CHAPTER 3
Computer Systems Security Part II
This chapter covers the following subjects:
![]() Implementing Security Applications: In this section, you learn how to select, install, and configure security applications such as personal firewalls, antivirus programs, and host-based intrusion detection systems. You’ll be able to distinguish between the various tools and decide which is best for the different situations you’ll see in the field.
Implementing Security Applications: In this section, you learn how to select, install, and configure security applications such as personal firewalls, antivirus programs, and host-based intrusion detection systems. You’ll be able to distinguish between the various tools and decide which is best for the different situations you’ll see in the field.
![]() Securing Computer Hardware and Peripherals: Here we delve into the physical: how to protect a computer’s hardware, UEFI/BIOS, wireless devices, and peripherals such as USB devices.
Securing Computer Hardware and Peripherals: Here we delve into the physical: how to protect a computer’s hardware, UEFI/BIOS, wireless devices, and peripherals such as USB devices.
![]() Securing Mobile Devices: In this section, we will discuss how to protect mobile devices and the data they contain. By using screenlocks, encryption, remote wipe utilities, good BYOD policies, and more, we can protect devices from malicious attack, theft, and data loss.
Securing Mobile Devices: In this section, we will discuss how to protect mobile devices and the data they contain. By using screenlocks, encryption, remote wipe utilities, good BYOD policies, and more, we can protect devices from malicious attack, theft, and data loss.
In the previous chapter we discussed malicious software, which is one of the biggest threats to computer systems’ security. But it doesn’t stop there; your computer can be accessed in other ways, including via the UEFI/BIOS and by external devices. And “computer” doesn’t just mean that desktop computer at a user’s desk. It also means laptops, tablets, and smartphones—actually any other systems or devices that have processing power and an operating system. These threats can be eliminated by implementing proper configuration of the UEFI/BIOS, and providing for security applications on every one of your client computers on the network—be they desktop computers, laptops, mobile devices, or IoT devices.
Foundation Topics
Implementing Security Applications
In the previous chapter, we discussed endpoint protection platforms; namely anti-malware suites. These application suites usually have antivirus, anti-spyware, and anti-spam components. Often, they also have a built-in firewall, known as a personal firewall. And perhaps the application suite also has a built-in intrusion detection system (IDS), a piece of software that monitors and analyzes the system in an attempt to detect malicious activities. The type of IDS that a client computer would have is a host-based intrusion detection system (HIDS). But there are other types of standalone software firewalls and HIDSs; we cover these in just a bit. Another type of built-in security is the pop-up blocker. Integrated into web browsers and web browser add-ons, pop-up blockers help users avoid websites that could be malicious. Let’s discuss these security applications in a little more depth, starting with personal firewalls.
Personal Software Firewalls
Personal firewalls are applications that protect an individual computer from unwanted Internet traffic. They do so by way of a set of rules and policies. Some personal firewalls (also known as host-based firewalls) prompt the user for permission to enable particular applications to access the Internet. In addition, some personal firewalls have the capability to detect intrusions to a computer and block those intrusions; this is a basic form of a HIDS that we talk more about in the next section.
Examples of software-based personal firewalls include the following:
![]() Windows Firewall: Built into Windows, the basic version is accessible from the Control Panel or by typing
Windows Firewall: Built into Windows, the basic version is accessible from the Control Panel or by typing firewall.cpl in the Run prompt or Command Prompt. The advanced version, Windows Firewall with Advanced Security, can be accessed by typing wf.msc in the Run prompt or Command Prompt. This advanced version enables a user to perform more in-depth configurations such as custom rules.
![]() ZoneAlarm: Originally a free product that is still available (see the following link), this was purchased by Check Point and is now also offered as part of a suite of security applications. Go to https://www.zonealarm.com/software/free-firewall/.
ZoneAlarm: Originally a free product that is still available (see the following link), this was purchased by Check Point and is now also offered as part of a suite of security applications. Go to https://www.zonealarm.com/software/free-firewall/.
![]() PF (packet filter) and IPFW (IP Firewall): PF is the command-line-based firewall built into OS X version 10.10 and higher and macOS. Its predecessor, IPFW, was available in OS X through 10.9 but was deprecated in 10.7. Some OS X versions and macOS also include a graphical firewall titled “Firewall.” PF and IPFW are also used in FreeBSD.
PF (packet filter) and IPFW (IP Firewall): PF is the command-line-based firewall built into OS X version 10.10 and higher and macOS. Its predecessor, IPFW, was available in OS X through 10.9 but was deprecated in 10.7. Some OS X versions and macOS also include a graphical firewall titled “Firewall.” PF and IPFW are also used in FreeBSD.
![]() iptables: Used in Linux systems. Is used to configure the tables provided by the Linux kernel firewall and its rules. Can be extended upon using various configuration tools and third-party add-ons.
iptables: Used in Linux systems. Is used to configure the tables provided by the Linux kernel firewall and its rules. Can be extended upon using various configuration tools and third-party add-ons.
Anti-malware application suites from Symantec, McAfee, Kaspersky, and so on include personal firewalls as well. This has become a common trend, and you can expect to see personal firewall applications built into most anti-malware application suites in the future.
Because they are software, and because of the ever-increasing level of Internet attacks, personal firewalls should be updated often, and in many cases it is preferable to have them auto-update, although this depends on your organization’s policies.
As software, a personal firewall can utilize some of the computer’s resources. In the late 1990s and early 2000s, there were some complaints that particular anti-malware suites used too much CPU power and RAM, sometimes to the point of crashing the computer; in some cases this was because of the resources used by the firewall. Today, some anti-malware suites still run better than others, depending on the scenario. So, a smart systems administrator selects an endpoint protection platform that has a small footprint, and one that works best with the organization’s operating systems and applications. Some organizations opt not to use personal firewalls on client computers and instead focus more on network-based firewalls and other security precautions. The choice of whether to use personal firewalls, network-based firewalls, or both can vary but careful analysis should be performed before a decision is made. For example, take an organization that accepts credit card payments over the phone and performs the transactions over the Internet. The individual computers that are used to carry out the transactions need to have a personal firewall installed with the proper ports filtered in order to comply with financial regulations.
Personal firewalls (like any software application) can also be the victim of attack. If worms or other malware compromise a system, the firewall could be affected. This just reinforces the concept that antivirus suites should be updated often; daily updates would be the optimal solution.
A common scenario for security in small offices and home offices is to have a four-port SOHO router/firewall protecting the network and updated personal firewalls on every client computer. This combination provides two levels of protection for the average user. This defense layering approach is normally adequate for smaller networks, but larger networks usually concentrate more on the network firewall(s) and network-based IDS(s) than on personal firewalls, although it is common to see both levels of firewall security in larger networks as well.
Host-Based Intrusion Detection Systems
Let’s start by talking about intrusion detection systems (IDSs) in general. An IDS is used to monitor an individual computer system or a network, or a portion of a network, and analyze data that passes through to identify incidents, attacks, and so forth. You should be aware of two types of IDSs for the exam:
![]() Host-based intrusion detection system (HIDS): Loaded on an individual computer, it analyzes and monitors what happens inside that computer—for example, whether any changes have been made to file integrity. A HIDS is installed directly within an operating system, so it is not considered to be an “inline” device, unlike other network-based IDS solutions. One of the advantages of using a HIDS is that it can interpret encrypted traffic. Disadvantages include its purchase price, its resource-intensive operation, and its default local storage of the HIDS object database; if something happens to the computer, the database will be unavailable.
Host-based intrusion detection system (HIDS): Loaded on an individual computer, it analyzes and monitors what happens inside that computer—for example, whether any changes have been made to file integrity. A HIDS is installed directly within an operating system, so it is not considered to be an “inline” device, unlike other network-based IDS solutions. One of the advantages of using a HIDS is that it can interpret encrypted traffic. Disadvantages include its purchase price, its resource-intensive operation, and its default local storage of the HIDS object database; if something happens to the computer, the database will be unavailable.
![]() Network intrusion detection system (NIDS): Can be loaded on the computer, or can be a standalone appliance, but it checks all the packets that pass through the network interfaces, enabling it to “see” more than just one computer; because of this, a NIDS is considered to be an “inline” device. Advantages include the fact that it is less expensive and less resource intensive, and an entire network can be scanned for malicious activity as opposed to just one computer. Of course, the disadvantage is that a NIDS cannot monitor for things that happen within an operating system. For more information about NIDS solutions, see the section “NIDS Versus NIPS” in Chapter 8, “Network Perimeter Security.”
