Chapter 18. Understanding REST and JSON
This chapter covers the following exam topics:
6.0 Automation and Programmability
6.5 Describe characteristics of REST-based APIs (CRUD, HTTP verbs, and data encoding)
6.7 Interpret JSON encoded data
To automate and program networks, some automation software does several tasks. The software analyzes data in the form of variables, makes decisions based on that analysis, and then may take action to change the configuration of network devices or report facts about the state of the network.
The different automation functions reside on different devices: the network engineer’s device, a server, a controller, and the various network devices themselves. For these related automation processes to work well, all these software components need useful well-defined conventions to allow easy communication between software components.
This chapter focuses on two conventions that allow automation software to communicate. The first major section discusses application programming interfaces (APIs), specifically APIs that follow a style called REpresentational State Transfer (REST). APIs of any kind create a way for software applications to communicate, while RESTful APIs (APIs that use REST conventions) follow a particular set of software rules. Many APIs used in network automation today use REST-based APIs.
The second half of the chapter focuses on the conventions and standards for the data variables exchanged over APIs, with a focus on one: JavaScript Object Notation (JSON). If REST provides one standard method of how two automation programs should communicate over a network, JSON then defines how to communicate the variables used by a program: the variable names, their values, and the data structures of those variables.
“Do I Know This Already?” Quiz
Take the quiz (either here or use the PTP software) if you want to use the score to help you decide how much time to spend on this chapter. The letter answers are listed at the bottom of the page following the quiz. Appendix C, found both at the end of the book as well as on the companion website, includes both the answers and explanations. You can also find both answers and explanations in the PTP testing software.
Table 18-1 “Do I Know This Already?” Foundation Topics Section-to-Question Mapping
Foundation Topics Section |
Questions |
REST-based APIs |
1–3 |
Data Models and JSON |
4–6 |
1. Which of the following are required attributes of a REST-based API? (Choose two answers.)
Uses HTTP
Objects noted as to whether they can be cached
Classful operation
Client/server architecture
2. Which answers list a matching software development CRUD action to an HTTP verb that performs that action? (Choose two answers.)
CRUD create and HTTP PATCH
CRUD update and HTTP PATCH
CRUD delete and HTTP PUT
CRUD read and HTTP GET
3. Examine the following URI that works with a Cisco DNA Controller:
https://dnac.example.com/dna/intent/api/v1/network-device?managementIPAddress = 10.10.22.74
Which part of the URI, per the API documentation, is considered to identify the resource but not any parameters?
https://
dnac.example.com
dna/intent/api/v1/network-device
managementIPAddress = 10.10.22.74
4. Which of the following data serialization and data modeling languages would be most likely to be used in a response from a REST-based server API used for networking applications? (Choose two answers.)
JSON
YAML
JavaScript
XML
5. Which answers correctly describe the format of the JSON text below? (Choose two answers.)
{ "myvariable":[1,2,3] }
One JSON object that has one key:value pair
One JSON object that has three key:value pairs
A JSON object whose value is a second JSON object
A JSON object whose value is a JSON array
6. Which answers refer to JSON values rather than JSON keys as found in the sample JSON data? (Choose two answers.)
{
"response": {
"type": "Cisco Catalyst 9300 Switch",
"family": "Switches and Hubs",
"role": "ACCESS",
"managementIpAddress": "10.10.22.66"
}
}
“response”
“type”
“ACCESS”
The entire gray area
Answers to the “Do I Know This Already?” quiz:
1 B, D
2 B, D
3 C
4 A, D
5 A, D
6 C, D
Foundation Topics
REST-Based APIs
Applications use application programming interfaces (APIs) to communicate. To do so, one program can learn the variables and data structures used by another program, making logic choices based on those values, changing the values of those variables, creating new variables, and deleting variables. APIs allow programs running on different computers to work cooperatively, exchanging data to achieve some goal.
In an API software world, some applications create an API, with many other applications using (consuming) the API. Software developers add APIs to their software so other application software can make use of the first application’s features.
When writing an application, the developer will write some code, but often the developer may do a lot of work by looking for APIs that can provide the data and functions, reducing the amount of new code that must be written. As a result, much of modern software development centers on understanding and learning new APIs, along with the available libraries (prebuilt software that can be used to accomplish tasks rather than writing the equivalent from scratch).
Several types of APIs exist, each with a different set of conventions to meet a different set of needs. The CCNA blueprint mentions one type of API—REpresentational State Transfer (REST)—because of its popularity as a type of API in networking automation applications. This first major section of the chapter takes a closer look at REST-based APIs.
REST-Based (RESTful) APIs
REST APIs follow a set of foundational rules about what makes a REST API and what does not. First, from a literal perspective, REST APIs include the six attributes defined a few decades back by its creator, Roy Fielding. (You can find a good summary at https://restfulapi.net). Those six attributes are

Client/server architecture
Stateless operation
Clear statement of cacheable/uncacheable
Uniform interface
Layered
Code-on-demand
The first three of these attributes get at the heart of how a REST API works. You can more easily see those first three features at work with networking REST APIs, so the next few paragraphs give a little more explanation about those first three points.
