Chapter 1
Security and Risk Management (Domain 1)
-
What is the final step of a quantitative risk analysis?
- Determine asset value.
- Assess the annualized rate of occurrence.
- Derive the annualized loss expectancy.
- Conduct a cost/benefit analysis.
-
An evil twin attack that broadcasts a legitimate SSID for an unauthorized network is an example of what category of threat?
- Spoofing
- Information disclosure
- Repudiation
- Tampering
-
Under the Digital Millennium Copyright Act (DMCA), what type of offenses do not require prompt action by an Internet service provider after it receives a notification of infringement claim from a copyright holder?
- Storage of information by a customer on a provider’s server
- Caching of information by the provider
- Transmission of information over the provider’s network by a customer
- Caching of information in a provider search engine
-
FlyAway Travel has offices in both the European Union and the United States and transfers personal information between those offices regularly. Which of the seven requirements for processing personal information states that organizations must inform individuals about how the information they collect is used?
- Notice
- Choice
- Onward Transfer
- Enforcement
-
Which one of the following is not one of the three common threat modeling techniques?
- Focused on assets
- Focused on attackers
- Focused on software
- Focused on social engineering
-
Which one of the following elements of information is not considered personally identifiable information that would trigger most US state data breach laws?
- Student identification number
- Social Security number
- Driver’s license number
- Credit card number
-
In 1991, the federal sentencing guidelines formalized a rule that requires senior executives to take personal responsibility for information security matters. What is the name of this rule?
- Due diligence rule
- Personal liability rule
- Prudent man rule
- Due process rule
-
Which one of the following provides an authentication mechanism that would be appropriate for pairing with a password to achieve multifactor authentication?
- Username
- PIN
- Security question
- Fingerprint scan
-
What United States government agency is responsible for administering the terms of safe harbor agreements between the European Union and the United States under the EU Data Protection Directive?
- Department of Defense
- Department of the Treasury
- State Department
- Department of Commerce
-
Yolanda is the chief privacy officer for a financial institution and is researching privacy issues related to customer checking accounts. Which one of the following laws is most likely to apply to this situation?
- GLBA
- SOX
- HIPAA
- FERPA
-
Tim’s organization recently received a contract to conduct sponsored research as a government contractor. What law now likely applies to the information systems involved in this contract?
- FISMA
- PCI DSS
- HIPAA
- GISRA
-
Chris is advising travelers from his organization who will be visiting many different countries overseas. He is concerned about compliance with export control laws. Which of the following technologies is most likely to trigger these regulations?
- Memory chips
- Office productivity applications
- Hard drives
- Encryption software
-
Bobbi is investigating a security incident and discovers that an attacker began with a normal user account but managed to exploit a system vulnerability to provide that account with administrative rights. What type of attack took place under the STRIDE model?
- Spoofing
- Repudiation
- Tampering
- Elevation of privilege
-
You are completing your business continuity planning effort and have decided that you wish to accept one of the risks. What should you do next?
- Implement new security controls to reduce the risk level.
- Design a disaster recovery plan.
- Repeat the business impact assessment.
- Document your decision-making process.
-
Which one of the following control categories does not accurately describe a fence around a facility?
- Physical
- Detective
- Deterrent
- Preventive
-
Tony is developing a business continuity plan and is having difficulty prioritizing resources because of the difficulty of combining information about tangible and intangible assets. What would be the most effective risk assessment approach for him to use?
- Quantitative risk assessment
- Qualitative risk assessment
- Neither quantitative nor qualitative risk assessment
- Combination of quantitative and qualitative risk assessment
-
What law provides intellectual property protection to the holders of trade secrets?
- Copyright Law
- Lanham Act
- Glass-Steagall Act
- Economic Espionage Act
-
Which one of the following principles imposes a standard of care upon an individual that is broad and equivalent to what one would expect from a reasonable person under the circumstances?
- Due diligence
- Separation of duties
- Due care
- Least privilege
-
Darcy is designing a fault tolerant system and wants to implement RAID-5 for her system. What is the minimum number of physical hard disks she can use to build this system?
- One
- Two
- Three
- Five
-
Which one of the following is an example of an administrative control?
- Intrusion detection system
- Security awareness training
- Firewalls
- Security guards
-
Keenan Systems recently developed a new manufacturing process for microprocessors. The company wants to license the technology to other companies for use but wishes to prevent unauthorized use of the technology. What type of intellectual property protection is best suited for this situation?