Network intrusion detection system (NIDS): Can be loaded on the computer, or can be a standalone appliance, but it checks all the packets that pass through the network interfaces, enabling it to “see” more than just one computer; because of this, a NIDS is considered to be an “inline” device. Advantages include the fact that it is less expensive and less resource intensive, and an entire network can be scanned for malicious activity as opposed to just one computer. Of course, the disadvantage is that a NIDS cannot monitor for things that happen within an operating system. For more information about NIDS solutions, see the section “NIDS Versus NIPS” in Chapter 8, “Network Perimeter Security.”
Following are two main types of monitoring that an IDS can carry out:
![]() Statistical anomaly: It establishes a performance baseline based on normal network traffic evaluations, and then compares current network traffic activity with the baseline to detect whether it is within baseline parameters. If the sampled traffic is outside baseline parameters, an alarm is triggered and sent to the administrator.
Statistical anomaly: It establishes a performance baseline based on normal network traffic evaluations, and then compares current network traffic activity with the baseline to detect whether it is within baseline parameters. If the sampled traffic is outside baseline parameters, an alarm is triggered and sent to the administrator.
![]() Signature-based: Network traffic is analyzed for predetermined attack patterns, which are known as signatures. These signatures are stored in a database that must be updated regularly to have effect. Many attacks today have their own distinct signatures. However, only the specific attack that matches the signature will be detected. Malicious activity with a slightly different signature might be missed.
Signature-based: Network traffic is analyzed for predetermined attack patterns, which are known as signatures. These signatures are stored in a database that must be updated regularly to have effect. Many attacks today have their own distinct signatures. However, only the specific attack that matches the signature will be detected. Malicious activity with a slightly different signature might be missed.
For more information about the various types of monitoring methodologies, see the section “Monitoring Methodologies” in Chapter 13, “Monitoring and Auditing.”
IDS solutions need to be accurate and updated often to avoid the misidentification of legitimate traffic or, worse, the misidentification of attacks. Following are two main types of misidentification you need to know for the exam:
![]() False positive: The IDS identifies legitimate activity as something malicious.
False positive: The IDS identifies legitimate activity as something malicious.
![]() False negative: The IDS identifies an attack as legitimate activity. For example, if the IDS does not have a particular attack’s signature in its database, the IDS will most likely not detect the attack, believing it to be legitimate, and the attack will run its course without any IDS warnings.
False negative: The IDS identifies an attack as legitimate activity. For example, if the IDS does not have a particular attack’s signature in its database, the IDS will most likely not detect the attack, believing it to be legitimate, and the attack will run its course without any IDS warnings.
Some antivirus application suites have basic HIDS functionality, but true HIDS solutions are individual and separate applications that monitor log files, check for file integrity, monitor policies, detect rootkits, and alert the administrator in real time of any changes to the host. This is all done in an effort to detect malicious activity such as spamming, zombie/botnet activity, identity theft, keystroke logging, and so on. Three examples of HIDS applications include the following:
![]() Trend Micro OSSEC (https://ossec.github.io/index.html): A free solution with versions for several platforms.
Trend Micro OSSEC (https://ossec.github.io/index.html): A free solution with versions for several platforms.
![]() Verisys (www.ionx.co.uk/products/verisys): A commercial HIDS file integrity monitoring solution for Windows.
Verisys (www.ionx.co.uk/products/verisys): A commercial HIDS file integrity monitoring solution for Windows.
![]() Tripwire (https://www.tripwire.com/products/tripwire-file-integrity-monitoring/): Another commercial HIDS solution.
Tripwire (https://www.tripwire.com/products/tripwire-file-integrity-monitoring/): Another commercial HIDS solution.
There are several compliance regulations that require the type of file integrity monitoring that a HIDS can provide, including PCI DSS and NIST 800-53. When selecting a HIDS, make sure it meets the criteria of any compliance regulations that your organization must adhere to.
It is important to protect the HIDS database because this can be a target for attackers. It should either be encrypted, stored on some sort of read-only memory, or stored outside the system.
If an IDS observes an incident, it notifies the systems or network administrator so that she might quarantine and fix the problem. However, over time, the need for prevention has become more desirable, and so intrusion prevention systems (IPSs) and intrusion detection and prevention systems (IDPSs) were developed. For the local computer system, this is known as host-based IPS, or HIPS. These not only detect incidents and attacks, but also attempt to prevent them from doing any real damage to the computer or to the network. Once again, typical companies such as McAfee and Symantec (and the aforementioned HIDS/HIPS providers) offer host-based intrusion prevention systems. There are also downloadable implementations for Linux that prevent malicious code from executing, such as Security-Enhanced Linux (SELinux). It is a set of kernel modifications originally developed by the National Security Agency (NSA) but was released to the open source community for download. We talk more about this in Chapter 11, “Access Control Methods and Models.”
A security administrator can review the logs of a host-based IDS at any time. However, if the computer has been shut down, the administrator will not be able to review information pertaining to system processes and network processes, nor information stored in memory, because all those items are volatile. HIDS logs that refer to archived storage, the MBR (or GPT), the system disk, e-mail, and so on will still be available for review. By reviewing the logs of a HIDS, a security administrator can find out if the computer has been compromised by malware, or if it is communicating with a botnet.
Pop-Up Blockers
For a website to generate revenue, a webmaster often advertises other products and services, charging fees to the organization that creates these products and services. The only way that an organization can continually advertise on the website is if it is positive it will get a certain amount of click-through response for its ads. However, web users quickly learn to define which windows are advertisements and which aren’t. So advertisers need to constantly create new and exciting ways to advertise their products. The traditional JavaScript-based pop-up window doesn’t do as good of a job as it used to because many web browsers have built-in pop-up blockers, but you still see tons of them on the Internet, perhaps in other formats such as Flash. They can take their toll on user productivity—and can be detrimental to the user’s computer. For example, some pop-up ads, if clicked, force the user to go to one or more separate websites that could have harmful code. Or worse yet, the pop-up itself could have malicious code built in; perhaps the Close button within the ad launches some other process altogether.
Some attackers create entire websites with malicious pop-ups just to infect as many computers as they can. You might ask: “Why take advantage of users?” Some attackers might answer: “Because they are there to be taken advantage of!” Not that I condone this behavior, but this mentality is infectious, making pop-ups and all their cousins common; so, systems administrators should try their best to block pop-ups. One way to do this is with a pop-up blocker. These can be either enabled on or added to most web browsers.
One of the problems with pop-up blocking is that it might block content that is not an advertisement but instead is integral to the actual website. For example, I used to run a bulletin board system that has the capability to let users know that they have new private messages from other users; one of the options is for this alert to show up as a pop-up window. Because so many users do not see this alert, and instead get a message from the browser that says “Pop-up blocked” or something similar, which can look sort of suspicious to the user, I decided to turn off that functionality and instead let the main login page of the website (and e-mails) notify the user of new messages. This type of philosophy should be taken into account by webmasters when they define what the purpose of their website will be. Proper website functionality should be integrated directly into the actual web page, because most users ignore pop-ups or consider them malicious and attempt to close them, or block them, if they weren’t otherwise blocked automatically by their browser.
When dealing with the previously listed applications and add-ons, pop-up blocking is known as ad filtering, but this can be taken to another level, known as content filtering. Content filters block external files that use JavaScript or images from loading into the browser. Content filtering continues to become more and more important as advertisers become more and more clever. Most newer web browser versions offer some kind of filtering, plus proxy-based programs such as Squid can filter content (among other things) for multiple computers. For more about proxy servers, see the section “Firewalls and Network Security” in Chapter 8.
Of course, advertisers have devised some new tricks in an attempt to get past the pop-up blockers and content filters: flash-based pop-ups, pop-under ads, dynamic HTML (DHTML) hover ads, and so on. Advertisers continue to battle for ad space with smart new ad types, so systems administrators should be prepared to update their clients’ web browsers and browser add-ons on a regular basis.
Data Loss Prevention Systems
Data loss prevention (DLP) is a concept that refers to the monitoring of data in use, data in motion, and data at rest. A DLP system performs content inspection and is designed to prevent unauthorized use of data as well as prevent the leakage of data outside the computer (or network) that it resides in. DLP systems can be software or hardware-based solutions and come in three varieties:
![]() Endpoint DLP systems: These systems run on an individual computer and are usually software-based. They monitor data in use, such as e-mail communications, and can control what information flows between various users. These systems can also be used to inspect the content of USB-based mass-storage devices or block those devices from being accessed altogether by creating rules within the software.
Endpoint DLP systems: These systems run on an individual computer and are usually software-based. They monitor data in use, such as e-mail communications, and can control what information flows between various users. These systems can also be used to inspect the content of USB-based mass-storage devices or block those devices from being accessed altogether by creating rules within the software.