Client/Server Architecture
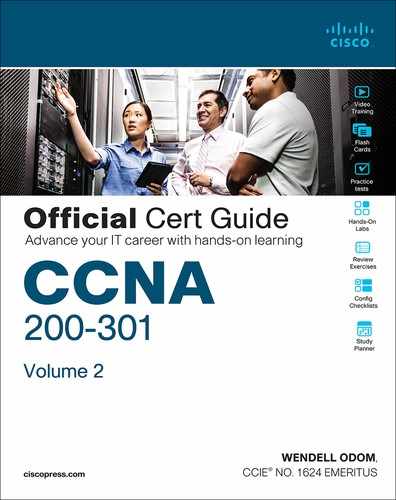
Like many applications, REST applications use a client/server architectural model. First, an application developer creates a REST API, and that application, when executing, acts as a REST server. Any other application can make a REST API call (the REST client) by executing some code that causes a request to flow from the client to the server. For instance, in Figure 18-1
The REST client on the left executes a REST API call, which generates a message sent to the REST server.
The REST server on the right has API code that considers the request and decides how to reply.
The REST server sends back the reply message with the appropriate data variables in the reply message.
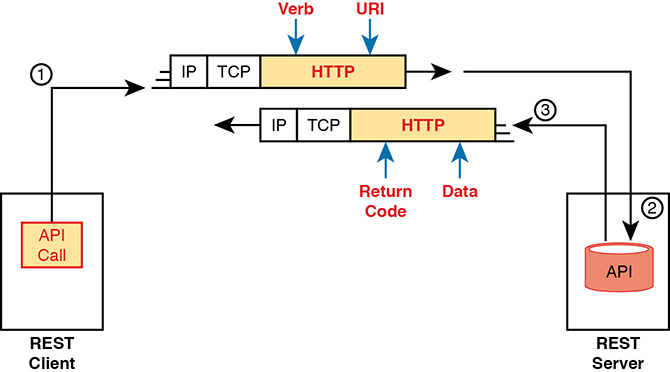
Figure 18-1 Client/Server Operation with REST
Stateless Operation
The stateless attribute of REST APIs means that REST does not record and use information about one API exchange for the purpose of how subsequent API exchanges are processed. In other words, each API request and reply does not use any other past history considered when processing the request.
For comparison, the TCP protocol uses a stateful approach, whereas UDP uses stateless operation. A TCP connection requires the endpoints to initialize variables on each end, with those variables updating over time, and with those variables being used for subsequent TCP messages. For instance, TCP uses sequence numbers and acknowledgment numbers to manage the flow of data in a TCP connection.
Cacheable (or Not)
To appreciate what is meant by cacheable, consider what happens when you browse a website. When your browser loads a new web page, the page itself contains a variety of objects (text, images, videos, audio). Some objects seldom change, so it would be better to download the object once and not download it again; in that case, the server marks that object as cacheable. For instance, a logo or other image shown on many pages of a website would almost never change and would likely be cacheable. However, the product list returned in your most recent search of the website would not be cacheable because the server would want to update and supply a new list each time you request the page.
REST APIs require that any resource requested via an API call have a clear method by which to mark the resource as cacheable or not. The goals remain the same: improve performance by retrieving resources less often (cacheable). Note that cacheable resources are marked with a timeframe so that the client knows when to ask for a new copy of the resource again.
Background: Data and Variables
To appreciate a few of the upcoming topics, it helps to have a basic idea about how programming languages use variables. Anyone who has done even a small amount of programming should have enough background, but for those who have not written programs before, this next topic gives you enough background about data and variables inside programs to understand the next topic.
If you have some programming experience and already know about simple variables, list variables, and dictionary variables, then feel free to skip ahead to the section “REST APIs and HTTP.”
Simple Variables
Applications all process data with the same general actions, starting with some kind of input. The program needs data to process, so the input process reads files, sends database queries to a database server, or makes API calls to retrieve data from another application’s API. The goal: gather the data that the program needs to process to do its work.
Programs then process data by making comparisons, making decisions, creating new variables, and performing mathematical formulas to analyze the data. All that logic uses variables. For instance, a program might process data with the following logic:
If the router’s G0/0 interface has a configuration setting of switchport mode dynamic auto, then gather more data to ensure that interface currently operates as a trunk rather than as an access port.
In programming, a variable is a name or label that has an assigned value. To get a general sense for programming variables, you can think of variables much like variables from algebra equations back in school. Example 18-1 shows some samples of variables of different types in a Python program (the Python language is the most popular language today for writing network automation applications). This program begins with a comment (the top three lines with triple single quotes) and then creates four variables, assigning them to different values, and prints a line of output: “The product is -12.”
Example 18-1 Simple Python Program That Shows a Product
''' Sample program to multiply two numbers and display the result ''' x = 3 y = -4 z = 1.247 heading = "The product is " print(heading,x*y)
The variables in Example 18-1 can be called simple variables because each variable name has a single value associated with it. Simple variables have one variable name and one associated value, so they have a simple structure.
The values of simple variables can have a variety of formats, as shown in Example 18-1. The example includes variables that contain
Unsigned integers (x)
Signed integers (y)
Floating-point numbers (z)
Text (heading)
List and Dictionary Variables
While simple variables have many great uses, programs need variables with more complex data structures. In programming, a data structure defines a related set of variables and values. For instance, Python uses list variables so that one variable name is assigned a value that is a list of values rather than a single value. You could imagine that a network automation program might want to have lists, such as a list of devices being managed, a list of interfaces on a device, or list of configuration settings on an interface.
First, consider the variable named list1 in Example 18-2; note that the lines that begin with a # are comment lines.
