4.2. RISK ASSESSMENT FRAMEWORK FOR WSN IN A SENSOR CLOUD 49
Attack Graph
reat level estimation—Bayesian network
Time frame estimations
Develop attack pattern
& attack module
Create attack graph from
attack module
Severity ratings of attacks as
per CVSS guidelines
Attack’s probability of
success from severity ratings
Determine misuse frequency &
misuse impact of attacks
Model problem as a continuous-
time Markov process
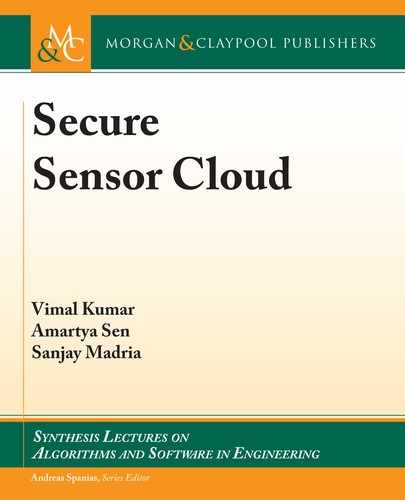
Figure 4.2: Proposed risk assessment framework.
4.2.1 ATTACK GRAPHS FOR WIRELESS SENSOR NETWORKS
Attack graphs, as introduced earlier in this chapter, are graphical structures with a bottom-
up assessment approach in which the root node is a critical system asset that we are trying to
evaluate based on the identified vulnerabilities in various systems it may interact with. ese
interconnected systems are depicted as the intermediate and the leaf nodes of the attack graph
structure. To generate an attack graph structure, the two pre-requisites are to develop an attack
pattern and an attack module database.
e very first step toward generating an attack graph is to to develop an attack pattern
database. It stores data about different attacks pertaining to knowledge such as vulnerabilities
they exploit, techniques they use to exploit the identified vulnerabilities, and so forth. is gives
us insight about the motivation and goal of an attacker which is then useful in devising security
measures that allows us to avert these attacks. An attack on a WSN will tend to exploit one or
more of the WSNs security parameters like confidentiality, integrity, and availability. us, in
the domain of WSNs, we can group the attacks according to the security parameter(s) they tend
to exploit. is will help in developing the attack pattern for attacks on a WSN [51].
Definition 4.1 Attack Pattern. An attack pattern is a tuple P
i
D .s
i
; /, where s
i
is the attack
and 2 [Confidentiality, Integrity, Availability] is one of the exploited WSN security param-
eters.

50 4. RISK ASSESSMENT IN A SENSOR CLOUD
Attacks on a WSN can be categorized as active or passive attacks [52]. Active attacks, such
as sinkhole, are executed to alter the network resources or operations such as routing protocol.
Passive attacks, such as eavesdropping, are executed to gather information about the network
which can then be used to execute Active attacks. An example instance of classification of active
and passive attacks is shown in Table 4.1. An instance of the set of known attacks along with
their definition and attack patterns [38, 39, 51] is given in Table 4.2.
Table 4.1: Classification of attacks on a WSN
Types of Security Attacks
Active Attacks Passive Attacks
Routing Attacks (Spoof, Alter and Replay;
Selective Forwarding; Sinkhole; Sybil;
Wormhole; HELLO Flood)
Passive information Gathering (Eavesdrop-
ping)
Denial of Service (Frequency Jamming) Traffi c Analysis
Fabrication (Node Subversion and Node
Malfunction)
Camoufl aged Adversaries
Lack of Cooperation (Node Outage)
Modifi cation (Physical Tampering and
Message Corruption)
Impersonation (Node Replication)
Further, to understand the cause-consequence relationships between attacks on a WSN,
we should be aware of the conditions that are required to execute a particular attack, also known
as pre-conditions of an attack, and the consequences of successful execution of an attack, also
known as the post-conditions of an attack. If the post-conditions of an attack satisfies the pre-
conditions of another attack then these two attacks will have a cause-consequence relationship
which is represented as an edge in the attack graph. We develop an attack module that will
capture the cause-consequence relationship between the attacks (Table 4.3). In some cases, pre-
conditions of an attack may be satisfied by the post-conditions of a single attack, these kinds
of attacks will be connected by an OR type join in the attack graph (Figure 4.3), whereas, if
post-conditions of two or more attacks are required simultaneously to satisfy the pre-conditions
of an attack, they are connected by AND type joins.
Definition 4.2 Attack Module. An attack module is defined as a tuple, (P
i
, S
pre
, S
post
, ),
where P
i
is the attack pattern, s
pre
is the pre-conditions required to execute the attack, s
post
are
the post-conditions after the execution of the attack, and is the join type, 2 [OR, AND].