![]() Network DLP systems: These can be software- or hardware-based solutions and are often installed on the perimeter of the network. They inspect data that is in motion.
Network DLP systems: These can be software- or hardware-based solutions and are often installed on the perimeter of the network. They inspect data that is in motion.
![]() Storage DLP systems: These are typically installed in data centers or server rooms as software that inspects data at rest.
Storage DLP systems: These are typically installed in data centers or server rooms as software that inspects data at rest.
Cloud-based DLP solutions are offered by most cloud providers to protect against data breaches and misuse of data. These often integrate with software, infrastructure, and platform services, and can include any of the systems mentioned previously. Cloud-based DLP is necessary for companies that have increased bring your own device (BYOD) usage (discussed later in the chapter), and that store data and operate infrastructure within the cloud.
As with HIDS solutions, DLP solutions must be accurate and updated to reduce the number of false positives and false negatives. Most systems alert the security administrator in the case that there was a possibility of data leakage. However, it is up to the administrator to determine whether the threat was real.
Securing Computer Hardware and Peripherals
Now that the operating system is better secured, let’s talk about securing computer hardware, the BIOS, and external peripheral devices.
There is a plethora of devices that can be connected to a computer system, such as USB flash drives, external SATA hard drives, and optical discs, just to mention a few. What if you want to stop people from using USB connections and USB-connected devices on the computer—without using a DLP solution? Well, there’s the underlying firmware without which our computer could not run; I’m speaking of the BIOS, which can secure these ports and devices. However, the BIOS must be secured as well!
Note
While firmware implementations such as UEFI replace, or work in conjunction with, the BIOS in many new computers, manufacturers still tend to refer to the firmware as the BIOS. For simplicity in this book I normally use the term “BIOS” to refer to both the BIOS and the UEFI. However, if a particular technology works in the UEFI only, it will be described as such.
Securing the BIOS
The BIOS can be the victim of malicious attacks; for mischievous persons, it can also act as the gateway to the rest of the system. Protect it! Otherwise, your computer might not boot—or worse. Following are a few ways to do so:
![]() Flash the BIOS: Flashing is a term that describes the updating of the BIOS. By updating the BIOS to the latest version, you can avoid possible exploits and BIOS errors that might occur. An updated BIOS (and newer motherboard) can also better protect from electromagnetic interference (EMI) and electromagnetic pulses (EMP). All new motherboards issue at least one new BIOS version within the first six months of the motherboard’s release. Normally, you would flash the BIOS first before making any changes to the BIOS configurations.
Flash the BIOS: Flashing is a term that describes the updating of the BIOS. By updating the BIOS to the latest version, you can avoid possible exploits and BIOS errors that might occur. An updated BIOS (and newer motherboard) can also better protect from electromagnetic interference (EMI) and electromagnetic pulses (EMP). All new motherboards issue at least one new BIOS version within the first six months of the motherboard’s release. Normally, you would flash the BIOS first before making any changes to the BIOS configurations.
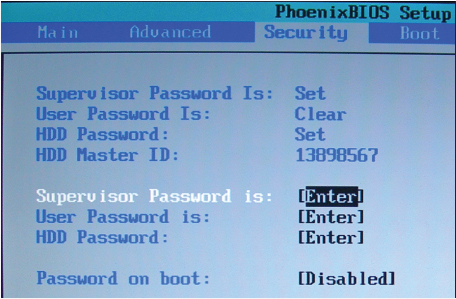
![]() Use a BIOS password: The password that blocks unwanted persons from gaining access to the BIOS is the supervisor password. Don’t confuse it with the user password (or power-on password) employed so that the BIOS can verify a user’s identity before accessing the operating system. Both of these are shown in Figure 3-1. Because some computers’ BIOS password can be cleared by opening the computer (and either removing the battery or changing the BIOS jumper), some organizations opt to use locking cables or a similar locking device that deters a person from opening the computer.
Use a BIOS password: The password that blocks unwanted persons from gaining access to the BIOS is the supervisor password. Don’t confuse it with the user password (or power-on password) employed so that the BIOS can verify a user’s identity before accessing the operating system. Both of these are shown in Figure 3-1. Because some computers’ BIOS password can be cleared by opening the computer (and either removing the battery or changing the BIOS jumper), some organizations opt to use locking cables or a similar locking device that deters a person from opening the computer.
On a semi-related note, many laptops come equipped with drive lock technology; this might simply be referred to as an HDD password or other similar name. If enabled, it prompts the user to enter a password for the hard drive when the computer is first booted. If the user of the computer doesn’t know the password for the hard drive, the drive locks and the OS does not boot. An eight-digit or similar hard drive ID can associate the laptop with the hard drive installed (refer to Figure 3-1). On most systems this password is clear by default, but if the password is set and forgotten, it can usually be reset within the BIOS. Some laptops come with documentation clearly stating the default BIOS and drive lock passwords—change them as part of the initial configuration of the computer.
![]() Configure the BIOS boot order: Set up the BIOS to reduce the risk of infiltration. For example, change the BIOS boot order (boot device priority) so that it looks for a hard drive first and not any type of removable media.
Configure the BIOS boot order: Set up the BIOS to reduce the risk of infiltration. For example, change the BIOS boot order (boot device priority) so that it looks for a hard drive first and not any type of removable media.
![]() Disable external ports and devices: If a company policy requires it, disable removable media including the optical drives, eSATA ports, and USB ports.
Disable external ports and devices: If a company policy requires it, disable removable media including the optical drives, eSATA ports, and USB ports.
![]() Enable the secure boot option: UEFI 2.3.1 and higher offer an option called secure boot. This can secure the boot process of the computer by preventing unsigned—or improperly signed—device drivers and OS loaders. Implementing this may or may not be possible depending on the type of hardware used by your organization. Review hardware documentation and device drivers, and more importantly test the configuration, before implementing this option.
Enable the secure boot option: UEFI 2.3.1 and higher offer an option called secure boot. This can secure the boot process of the computer by preventing unsigned—or improperly signed—device drivers and OS loaders. Implementing this may or may not be possible depending on the type of hardware used by your organization. Review hardware documentation and device drivers, and more importantly test the configuration, before implementing this option.
Today’s UEFI-based systems use a root of trust, which is code—usually embedded in hardware in the form of a trusted platform module (TPM)—that incorporates encryption in the form of a public key. For a system with secure boot enabled to start up properly, kernel-based operating system drivers must present private keys that match the root of trust’s public key. This process can prevent a system from being booted by undesirable OSes that can reside on flash drives or elsewhere, and prevent OSes that have been tampered with from booting. This tampering might occur in-house, or previously while in transit through the manufacturing supply chain.
Secure boot, also known as trusted boot, is an excellent method for protecting the boot process. However, if something occurs that causes the boot process to fail, we won’t know because that data is stored in the UEFI of the system that failed to boot. More importantly, we want to be sure that secure boot is working properly. Enter the measured boot option. Measured boot takes measurements of each step of the secure boot process. It signs them, stores them, and sends those measurements to an external source, such as a remote attestation service. A trusted, external, third-party system is required for attestation—meaning verification of the integrity of the computer in question has been corroborated. Basically, the remote attestation service compares the measurements with known good values. From this information, the remote service can attest to the fact that the boot process is indeed secure—or has failed to meet the requirements.
Securing Storage Devices
The storage device is known to be a common failure point because many storage devices have moving parts or use removable media. Storage devices also can pose security risks because usually they are external from a computer system and are possibly located in an insecure area. Also, keeping track of removable media can be difficult. Some of the solutions to this include physical security, encryption, and policies that govern the use and storage of removable media. This section discusses removable storage devices, such as discs and external USB drives, network attached storage (NAS), and whole disk encryption. Hardware security modules take hardware-based encryption to the next level—we also discuss the basics of how these HSMs operate.
Removable Storage
Removable storage, or removable media, includes optical discs, USB devices, eSATA devices, and even floppy disks in some cases. A network administrator can prevent access to removable media from within the BIOS and within the operating system policies. In many companies, all removable media is blocked except for specifically necessary devices, which are approved on a case-by-case basis. Users should be trained on the proper usage of removable media and should not be allowed to take any data home with them. Users who sometimes work from home should do so via a virtual private network (VPN) connection to keep the data confidential, yet accessible.