Example 18-2 Sample List and Dictionary Variables in Python
# Variable list1 is a list in Python (called an array in Java)
list1 = ["g0/0", "g0/1", "g0/2"]
# Variable dict1 is a dictionary (called an associative array in Java)
dict1 = {"config_speed":'auto', "config_duplex":"auto", "config_ip":"10.1.1.1"}
Even if you have never seen Python code before, you can guess at some of the meaning of the list1 variable. The code assigns variable list1 to a value that itself is a list of three text strings. Note that the list could include text, unsigned integers, signed integers, and so on.
Figure 18-2 shows the data structure behind variable list1 in Example 18-2. The variable is assigned to the list, with the list having three list elements.
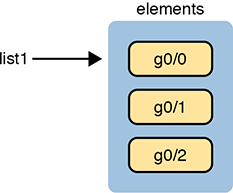
Figure 18-2 The List Data Structure in Python
Python supports a similar data structure called a dictionary. If you think of the contents of a dictionary for the English language, that dictionary lists a series of paired items: a term and a matching definition. With programming languages like Python, the dictionary data structure lists paired items as well: keys (like terms) and values (like definitions). Figure 18-3 shows the structure of that dictionary value matching the dict1 variable at the bottom of Example 18-2. Note that each key and its value is called a key:value pair.

Figure 18-3 Dictionary Data Structures in Python
Data structures can get more complex. Additionally, the data structures can be nested. For instance, a single variable’s value could be a list, with each list element being a dictionary, with the values in some key:value pairs being other lists, and so on. For now, be aware of the fact that programs use simple variables but also use list and dictionary variables to make it easier to perform different kinds of logic.
REST APIs and HTTP
APIs exist to allow two programs to exchange data. Some APIs may be designed as an interface between programs running on the same computer, so the communication between programs happens within a single operating system. Many APIs need to be available to programs that run on other computers, so the API must define the type of networking protocols supported by the API—and many REST-based APIs use the HTTP protocol.
The creators of REST-based APIs often choose HTTP because HTTP’s logic matches some of the concepts defined more generally for REST APIs. HTTP uses the same principles as REST: it operates with a client/server model; it uses a stateless operational model; and it includes headers that clearly mark objects as cacheable or not cacheable. It also includes verbs—words that dictate the desired action for a pair HTTP Request and Reply—which matches how applications like to work.
This section breaks down the fundamentals of some programming terminology, how that matches HTTP verbs, and how REST APIs make use of Uniform Resource Identifiers (URIs) to specify the data desired from a RESTful API call.
Software CRUD Actions and HTTP Verbs
The software industry uses a memorable acronym—CRUD—for the four primary actions performed by an application. Those actions are

Create: Allows the client to create some new instances of variables and data structures at the server and initialize their values as kept at the server
Read: Allows the client to retrieve (read) the current value of variables that exist at the server, storing a copy of the variables, structures, and values at the client
Update: Allows the client to change (update) the value of variables that exist at the server
Delete: Allows the client to delete from the server different instances of data variables
For instance, if using the northbound REST API of a DNA controller, as discussed in Chapter 17, “Cisco Software-Defined Access (SDA),” you might want to create something new, like a new security policy. From a programming perspective, the security policy exists as a related set of configuration settings on the DNA controller, internally represented by variables. To do that, a REST client application would use a create action, using the DNA Center RESTful API, that created variables on the DNA Controller via the DNA Center REST API. The concept of creating new configuration at the controller is performed via the API using a create action per the CRUD generic acronym.
Other examples of CRUD actions include a check of the status of that new configuration (a read action), an update to change some specific setting in the new configuration (an update action), or an action to remove the security policy definition completely (a delete action).
HTTP uses verbs that mirror CRUD actions. HTTP defines the concept of an HTTP request and reply, with the client sending a request and with the server answering back with a reply. Each request/reply lists an action verb in the HTTP request header, which defines the HTTP action. The HTTP messages also include a URI, which identifies the resource being manipulated for this request. As always, the HTTP message is carried in IP and TCP, with headers and data, as represented in Figure 18-4.

Figure 18-4 HTTP Verb and URI in an HTTP Request Header
To get some perspective about HTTP, ignore REST for a moment. Whenever you open a web browser and click a link, your browser generates an HTTP GET request message similar to Figure 18-4 in structure. The message includes an HTTP header with the GET verb and the URI. The resources returned in the reply are the components of a web page, like text files, image files, and video files.
HTTP works well with REST in part because HTTP has verbs that match the common program actions in the CRUD paradigm. Table 18-2 lists the HTTP verbs and CRUD terms for easy reference and study.

Table 18-2 Comparing CRUD Actions to REST Verbs
Action |
CRUD Term |
REST (HTTP) Verb |
Create new data structures and variables |
Create |
POST |
Read (retrieve) variable names, structures, and values |
Read |
GET |
Update or replace values of some variable |
Update |
PATCH, PUT |
Delete some variables and data structures |
Delete |
DELETE |
Using URIs with HTTP to Specify the Resource
In addition to using HTTP verbs to perform the CRUD functions for an application, REST uses URIs to identify what resource the HTTP request acts on. For REST APIs, the resource can be any one of the many resources defined by the API. Each resource contains a set of related variables, defined by the API and identified by a URI.
