- Cover Page
- Title Page
- Copyright Page
- About the Author
- About the Technical Reviewer
- Dedication
- Acknowledgments
- Contents at a Glance
- Contents
- Reader Services
- Icons Used in This Book
- Command Syntax Conventions
- Introduction
- Part I Troubleshooting and Administration of Hardware Platform
- Chapter 1 Introduction to the Cisco Firepower Technology
- Chapter 2 FTD on ASA 5500-X Series Hardware
- Chapter 3 FTD on the Firepower eXtensible Operating System (FXOS)
- Chapter 4 Firepower Management Center (FMC) Hardware
- Chapter 5 Firepower System Virtual on VMware
- Part II Troubleshooting and Administration of Initial Deployment
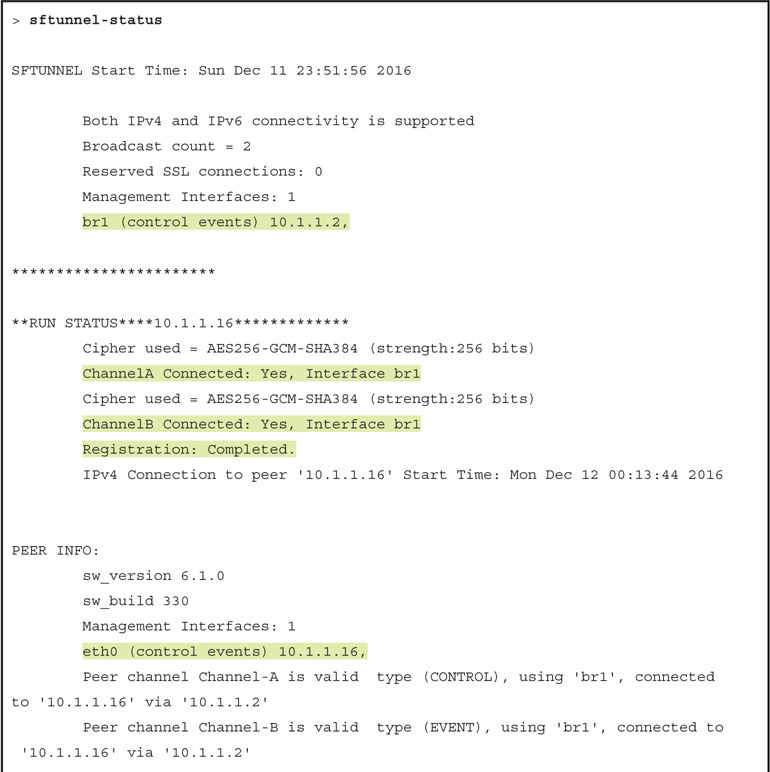
- Chapter 6 The Firepower Management Network
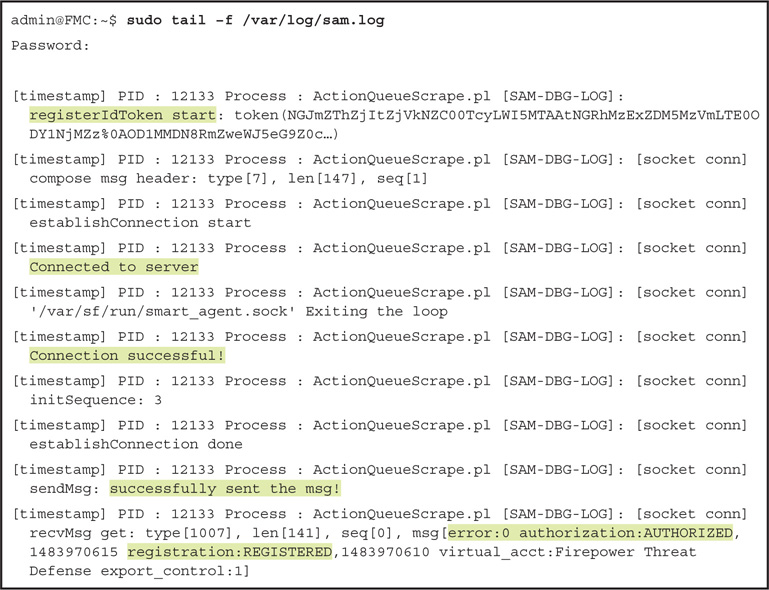
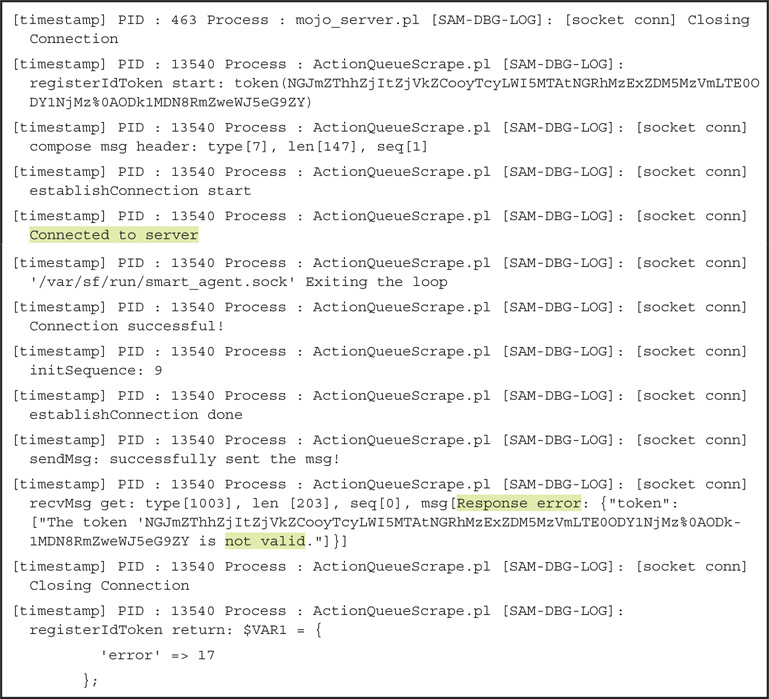
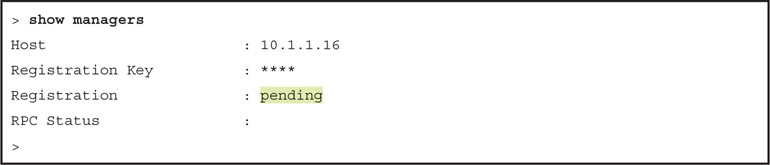
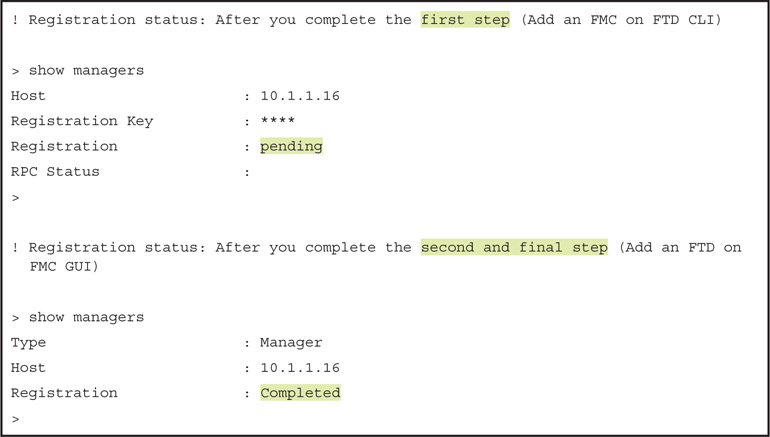
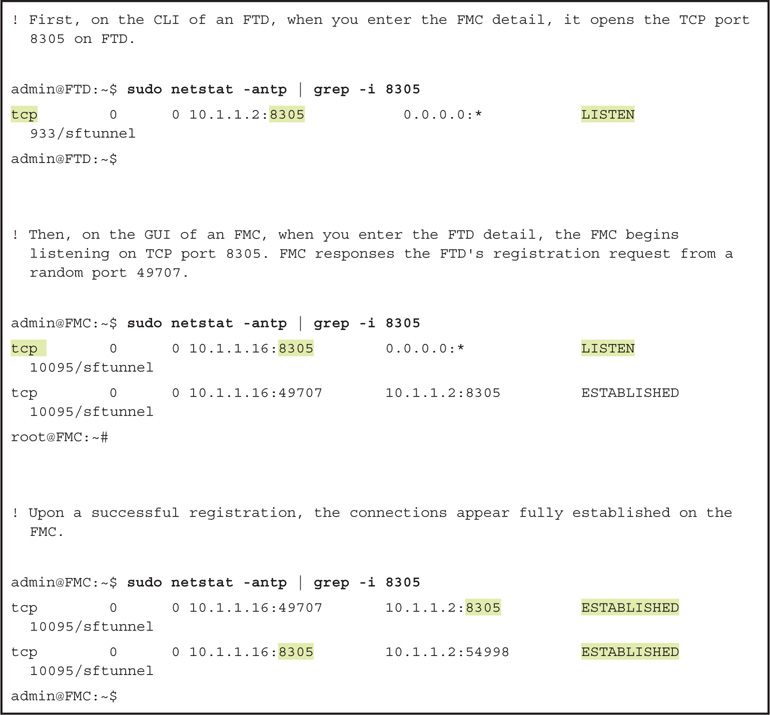
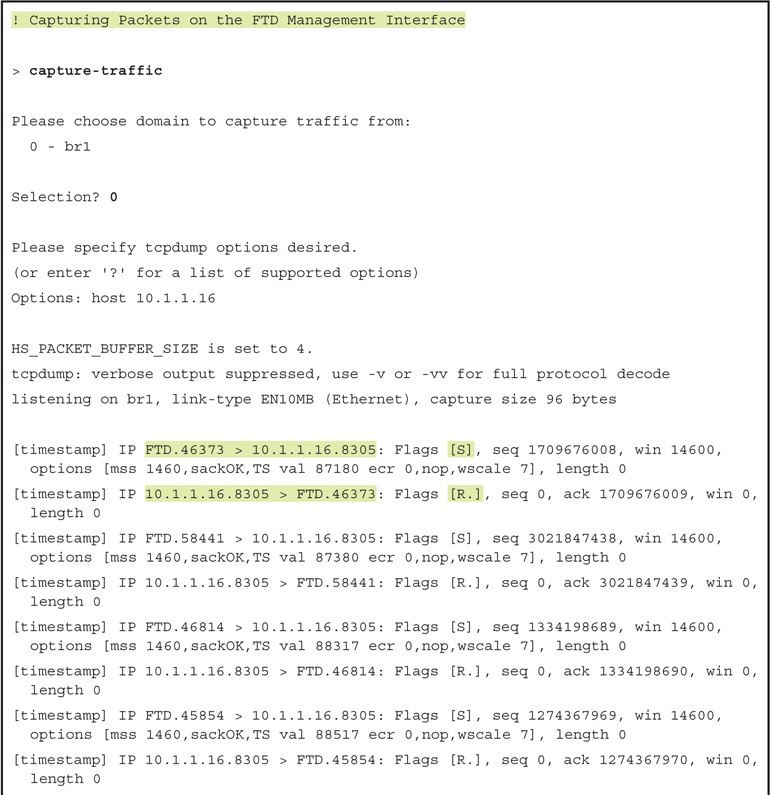
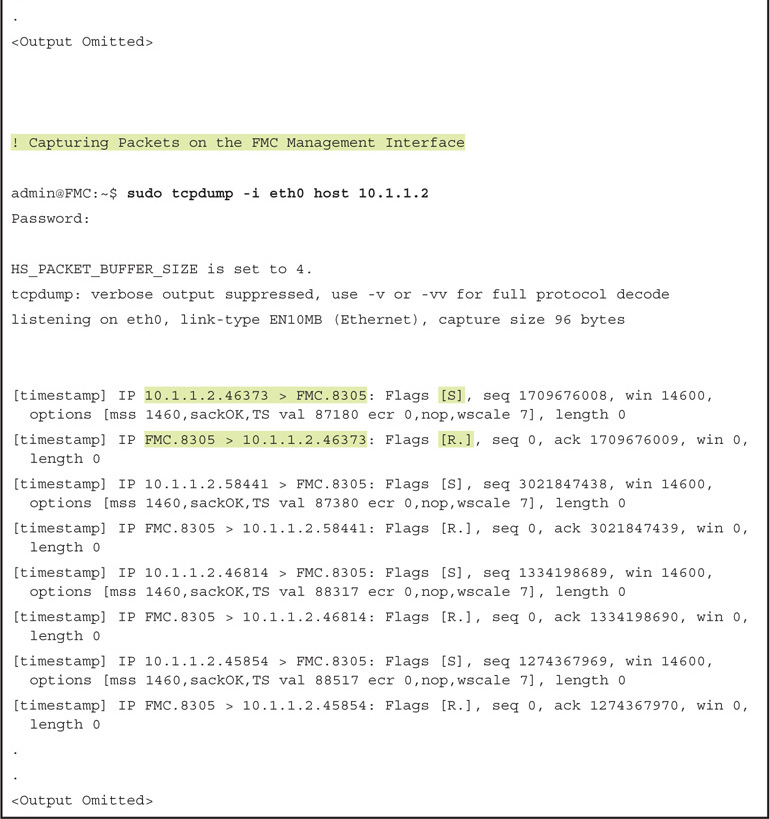
- Chapter 7 Firepower Licensing and Registration
- Chapter 8 Firepower Deployment in Routed Mode
- Chapter 9 Firepower Deployment in Transparent Mode