USB devices must be carefully considered. They are small but can transport a lot of data. These devices can be the victim of attacks and can act as the delivery mechanism for attacks to a computer. For example, a USB flash drive might have data files or entire virtual operating systems that can be exploited by viruses and worms. Also, an attacker can install a special type of virus or worm onto the flash drive that is executed when the flash drive is connected to the computer; in this scenario the computer is the target for the malware. Organizations must decide whether to allow USB devices to be used. Organizational policies should state that USB sticks should not be carried from one department to another without proper security procedures in place. Operating system group policies can be implemented to enforce which users are allowed to use USB devices. As mentioned earlier, the BIOS can also disable the use of USB devices on a local computer. Finally, the data on a USB device can be encrypted with various programs—for example, Windows BitLocker—on the software side, or you might opt to purchase a secure USB flash drive, such as one by IronKey (http://www.ironkey.com/en-US/).
USB flash drives can easily be considered inherently insecure devices. It’s the nature of the beast, so to speak. As such, a security administrator needs to implement removable media controls governing the usage of USB sticks and other removable media. These should include but are not limited to: USB lockdown in the BIOS and OS; limited use of USB devices; scanning of media devices for malware; encryption of data; monitoring of connected systems; and auditing of removable media. In addition, the reuse and disposal of removable media should be carefully managed—destruction of media might be necessary. Finally, a security administrator should be instrumental in writing policies for the company that dictate how these controls are implemented and educate users about these policies and maintain their awareness over time.
Network Attached Storage
Network attached storage (NAS) is a storage device that connects directly to your Ethernet network. Basic home and office NAS devices usually contain two hard drives, enabling you to set up RAID 1 mirroring, which protects your data if one drive fails. A more advanced example of NAS would be a device that looks more like a computer and might house up to 32 drives and contain terabytes of data. Possibly hot-swappable, these drives can be physically replaced, and the data can be rebuilt in a short amount of time. However, when it comes to RAID arrays, what we desire is high availability—meaning continuously operational for extended periods of time—in the neighborhood of 99.9% average uptime or higher.
A NAS device might be part of a larger storage area network (SAN); therefore, network security should also be considered when implementing any type of NAS. For more information on network security, see Chapters 6 through 9. To protect a single NAS device, consider data encryption, authentication, and constant secure logging of the device.
Whole Disk Encryption
Encryption is a huge component of today’s computer security. By encrypting information, the data is rearranged in such a way that only the persons with proper authentication can read it. To encrypt an entire hard drive, you either need a self-encrypting drive (SED) or some kind of full disk encryption (FDE) software. (“Disk,” though not accurate in some cases, is the commonly used term here.) Several types of FDE software are currently available on the market; one developed by Microsoft is called BitLocker—available in the elite editions of several newer versions of Windows. Full disk encryption software can encrypt the entire disk, which, after complete, is transparent to the user. Following are some requirements for encrypting an entire drive:
![]() Trusted platform module (TPM)—A chip residing on the motherboard that stores the encrypted keys. (This is part of the concept mentioned previously known as the root of trust.)
Trusted platform module (TPM)—A chip residing on the motherboard that stores the encrypted keys. (This is part of the concept mentioned previously known as the root of trust.)
or
![]() An external USB key to store the encrypted keys.
An external USB key to store the encrypted keys.
and
![]() A hard drive with two volumes, preferably created during the installation of Windows. One volume is for the operating system (most likely C:) that will be encrypted; the other is the active volume that remains unencrypted so that the computer can boot. If a second volume needs to be created, the BitLocker Drive Preparation Tool can be of assistance and can be downloaded from the Microsoft Download Center.
A hard drive with two volumes, preferably created during the installation of Windows. One volume is for the operating system (most likely C:) that will be encrypted; the other is the active volume that remains unencrypted so that the computer can boot. If a second volume needs to be created, the BitLocker Drive Preparation Tool can be of assistance and can be downloaded from the Microsoft Download Center.
BitLocker software is based on the Advanced Encryption Standard (AES) and can use 128-bit and 256-bit keys. Keep in mind that a drive encrypted with BitLocker usually suffers in performance compared to a nonencrypted drive and could have a shorter shelf life as well.
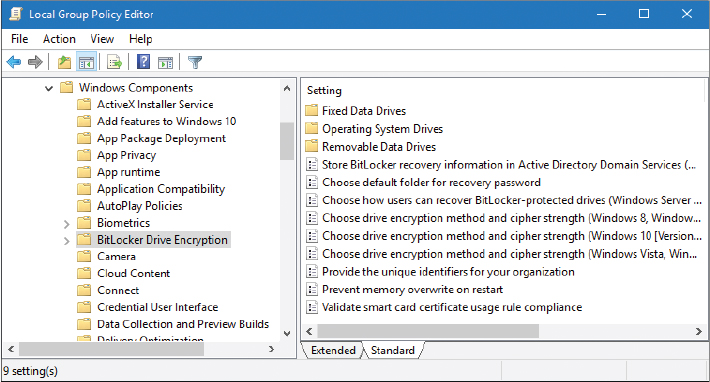
In the appropriate Windows version/edition, BitLocker security settings can be accessed via the following steps:
Step 1. Navigate to the Run prompt.
Step 2. Type gpedit.msc and press Enter.
Step 3. In the Group Policy Editor window, navigate to Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption.
Figure 3-2 shows the BitLocker configuration settings window.

Note
For more information about BitLocker and how to use it, see the follow-
ing link:
https://technet.microsoft.com/en-us/library/hh831713(v=ws.11).aspx
Although it can be a lot of work to implement, double encryption can be a very successful technique when it comes to securing files. For example, a hard drive encrypted with BitLocker could also use EFS to encrypt individual files. This way, files that are copied to external media will remain encrypted, even though they don’t reside on the drive using whole disk encryption.
Hardware Security Modules
Hardware security modules (HSMs) are physical devices that act as secure cryptoprocessors. This means that they are used for encryption during secure login/authentication processes, during digital signings of data, and for payment security systems. The beauty of a hardware-based encryption device such as an HSM (or a TPM) is that it is faster than software encryption.
HSMs can be found in adapter card form, as devices that plug into a computer via USB, and as network-attached devices. They are generally tamper-proof, giving a high level of physical security. They can also be used in high-availability clustered environments because they work independently of other computer systems and are used solely to calculate the data required for encryption keys. However, many of these devices require some kind of management software to be installed on the computer they are connected to. Some manufacturers offer this software as part of the purchase, but others do not, forcing the purchaser to build the management software themselves. Due to this lack of management software, and the cost involved in general, HSMs have seen slower deployment with some organizations. This concept also holds true for hardware-based drive encryption solutions.
Often, HSMs are involved in the generation, storage, and archiving of encrypted key pairs such as the ones used in Secure Sockets Layer (SSL) sessions online, public key cryptography, and public key infrastructures (PKIs), which we discuss more in Chapter 14, “Encryption and Hashing Concepts,” and Chapter 15, “PKI and Encryption Protocols.”
Securing Wireless Peripherals
In today’s “hassle-free” world of peripherals, there are a ton of wireless devices in use. Unfortunately, because wireless signals are generally spread spectrum, they can be more easily intercepted than wired signals. Some wireless peripherals, such as keyboards and mice, can have their keystrokes and clicks captured with the most basic of attacks. To protect against this, some manufacturers offer encrypted wireless device solutions, with AES being one of the most common encryption protocols used. Wireless displays use technologies such as Wi-Fi Direct (WiDi) that is backward compatible with standard Wi-Fi technologies. As such, these displays should make connections using WPA2 and AES. Wi-Fi-enabled cameras and SD/microSD cards should be configured in a similar manner. The same goes with external storage devices, printers, and multi-function devices. The bottom line is this: Any peripheral that connects in a wireless fashion needs to have proper authentication put in place (such as WPA2) and strong encryption (such as AES-256 or higher). Also keep in mind that newer types of authentication and encryption become available occasionally. Remember to periodically check whether your wireless security schemes are up to date.
Securing Mobile Devices
Unfortunately, smartphones and tablets (and other mobile devices) can be the victims of attack as well. Attackers might choose to abuse your service or use your device as part of a larger scale attack, and possibly to gain access to your account information. Though mobile devices can be considered “computers,” and most of the information mentioned in this chapter and the previous chapter applies to them as well, there are some other things we should consider specifically for the mobile device.
Users of mobile devices should be careful who they give their phone number to, and should avoid listing their phone number on any websites, especially when purchasing products. Train your users not to follow any links sent by e-mail or by text messages if these are unsolicited. (If there is any doubt in the user’s mind, then it is best to ignore the communication.) Explain the issues with much of the downloadable software, such as games and ringtones, to your users. Use a locking code/password/gesture that’s hard to guess; this locks the mobile device after a specific amount of time has lapsed. Use complex passwords when necessary; for example, if required by company policy.
In general, mobile operating system software must be updated just like desktop computer software. Keep these devices up to date, and there will be less of a chance that they will be affected by viruses and other malware. You can encrypt data in several ways, and some organizations have policies that specify how data will be encrypted. More good general tips are available at the following National Cyber Awareness System (NCAS) and U.S. Computer Emergency Readiness Team (US-CERT) website links. Make your users aware of them.
