- About This eBook
- Title Page
- Copyright Page
- Contents at a Glance
- Table of Contents
- About the Author
- About the Technical Reviewer
- Dedication
- Acknowledgments
- We Want to Hear from You!
- Reader Services
- Introduction
- Chapter 1. The Scope of Computer Forensics
- Chapter 2. Windows Operating and File Systems
- Chapter 3. Handling Computer Hardware
- Chapter 4. Acquiring Evidence in a Computer Forensics Lab
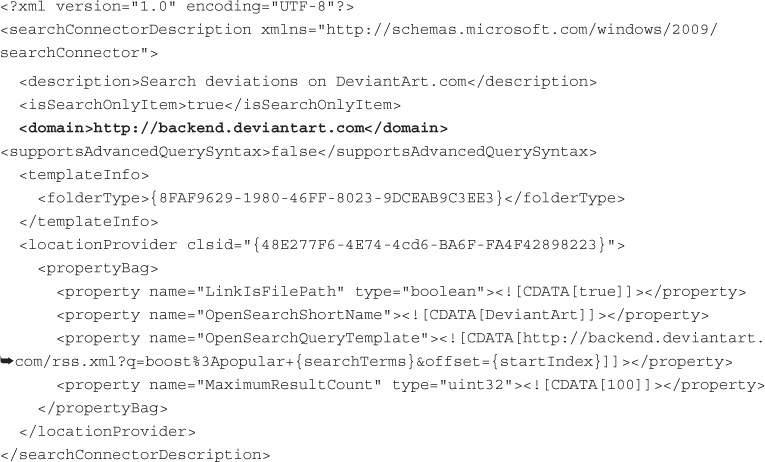
- Chapter 5. Online Investigations
- Chapter 6. Documenting the Investigation
- Chapter 8. Network Forensics
- Chapter 9. Mobile Forensics
- Chapter 10. Photograph Forensics
- Chapter 12. Case Studies
- Index
- Answers to Multiple-Choice and Fill in the Blanks Questions
- Code Snippets
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.