 Appendix A Objective Map
by
AWS Certified Solutions Architect Associate All-in-One Exam Guide, Second Edition (Exam SAA-C02), 2nd Edition
Appendix A Objective Map
by
AWS Certified Solutions Architect Associate All-in-One Exam Guide, Second Edition (Exam SAA-C02), 2nd Edition
- Cover
- About the Author
- Title Page
- Copyright Page
- Dedication
- Contents at a Glance
- Contents
- Acknowledgments
- Introduction
- Chapter 1 Overview of Cloud Computing and Amazon Web Services
- Advantages of Running Cloud Computing on AWS
- Three Models of Cloud Computing
- Three Cloud Computing Deployment Models
- History of AWS
- AWS Global Infrastructure
- AWS Security and Compliance
- AWS Products and Services
- Compute
- Networking
- Security and Compliance
- Storage and Content Delivery
- Database
- Analytics
- Application Services
- Developer Tools
- Management Tools
- Messaging
- Migration
- Artificial Intelligence
- Internet of Things
- Mobile Services
- Chapter Review
- Questions
- Answers
- Chapter 2 Storage on AWS
- Amazon Simple Storage Service (S3)
- Advantages of Amazon S3
- Usage of Amazon S3 in Real Life
- Amazon S3 Basic Concepts
- Amazon S3 Data Consistency Model
- Amazon S3 Performance Considerations
- Reverse the Key Name String
- Adding a Hex Hash Prefix to a Key Name
- Encryption in Amazon S3
- Amazon S3 Access Control
- Access Policies
- Bucket Policies
- Access Control List
- S3 Security Best Practices
- Amazon S3 Storage Class
- Versioning of Objects in Amazon S3
- Amazon S3 Object Lifecycle Management
- Amazon S3 Replication
- Static Web Site Hosting in Amazon S3
- Amazon S3 Glacier
- Amazon S3 Glacier Key Terminology
- Accessing Amazon S3 Glacier
- Uploading Files to AmazonS3 Glacier
- Retrieving Files from Amazon S3 Glacier
- Amazon Elastic Block Store
- Features of Amazon EBS
- AWS Block Storage Offerings
- Amazon Elastic File System
- Using Amazon Elastic File System
- Performance Mode of Amazon EFS
- On-Premise Storage Integration with AWS
- AWS Storage Gateway
- AWS Snowball and AWS Snowball Edge
- AWS Snowmobile
- Chapter Review
- Lab 2-1: Creating, Moving, and Deleting Objects in Amazon S3
- Lab 2-2: Using Version Control in Amazon S3
- Lab 2-3: Using the Bucket Policy Generator for Amazon S3
- Questions
- Answers
- Chapter 3 Virtual Private Cloud
- Amazon VPC Components and Terminology
- Amazon VPC
- Subnet
- Route Table
- Internet Gateway
- Network Address Translation
- Egress-Only Internet Gateway
- Elastic Network Interface
- Enhanced Networking (Linux Only)
- Elastic IP Address
- Network Security
- Amazon VPC Peering
- Amazon VPC Endpoint
- Transit Gateway
- DNS and VPC
- DHCP Option Sets
- Connecting to a VPC
- VPC Flow Logs
- Default VPC
- Labs on VPC
- Lab 3-1: Using the VPC Wizard
- Lab 3-2: Creating a VPC with Public and Private Subnets
- Lab 3-3: Exploring All the Options in a Virtual Private Cloud
- Chapter Review
- Questions
- Answers
- Chapter 4 Introduction to Amazon Elastic Compute Cloud
- Benefits of Amazon EC2
- Amazon EC2 Instance Types and Features
- General Purpose (T3, T3a, T2, M6g, M5, M5a, M5n, M4, and A1)
- Compute Optimized (C6g, C5, C5a, C5n, and C4)
- Memory Optimized (R6g, R5, R5a, R5n, R4, X1e, X1, High Memory, and Z1d)
- Storage Optimized (I3, I3en, D2, and H1)