![]() https://www.us-cert.gov/ncas/tips/ST05-017.html
https://www.us-cert.gov/ncas/tips/ST05-017.html
It should be noted that some organizations will use the term “portable electronic device,” which refers to any portable device that can store and record data and transmit text, images, video, and audio data. Devices in the portable electronic device (PED) category include laptops, media players, e-readers, gaming devices, cell phones, pagers, radios, audio devices, fitness devices, and so on. However, for this book we are most concerned with smartphones and tablets and refer to them as mobile devices.
Let’s discuss some of the attacks and other concerns for mobile devices, as well as ways to prevent these things from happening, and how to recover from them if they do occur.
Malware
It’s not just Windows that you have to worry about when it comes to malware. Every operating system is vulnerable, some less than others. Historically, in the mobile device marketplace, Android has proven to be somewhat of a stomping ground for malware; for example, the GinMaster Trojan steals confidential information from the Android device and sends it to a remote website. Viruses, worms, rootkits, and other types of malware are commonly found in the Android OS, and are sometimes found in iOS and other mobile device operating systems.
As with desktop operating systems, mobile operating systems should be updated to the newest version possible (or the point release for the version installed). AV software can also be used. Newer models of mobile devices come with built-in security programs. These programs should be updated regularly, and configured for optimal security. Care should be taken when tapping links within e-mails, texts, or social media networks. Personal or organizational information should never be shared on social networks, and should usually not be stored on the mobile device.
Note
Social engineering attacks are also quite common on mobile devices. Techniques such as hoaxes, pretexting, phishing, and many more are commonplace. We’ll discuss how to combat social engineering in general within Chapter 17, “Social Engineering, User Education, and Facilities Security.”
Botnet Activity
Mobile devices can be part of botnets—just like desktop computers. Because they are more easily accessible than desktop computers at this point, they make up a big part of some of today’s botnets. A mobile device can take part in the launching of distributed denial-of-service (DDoS) attacks, or inadvertently join in with a click fraud outfit, or could be part of a scam to get users of other mobile devices to send premium-rate Short Message Service (SMS) messages. And that’s just the beginning. Methods for preventing a mobile device from joining a botnet (without the user’s knowledge) are similar to those mentioned previously concerning malware. Great care should be taken when downloading applications. The user should make sure the apps are from a legitimate source. Also, rooting (or jailbreaking) the mobile device is not recommended. The programs used in conjunction with rooting the device are often malicious, or are closely aligned with other malicious programs. In addition, a mobile device with custom firmware, also known as custom ROM, is more susceptible to root access from would-be attackers and botnets. Not to mention that over-the-air (OTA) firmware updates might not work anymore. If it appears that a device has become part of a botnet, that device should be wiped, either by a hard reset or other means.
SIM Cloning and Carrier Unlocking
Another attack on smartphones is SIM cloning (also known as phone cloning), which allows two phones to utilize the same service and allows an attacker to gain access to all phone data. V1 SIM cards had a weak algorithm that made SIM cloning possible (with some expertise). However, V2 cards and higher are much more difficult (if not impossible) to clone due to a stronger algorithm on the chip. Users and administrators should be aware of the version of SIM card being used and update it (or the entire smartphone) if necessary.
There are techniques available to unlock a smartphone from its carrier. Users should be advised against this, and a security administrator should create and implement policies that make unlocking the SIM card difficult, if not impossible. Unlocking the phone—making it SIM-free—effectively takes it off the grid and makes it difficult to track and manage. When the SIM is wiped, the International Mobile Subscriber Identity (IMSI) is lost and afterward the user cannot be recognized. However, the security administrator can attempt to blacklist the smartphone through its provider using the International Mobile Equipment Identity (IMEI), electronic serial number (ESN), or Mobile Equipment Identifier (MEID). The ID used will vary depending on the type and age of smartphone. Regardless, as a security administrator, you would rather avoid that tactic altogether because the damage has already been done; so, protection of the SIM becomes vital.
Wireless Attacks
Anytime a cell phone or smartphone connects, it uses some type of wireless service. Whether it’s 4G, 3G, GSM, Wi-Fi, infrared, RFID, or Bluetooth, security implications exist. To minimize risks, the best solution is to turn off the particular service when not in use, use airplane mode, or simply turn the mobile device off altogether if it is not being used.
Bluetooth is especially vulnerable to virus attacks, as well as bluejacking and bluesnarfing.
Bluejacking is the sending of unsolicited messages to Bluetooth-enabled devices such as mobile phones. Bluejacking can be stopped by setting the affected Bluetooth device to “undiscoverable” or by turning off Bluetooth altogether.
Bluesnarfing is the unauthorized access of information from a wireless device through a Bluetooth connection. Generally, bluesnarfing is the theft of data (calendar information, phonebook contacts, and so on). Ways of discouraging bluesnarfing include using a pairing key that is not easy to guess; for example, stay away from 0000 or similar default Bluetooth pairing keys! Otherwise, Bluetooth devices should be set to “undiscoverable” (only after legitimate Bluetooth devices have been set up, of course), or Bluetooth can be turned off altogether.
For more information about Bluetooth vulnerabilities (and other wireless attacks in general), see the section “Securing Wireless Networks” in Chapter 9, “Securing Network Media and Devices.”
Wi-Fi has many vulnerabilities as well. Not only should mobile devices connect in a secure, encrypted fashion, but also the security administrator needs to keep a sharp eye on the current CVEs, and the available updates and patches for those vulnerabilities. For example, there was a flaw in the programming of a well-known Wi-Fi System on Chip (SoC). The firmware had a vulnerability that could result in buffer overflows, which could then be exploited by an attacker—connecting remotely via Wi-Fi—ultimately allowing the execution of their own code. Sometimes SoCs are not properly vetted for vulnerabilities and so security administrators must be ready to patch at a moment’s notice—and this applies not only to smartphones and other typical mobile devices, but also to just about any devices in the Internet of Things (IoT) that have built-in Wi-Fi connections.
Theft
More than 100 mobile devices end up missing (often stolen) every minute. Let me repeat—every minute! You can imagine the variety of reasons why this is. The worst attack that can be perpetuated on a smartphone or tablet is theft. The theft of a mobile device means the possible loss of important data and personal information. There are a few ways to protect against this loss of data, and recover from the theft of a mobile device if it does happen.
First, mobile devices in an organization should utilize data encryption. The stronger the encryption, the more difficult it is for a thief to decode and use the data on the device. If at all possible, use full device encryption, similar to Windows BitLocker. The actual conversations on phones can also be encrypted. Voice encryption can protect the confidentiality of spoken conversations and can be implemented with a special microSD chip (preferably) or with software.
Mobile devices should also be set up for GPS tracking so that they can be tracked if they are lost or stolen. The quicker a device can be located, the less risk of data loss, especially if it is encrypted. However, GPS tracking can also be a security vulnerability for the device and possibly the user if an attacker knows how to track the phone.
The beauty of mobile devices is in their inherent portability—that and the ability to track SIM cards. Administrators of mobile devices should consider remote lockout programs. If a device is lost or stolen, the admin can lock the device, disallowing a would-be attacker access. In addition, the device can be configured to use the “three strikes and you’re out” rule, meaning that if a user tries to be authenticated to the device and is unsuccessful after three attempts, the user is locked out. Taking it to the next level, if the data is extremely sensitive, you might want to consider a remote wipe program. If the mobile device is reported as lost or stolen, these programs can remove all data from the phone in a bit by bit process, making it difficult (if not impossible) to recover. This is known as sanitizing the phone remotely. Of course, a solid backup strategy should be in place before a data sanitizing or remote wipe solution is implemented.
Screen locks, complex passwords, and taking care when connecting to wireless networks are also important. Though a screen lock won’t deter the knowledgeable attacker, it will usually deter the average person who, for example, finds a stray phone sitting in a coffee shop, mall, or other public location. User training should be implemented when users first receive their device. Though many organizations don’t take the time to do this, it is a great way to show users how to secure their device, while checking whether their encryption, GPS tracking, and other features are working properly. They can also be trained on how to inform your organization and local law enforcement in the case that a device is lost or stolen, effectively reducing the risk of data loss by allowing you to find the device faster or mitigate the problem in other ways.
Note
In the case of theft, the two best ways to protect against the loss of confidential or sensitive information are encryption and a remote wipe program.
Application Security
Let’s speak more about the applications’ security on mobile devices. We’ve already mentioned that applications should (usually) be updated to the latest version, and discussed the importance of proper user interaction; but let’s delve a bit deeper and talk about ways to encrypt data that is transferred through applications.
