portal=portal.Portal(SSHDemoRealm())users={'admin':'aaa','guest':'bbb'}sshFactory.portal.registerChecker(checkers.InMemoryUsernamePasswordDatabaseDontUse(**users))pubKey,privKey=getRSAKeys()sshFactory.publicKeys={'ssh-rsa':pubKey}sshFactory.privateKeys={'ssh-rsa':privKey}reactor.listenTCP(2222,sshFactory)reactor.run()
sshserver.py will run an SSH server on port 2222. Connect to this server with an SSH client using the username admin and password aaa, and try typing some commands:
$ssh admin@localhost -p 2222admin@localhost's password:aaa>>> Welcome to my test SSH server. Commands: clear echo help quit whoami $whoamiadmin $echo hello SSH world!hello SSH world! $quitConnection to localhost closed.
Tip
If you’ve already been using an SSH server on your local machine, you might get an error when you try to connect to the server in this example. You’ll get a message saying something like “Remote host identification has changed” or “Host key verification failed,” and your SSH client will refuse to connect.
The reason you get this error message is that your SSH client is remembering the public key used by your regular localhost SSH server. The server in Example 14-1 has its own key, and when the client sees that the keys are different, it gets suspicious that this new server may be an impostor pretending to be your regular localhost SSH server. To fix this problem, edit your ~/.ssh/known_hosts file (or wherever your SSH client keeps its list of recognized servers) and remove the localhost entry.
The SSHDemoProtocol class in Example 14-1 inherits from twisted.conch.recvline.HistoricRecvline. HistoricRecvLine is a protocol with built-in features for building command-line
shells. It gives your shell features that most people take for granted in a modern shell,
including backspacing, the ability to use the arrow keys to move the cursor forwards and
backwards on the current line, and a command history that can be accessed using the up and
down arrows key. twisted.conch.recvline also provides a
plain RecvLine class that works the same way, but without
the command history.
The lineReceived method in HistoricRecvLine is called whenever a user enters a line. Example 14-1 shows how you might override this method to parse and
execute commands. There are a couple of differences between HistoricRecvLine and a regular Protocol,
which come from the fact that with HistoricRecvLine
you’re actually manipulating the current contents of a user’s terminal window, rather than
just printing out text. To print a line of output, use self.terminal.write; to go to the next line, use self.nextLine.
The twisted.conch.avatar.ConchUser class represents
the actions available to an authenticated SSH user. By default, ConchUser doesn’t allow the client to do anything. To make it possible for the
user to get a shell, make the user’s avatar implement twisted.conch.interfaces.ISession. The SSHDemoAvatar class in Example 14-1 doesn’t
actually implement all of ISession; it only implements
enough for the user to get a shell.
The openShell method is called with a
twisted.conch.ssh.session.SSHSessionProcessProtocol object that
represents the encrypted client’s end of the encrypted channel. You have to perform a few
steps to connect the client’s protocol to your shell protocol so they can communicate with
each other:
Wrap your protocol class in a
twisted.conch.insults.insults.ServerProtocolobject. You can pass extra arguments toinsults.ServerProtocol, and it will use them to initialize your protocol object.This sets up your protocol to use a virtual terminal.
Use
makeConnectionto connect the two protocols to each other.The client’s protocol actually expects
makeConnectionto be called with an object implementing the lower-leveltwisted.internet.interfaces.ITransportinterface, not aProtocol; thetwisted.conch.session.wrapProtocolfunction wraps aProtocolin a minimalITransportinterface.
Tip
The library traditionally used for manipulating a Unix terminal is called curses. The Twisted developers, never willing to pass up the chance to use a pun in a module name, therefore chose the name insults for this library of classes for terminal programming.
To make a realm for your SSH server, create a class that has a requestAvatar method. The SSH server will call requestAvatar with the username as avatarId
and twisted.conch.interfaces.IAvatar as one of the
interfaces. Return your subclass of twisted.conch.avatar.ConchUser.
To run the SSH server, create a twisted.conch.ssh.factory.SSHFactory object. Set its portal attribute to a portal using your realm, and register a credentials
checker that can handle twisted.cred.credentials.IUsernamePassword credentials. Set the SSHFactory’s publicKeys
attribute to a dictionary that matches encryption algorithms to keys.
Once the SSHFactory has the keys, it’s ready to go.
Call reactor.listenTCP to have it start listening on a
port, and you’ve got an SSH server.
Using Public Keys for Authentication
The SSH server in Example 14-1 used usernames and passwords for authentication. But heavy SSH users will tell you that one of the nicest features of SSH is its support for key-based authentication. With key-based authentication, the server is given a copy of a user’s public key. When the user tries to log in, the server asks her to prove her identity by signing some data with her private key. The server then checks the signed data against its copy of the user’s public key.