For instance, imagine a user creates a REST-based API. When she does so, she creates a set of resources that she wants to make available via the API, and she also assigns a unique URI to each resource. In other words, the API creator creates a URI and a matching set of variables, and defines the actions that can be performed against those variables (read, update, and so on).
The API creator also creates API documentation that lists the resources and the URI that identifies each resource, among other details. The programmer for a REST client application can read the API documentation, build a REST API request, and ask for the specific resource, as shown in the example in Figure 18-5.
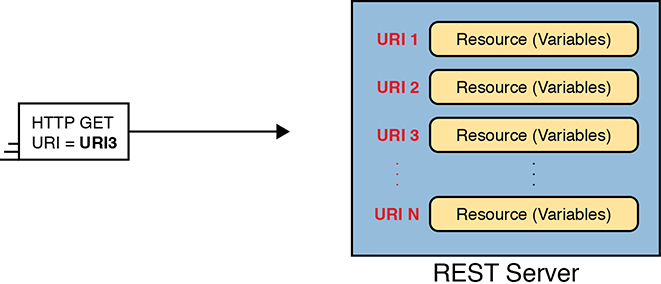
Figure 18-5 One URI for Each API Resource—Conceptual View
Figure 18-5 shows the URIs as generic values; however, today’s network engineers need to be able to read API documentation, see URIs in that documentation, and understand the meaning of each part of the URI. Figure 18-6 shows a URI specific to the Cisco DNA Center northbound REST API as an example of some of the components of the URI.
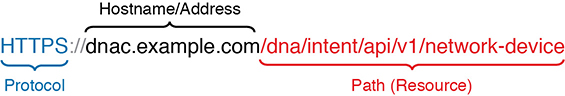
Figure 18-6 URI Structure for REST GET Request
The figure shows these important values and concepts:
HTTPS: The letters before the :// identify the protocol used—in this case, HTTP Secure (which uses HTTP with SSL encryption).
Hostname or IP Address: This value sits between the // and first /, and identifies the host; if using a hostname, the REST client must perform name resolution to learn the IP address of the REST server.
Path (Resource): This value sits after the first / and finishes either at the end of the URI or before any additional fields (like a parameter query field). HTTP calls this field the path, but for use with REST, the field uniquely identifies the resource as defined by the API.
To drive home the connection between the API, URI, and resource part of the API, it can be helpful to just do a general tour of the API documentation for any REST-based API. For instance, when Cisco created DNA Center, it created the REST-based northbound interface and chose one URI as shown in Figure 18-6. Figure 18-7 shows a copy of the doc page for that particular resource for comparison. Go to https://developer.cisco.com and search for “Cisco DNA Center API documentation.” Continue to search for yourself to see more examples of the resources defined by the Cisco DNA Center API.

Figure 18-7 DNA Center API Doc Page for the Network Device (List) Resource
Many of the HTTP request messages need to pass information to the REST server beyond the API. Some of that data can be passed in header fields—for instance, REST APIs use HTTP header fields to encode much of the authentication information for REST calls. Additionally, parameters related to a REST call can be passed as parameters as part of the URI itself.
For instance, the URI in Figure 18-6 asks the Cisco DNA Center for a list of all known devices, with Cisco DNA Center returning a dictionary of values for each device. You might instead want that dictionary of values for only a single device. The Cisco DNA Center API allows for just that by tacking on the following to the end of the URI shown in Figure 18-6.
?managementIPAddress = 10.10.22.66&macAddress = f8:7b:20:67:62:80
Figure 18-8 summarizes the major components of the URIs commonly used with a REST API, with the resource and parameter parts of the URI identifying specifically what the API should supply to the REST client.

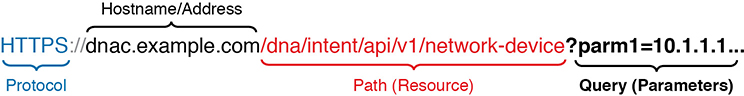
Figure 18-8 Example Components of a URI Used in a REST API Call
Example of REST API Call to DNA Center
To pull some of the REST API concepts together, the next few pages work through a few sample API calls using a software application called an API development environment tool.
For a bit of development perspective, when working to automate some part of your network operation tasks, you would eventually use a program that made API calls. However, early in the process of developing an application, you might first focus on the data available from the API and ignore all the programming details at first. API development environments let you focus on the API calls. Later, that same tool can typically generate correct code that you can copy into your program to make the API calls.
The examples in this section use an app named Postman. Postman can be downloaded for free (www.postman.co) and used as shown in this section. Note that Cisco DevNet makes extensive use of Postman in its many labs and examples.
The first example shows a screenshot of a part of the Postman app after it sends a REST client GET request to a DNA Center REST API (see Figure 18-9). In particular, look for the following:
The URI, near the top, lists a hostname of sandboxdnac2.cisco.com, which is an always-on DNA Center instance supplied by Cisco’s DevNet site (which you can use).
The resource part of the URI shows the same resource listed earlier in Figure 18-6, asking for a list of devices.
The bottom center of the window shows the data returned by the DNA Center REST HTTP GET response.
At the middle right, it lists the GET response’s status code of 200, meaning “OK.”