Encryption is one of the best ways to ensure that data is secured and that applications work properly without interference from potential attackers. However, a security administrator should consider whole device encryption, which encrypts the internal memory and any removable (SD) cards. Sometimes an admin might forget about one or the other. Then there is data in transit; data that is on the move between a client and a server. Most applications for mobile devices communicate with a server of some sort; for example, when a person uses a web browser, an e-mail client, a contacts database, or actual “apps” that work independently of a browser, but operate in a similar manner, meaning that they ultimately connect to a server. Weather apps, games, social media apps, and so on all fall into this category.
Let’s consider the web browser, for instance. A mobile device will connect to websites in a very similar manner as a desktop computer. Basic websites will use a Hypertext Transfer Protocol (HTTP) connection. But websites that require any type of personally identifiable information (PII) will use HTTP Secure (HTTPS). This can then utilize one of several types of encryption, such as Transport Layer Security (TLS).
Note
We’ll discuss HTTPS, TLS, and many other security protocols in more depth within Chapter 5 and Chapter 15.
Whatever the security protocol, the important point here is that the server connected to makes use of a database that stores encryption keys. The key (or a portion thereof) is sent to the client device and is agreed upon (handshaking occurs) so that the transfer of data, especially private information, is encrypted and protected. Often, HTTPS pages are used to aid in the process of authentication—the confirmation of a person’s (or computer’s) identity, typically with the help of a username/password combination. Examples of this include when you log in to your account with a bank or with a shopping portal.
One of the important roles for the server is key management—the creation, storage, usage, and retirement of encryption keys. Proper key management (and the regular updating of keys) is a security administrator’s primary concern. Generally, an organization will purchase a master key algorithm from a third-party company such as VeriSign. That company informs the organization if a key has become compromised and needs to be revoked. These third parties might also take part in credential management (the managing of usernames, passwords, PINs, and other passcodes, usually stored within a secure database) to make things a bit easier for the security administrator. It depends on the size of the organization and its budget. This gets quite in-depth, as you can imagine. For now, realize that a mobile device is an easy target. Therefore, applications (especially third-party apps) should be scrutinized to make sure they are using a solid encryption plan when personal information is transferred back and forth. Of course, we’ll get more into encryption and key management in Chapters 14 and 15.
Authentication to servers and other networks (and all their applications) can get even more complicated when the concept of transitive trust is implemented. Effectively, a transitive trust is when two networks (or more) have a relationship such that users logging in to one network get access to data on the other. In days gone by, these types of trusts were created automatically between different sections of networks. However, it was quickly realized that this type of transitivity was insecure, allowing users (and potential attackers) access to other networks that they shouldn’t have had access to in the first place. There’s a larger looming threat here as well. The transitive trust is based on the transitive property in mathematics, which states that if A is equal to B, and B is equal to C, then A is automatically equal to C. Put into computer terms: if the New York network trusts the California network, and the California network trusts the Hong Kong network, then the New York network automatically trusts the Hong Kong network. You can imagine the security concerns here, as well as the domino effect that could occur. So, organizations will usually prefer the non-transitive trust, where users need to be authenticated to each network separately, and therefore are limited to the applications (and data) they have access to on a per-network basis.
To further restrict users, and increase application security, application whitelisting is often used. This means that a list of approved applications is created by the administrator and that the user can work with only those applications, and no others. This is often done within a computer policy and can be made more manageable by utilizing a mobile device management system (which we will detail a bit later). Users often only need access to several apps: phone, e-mail, contacts, and web browser. These applications would make up the whitelist, and if a user tried to use other apps, they would be denied, or at the very least, would be prompted for additional user credentials. If a user needed access to another app, such as the camera, the security administrator would weigh the security concerns (GPS, links to social media, and so on) and decide whether to add the app to the whitelist. Whitelisting can also be helpful when dealing with apps that utilize OAuth; a common mechanism used by social media companies to permit users to share account information with third-party applications and websites. Contrast the concept of application whitelisting with application blacklisting—the denial of individual applications—a common method used when working with e-mail, and by antivirus and HIDS programs.
The messaging app is a particularly devious gateway for attackers. SMS and MMS are vulnerable to malware, and unwary users of mobile devices are especially susceptible to Trojans and phishing via SMS texts. One way to prevent this is to install mobile anti-malware in the form of one mobile security suite or another. This endpoint protection platform needs to be updated and is best controlled from a mobile device management (MDM) solution. Another way is to block messaging apps altogether or to use company-approved messaging apps. This option depends on what type of mobile environment you are allowing. It will work for some mobile environments where the IT department has more control over devices, but probably not for BYOD.
If your organization uses a mobile payment method, it is important to understand that the applications that control these payment methods and the devices they run on can have several vulnerabilities. These include weak passwords (for the mobile device and for the payment app), user error, and phishing. Not only that, the technology itself is inherently insecure given the mobility of the device. Users should be educated about not using their mobile devices for payment while making a public Wi-Fi connection. They should also be taught how to properly and discreetly use payment apps. And of course, they should be instructed on how to avoid loss or theft of a mobile device, and what to do if loss or theft occurs. As the security administrator, you should consider using an external reader for payment transactions on mobile devices and teaching users to keep the reader separate from the mobile device when not in use.
Geotagging (also written as geo-tagging) is another application concern. Photos, videos, websites, messages, and much more can be geotagged. Geotagging is the adding of data to the content in question, helping users to gather location-specific information. For example, if a user wanted to take a picture of their favorite store at the mall and help friends to find it, the user could geotag the picture. However, this requires that the smartphone (or other mobile device) have GPS installed and running. This then means that the user’s smartphone can be physically located and tracked. Depending on the applications running, this could pose a security threat. In a corporate environment, the security administrator will often choose to disable geotagging features. There are several privacy implications when it comes to geotagging. One of the most dangerous is the fact that many users don’t even know that they are geotagging their media when they do so—some of the applications are that transparent. For people in the company such as executives (who might carry a wealth of confidential information), this is the type of feature that should be disabled. If a potential attacker can track an executive, then the attacker can find out where the executive lives, determine when the executive is in the office, and determine the location of clients, all of which can help the attacker to commit corporate espionage. When it comes down to it, the usage of GPS in general should be examined carefully, weighing the benefits against the possible vulnerabilities. This includes GPS derivatives such as GPS tagging, geofencing, and geolocation. (We’ll discuss those terms in more depth in Chapter 9.) Many executives and other employees use their mobile devices at work, which brings up many security concerns besides GPS. Collectively these are known as BYOD concerns and are described in the following section.
BYOD Concerns
Around 2011, organizations began to allow employees to bring their own mobile devices into work and connect them to the organization’s network (for work purposes only, of course). This “bring your own device” concept has since grown into a more popular method of computing for many organizations. It is enticing from a budgeting standpoint, but can be very difficult on the security administrator, and possibly on the user as well.
Note
Companies may implement similar strategies, such as choose your own device (CYOD), where employees select a device from a company-approved list, or corporate owned, personally enabled (COPE), where employees are supplied a phone by the company that can also be used for personal activities. For simplicity, I refer to these collectively as BYOD unless CYOD or COPE needs to be addressed specifically.
In order to have a successful BYOD implementation, the key is to implement storage segmentation—a clear separation of organizational and personal information, applications, and other content. It must be unmistakable where the data ownership line occurs. For networks with a lot of users, consider third-party offerings from companies that make use of mobile device management (MDM) platforms. These are centralized software solutions that can control, configure, update, and secure remote mobile devices such as Android, iOS, BlackBerry, and so on, all from one administrative console. The MDM software can be run from a server within the organization, or administered within the cloud. It makes the job of a mobile IT security administrator at least manageable. From the central location, the security administrator can carry out the tasks of application management, content management, and patch management. The admin can also set up more secure levels of mobile device access control. Access control is the methodology used to allow access to computer systems. (More on access control in Chapter 11.) For larger organizations, MDM software makes it easy for an admin to view inventory control, such as how many devices are active for each of the mobile operating systems used. It also makes it simpler to track assets, such as the devices themselves, and the types of data each contains. In addition, MDM software makes it less complicated to disable unused features on multiple devices at once, thereby increasing the efficiency of the devices, reducing their footprint, and ultimately making them more secure. For instance, an employee who happens to have both a smartphone and a tablet capable of making cellular calls doesn’t necessarily need the latter. The admin could disable the tablet’s cellular capability, which would increase battery efficiency as well as security for that device. Insecure user configurations such as rooting and jailbreaking can be blocked from MDM, as can sideloading—the art of loading third-party apps from a location outside of the official application store for that device. Note that sideloading can occur in several ways: by direct Internet connection (usually disabled by default); by connecting to a second mobile device via USB OTG (USB On-The-Go) or Bluetooth; by copying apps directly from a microSD card; or via tethering to a PC or Mac. Finally, application control becomes easier as well. Applications can be installed, uninstalled, updated, and secured from that central location. Even devices’ removable storage (often USB-based) can be manipulated—as long as the removable storage is currently connected to the device.