In practice, using public keys for authentication is nice because it saves the user from having to manage a lot of passwords. A user can use the same key for multiple servers. She can choose to password-protect her key for extra security, or she can use a key with no password for a completely transparent login process.
To change the Twisted Cred backend for Example 14-1 to use
public key authentication, store a public key for each user and write a credentials checker
that accepts credentials implementing twisted.conch.credentials.ISSHPrivateKey. Verify the users’ credentials by
checking to make sure that their public keys match the keys you have stored and that their
signatures prove that the users possess the matching private keys. Example 14-2 implements this checker.
fromsshserverimportSSHDemoRealm,getRSAKeysfromtwisted.conchimporterrorfromtwisted.conch.sshimportkeys,factoryfromtwisted.credimportcheckers,credentials,portalfromtwisted.internetimportreactorfromtwisted.pythonimportfailurefromzope.interfaceimportimplementsimportbase64classPublicKeyCredentialsChecker(object):implements(checkers.ICredentialsChecker)credentialInterfaces=(credentials.ISSHPrivateKey,)def__init__(self,authorizedKeys):self.authorizedKeys=authorizedKeysdefrequestAvatarId(self,credentials):userKeyString=self.authorizedKeys.get(credentials.username)ifnotuserKeyString:returnfailure.Failure(error.ConchError("No such user"))# Remove the 'ssh-rsa' type before decoding.ifcredentials.blob!=base64.decodestring(userKeyString.split(" ")[1]):raisefailure.failure(error.ConchError("I don't recognize that key"))ifnotcredentials.signature:returnfailure.Failure(error.ValidPublicKey())userKey=keys.Key.fromString(data=userKeyString)ifuserKey.verify(credentials.signature,credentials.sigData):returncredentials.usernameelse:"signature check failed"returnfailure.Failure(error.ConchError("Incorrect signature"))sshFactory=factory.SSHFactory()sshFactory.portal=portal.Portal(SSHDemoRealm())# The server's keys.pubKey,privKey=getRSAKeys()sshFactory.publicKeys={"ssh-rsa":pubKey}sshFactory.privateKeys={"ssh-rsa":privKey}# Authorized client keys.authorizedKeys={"admin":"ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAAAgQC2HXjFquK08rpEQCxLu/f4btDQ/2r3qRImVV/daKfQDu6QVm2P0BQ91Svyg60/VKxASqA1/PeN8Q0jSrdKcABy9OKfkD2BCUk9gL0wCAfm8E5lNSbH54WY8l1XaUbQr+KitN1GSY/MgBvzqm5m7EdIHJjuX+54j4i0EEey46qJaQ=="}sshFactory.portal.registerChecker(PublicKeyCredentialsChecker(authorizedKeys))reactor.listenTCP(2222,sshFactory)reactor.run()
To test this example, you’ll need to generate a public key pair for the SSH client to use, if you don’t have one already. You can generate a key using the same command from the previous example. Once you’ve generated a key, you can get the public key from the file ~/.ssh/id_rsa.pub. Edit Example 14-2 to use your public key for the admin user in the authorizedKeys dictionary. Then run pubkeyssh.py to start the server on port 2222. You should log right in without being prompted for a password:
$ ssh admin@localhost -p 2222
>>> Welcome to my test SSH server.
Commands: clear echo help quit whoami
$If you try to log in as a user who doesn’t possess the matching private key, you’ll be denied access:
$ ssh bob@localhost -p 2222
Permission denied (publickey).
Example 14-2 reuses most of the SSH server classes from Example 14-1. To support public key authentication, it uses a new
credentials checker class named PublicKeyCredentialsChecker. PublicKeyCredentialsChecker accepts credentials implementing ISSHPrivateKey, which have the attributes username, blob, signature, and sigData. To verify the key,
PublicKeyCredentialsChecker goes through three tests.
First, it makes sure it has a public key on file for credentials.username. Next, it verifies that the public key provided in blob matches the public key it has on file for that user.
It’s possible that the user may have provided just the public key at this point, but not
a signed token. If the public key was valid but no signature was provided, PublicKeyCredentialsChecker.requestAvatar raises the special
exception twisted.conch.error.ValidPublicKey. The SSH
server will understand the meaning of this exception and ask the client for the missing
signature.
Finally, we use the key’s verify method to check whether
the data in the signature really is the data in sigData
signed with the user’s private key. If verify returns
True, authentication is successful and
requestAvatarId returns username as the
avatar ID.
Providing an Administrative Python Shell
Example 14-1 demonstrated how to provide an interactive shell through SSH. That example implemented its own language with a small set of commands. But there’s another kind of shell that you can run over SSH: the same interactive Python prompt you know and love from the command line.