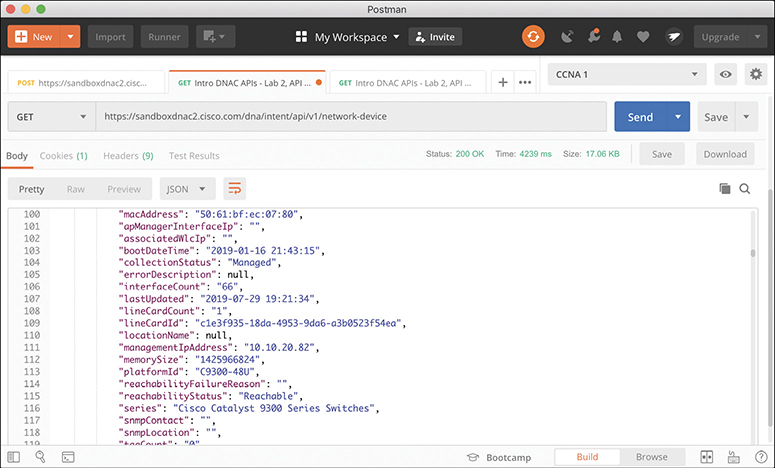
Figure 18-9 URI Structure for REST GET Request
Take a moment to look through the data at the bottom of the Postman window in Figure 18-9. The text follows a data modeling format called JavaScript Object Notation (JSON), which is one of the main topics for the remainder of the chapter. However, armed with just a knowledge of routers, you can find a few facts that look familiar. To help you see the text, Example 18-3 shows an edited (shortened to reduce the length) view of some of the JSON output in that window, just so you can see the format and some of the data returned in this single API call.
Example 18-3 JSON Output from a REST API Call
{
"response": {
"type": "Cisco Catalyst 9300 Switch",
"family": "Switches and Hubs",
"role": "ACCESS",
"macAddress": "f8:7b:20:67:62:80",
"hostname": "cat_9k_1",
"serialNumber": "FCW2136L0AK",
"softwareVersion": "16.6.1",
"upTime": "17 days, 22:51:04.26",
"interfaceCount": "41",
"lineCardCount": "2",
"managementIpAddress": "10.10.22.66",
"series": "Cisco Catalyst 9300 Series Switches",
"softwareType": "IOS-XE"
}
}
API development tools like Postman help you work out the particulars of each API call, save the details, and share with other engineers and developers. Eventually, you will be ready to make the API call from a program. With a simple click from the Postman UI, Postman supplies the code to copy/paste into your program so that it returns all the output shown in the center/bottom of the window back as a variable to your program.
By now, you have a good foundational knowledge of the mechanics of REST APIs. By learning some skills, and using the API documentation for any REST API, you could now experiment with and try to make REST API calls. For many of those, the data will return to you as text, often in JSON format, so the second half of the chapter examines the meaning of that text.
Data Serialization and JSON
In your journey to become a modern network engineer with network automation skills, you will learn to understand several data serialization languages. Each data serialization language provides methods of using text to describe variables, with a goal of being able to send that text over a network or to store that text in a file. Data serialization languages give us a way to represent variables with text rather than in the internal representation used by any particular programming language.
Each data serialization language enables API servers to return data so that the API client can replicate the same variable names as well as data structures as found on the API server. To describe the data structures, the data serialization languages include special characters and conventions that communicate ideas about list variables, dictionary variables, and other more complex data structures.
This second major section of the chapter examines the concept of a data serialization language, with a focus on the one data modeling language as mentioned in the current CCNA blueprint: JavaScript Object Notation (JSON).
The Need for a Data Model with APIs
This section shows some ideas of how to move variables in a program on a server to a client program. First, Figure 18-10 and surrounding text show a nonworking example as a way to identify some of the challenges with copying variable values from one device to another. Then Figure 18-11 and its related text show how to use a data serialization language to solve the problems shown around Figure 18-10.
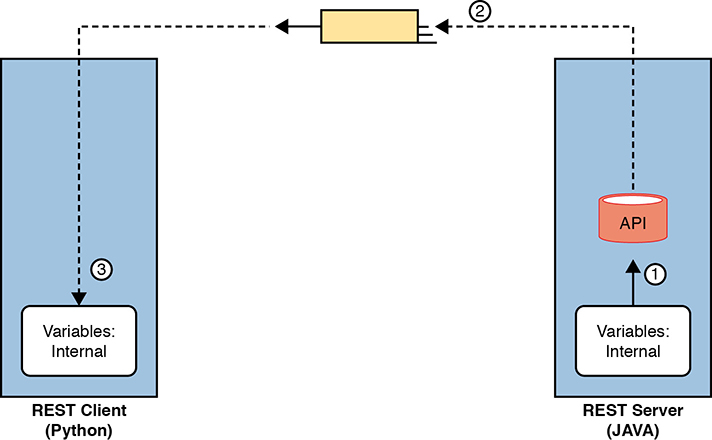
Figure 18-10 Broken Concept: Exchanging Internal Representations of Variables
First, for the nonworking example, consider the flow and numbered steps in Figure 18-10. A REST client sits on the left. The REST client asks for a resource, and the server needs to reply. In REST, a resource is a set of variables as defined by the API, so the REST server needs to return a set of variables to the REST client on the left. The steps in the figure run as follows:
The REST server (a JAVA application) takes a copy of the stored variables in RAM (step 1) in response to the REST request.
The REST API code creates the REST reply and sends it over the network, placing an exact replica of what the REST server had in RAM to represent the variables in that resource.
The REST client (a Python application) receives the REST reply message, storing the exact same bits and bytes into its RAM, in an attempt to have a copy of the variables, data, and data structures on the server.