4.2. RISK ASSESSMENT FRAMEWORK FOR WSN IN A SENSOR CLOUD 51
Table 4.2: Attack definition and attack pattern
Attack Defi nition
Target
Security
Parameter
Eavesdropping Listening to communication between the nodes C
Jamming and DoS Disrupting network communication by jamming communi-
cation frequency or sending additional garbage packets the
network cannot handle
A
Node Subversion Adversary taking over a legitimate sensor node C; I
Sybil Adversary node creating false virtual node identities and
making them seem like legitimate sensor nodes
C; I
Spoofi ng Adversary node pretending to be a legitimate node of a WSN C; I
Altering; Replay Continuously changing the route of packets; sending the
same packets over and over again
I; A
Wormhole;
Sinkhole;
Blackhole
Adversary falsely advertising effi cient route paths and rerout-
ing traffi c from actual paths—all traffic can now pass through
the adversary and (s)he may choose to drop all the packets
C; I; A
Selective
Forwarding
Once packet traffi c gets rerouted through the adversary (s)he
may decide to selectively drop some of the packets
C; I; A
Acknowledgment
Spoofi ng
Falsifying acknowledgment during authentication procedure or
when legitimate sensor nodes are trying to identify its neighbors
C; I
Node Malfunction A legitimate sensor node functionally abnormally due to
scare resources or a malware running on them
I; A
Node Replication An adversary creating a rogue sensor node which is based on
a legitimate sensor node
C; I
False Data
Injection
Adversary introducing garbage packets within the actual
packet transmission
I
Node Outage When a legitimate sensor node is no longer able to function A
Directed Physical
Attack
Physical damage brought unto the sensor nodes A
Hello Floods Continuous Hello messages sent to sensor node, which
makes them unable to handle any other messages and drains
their resources as a result of constantly having to deal with
these Hello messages
A
Desynchronization Sensor nodes constantly trying to re-establish broken com-
munication and not being able to do so
A
Malware Attack Execution of a malicious code on a legitimate sensor node C; I; A

52 4. RISK ASSESSMENT IN A SENSOR CLOUD
Table 4.3: Attack module
Attack Pre-condition Post-condition
Join
Type
Eavesdropping Adversary node within physical
reach of WSN and unencrypted
communication
Acquire unencrypted data AND
Jamming and DoS Adversary within the reach of
WSN
Disrupt network communication OR
Node Subversion Inability to authenticate; running
malicious codes
Attacks that require bypassing
authentication
OR
Sybil Node subversion; inability to au-
thenticate
Bypass authentication; breaking
of key distribution
AND
Spoofi ng Sybil; node subversion Further degradation of authen-
tication
OR
OR
OR
Altering; Replay Sybil; spoofi ng Loss of energy; loss of integrity OR
Wormhole;
Sinkhole; Blackhole
(Node subversion) Sybil; spoofi ng Route control; packet drop—par-
tial or complete; communication
disruption
AND
-OR
Selective
Forwarding
Wormhole; sinkhole Network more vulnerable to re-
play and rerouting
AND
Acknowledgment
Spoofi ng
Node subversion; Sybil Spoofi ng; wormhole; sinkhole AND
Node Malfunction Low snergy of the sensor nodes;
execution of malicious codes on
the sensor
Erroneous data in the network OR
Node Replication Physical tampering Adversary node legitimate part
of WSN
AND
False Data
Injection
Adversary node; In communica-
tion range of WSN
Presence of garbage data in the
WSN; jamming due to more
traffi c
AND
Node Outage Severe energy drain; directed
physical attack ; blackhole
Network disruption
Directed Physical
Attack
Topology discovery Node outage
Hello Floods Spoofi ng; Sybil Energy drain; breaking route
table due to continuous Hello
Packet transmissions
OR
OR
Desynchronization Node outage; Hello fl oods; replay;
reactive jamming
Communication disruption
Malware Attack Architecture of the sensor nodes;
user can execute his/her code
Node subversion AND
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.