User acceptance of BYOD is mixed in its reactions. Some employees like the idea of using their own device (which they might not have been allowed to use at work previously) and not having to train on a separate work computer. However, some employees believe that BYOD is just a way to move computing costs from the company to the user, and the level of trust is low. Around 2013, studies showed that the perception of BYOD (and MDM solutions) varied. Approximately 40 percent of users believe that their employer can see personal information on their mobile devices. This brings up a variety of legal concerns, such as the right to privacy. Companies that offer BYOD MDM solutions counter this by drawing a clear line in the sand, defining exactly what employers can see (for example, corporate e-mail) and what they can’t see (such as personal texts). In general, these companies try to protect the privacy of the individual. Many organizations will write clear privacy policies that define, if necessary, selective wipes of secure corporate data while protecting personal data. As of the writing of this book, the technology is not perfect, and there will be some debate over time as to its long-term viability.
Part of the debate includes some additional concerns; for example, additional legal concerns exist about such things as employee misconduct and fraud. As of the writing of this book, legal precedents are being set, and the general consensus is gravitating toward a separation of personal and organizational data. Anything found that could possibly implicate an employee of wrongdoing would have to be found in the organizational portion of the data. From a forensics point of view, however, and because the device can’t be split in two, if any potential wrongdoing is investigated, the device would need to be confiscated for analysis.
Most employees (of all age groups) are also concerned with how on-board devices (such as the on-board camera) can be used against them with or without their knowledge. Companies that offer BYOD solutions tend to refer to the camera (and photos/video taken) as part of the personal area of the device. However, those same companies will include GPS location as something the company can see, but this can be linked to a corporate login, with GPS tracking the user only when the user is logged in. Onboarding and offboarding in general are another concern. Essentially, onboarding is when the security administrator takes control of the device temporarily to configure it, update it, and perhaps monitor it, and offboarding is when the security administrator relinquishes control of the device when finished with it. It brings up some questions for the employee: When does it happen? How long does it last? How will my device be affected? Are there any architectural/infrastructural concerns? For example, will the BYOD solution change the core files of my device? Will an update done by a person when at home render the device inactive the next day at work? That’s just the tip of the iceberg when it comes to questions and concerns about BYOD. The best course of action is for an organization to set firm policies about all of these topics.
Policies that need to be instituted include an acceptable use policy, a data ownership policy, and a support ownership policy. In essence, these define what a user is allowed to do with the device (during work hours), who owns what data and how that data is separated, and under what scenarios the organization takes care of technical support for the device as opposed to the user. We’ll talk more about policies such as these in Chapter 18.
To help secure the mobile devices in a BYOD enterprise environment, some third-party providers offer: embedded certificate authority for managing devices and user identify; sophisticated posture monitoring and automated policy workflow so non-compliant devices do not get enterprise access; and certificate-based security to secure e-mail and reduce the chance of data loss.
Table 3-1 summarizes the mobile security techniques we covered in this section. With a mixture of user adherence to corporate policies, the workplace respecting the user’s right to privacy, and a strong security plan, BYOD can be a success.

Table 3-1 Summary of Mobile Device Security
Mobile Device Security Topic |
Countermeasure |
Malware |
Update device to latest version (or point release for the current version). Use security suites and AV software. Enable them if preloaded on the device and update regularly. Train users to carefully screen e-mail and selectively access websites. Be careful of social networks and third-party apps. |
Botnets & DDoS |
Download apps from a legitimate source. If BYOD is in place, use company-approved apps. Refrain from “rooting” or “jailbreaking” the device. Have data backed up in case the device becomes part of a botnet and has to be wiped. |
SIM cloning |
Use V2 and newer cards with strong encryption algorithms. |
Wireless attacks |
Use a strong password for the wireless network. Turn off unnecessary wireless features such as mobile hotspot, tethering, and so on. Disable Bluetooth if not in use for long periods of time (also conserves battery). Set device to undiscoverable. |
Theft |
Utilize data and voice encryption (especially in BYOD implementations). Implement lockout, remote locator, and remote wipe programs. Limit the amount of confidential information stored on the device. Use screen locks and complex passwords. |
Application security |
Use encryption from reputable providers. Use anti-malware endpoint protection platforms. Utilize non-transitive trusts between networks and apps. White-list applications. Disable geotagging. |
BYOD concerns |
Implement storage segmentation. Utilize an MDM solution. Create and implement clear policies that the organization and user must adhere to. Consider CYOD or COPE as opposed to the traditional BYOD method. |
Chapter Summary
A good security administrator is proactive. Preventing the threats discussed in this chapter requires updating systems and applications, and possibly redesigning networks and systems from the ground up. It also means using firewalls, host-based intrusion detection systems (HIDSs), and data loss prevention (DLP) systems. It requires in-depth configuration of applications, filtering, and secure policies. And of course, this all signifies a need for user training.
Software is not the only place to increase security. Hardware can be physically protected, and firmware such as the BIOS should be secured as well. As mentioned, the most important thing to a company (technologically speaking) is its data. So, the securing of all types of storage devices, especially removable storage, is paramount. This can be done in a physical manner and in a logical manner by utilizing hardware security modules (HSMs) and encryption, respectively.
A computer is a computer. It doesn’t matter if it’s a PC from 1986 or a mobile device from this year. All computers need to be secured using the same principles and policies. However, historically mobile devices have tended to fall through the cracks. So, companies have really started gearing up the security for these devices. In most organizations it is not feasible to stop a person from bringing their smartphone into work. Some organizations have decided to embrace this practice and benefit from it with a policy of bringing in your own device (BYOD) to be used for work purposes in addition to personal. While this creates a whole slew of new security considerations, some organizations are implementing BYOD and CYOD successfully by creating a well-defined demarcation point between the user’s data and the organization’s. By instituting this concept, along with a mobile device management (MDM) solution and strong policies for theft, wireless attacks, and application security, mobile devices can survive and thrive in the enterprise or small office, yet remain safe and accessible for personal use.
Many of the topics we discussed in this chapter, such as encryption and policies, will be covered in more depth as we progress throughout the book. You will find that the upcoming chapters tend to build upon this and the previous chapter. Be sure to review these chapters carefully before continuing with the book.
Chapter Review Activities
Use the features in this section to study and review the topics in this chapter.
Review Key Topics
Review the most important topics in the chapter, noted with the Key Topic icon in the outer margin of the page. Table 3-2 lists a reference of these key topics and the page number on which each is found.

Table 3-2 Key Topics for Chapter 3
Key Topic Element |
Description |
Page Number |
BIOS and drive lock passwords |
||
BitLocker configuration settings window |
||
Summary of mobile device security |
Define Key Terms
Define the following key terms from this chapter, and check your answers in the glossary:
host-based intrusion detection system (HIDS), personal firewall, pop-up blocker, ad filtering, content filters, root of trust, measured boot, attestation, removable media controls, high availability, self-encrypting drive (SED), hardware security module (HSM), bluejacking, bluesnarfing, transitive trust, application whitelisting, application blacklisting, storage segmentation, mobile device management (MDM), sideloading
Complete the Real-World Scenarios
Complete the Real-World Scenarios found on the companion website (www.pearsonitcertification.com/title/9780789758996). You will find a PDF containing the scenario and questions, and also supporting videos and simulations.
Review Questions
Answer the following review questions. Check your answers with the correct answers that follow.
1. What are some of the drawbacks to using a HIDS instead of a NIDS on a server? (Select the two best answers.)
A. A HIDS may use a lot of resources, which can slow server performance.
B. A HIDS cannot detect operating system attacks.
C. A HIDS has a low level of detection of operating system attacks.
D. A HIDS cannot detect network attacks.
2. What are two ways to secure the computer within the BIOS? (Select the two best answers.)
A. Configure a supervisor password.
B. Turn on BIOS shadowing.
C. Flash the BIOS.
D. Set the hard drive first in the boot order.
3. What are the two ways in which you can stop employees from using USB flash drives? (Select the two best answers.)
A. Utilize RBAC.
B. Disable USB devices in the BIOS.
C. Disable the USB root hub.
D. Enable MAC filtering.
4. Which of the following are Bluetooth threats? (Select the two best answers.)
A. Bluesnarfing
B. Blue bearding
C. Bluejacking
D. Distributed denial-of-service
5. To mitigate risks when users access company e-mail with their smartphone, what security policy should be implemented?
A. Data connection capabilities should be disabled.
B. A password should be set on the smartphone.
C. Smartphone data should be encrypted.
D. Smartphones should be only for company use.
6. Your manager wants you to implement a type of intrusion detection system (IDS) that can be matched to certain types of traffic patterns. What kind of IDS is this?