- Transparent Mode Essentials
- Best Practices for Transparent Mode
- Configuring Transparent Mode
- Fulfilling Prerequisites
- Changing the Firewall Mode
- Deploying Transparent Mode in a Layer 2 Network
- Configuring the Physical and Virtual Interfaces
- Verifying the Interface Status
- Verifying Basic Connectivity and Operations
- Deploying an FTD Device Between Layer 3 Networks
- Selecting the Default Action
- Adding an Access Rule
- Creating an Access Rule for SSH
- Verifying Access Control Lists
- Summary
- Quiz
- Part III Troubleshooting and Administration of Traffic Control
- Chapter 10 Capturing Traffic for Advanced Analysis
- Traffic Capture Essentials
- Best Practices for Capturing Traffic
- Configuring Firepower System for Traffic Analysis
- Capturing Traffic from a Firepower Engine
- tcpdump Options
- Downloading a .pcap File Generated by Firepower Engine
- Capturing Traffic from the Firewall Engine
- Downloading a .pcap File Generated by Firewall Engine
- Enabling HTTP Service in FTD
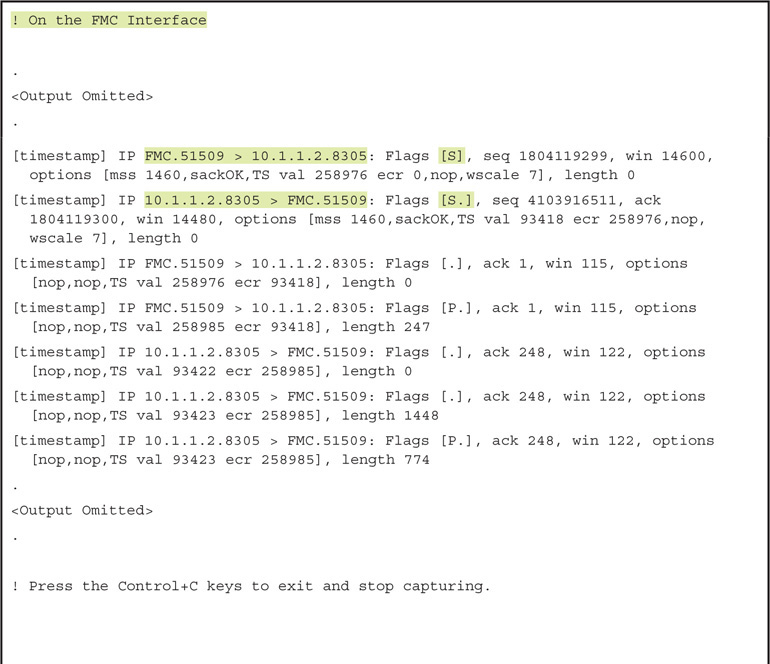
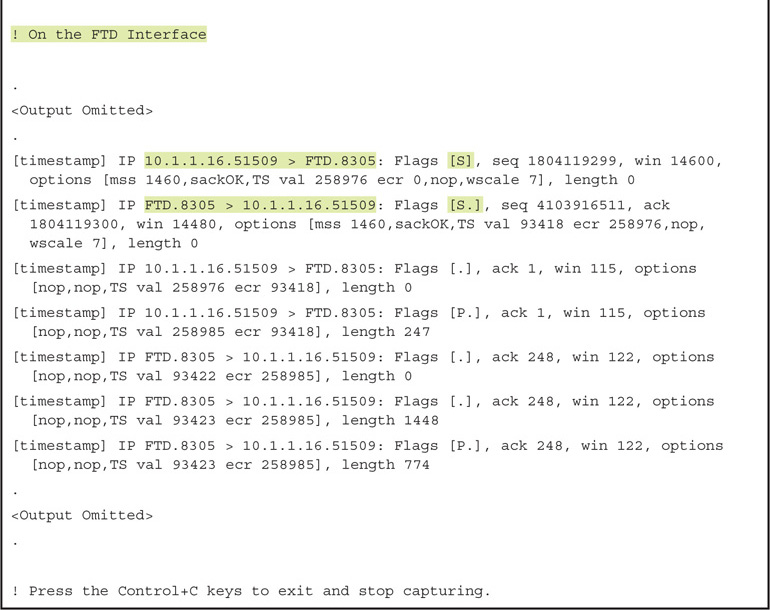
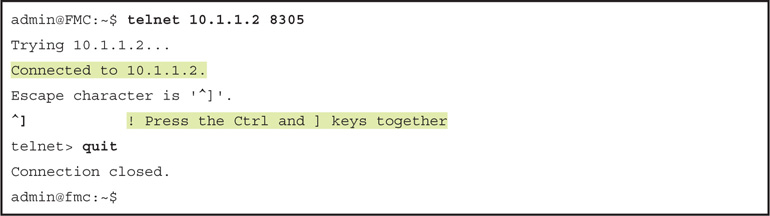
- Capturing Traffic from the FMC