- Accelerated Computing (P3, P2, Inf1, G4, G3, and F1)
- Processor Features
- Network Features
- Storage Features
- Steps for Using Amazon EC2
- Pricing for Amazon EC2
- On-Demand Instance
- Reserved Instance
- Spot Instance
- Shared Tenancy, Dedicated Hosts, and Dedicated Instances
- Shared Tenancy
- Dedicated Host
- Dedicated Instance
- Instances and AMIs
- Instance Root Volume
- Obtaining an AMI
- Virtualization in AMI
- HVM AMI
- PV AMI
- Instance Life Cycle
- Launch
- Start and Stop
- Reboot
- Termination
- Retirement
- Connecting to an Instance
- Security Group
- Amazon Elastic Container Service
- Lab 4-1: Using EC2
- Creating a New Key Pair
- Launching a Web Server Instance
- Browsing the Web Server
- Lab 4-2: Creating an EBS Instance and Attaching It to an EC2 Instance
- Lab 4-3: Creating an Elastic File System (EFS) and Mounting Across Two EC2 Instances in Different AZs
- Chapter Review
- Questions
- Answers
- Chapter 5 Identity and Access Management and Security on AWS
- Authentication
- Authorization
- Auditing
- Types of Security Credentials
- Temporary Security Credentials
- Users
- Groups
- Roles
- IAM Hierarchy of Privileges
- IAM Best Practices
- Use the IAM User
- Create a Strong Password Policy
- Rotate Security Credentials Regularly
- Enable MFA
- Manage Permissions with Groups
- Grant the Least Privileges
- Use IAM Roles
- Use IAM Roles for Amazon EC2 Instances
- Use IAM Policy Conditions for Extra Security
- Enable AWS CloudTrail
- AWS Compliance Program
- Shared Responsibility Model
- AWS Responsibility
- Customer’s Responsibility
- AWS Security Products and Services
- Resource Access Manager
- AWS Secrets Manager
- Amazon GuardDuty
- Amazon Inspector
- Amazon Macie
- AWS Certificate Manager
- AWS Web Application Firewall
- AWS Shield
- AWS CloudHSM
- AWS KMS
- Lab 5-1: Creating IAM Users, Groups, and Roles
- Managing IAM User Permissions and Credentials
- IAM Roles for Amazon EC2
- Chapter Review
- Questions
- Answers
- Chapter 6 Auto Scaling
- Benefits of Auto Scaling
- Scaling Plan
- Identify Scalable Resources
- Specify Scaling Strategy
- Using EC2 Auto Scaling
- Launch Configuration
- Auto Scaling Groups
- Termination Policy
- Elastic Load Balancing
- How ELB Works
- Types of Load Balancers
- Load Balancer Key Concepts and Terminology
- Health Check
- Using Multiple AZs
- Lab 6-1: Set Up Auto Scaling
- Chapter Review
- Questions
- Answers
- Chapter 7 Deploying and Monitoring Applications on AWS
- AWS Lambda
- Is AWS Lambda Really Serverless?
- Understanding AWS Lambda
- Amazon API Gateway
- API Types Supported by API Gateway
- Benefits of Amazon API Gateway
- Amazon Kinesis
- Real-Time Application Scenarios
- Differences Between Batch and Stream Processing
- Amazon Kinesis Data Steams
- Benefits of Amazon Kinesis Data Streams
- Amazon Kinesis Data Firehose
- Benefits of Amazon Kinesis Data Firehose
- Amazon Kinesis Data Analytics
- Benefits of Amazon Kinesis Data Analytics
- Use Cases for Amazon Kinesis Data Analytics
- Amazon Kinesis Video Streams
- Reference Architectures Using Serverless Services
- Real-Time File Processing
- Real-Time Stream Processing
- Extract, Transformation, and Load (ETL) Processing
- IoT Back Ends
- Amazon CloudFront
- Amazon CloudFront Key Concepts