A. Anomaly-based IDS
B. Signature-based IDS
C. Behavior-based IDS
D. Heuristic-based IDS
7. You are the security administrator for your organization. You want to ensure the confidentiality of data on mobile devices. What is the best solution?
A. Device encryption
B. Remote wipe
C. Screen locks
D. AV software
8. You are tasked with implementing a solution that encrypts the CEO’s laptop. However, you are not allowed to purchase additional hardware or software. Which of the following solutions should you implement?
A. HSM
B. TPM
C. HIDS
D. USB encryption
9. A smartphone has been lost. You need to ensure 100% that no data can be retrieved from it. What should you do?
A. Remote wipe
B. GPS tracking
C. Implement encryption
D. Turn on screen locks
10. Which of the following is a concern based on a user taking pictures with a smartphone?
A. Application whitelisting
B. Geotagging
C. BYOD
D. MDM
11. A smartphone is an easy target for theft. Which of the following are the best methods to protect the confidential data on the device? (Select the two best answers.)
A. Remote wipe
B. E-mail password
C. GPS
D. Tethering
E. Encryption
F. Screen lock
12. Carl is the security administrator for a transportation company. Which of the following should he encrypt to protect the data on a smartphone? (Select the two best answers.)
A. Public keys
B. Internal memory
C. Master boot record (MBR)
D. Steganographic images
E. Removable memory cards
13. Which of the following is an advantage of implementing individual file encryption on a hard drive that already uses whole disk encryption?
A. Individually encrypted files will remain encrypted if they are copied to external drives.
B. It reduces the processing overhead necessary to access encrypted files.
C. NTFS permissions remain intact when files are copied to an external drive.
D. Double encryption doubles the bit strength of the encrypted file.
14. You oversee compliance with financial regulations for credit card transactions. You need to block out certain ports on the individual computers that do these transactions. What should you implement to best achieve your goal?
A. HIPS
B. Antivirus updates
C. Host-based firewall
D. NIDS
15. Which of the following would most likely be considered for DLP?
A. Proxy server
B. Print server
C. USB mass storage device
D. Application server content
Answers and Explanations
1. A and D. Host-based intrusion detection systems (HIDSs) run within the operating system of a computer. Because of this, they can slow a computer’s performance. Most HIDS do not detect network attacks well (if at all). However, a HIDS can detect operating system attacks and will usually have a high level of detection for those attacks.
2. A and D. Configuring a supervisor password in the BIOS disallows any other user to enter the BIOS and make changes. Setting the hard drive first in the BIOS boot order disables any other devices from being booted off, including floppy drives, optical drives, and USB flash drives. BIOS shadowing doesn’t have anything to do with computer security, and although flashing the BIOS may include some security updates, it’s not the best answer.
3. B and C. By disabling all USB devices in the BIOS, a user cannot use his flash drive. Also, the user cannot use the device if you disable the USB root hub within the operating system. RBAC, which stands for role-based access control, defines access to networks by the person’s role in the organization (we will cover this more later in the book). MAC filtering is a method of filtering out computers when they attempt to access the network (using the MAC addresses of those computers).
4. A and C. Bluesnarfing and bluejacking are the names of a couple of Bluetooth threats. Another attack could be aimed at a Bluetooth device’s discovery mode. To date there is no such thing as blue bearding, and a distributed denial-of-service attack uses multiple computers to attack one host.
5. B. A password should be set on the phone, and the phone should lock after a set period of time. When the user wants to use the phone again, the user should be prompted for a password. Disabling the data connection altogether would make access to e-mail impossible on the smartphone. Smartphone encryption of data is possible, but it could use a lot of processing power that may make it unfeasible. Whether the smartphone is used only for company use is up to the policies of the company.
6. B. When using an IDS, particular types of traffic patterns refer to signature-based IDS.
7. A. Device encryption is the best solution listed to protect the confidentiality of data. By encrypting the data, it makes it much more difficult for a malicious person to make use of the data. Screen locks are a good idea but are much easier to get past than encryption. Antivirus software will not stop an attacker from getting to the data once the mobile device has been stolen. Remote sanitization (remote wipe) doesn’t keep the data confidential; it removes it altogether! While this could be considered a type of confidentiality, it would only be so if a good backup plan was instituted. Regardless, the best answer with confidentiality in mind is encryption. For example, if the device was simply lost, and was later found, it could be reused (as long as it wasn’t tampered with). But if the device was sanitized, it would have to be reloaded and reconfigured before being used again.
8. B. A TPM, or trusted platform module, is a chip that resides on the motherboard of the laptop. It generates cryptographic keys that allow the entire disk to be encrypted, as in full disk encryption (FDE). Hardware security modules (HSMs) and USB encryption require additional hardware. A host-based intrusion detection system requires either additional software or hardware.
9. A. If the device has been lost and you need to be 100% sure that data cannot be retrieved from it, then you should remotely sanitize (or remotely “wipe”) the device. This removes all data to the point where it cannot be reconstructed by normal means. GPS tracking might find the device, but as time is spent tracking and acquiring the device, the data could be stolen. Encryption is a good idea, but over time encryption can be deciphered. Screen locks can be easily circumvented.
10. B. Geotagging is a concern based on a user taking pictures with a mobile device such as a smartphone. This is because the act of geotagging utilizes GPS, which can give away the location of the user. Application whitelisting is when there is an approved list of applications for use by mobile devices. Usually implemented as a policy, if the mobile device attempts to open an app that is not on the list, the process will fail, or the system will ask for proof of administrative identity. BYOD stands for bring your own device, a technological concept where organizations allow employees to bring their personal mobile devices to work and use them for work purposes. MDM stands for mobile device management, a system that enables a security administrator to configure, update, and secure multiple mobile devices from a central location.
11. A and E. Remote wipe and encryption are the best methods to protect a stolen device’s confidential or sensitive information. GPS can help to locate a device, but it can also be a security vulnerability in general; this will depend on the scenario in which the mobile device is used. Passwords should never be e-mailed and should not be associated with e-mail. Tethering is when a mobile device is connected to another computer (usually via USB) so that the other computer can share Internet access, or other similar sharing functionality in one direction or the other. This is great as far as functionality goes, but more often than not can be a security vulnerability. Screen locks are a decent method of reducing the chance of login by the average person, but they are not much of a deterrent for the persistent attacker.
12. B and E. When encrypting a smartphone, the security administrator should encrypt internal memory and any long-term storage such as removable media cards. The admin must remember that data can be stored on both. Public keys are already encrypted; it is part of their inherent nature. Smartphones don’t necessarily use an MBR the way Windows computers do, but regardless, if the internal memory has been encrypted, any boot sector should be secured. Images based on steganography, by their very nature, are encrypted through obfuscation. It is different from typical data encryption, but it’s a type of cryptography nonetheless.
13. A. By implementing individual file encryption (such as EFS) on files that are stored on a disk encrypted with whole disk encryption, the files will remain encrypted (through EFS) even if they are copied to a separate drive that does not use whole disk encryption. However, running two types of encryption will usually increase processing overhead, not reduce it. NTFS permissions aren’t relevant here; however, if files are copied to an external drive, those files by default lose their NTFS permissions and inherit new permissions from the parent folder on the new drive. We’ll discuss NTFS permissions more in Chapter 11. We shouldn’t call this double encryption—rather, the files are encrypted twice separately. The bit strength is not cumulative in this example, but there are two layers of encryption, which is an example of defense in depth and security layering.
14. C. To meet regulations, a properly configured host-based firewall will be required on the computers that will be transacting business by credit card over the Internet. All of the other answers—antivirus updates, NIDS, and HIPS—are good ideas to secure the system (and/or network), but they do not address the core issue of filtering ports, which is the primary purpose of the firewall. Also, a network-based firewall will often not be secure enough to meet regulations, thus the need for the extra layer of protection on the individual computers.
15. C. Of the answers listed, the USB mass storage device would be the most likely asset to be considered for data loss prevention (DLP). It’s the only device listed in the answers that should have any real organizational data! A proxy server temporarily caches such data as HTTP and FTP. A print server forwards printed documents to the correct printer (again the data is usually held temporarily). An application server contains programs, but usually doesn’t store organizational data files. It’s the devices and computers that store actual company data files that we are primarily concerned with.