The process shown in Figure 18-10 does not work (and is not attempted) because the REST client programs may not store variables in the same ways. First, programs written in different languages use different conventions to store their variables internally because there is no standard for internal variable storage across languages. In fact, programs written in the same language but with different versions of that language may not store all their variables with the same internal conventions.
To overcome these issues, applications need a standard method to represent variables for transmission and storage of those variables outside the program. Data serialization languages provide that function.
Figure 18-11 shows the correct process flow in comparison to Figure 18-10 with the data serialization process included:
The server collects the internally represented data and gives it to the API code.
The API converts the internal representation to a data model representing those variables (with JSON shown in the figure).
The server sends the data model in JSON format via messages across the network.
The REST client takes the received data and converts the JSON-formatted data into variables in the native format of the client application.

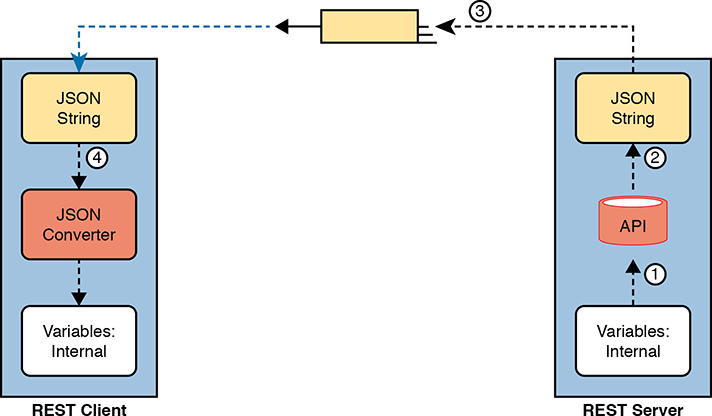
Figure 18-11 Correct Concept: Exchanging Internal Representations of Variables
At the end of the process, the REST client application now has equivalent variables to the ones it requested from the server in the API call. Note that the final step—to convert from the data serialization language to the native format—can be as little as a single line of code!
Finally, note that while data serialization languages like JSON enable applications to exchange variables over a network, applications can also store data in JSON format.
Data Serialization Languages
You will hear about and eventually use several data serialization and data modeling languages the more you learn about network automation. While the current CCNA blueprint mentions only JSON, learning a few facts about some of the alternatives can be helpful to add a little context to your new knowledge of JSON. These different data serialization languages exist to meet different needs that have arisen over the years. This next short section highlights four such languages.
JSON
JavaScript Object Notation attempts to strike a balance between human and machine readability. Armed with a few JSON rules, most humans can read JSON data, move past simply guessing at what it means, and confidently interpret the data structures defined by the JSON data. At the same time, JSON data makes it easy for programs to convert JSON text into variables, making it very useful for data exchange between applications using APIs.
You can find the details of JSON in IETF RFC 8259 and in a number of sites found with Internet searches, including www.json.org.
XML
Back in the 1990s, when web browsers and the World Wide Web (WWW) were first created, web pages primarily used Hypertext Markup Language (HTML) to define web pages. As a markup language, HTML defined how to add the text or a web page to a file and then add “markup”—additional text to denote formatting details for the text that should be displayed. For instance, the markup included codes for headings, font types, sizes, colors, hyperlinks, and so on.
The eXtensible Markup Language (XML) came later to make some improvements for earlier markup languages. In particular, over time web pages became more and more dynamic, and to make the pages dynamic, the files needed to store variables whose values could be changed and replaced over time by the web server. To define variables to be substituted into a web page, the world needed a markup language that could define data variables. XML defines a markup language that has many features to define variables, values, and data structures.
Over time, XML has grown beyond its original use as a markup language. XML’s features also make it a useful general data serialization language, and it is used as such today.
Comparing XML to JSON, both attempt to be human readable, but with XML being a little more challenging to read for the average person. For instance, like HTML, XML uses beginning and ending tags for each variable, as seen in Example 18-4. In the highlighted line in the example, the <macAddress> and </macAddress> tags denote a variable name, with the value sitting between the tags.
Example 18-4 JSON Output from a REST API Call
<?xml version = "1.0" encoding = "UTF-8"?>
<root>
<response>
<family>Switches and Hubs</family>
<hostname>cat_9k_1</hostname>
<interfaceCount>41</interfaceCount>
<lineCardCount>2</lineCardCount>
<macAddress>f8:7b:20:67:62:80</macAddress>
<managementIpAddress>10.10.22.66</managementIpAddress>
<role>ACCESS</role>
<serialNumber>FCW2136L0AK</serialNumber>
<series>Cisco Catalyst 9300 Series Switches</series>
<softwareType>IOS-XE</softwareType>
<softwareVersion>16.6.1</softwareVersion>
<type>Cisco Catalyst 9300 Switch</type>
<upTime>17 days, 22:51:04.26</upTime>
</response>
</root>
YAML
YAML Ain’t Markup Language (YAML) has a clever recursive name, but the name does tell us something. YAML does not attempt to define markup details (while XML does). Instead, YAML focuses on the data model (structure) details. YAML also strives to be clean and simple: of the data serialization/modeling languages listed here, YAML is easily the easiest to read for anyone new to data models.
Ansible, one of the topics in Chapter 19, “Understanding Ansible, Puppet, and Chef,” makes extensive use of YAML files. Example 18-5 shows a brief sample. And to make the point about readability, even if you have no idea what Ansible does, you can guess at some of the functions just reading the file. (Note that YAML denotes variables in double curly brackets: {{ }}.)