- Geo Restriction
- Error Handling
- Amazon Route 53
- AWS Web Application Firewall
- Amazon Shield
- Benefits of AWS Shield
- Amazon Simple Queue Service
- Amazon Simple Notification Service
- AWS Step Functions and Amazon Simple Workflow (SWF)
- AWS Elastic Beanstalk
- AWS OpsWorks
- Amazon Cognito
- Amazon Elastic MapReduce
- AWS CloudFormation
- Monitoring in AWS
- Amazon CloudWatch
- Metrics Collection and Tracking
- Capture Real-Time Changes Using Amazon CloudWatch Events
- Monitoring and Storing Logs
- Set Alarms
- View Graphs and Statistics
- AWS CloudTrail
- AWS Config
- Amazon VPC Flow Logs
- AWS Trusted Advisor
- AWS Organizations
- Chapter Review
- Questions
- Answers
- Chapter 8 Databases on AWS
- Understanding Relational Databases
- Understanding the Amazon Relational Database Service
- Scenario 1: Hosting the Database in Your Data Center On-Premises
- Scenario 2: Hosting the Database on Amazon EC2 Servers
- Scenario 3: Hosting the Database Using Amazon RDS
- Hosting a Database in Amazon EC2 vs. Amazon RDS
- High Availability on Amazon RDS
- Simplest Architecture: Single-AZ Deployment
- High Availability: Multiple AZs
- Scaling on Amazon RDS
- Changing the Instance Type
- Read Replica
- Security on Amazon RDS
- Amazon VPC and Amazon RDS
- Backups, Restores, and Snapshots
- Monitoring
- Amazon Aurora
- Amazon Redshift
- Benefits of Amazon Redshift
- Amazon Redshift Architecture
- Sizing Amazon Redshift Clusters
- Networking for Amazon Redshift
- Encryption
- Security
- Backup and Restore
- Data Loading in Amazon Redshift
- Data Distribution in Amazon Redshift
- Amazon DynamoDB
- Benefits of Amazon DynamoDB
- Amazon DynamoDB Terminology
- Secondary Index
- Consistency Model
- Global Table
- Amazon DynamoDB Streams
- Amazon DynamoDB Accelerator
- Encryption and Security
- Amazon ElastiCache
- Amazon Neptune
- Benefits of Amazon Neptune
- Amazon Neptune Use Cases
- Amazon DocumentDB
- Benefits of Amazon DocumentDB
- Amazon DocumentDB Use Cases
- Lab 8-1: RDS: Creating an Amazon Aurora Database
- Lab 8-2: Taking a Snapshot of a Database
- Lab 8-3: Creating an Amazon Redshift Cluster
- Lab 8-4: Creating an Amazon DynamoDB Table
- Chapter Review
- Questions
- Answers
- Chapter 9 AWS Well-Architected Framework and Best Practices
- Operational Excellence
- Prepare
- Operate
- Evolve
- Security
- Have a Strong Identity Foundation
- Enable Traceability
- Implement Security at All Layers
- Secure the Data
- Automate for Security
- Plan for Security Events
- Best Practices
- Performance
- Performance Efficiency
- Reliability
- Best Practices
- Cost Optimization Pillar
- Finding Cost-Effective Resources
- Matching Supply with Demand
- Being Aware of Expenditures
- Optimizing Over Time
- AWS Best Practices
- Design for Failures
- Build Security in Every Layer
- Leverage Multiple Storage Options
- Implement Elasticity
- Think Parallel
- Loosely Couple Your Architecture
- There Are No Constraints in the AWS Cloud
- Chapter Review
- Questions
- Answers
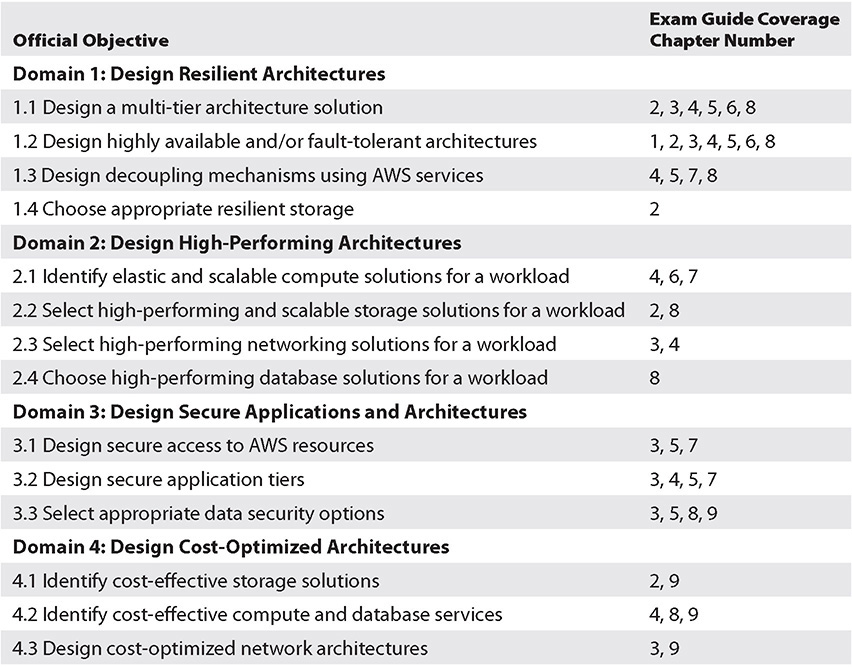
- Appendix A Objective Map
- Appendix B Additional Resources
- Appendix C About the Online Content
- Acronyms and Glossary
- Index
APPENDIX A
Objective Map
Exam SAA-C02
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.