- Downloading a .pcap File Generated by FMC
- Verification and Troubleshooting Tools
- Summary
- Quiz
- Chapter 11 Blocking Traffic Using Inline Interface Mode
- Inline Mode Essentials
- Best Practices for Inline Mode Configuration
- Configuring Inline Mode
- Fulfilling Prerequisites
- Creating an Inline Set
- Verifying the Configuration
- Verifying Packet Flow by Using packet-tracer
- Verifying Packet Flow by Using Real Packet Capture
- Enabling Fault Tolerance Features
- Configuring Fault Tolerance Features
- Verifying Fault Tolerance Features
- Blocking a Specific Port
- Configuring Blocking a Specific Port
- Verifying Blocking of a Specific Port
- Analyzing a Packet Drop by Using a Simulated Packet
- Analyzing a Packet Drop by Using a Real Packet
- Summary
- Quiz
- Chapter 12 Inspecting Traffic Without Blocking It
- Chapter 13 Handling Encapsulated Traffic
- Chapter 14 Bypassing Inspection and Trusting Traffic
- Chapter 15 Rate Limiting Traffic
- Chapter 10 Capturing Traffic for Advanced Analysis
- Part IV Troubleshooting and Administration of Next-Generation Security Features
- Chapter 16 Blacklisting Suspicious Addresses by Using Security Intelligence
