- Copyright
- Preface
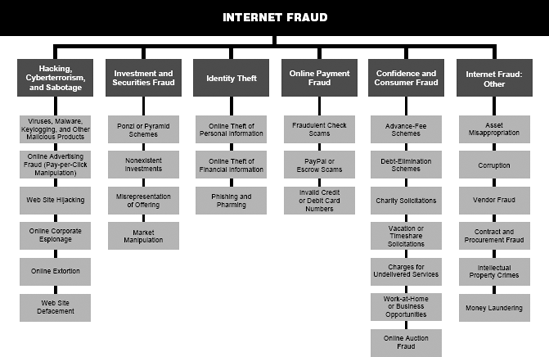
- Internet Fraud Tree
- 1. Phantom Figurines
- 2. From Russia With Love?
- 3. Behind a Smoke Screen
- 4. Cars, Cards, Chemicals And Crayons
- 5. Small-Town Boys
- 6. Dangerous Diet
- 7. The Suburban Spoofer
- 8. Don'T Mess With Texas
- 9. Hot Wire
- 10. A Business Within A Business
- 11. Double Play
- 12. The eBay-Fraud Brothers
- 13. Not-So-Precious Metals
- 14. The Cool-Cash Syndicate
- 15. Dastardly Design
- 16. The Reckless Clerk
- 17. Close Quarters
- 18. Playing With Fire
- 19. Hack, Pump And Dump
- 20. Dangerous Learning Curve
- 21. The Sherwood Boys
- 22. The Broken Nest Egg
- 23. One More Lap To Go
- 24. Death And Taxes
- 25. Keeping It All In The Family
- 26. No Security In Online Advance Fees
- 27. The G.I. Hacker
- 28. The Wrong Suspect
- 29. Dribbling On The Internet
- 30. Behind The Mask
- 31. Online Pharmacy
- 32. The Porn Procurement Process
- 33. Gambling On A Profit
- 34. The Solitaire Trader
- 35. The Big Brother He Never Had
- 36. Wanted: Your Money
- 37. The Business Of Making Money
- 38. Failure To Deliver
- 39. Cyber Psycho
- 40. Drag Queens And Drugs
- 41. Wire Transfers From Nowhere
- Glossary
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.