Example 18-5 YML File Used by Ansible
---
# This comment line is a place to document this Playbook
- name: Get IOS Facts
hosts: mylab
vars:
cli:
host: "{{ ansible_host }}"
username: "{{ username }}"
password: "{{ password }}"
tasks:
- ios_facts:
gather_subset: all
provider: "{{ cli }}"
Summary of Data Serialization
As an easy reference, Table 18-3 summarizes the data serialization languages mentioned in this section, along with some key facts.

Table 18-3 Comparing Data Modeling Languages
Acronym |
Name |
Origin/Definition |
Central Purpose |
Common Use |
JSON |
JavaScript Object Notation |
JavaScript (JS) language; RFC 8259 |
General data modeling and serialization |
REST APIs |
XML |
eXtensible Markup Language |
World Wide Web Consortium (W3C.org) |
Data-focused text markup that allows data modeling |
REST APIs, Web pages |
YAML |
YAML Ain’t Markup Language |
General data modeling |
Ansible |
Interpreting JSON
Cisco includes one exam topic in the current CCNA 200-301 blueprint that mentions JSON:
6.7 Interpret JSON encoded data
You can think of that skill and task with two major branches. First, even ignoring the syntax and special characters, anyone who knows the topic can probably make intelligent guesses about the meaning of many of the key:value pairs. For example, without knowing anything about JSON syntax, you could probably determine from your prior knowledge of Cisco routers and switches that the JSON in Example 18-6 lists two devices (maybe their host-names) and a list of interfaces on each device.
Example 18-6 Simple JSON That Lists a Router’s Interfaces
{
"R1": ["GigabitEthernet0/0", "GigabitEthernet0/1", "GigabitEthernet0/2/0"],
"R2": ["GigabitEthernet1/0", "GigabitEthernet1/1", "GigabitEthernet0/3/0"]
}
Honestly, you probably already know everything needed to do this kind of intelligent guessing. However, to perform the second type of task, where you analyze the JSON data to find the data structures, including objects, lists, and key:value pairs, you need to know a bit more about JSON syntax. This final topic in the chapter gives you the basic rules, with some advice on how to break down JSON data.
Interpreting JSON Key:Value Pairs
First, consider these rules about key:value pairs in JSON, which you can think of as individual variable names and their values:

Key:Value Pair: Each and every colon identifies one key:value pair, with the key before the colon and the value after the colon.
Key: Text, inside double quotes, before the colon, used as the name that references a value.
Value: The item after the colon that represents the value of the key, which can be
Text: Listed in double quotes.
Numeric: Listed without quotes.
Array: A special value (more details later).
Object: A special value (more details later)
Multiple Pairs: When listing multiple key:value pairs, separate the pairs with a comma at the end of each pair (except the last pair).
To work through some of these rules, consider Example 18-7’s JSON data, focusing on the three key:value pairs. The text after the example will analyze the example.
Example 18-7 One JSON Object (Dictionary) with Three Key:Value Pairs
{
"1stbest": "Messi",
"2ndbest": "Ronaldo",
"3rdbest": "Pele"
}
As an approach, just find each colon, and look for the quoted string just before each colon. Those are the keys (“1stbest”, “2ndbest”, and “3rdbest”.) Then look to the right of each colon to find their matching values. You can know all three values are text values because JSON lists the values within double quotes.
As for other special characters, note the commas and the curly brackets. The first two key:value pairs end with a comma, meaning that another key:value pair should follow. The curly brackets that begin and end the JSON data denote a single JSON object (one pair of curly brackets, so one object). JSON files, and JSON data exchanged over an API, exist first as a JSON object, with an opening (left) and closing (right) curly bracket as shown.
Interpreting JSON Objects and Arrays
To communicate data structures beyond a key:value pair with a simple value, JSON uses JSON objects and JSON arrays. Objects can be somewhat flexible, but in most uses, they act like a dictionary. Arrays list a series of values.
To begin, consider this set of rules about how to interpret the syntax for JSON objects and arrays:

{ } - Object: A series of key:value pairs enclosed in a matched pair of curly brackets, with an opening left curly bracket and its matching right curly bracket.
[ ] - Array: A series of values (not key:value pairs) enclosed in a matched pair of square brackets, with an opening left square bracket and its matching right square bracket.
Key:value pairs inside objects: All key:value pairs inside an object conform to the earlier rules for key:value pairs.
Values inside arrays: All values conform to the earlier rules for formatting values (for example, double quotes around text, no quotes around numbers).
Example 18-8 shows a single array in JSON format. Notice the JSON data begins with a [ and then lists three text values (the values could have been a mix of values). It then ends with a ].
Example 18-8 A JSON Snippet Showing a Single JSON Array (List)
[
"Messi",
"Ronaldo",
"Dybala"
]
While Example 18-8 shows only the array itself, JSON arrays can be used as a value in any key:value pair. Figure 18-12 does just that, shown in a graphic to allow easier highlighting of the arrays and object. The JSON text in the figure includes two arrays (lists) as values (each found just after a colon, indicating they are values).