- Patent
- Trade secret
- Copyright
- Trademark
-
Which one of the following actions might be taken as part of a business continuity plan?
- Restoring from backup tapes
- Implementing RAID
- Relocating to a cold site
- Restarting business operations
-
When developing a business impact analysis, the team should first create a list of assets. What should happen next?
- Identify vulnerabilities in each asset.
- Determine the risks facing the asset.
- Develop a value for each asset.
- Identify threats facing each asset.
-
Mike recently implemented an intrusion prevention system designed to block common network attacks from affecting his organization. What type of risk management strategy is Mike pursuing?
- Risk acceptance
- Risk avoidance
- Risk mitigation
- Risk transference
-
Which one of the following is an example of physical infrastructure hardening?
- Antivirus software
- Hardware-based network firewall
- Two-factor authentication
- Fire suppression system
-
Which one of the following is normally used as an authorization tool?
- ACL
- Token
- Username
- Password
-
The International Information Systems Security Certification Consortium uses the logo below to represent itself online and in a variety of forums. What type of intellectual property protection may it use to protect its rights in this logo?

- Copyright
- Patent
- Trade secret
- Trademark
-
Mary is helping a computer user who sees the following message appear on his computer screen. What type of attack has occurred?

- Availability
- Confidentiality
- Disclosure
- Distributed
-
Which one of the following organizations would not be automatically subject to the terms of HIPAA if they engage in electronic transactions?
- Healthcare provider
- Health and fitness application developer
- Health information clearinghouse
- Health insurance plan
-
John’s network begins to experience symptoms of slowness. Upon investigation, he realizes that the network is being bombarded with ICMP ECHO REPLY packets and believes that his organization is the victim of a Smurf attack. What principle of information security is being violated?
- Availability
- Integrity
- Confidentiality
- Denial
-
Renee is designing the long-term security plan for her organization and has a three- to five-year planning horizon. What type of plan is she developing?
- Operational
- Tactical
- Summary
- Strategic
-
What government agency is responsible for the evaluation and registration of trademarks?
- USPTO
- Library of Congress
- TVA
- NIST
-
The Acme Widgets Company is putting new controls in place for its accounting department. Management is concerned that a rogue accountant may be able to create a new false vendor and then issue checks to that vendor as payment for services that were never rendered. What security control can best help prevent this situation?
- Mandatory vacation
- Separation of duties
- Defense in depth
- Job rotation
-
Which one of the following categories of organizations is most likely to be covered by the provisions of FISMA?
- Banks
- Defense contractors
- School districts
- Hospitals
-
Robert is responsible for securing systems used to process credit card information. What standard should guide his actions?
- HIPAA
- PCI DSS
- SOX
- GLBA
-
Which one of the following individuals is normally responsible for fulfilling the operational data protection responsibilities delegated by senior management, such as validating data integrity, testing backups, and managing security policies?
- Data custodian
- Data owner
- User
- Auditor
-
Alan works for an e-commerce company that recently had some content stolen by another website and republished without permission. What type of intellectual property protection would best preserve Alan’s company’s rights?
- Trade secret
- Copyright
- Trademark
- Patent
-
Florian receives a flyer from a federal agency announcing that a new administrative law will affect his business operations. Where should he go to find the text of the law?
- United States Code
- Supreme Court rulings
- Code of Federal Regulations
- Compendium of Laws
-
Tom is installing a next-generation firewall (NGFW) in his data center that is designed to block many types of application attacks. When viewed from a risk management perspective, what metric is Tom attempting to lower?
- Impact
- RPO
- MTO
- Likelihood
-
Which one of the following individuals would be the most effective organizational owner for an information security program?
- CISSP-certified analyst
- Chief information officer
- Manager of network security
- President and CEO
-
What important function do senior managers normally fill on a business continuity planning team?
- Arbitrating disputes about criticality
- Evaluating the legal environment
- Training staff
- Designing failure controls
-
You are the CISO for a major hospital system and are preparing to sign a contract with a Software-as-a-Service (SaaS) email vendor and want to ensure that its business continuity planning measures are reasonable. What type of audit might you request to meet this goal?
- SOC-1
- FISMA
- PCI DSS
- SOC-2
-
Gary is analyzing a security incident and, during his investigation, encounters a user who denies having performed an action that Gary believes he did perform. What type of threat has taken place under the STRIDE model?
- Repudiation
- Information disclosure
- Tampering
- Elevation of privilege
-
Beth is the security administrator for a public school district. She is implementing a new student information system and is testing the code to ensure that students are not able to alter their own grades. What principle of information security is Beth enforcing?