The twisted.conch.manhole and twisted.conch.manhole_ssh modules have classes designed to provide a remote
interactive Python shell inside your running server. Example 14-3
demonstrates a web server that can be modified on the fly using SSH and twisted.conch.manhole.
fromtwisted.internetimportreactorfromtwisted.webimportserver,resourcefromtwisted.credimportportal,checkersfromtwisted.conchimportmanhole,manhole_sshclassLinksPage(resource.Resource):isLeaf=1def__init__(self,links):resource.Resource.__init__(self)self.links=linksdefrender(self,request):return"<ul>"+"".join(["<li><a href='%s'>%s</a></li>"%(link,title)fortitle,linkinself.links.items()])+"</ul>"links={'Twisted':'http://twistedmatrix.com/','Python':'http://python.org'}site=server.Site(LinksPage(links))reactor.listenTCP(8000,site)defgetManholeFactory(namespace,**passwords):realm=manhole_ssh.TerminalRealm()defgetManhole(_):returnmanhole.Manhole(namespace)realm.chainedProtocolFactory.protocolFactory=getManholep=portal.Portal(realm)p.registerChecker(checkers.InMemoryUsernamePasswordDatabaseDontUse(**passwords))f=manhole_ssh.ConchFactory(p)returnfreactor.listenTCP(2222,getManholeFactory(globals(),admin='aaa'))reactor.run()
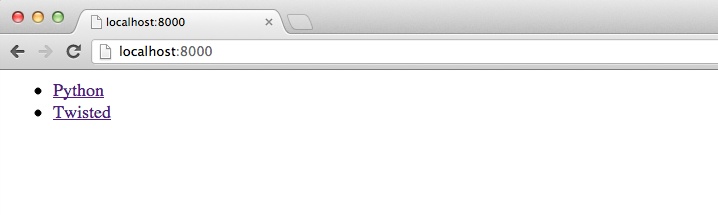
manholeserver.py will start up a web server on port 8000 and an SSH server on port 2222. Figure 14-1 shows what the home page looks like when the server starts.
Now log in using SSH. You’ll get a Python prompt, with full access to all the objects in the
server. Try modifying the links dictionary:
$ssh admin@localhost -p 2222admin@localhost's password:aaa>>>dir()['LinksPage', '__builtins__', '__doc__', '__file__', '__name__', 'checkers', 'getManholeFactory', 'links', 'manhole', 'manhole_ssh', 'portal', 'reactor', 'resource', 'server', 'site'] >>>links{'Python': 'http://python.org', 'Twisted': 'http://twistedmatrix.com/'} >>>links["Django"] = "http://djangoproject.com">>>links["O'Reilly"] = "http://oreilly.com">>>links{'Python': 'http://python.org', "O'Reilly": 'http://oreilly.com', 'Twisted': 'http://twistedmatrix.com/', 'Django': 'www.djangoproject.com'} >>>
Then refresh the home page of the web server. Figure 14-2 shows how your changes will be reflected on the website.
Example 14-3 defines a function called getManholeFactory that makes running a manhole SSH server trivially
easy. getManholeFactory takes an argument called namespace, which is a dictionary defining which Python objects to
make available, and then a number of keyword arguments representing usernames and
passwords. It constructs a manhole_ssh.TerminalRealm and
sets its chainedProtocolFactory.protocolFactory attribute
to an anonymous function that returns manhole.Manhole
objects for the requested namespace. It then sets up a portal using the realm and a dictionary
of usernames and passwords, attaches the portal to a manhole_ssh.ConchFactory, and returns the factory.
Note that passing a dictionary of Python objects as namespace is strictly for convenience (to limit the set of objects the user has
to look through). It is not a security mechanism. Only administrative
users should have permission to use the manhole server.
Example 14-3 creates a manhole factory using the built-in globals function, which returns a dictionary of all the objects in
the current global namespace. When you log in through SSH, you can see all the global objects
in manholeserver.py, including the
links dictionary. Because this dictionary is also used to generate the
home page of the website, any changes you make through SSH are instantly reflected on the Web.
Tip
The manhole_ssh.ConchFactory class includes
its own default public/private key pair. For your own projects, however, you shouldn’t rely
on these built-in keys. Instead, generate your own and set the publicKeys and privateKeys attributes of the ConchFactory.
See Example 14-1, earlier in this chapter, for an example of how
to do this.
Running Commands on a Remote Server
You can use twisted.conch to communicate with a server
using SSH: logging in, executing commands, and capturing the output.