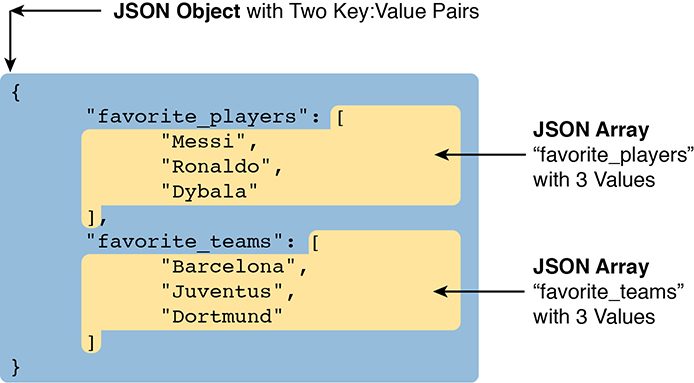
Figure 18-12 Accurate/Complete JSON Data with One Object, Two Keys, Two JSON List Values
Now think about the entire structure of the JSON data in Figure 18-12. It has a matched pair of curly brackets to begin and end the text, encapsulating one object. That object contains two colons, so there are two key:value pairs inside the object. When you think about the broader structure, as depicted in Figure 18-13, this JSON file has one JSON object, itself with two key:value pairs. (Note that Figure 18-13 does NOT show correct JSON syntax for the lists; it instead is intended to make sure you see the structure of the one object and its two key:value pairs.)
![A figure shows a JSON object with two key: value pair. The first key-value pair is "favorite_players":[...] and the second key-value pair is "favorite_teams": [...].](http://images-20200215.ebookreading.net/1/1/1/9780135262726/9780135262726__ccna-200-301-official__9780135262726__graphics__18fig13.jpg)
Figure 18-13 Structural Representation of Figure 18-13’s Primary Object and Two Key:Value Pairs
To drive home the idea of how to find JSON objects, consider the example shown in Figure 18-14. This figure shows correct JSON syntax. It has the following:
There is one object for the entire set because it begins and ends with curly braces.
The outer object has two keys (Wendells_favorites and interface_config).
The value of each key:value pair is another object (each with curly braces and three key:value pairs).
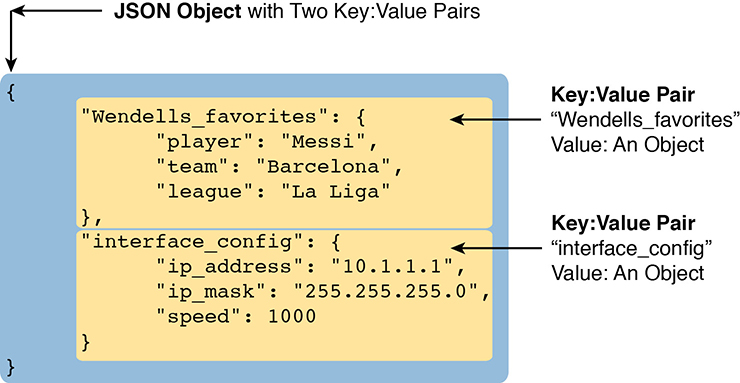
Figure 18-14 A JSON Object, with Two Key:Value Pairs, Each Value Another Object
The JSON example in Figure 18-14 shows how JSON can nest objects and arrays; that is, JSON puts one object or array inside another. Much of the JSON output you will see as you learn more and more about network automation will include JSON data with nested arrays and objects.
Minified and Beautified JSON
So far, all the JSON examples show lots of empty space. JSON allows for whitespace, or not, depending on your needs. For humans, reading JSON can be a lot easier with the text organized with space and aligned. For instance, having the matched opening and closing brackets sit at the same left-offset makes it much easier to find which brackets go with which.
When stored in a file or sent in a network, JSON does not use whitespace. For instance, earlier in this section, Example 18-7 showed one JSON object with three key:value pairs, with whitespace, taking five lines. However, stored in a file, or sent over a network, the JSON would look like the following:
{"1stbest": "Messi", "2ndbest": "Ronaldo", "3rdbest": "Pele"}
Most of the tools you might use when working with JSON will let you toggle from a pretty format (good for humans) to a raw format (good for computers). You might see the pretty version literally called pretty, or beautified, or spaced, while the version with no extra whitespace might be called minified or raw.
Chapter Review
One key to doing well on the exams is to perform repetitive spaced review sessions. Review this chapter’s material using either the tools in the book or interactive tools for the same material found on the book’s companion website. Refer to the “Your Study Plan” element for more details. Table 18-4 outlines the key review elements and where you can find them. To better track your study progress, record when you completed these activities in the second column.
Table 18-4 Chapter Review Tracking
Review Element |
Review Date(s) |
Resource Used |
Review key topics |
|
Book, website |
Review key terms |
|
Book, website |
Answer DIKTA questions |
|
Book, PTP |
Review memory tables |
|
Website |
Practice Editing JSON |
|
Website |
Review All the Key Topics

Table 18-5 Key Topics for Chapter 18
Key Topic Element |
Description |
Page Number |
List |
Attributes of REST APIs |
|
List |
The meaning of the CRUD acronym |
|
A comparison of CRUD actions and HTTP verbs |
||
Components of a URI |
||
The process of sending JSON data over a REST API |
||
A comparison of JSON, XML, and YAML |
||
List |
JSON rules related to key:value pairs |
|
List |
JSON rules for arrays and objects |
Key Terms You Should Know
REpresentational State Transfer (REST)
JSON (JavaScript Object Notation)
XML (eXtensible Markup Language)