- Integrity
- Availability
- Confidentiality
- Denial
-
Which one of the following issues is not normally addressed in a service-level agreement (SLA)?
- Confidentiality of customer information
- Failover time
- Uptime
- Maximum consecutive downtime
-
Joan is seeking to protect a piece of computer software that she developed under intellectual property law. Which one of the following avenues of protection would not apply to a piece of software?
- Trademark
- Copyright
- Patent
- Trade secret
Questions 47–49 refer to the following scenario.
Juniper Content is a web content development company with 40 employees located in two offices: one in New York and a smaller office in the San Francisco Bay Area. Each office has a local area network protected by a perimeter firewall. The LAN contains modern switch equipment connected to both wired and wireless networks.
Each office has its own file server, and the IT team runs software every hour to synchronize files between the two servers, distributing content between the offices. These servers are primarily used to store images and other files related to web content developed by the company. The team also uses a SaaS-based email and document collaboration solution for much of their work.
You are the newly appointed IT manager for Juniper Content and you are working to augment existing security controls to improve the organization’s security.
-
Users in the two offices would like to access each other’s file servers over the Internet. What control would provide confidentiality for those communications?
- Digital signatures
- Virtual private network
- Virtual LAN
- Digital content management
-
You are also concerned about the availability of data stored on each office’s server. You would like to add technology that would enable continued access to files located on the server even if a hard drive in a server fails. What integrity control allows you to add robustness without adding additional servers?
- Server clustering
- Load balancing
- RAID
- Scheduled backups
-
Finally, there are historical records stored on the server that are extremely important to the business and should never be modified. You would like to add an integrity control that allows you to verify on a periodic basis that the files were not modified. What control can you add?
- Hashing
- ACLs
- Read-only attributes
- Firewalls
-
What law serves as the basis for privacy rights in the United States?
- Privacy Act of 1974
- Fourth Amendment
- First Amendment
- Electronic Communications Privacy Act of 1986
-
Which one of the following is not normally included in business continuity plan documentation?
- Statement of accounts
- Statement of importance
- Statement of priorities
- Statement of organizational responsibility
-
An accounting employee at Doolitte Industries was recently arrested for participation in an embezzlement scheme. The employee transferred money to a personal account and then shifted funds around between other accounts every day to disguise the fraud for months. Which one of the following controls might have best allowed the earlier detection of this fraud?
- Separation of duties
- Least privilege
- Defense in depth
- Mandatory vacation
-
Which one of the following is not normally considered a business continuity task?
- Business impact assessment
- Emergency response guidelines
- Electronic vaulting
- Vital records program
-
Which information security goal is impacted when an organization experiences a DoS or DDoS attack?
- Confidentiality
- Integrity
- Availability
- Denial
-
Yolanda is writing a document that will provide configuration information regarding the minimum level of security that every system in the organization must meet. What type of document is she preparing?
- Policy
- Baseline
- Guideline
- Procedure
-
Who should receive initial business continuity plan training in an organization?
- Senior executives
- Those with specific business continuity roles
- Everyone in the organization
- First responders
-
James is conducting a risk assessment for his organization and is attempting to assign an asset value to the servers in his data center. The organization’s primary concern is ensuring that it has sufficient funds available to rebuild the data center in the event it is damaged or destroyed. Which one of the following asset valuation methods would be most appropriate in this situation?
- Purchase cost
- Depreciated cost
- Replacement cost
- Opportunity cost
-
The Computer Security Act of 1987 gave a federal agency responsibility for developing computer security standards and guidelines for federal computer systems. What agency did the act give this responsibility to?
- National Security Agency
- Federal Communications Commission
- Department of Defense
- National Institute of Standards and Technology
-
Which one of the following is not a requirement for an invention to be patentable?
- It must be new.
- It must be invented by an American citizen.
- It must be nonobvious.
- It must be useful.
-
Frank discovers a keylogger hidden on the laptop of his company’s chief executive officer. What information security principle is the keylogger most likely designed to disrupt?
- Confidentiality
- Integrity
- Availability
- Denial
-
What is the formula used to determine risk?
- Risk = Threat * Vulnerability
- Risk = Threat / Vulnerability
- Risk = Asset * Threat
- Risk = Asset / Threat
-
The graphic below shows the NIST risk management framework with step 4 missing. What is the missing step?