SSH Clients
There are several classes that work together to make up a twisted.conch.ssh SSH client. The transport.SSHClientTransport class sets up the connection and verifies the
identity of the server. The userauth.SSHUserAuthClient
class logs in using your authentication credentials. The connection.SSHConnection class takes over once you’ve logged in and creates one
or more channel.SSHChannel objects, which you then use to
communicate with the server over a secure channel. Example 14-4 shows how you can use these classes to make an SSH client that logs
into a server, runs a command, and prints the output.
fromtwisted.conch.sshimporttransport,connection,userauth,channel,commonfromtwisted.internetimportdefer,protocol,reactorimportsys,getpassclassClientCommandTransport(transport.SSHClientTransport):def__init__(self,username,password,command):self.username=usernameself.password=passwordself.command=commanddefverifyHostKey(self,pubKey,fingerprint):# in a real app, you should verify that the fingerprint matches# the one you expected to get from this serverreturndefer.succeed(True)defconnectionSecure(self):self.requestService(PasswordAuth(self.username,self.password,ClientConnection(self.command)))classPasswordAuth(userauth.SSHUserAuthClient):def__init__(self,user,password,connection):userauth.SSHUserAuthClient.__init__(self,user,connection)self.password=passworddefgetPassword(self,prompt=None):returndefer.succeed(self.password)classClientConnection(connection.SSHConnection):def__init__(self,cmd,*args,**kwargs):connection.SSHConnection.__init__(self)self.command=cmddefserviceStarted(self):self.openChannel(CommandChannel(self.command,conn=self))classCommandChannel(channel.SSHChannel):name='session'def__init__(self,command,*args,**kwargs):channel.SSHChannel.__init__(self,*args,**kwargs)self.command=commanddefchannelOpen(self,data):self.conn.sendRequest(self,'exec',common.NS(self.command),wantReply=True).addCallback(self._gotResponse)def_gotResponse(self,_):self.conn.sendEOF(self)defdataReceived(self,data):datadefclosed(self):reactor.stop()classClientCommandFactory(protocol.ClientFactory):def__init__(self,username,password,command):self.username=usernameself.password=passwordself.command=commanddefbuildProtocol(self,addr):protocol=ClientCommandTransport(self.username,self.password,self.command)returnprotocolserver=sys.argv[1]command=sys.argv[2]username=raw_input("Username: ")password=getpass.getpass("Password: ")factory=ClientCommandFactory(username,password,command)reactor.connectTCP(server,22,factory)reactor.run()
Run sshclient.py with two arguments: a hostname and a command. It will ask for your username and password, log into the server, execute the command, and print the output. For example, you could run the who command to get a list of who’s currently logged in to the server:
$python sshclient.pyUsername:myserver.example.comwhoPassword:jesstessroot pts/0 Jun 11 21:35 (192.168.0.13) phil pts/2 Jun 22 13:58 (192.168.0.1) phil pts/3 Jun 22 13:58 (192.168.0.1)password
The ClientCommandTransport class in Example 14-4 handles the initial connection to the SSH server. Its
verifyHostKey method checks to make sure the server’s
public key matches your expectations. Typically, you’d remember each server the first time
you connected and then check on subsequent connections to make sure that another server
wasn’t maliciously trying to pass itself off as the server you expected. Here, it just
returns a True value without bothering to check the key.
The connectionSecure method is called as soon as the
initial encrypted connection has been established. This is the appropriate time to send your
login credentials, by passing a userauth.SSHUserAuthClient
to self.requestService, along with a connection.SSHConnection object that should manage the connection
after authentication succeeds.
The PasswordAuth class inherits from userauth.SSHUserAuthClient. It has to implement only a single
method, getPassword, which returns the password it will
use to log in. If you wanted to use public key authentication, you’d implement the methods
getPublicKey and getPrivateKey instead, returning the appropriate key as a string in each case.
The ClientConnection class in Example 14-4 will have its serviceStarted method called as soon as the client has
successfully logged in. It calls self.openChannel with a
CommandChannel object, which is a subclass of channel.SSHChannel. This object is used to work with an
authenticated channel to the SSH server. Its channelOpen
method is called when the channel is ready.
At this point, you can call self.conn.sendRequest to send a
command to the server. You have to encode data sent over SSH as a specially formatted
network string; to get a string in this format, pass it to the twisted.conch.common.NS function. Set the keyword argument wantReply to True if you’re
interested in getting a response from the command; this setting will cause sendRequest to return a Deferred
that will be called back when the command is completed. (If you don’t set wantReply to True, sendRequest will return None.) As
data is received from the server, it will be passed to dataReceived. Once you’re done using the channel, close it by
calling self.conn.sendEOF. The closed method will be called to let you know when the channel has
been successfully closed.
More Practice and Next Steps
This chapter introduced the Twisted Conch subproject through example SSH clients and servers. Some of the examples utilized insults, Twisted’s terminal control library. Others utilized the twisted.conch.manhole module for introspecting and interacting with a running Python process.
The Twisted Conch HOWTO walks through implementing an SSH client. Prolific Twisted Core developer JP Calderone walks through implementing an SSH server in his “Twisted Conch in 60 Seconds” series.
The Twisted Conch examples include an insults-based drawing application, a Python interpreter with syntax highlighting, a telnet server, and scrolling.