Though you may be eager to grab a laptop, install Kali on it, and jump right into running the tools, you'd be best served to spend some time researching and validating the devices you plan to use. It can be very frustrating to begin working through the tutorials and exercises in this book only to be thwarted by hardware that is not working right or doesn't support all of the features required to complete your assessment. This section will discuss wireless adapters, antennas, and other considerations that provide you the best chance of success.
In this book, we will extensively make use of the advanced features of the wireless client that are not supported on all adapters. Two of these features, monitor and master modes, will help us capture the traffic and set up virtual access points, respectively. In the monitor mode, you are able to put your wireless adapter in a promiscuous (or listening) mode, which is capable of capturing the wireless frames from the air, while the master mode is essential for the setting up of an evil twin attack. These two modes are just some of the several supported modes in various wireless adapters, and the following are the commonly available modes and they explain what they are used for:
- The managed mode: This is the default mode for most wireless connections. In this mode, the wireless adapter is only capable of receiving packets from SSIDs that it is associated with. For instance, if the adapter is associated with a "packt" SSID, then it filters out packets from the other SSIDs. This is the common operating mode for clients who are actively associated with an access point and assigned an IP address and who carry on regular communications with their intended wireless network.
- The ad-hoc mode: This mode is rarely used since the majority of wireless networks participate in infrastructure mode and host clients directly. This mode is used only when an access point is not in place and clients are participating in a peer-to-peer mesh. The lack of an access point usually restricts the functionality and usefulness of the connecting clients and hence is rarely used in modern deployments.
- The master mode: This mode allows us to configure our wireless client as a base station or a wireless access point. In most production networks, clients are clients and access points are access points. This seems funny to say, but as a penetration tester, it is common for us to want to emulate an access point where we control the configuration and, more importantly, have visibility about all of the traffic traversing the wireless device. This mode is required if you intend to set up a virtual access point as part of your assessment.
- The monitor mode: The support for this mode is essential if you want to be able to capture all the traffic on the wireless spectrum. With the monitor mode, the wireless adapter is placed into a passive state, where it does not attempt to interact with any of the wireless devices around it. Instead, it enables us to sniff and capture the traffic for analysis, cracking, or decryption.
As mentioned, not all devices support all four of the preceding modes, notably missing either the monitor mode or the master mode. These two modes are important to many of the provided examples, and it might not be immediately clear that your chosen adapter does not support them. Next, we will discuss adapters that have been known to be successful in penetration tests, specifically with Kali Linux.
The first thing you'll look for when selecting a wireless adapter is the chipset used in the adapter. Many adapters may have different vendors and names printed on the outside of the device but use the same chipsets underneath the plastic where it really matters. The chipsets that have been known to be compatible are discussed in the upcoming sections.
This chipset is used in many different USB wireless adapters that are available in different form factors.
The following are examples of several common adapters at the time of writing this book. There are hundred more adapters that also use this chipset, which comes in a variety of sizes and hardware configurations.
This model is ALFA AWUS036NH (image courtesy: http://www.alfa.com.tw)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.11 b/g/n |
|
Band |
2.4 GHz |
|
Speed |
150 Mbps |
|
Gain |
2000 mW |
This model is ALFA AWUS036NEH (image courtesy: http://www.alfa.com.tw)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.11 b/g/n |
|
Band |
2.4 GHz |
|
Speed |
150 Mbps |
|
Gain |
1000 mW |
This model is Tenda UH151 (image courtesy: http://www.tendacn.com)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.11 b/g/n |
|
Band |
2.4 GHz |
|
Speed |
150 Mbps |
Similar to the RT3070, this chipset also supports 2.4 GHz and is used by several vendors, including ALFA, TP-LINK, D-Link, and others. You will find these adapters regularly recommended by pentesters on Kali and aircrack-ng forums. Here are a few adapters shown along with their specifications.
This model is ALFA AWUS036NHA (image courtesy: http://www.alfa.com.tw)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.11 b/g/n |
|
Band |
2.4 GHz |
|
Speed |
150 Mbps |
This model is ALFA AWUS036NH (image courtesy: http://www.alfa.com.tw)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.1 b/g/n |
|
Band |
2.4 GHz |
|
Speed |
150 Mbps |
|
Gain |
2000 mW |
This is the newer Ralink chipset, that has been found to be very compatible with Kali Linux, and it supports the modes that we are interested in. This chipset is capable of both 2.4 GHz and 5.0 GHz, making it very attractive for pentesters. A common example that uses this chipset is as follows:
This model is ALFA AWUS051NH (image courtesy: http://www.alfa.com.tw)