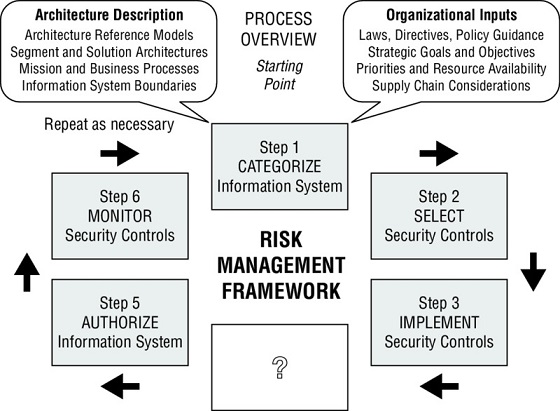
- Assess security controls
- Determine control gaps
- Remediate control gaps
- Evaluate user activity
-
HAL Systems recently decided to stop offering public NTP services because of a fear that its NTP servers would be used in amplification DDoS attacks. What type of risk management strategy did HAL pursue with respect to its NTP services?
- Risk mitigation
- Risk acceptance
- Risk transference
- Risk avoidance
-
Susan is working with the management team in her company to classify data in an attempt to apply extra security controls that will limit the likelihood of a data breach. What principle of information security is Susan trying to enforce?
- Availability
- Denial
- Confidentiality
- Integrity
-
Which one of the following components should be included in an organization’s emergency response guidelines?
- List of individuals who should be notified of an emergency incident
- Long-term business continuity protocols
- Activation procedures for the organization’s cold sites
- Contact information for ordering equipment
-
Who is the ideal person to approve an organization’s business continuity plan?
- Chief information officer
- Chief executive officer
- Chief information security officer
- Chief operating officer
-
Which one of the following actions is not normally part of the project scope and planning phase of business continuity planning?
- Structured analysis of the organization
- Review of the legal and regulatory landscape
- Creation of a BCP team
- Documentation of the plan
-
Gary is implementing a new RAID-based disk system designed to keep a server up and running even in the event of a single disk failure. What principle of information security is Gary seeking to enforce?
- Denial
- Confidentiality
- Integrity
- Availability
-
Becka recently signed a contract with an alternate data processing facility that will provide her company with space in the event of a disaster. The facility includes HVAC, power, and communications circuits but no hardware. What type of facility is Becka using?
- Cold site
- Warm site
- Hot site
- Mobile site
-
What is the threshold for malicious damage to a federal computer system that triggers the Computer Fraud and Abuse Act?
- $500
- $2,500
- $5,000
- $10,000
-
Ben is seeking a control objective framework that is widely accepted around the world and focuses specifically on information security controls. Which one of the following frameworks would best meet his needs?
- ITIL
- ISO 27002
- CMM
- PMBOK Guide
-
Which one of the following laws requires that communications service providers cooperate with law enforcement requests?
- ECPA
- CALEA
- Privacy Act
- HITECH Act
-
Every year, Gary receives privacy notices in the mail from financial institutions where he has accounts. What law requires the institutions to send Gary these notices?
- FERPA
- GLBA
- HIPAA
- HITECH
-
Which one of the following agreements typically requires that a vendor not disclose confidential information learned during the scope of an engagement?
- NCA
- SLA
- NDA
- RTO
-
Which one of the following is not an example of a technical control?
- Router ACL
- Firewall rule
- Encryption
- Data classification
-
Which one of the following stakeholders is not typically included on a business continuity planning team?
- Core business function leaders
- Information technology staff
- CEO
- Support departments
-
Ben is designing a messaging system for a bank and would like to include a feature that allows the recipient of a message to prove to a third party that the message did indeed come from the purported originator. What goal is Ben trying to achieve?
- Authentication
- Authorization
- Integrity
- Nonrepudiation
-
What principle of information security states that an organization should implement overlapping security controls whenever possible?
- Least privilege
- Separation of duties
- Defense in depth
- Security through obscurity
-
Which one of the following is not a goal of a formal change management program?
- Implement change in an orderly fashion.
- Test changes prior to implementation.
- Provide rollback plans for changes.
- Inform stakeholders of changes after they occur.
-
Ben is responsible for the security of payment card information stored in a database. Policy directs that he remove the information from the database, but he cannot do this for operational reasons. He obtained an exception to policy and is seeking an appropriate compensating control to mitigate the risk. What would be his best option?
- Purchasing insurance
- Encrypting the database contents
- Removing the data
- Objecting to the exception
-
The Domer Industries risk assessment team recently conducted a qualitative risk assessment and developed a matrix similar to the one shown below. Which quadrant contains the risks that require the most immediate attention?