- Security Intelligence Essentials
- Best Practices for Blacklisting
- Fulfilling Prerequisites
- Configuring Blacklisting
- Automatic Blacklist Using Cisco Intelligence Feed
- Manual Blacklisting Using a Custom Intelligence List
- Immediate Blacklisting Using a Connection Event
- Adding an Address to a Blacklist
- Deleting an Address from a Blacklist
- Monitoring a Blacklist
- Bypassing a Blacklist
- Adding an Address to a Whitelist
- Deleting an Address from a Whitelist
- Verification and Troubleshooting Tools
- Summary
- Quiz
- Chapter 17 Blocking a Domain Name System (DNS) Query
- Chapter 18 Filtering URLs Based on Category, Risk, and Reputation
- Chapter 19 Discovering Network Applications and Controlling Application Traffic
- Chapter 20 Controlling File Transfer and Blocking the Spread of Malware
- Chapter 21 Preventing Cyber Attacks by Blocking Intrusion Attempts
- Firepower NGIPS Essentials
- Best Practices for Intrusion Policy Deployment
- NGIPS Configuration
- Configuring a Network Analysis Policy
- Creating a New NAP with Default Settings
- Modifying the Default Settings of a NAP
- Configuring an Intrusion Policy
- Creating a Policy with a Default Ruleset
- Incorporating Firepower Recommendations
- Enabling or Disabling an Intrusion Rule
- Setting Up a Variable Set
- Configuring an Access Control Policy
- Verification and Troubleshooting Tools
- Summary
- Quiz
- Chapter 22 Masquerading the Original IP Address of an Internal Network Host
- NAT Essentials
- Best Practices for NAT Deployment
- Fulfilling Prerequisites
- Configuring NAT
- Masquerading a Source Address (Source NAT for Outbound Connection)
- Configuring a Dynamic NAT Rule
- Verifying the Configuration
- Verifying the Operation: Inside to Outside
- Verifying the Operation: Outside to Inside
- Connecting to a Masqueraded Destination (Destination NAT for Inbound Connection)
- Configuring a Static NAT Rule
- Verifying the Operation: Outside to DMZ
- Summary
- Quiz
- Chapter 16 Blacklisting Suspicious Addresses by Using Security Intelligence
- Appendix A Answers to the Review Questions
- Appendix B Generating and Collecting Troubleshooting Files Using the GUI
- Appendix C Generating and Collecting Troubleshooting Files Using the CLI
- Index
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.