|
Interface Type |
USB 2.0 |
|
Supported Protocols |
802.11 a/b/g/n |
|
Band |
2.4 GHz and 5 GHz |
|
Speed |
150 Mbps |
|
Gain |
500 mW |
You will notice that all of the wireless adapters that we recommend in this section have several things in common. First, they all utilize a USB connection rather than being embedded in the device. This is advantageous for a number of reasons. Embedded wireless devices, such as those that ship with your laptop, may have limited advanced functionality support due to driver and firmware limitations. Most pentesters will also use USB devices because of their portability. The USB wireless adapter can easily be disconnected from your primary penetration testing device and be moved to an alternate platform. We will be covering some of these platforms in the last chapter of the book. USB devices can also be easily mapped through to a virtual machine running on top of their existing operating system. This will be demonstrated later, when we cover the installation of Kali Linux on a VM running in Virtual Box.
Another common trait of these adapters is that they all support an external antenna connected to their radio. On the ALFA USB adapters, the antenna is connected via an RP-SMA, or a Reverse Polarity SubMinature Version A screw-on connection. This is a very common connection for antennas, and it allows you to select an antenna to fit the situation and environment where you are operating. The antenna types vary in their construction and design to optimize either the gain or focus their radio signals in a particular direction, increasing the distance in which they can transmit and receive. The next section will cover several antenna types and detail when each could be used during your wireless assessment.
Having the ability to replace the antenna on your wireless adapter, while penetration testing provides you some flexibility on how you conduct your wireless assessment. When testing the target environment, you must be within the RF range of the target network in order to do the majority of your testing. This limits how far away you can be from the physical location where the wireless is being utilized and, sometimes, your ability to be inconspicuous while conducting the testing. Increasing the gain and focusing the power of your wireless adapter may allow you to set up camp in a place that is a little more covert while still being able to see the target network. In this section, we will look at three common antenna choices that can be affixed to the wireless adapters mentioned earlier. Each has their own unique advantages and drawbacks.
Omnidirectional antenna, as the name implies, sends and receives wireless traffic in all directions around the circumference of the antenna. The amount of gain provided by these antennas varies between 5 dBi and 14 dBi. This is a great general-purpose antenna and will typically ship with an adapter that allows an external antenna. These antennas can be designed for 2.4 GHz, 5.0 GHz, or both, so ensure what band you will be utilizing and select the antenna that supports it.

Patch antennas allow you to focus the signal of your wireless interface in a particular direction that can improve the accuracy and range of the transmission over a long distance. The radiation pattern of the antenna only extends from one face of the patch antenna and typically has gains in the 7 dBi to 10 dBi range. This antenna will be beneficial if all of the devices you were testing or capturing from were located in the same direction from your testing location.

Image courtesy: http://www.alfa.com.tw
Yagi antennas are highly directional antennas, similar to patch antennas. They tend to be capable of even higher gains than the other two discussed antenna types since their radiation pattern is very focused in a particular direction. It is common to find these types of antennas with 18 dBi or higher gains, which allow you to be further away from the target wireless network you are testing if your directional aim with the antenna is true.
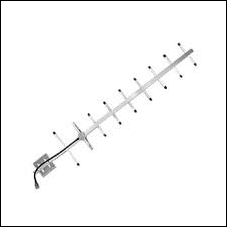
Image courtesy: http://www.alfa.com.tw