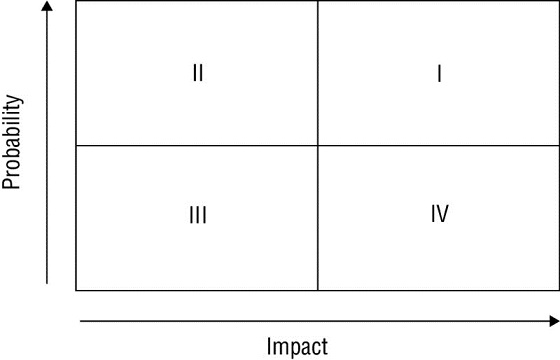
- I
- II
- III
- IV
-
Tom is planning to terminate an employee this afternoon for fraud and expects that the meeting will be somewhat hostile. He is coordinating the meeting with Human Resources and wants to protect the company against damage. Which one of the following steps is most important to coordinate in time with the termination meeting?
- Informing other employees of the termination
- Retrieval of photo ID
- Calculation of final paycheck
- Revocation of electronic access rights
-
Rolando is a risk manager with a large-scale enterprise. The firm recently evaluated the risk of California mudslides on its operations in the region and determined that the cost of responding outweighed the benefits of any controls it could implement. The company chose to take no action at this time. What risk management strategy did Rolando’s organization pursue?
- Risk avoidance
- Risk mitigation
- Risk transference
- Risk acceptance
-
Helen is the owner of a website that provides information for middle and high school students preparing for exams. She is concerned that the activities of her site may fall under the jurisdiction of the Children’s Online Privacy Protection Act (COPPA). What is the cutoff age below which parents must give consent in advance of the collection of personal information from their children under COPPA?
- 13
- 15
- 17
- 18
-
Tom is considering locating a business in the downtown area of Miami, Florida. He consults the FEMA flood plain map for the region, shown below, and determines that the area he is considering lies within a 100-year flood plain.
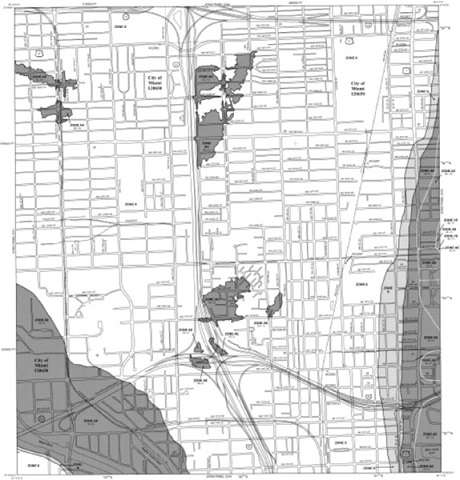
What is the ARO of a flood in this area?
- 100
- 1
- 0.1
- 0.01
-
You discover that a user on your network has been using the Wireshark tool, as shown in the following screen shot. Further investigation revealed that he was using it for illicit purposes. What pillar of information security has most likely been violated?
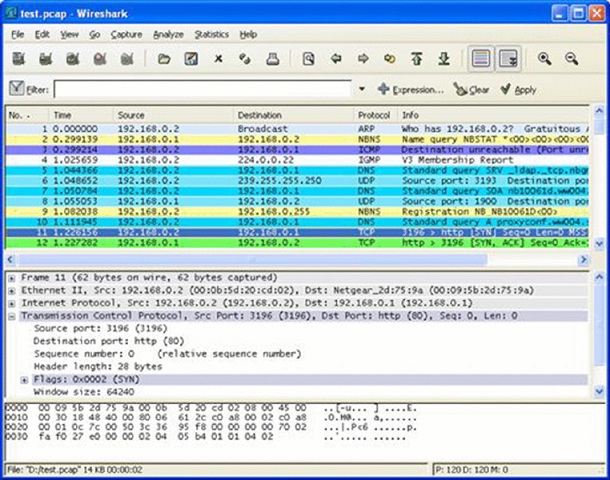
- Integrity
- Denial
- Availability
- Confidentiality
-
Alan is performing threat modeling and decides that it would be useful to decompose the system into the key elements shown in the following illustration. What tool is he using?
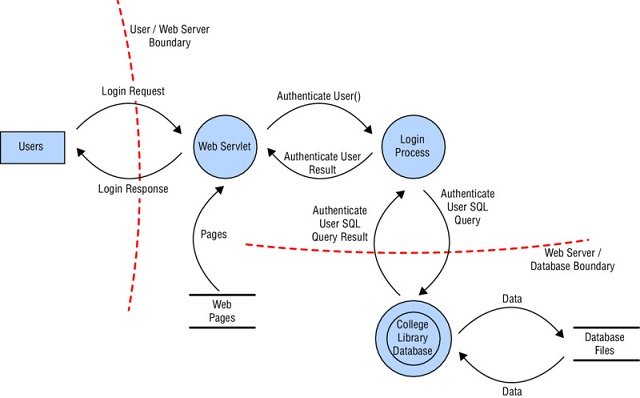
Image reprinted from CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide, 7th Edition © John Wiley & Sons 2015, reprinted with permission.
- Vulnerability assessment
- Fuzzing
- Reduction analsis
- Data modeling
-
What law governs the handling of information related to the financial statements of publicly traded companies?
- GLBA
- PCI DSS
- HIPAA
- SOX
-
Craig is selecting the site for a new data center and must choose a location somewhere within the United States. He obtained the earthquake risk map below from the United States Geological Survey. Which of the following would be the safest location to build his facility if he were primarily concerned with earthquake risk?
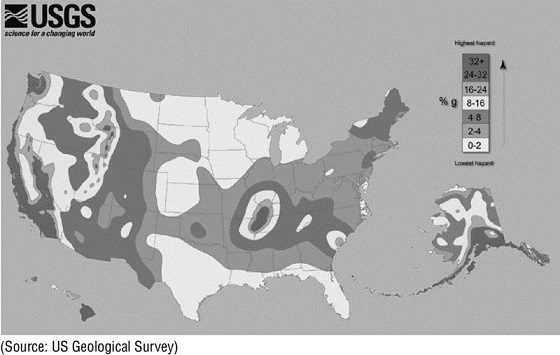
Image reprinted from CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide, 7th Edition © John Wiley & Sons 2015, reprinted with permission.
- New York
- North Carolina
- Indiana
- Florida
-
Which one of the following tools is most often used for identification purposes and is not suitable for use as an authenticator?
- Password
- Retinal scan
- Username
- Token
-
Which type of business impact assessment tool is most appropriate when attempting to evaluate the impact of a failure on customer confidence?
- Quantitative
- Qualitative
- Annualized loss expectancy
- Reduction
-
Which one of the following is the first step in developing an organization’s vital records program?
- Identifying vital records
- Locating vital records
- Archiving vital records
- Preserving vital records
-
Which one of the following security programs is designed to provide employees with the knowledge they need to perform their specific work tasks?
- Awareness
- Training
- Education
- Indoctrination
-
Which one of the following security programs is designed to establish a minimum standard common denominator of security understanding?
- Training
- Education
- Indoctrination
- Awareness
-
Ryan is a security risk analyst for an insurance company. He is currently examining a scenario in which a hacker might use a SQL injection attack to deface a web server due to a missing patch in the company’s web application. In this scenario, what is the threat?
- Unpatched web application
- Web defacement
- Hacker
- Operating system
Questions 96–98 refer to the following scenario.
Henry is the risk manager for Atwood Landing, a resort community in the midwestern United States. The resort’s main data center is located in northern Indiana in an area that is prone to tornados. Henry recently undertook a replacement cost analysis and determined that rebuilding and reconfiguring the data center would cost $10 million.
Henry consulted with tornado experts, data center specialists, and structural engineers. Together, they determined that a typical tornado would cause approximately $5 million of damage to the facility. The meteorologists determined that Atwood’s facility lies in an area where they are likely to experience a tornado once every 200 years.
-
Based upon the information in this scenario, what is the exposure factor for the effect of a tornado on Atwood Landing’s data center?
- 10%
- 25%
- 50%
- 75%
-
Based upon the information in this scenario, what is the annualized rate of occurrence for a tornado at Atwood Landing’s data center?
- 0.0025
- 0.005
- 0.01
- 0.015
-
Based upon the information in this scenario, what is the annualized loss expectancy for a tornado at Atwood Landing’s data center?
- $25,000
- $50,000
- $250,000
- $500,000
-
John is analyzing an attack against his company in which the attacker found comments embedded in HTML code that provided the clues needed to exploit a software vulnerability. Using the STRIDE model, what type of attack did he uncover?
- Spoofing
- Repudiation
- Information disclosure
- Elevation of privilege
-
Which one of the following is an administrative control that can protect the confidentiality of information?
- Encryption
- Non-disclosure agreement
- Firewall
- Fault tolerance
