Chapter 9. Securing Network Media and Devices
This chapter covers the following subjects:
![]() Securing Wired Networks and Devices: In this section, you learn about how to reduce the risk of attack to your wired networks and the central connecting devices that control access to those networks. Concepts covered include security for common network devices such as SOHO routers and firewalls, and how to secure twisted-pair, fiber-optic, and coaxial cables.
Securing Wired Networks and Devices: In this section, you learn about how to reduce the risk of attack to your wired networks and the central connecting devices that control access to those networks. Concepts covered include security for common network devices such as SOHO routers and firewalls, and how to secure twisted-pair, fiber-optic, and coaxial cables.
![]() Securing Wireless Networks: Here, we delve into wireless networks, how you can secure your wireless access points and protect your wireless network from intruders, inside or outside the building. Wireless concepts covered include Wi-Fi security, Bluetooth security, and security of other over-the-air technologies such as RFID.
Securing Wireless Networks: Here, we delve into wireless networks, how you can secure your wireless access points and protect your wireless network from intruders, inside or outside the building. Wireless concepts covered include Wi-Fi security, Bluetooth security, and security of other over-the-air technologies such as RFID.
Imagine if you will that you are in charge of securing your organization’s wired and wireless networks, and all the devices associated with them. There are several questions you should ask yourself: What kind of cables does your network use, what are the vulnerabilities of those cables, and how can they be secured? What are your future cabling plans? Do you have wireless networks, and if so, how can you protect data that is flinging through the air? How many devices can be accessed either from users on the network or remotely? And are there any older devices that need to be updated, or simply removed?
Verifying that all network devices, cables, and other mediums are secure might sound like a daunting task at first, but let’s take it step by step and discuss how this can be done. We begin with wired networks, cables, and the devices you might find on a wired network; then we move onto wireless transmissions. At the end of the chapter, we examine a final piece of network documentation that sums up many of the security precautions we implemented in Chapters 6 through 9.
Foundation Topics
Securing Wired Networks and Devices
Implementing a security plan for your wired network is critical. In Chapter 6, “Network Design Elements,” we talked about the design elements of your network. In Chapter 7, “Networking Protocols and Threats,” we discussed the possible threats to those design elements and to the computers and servers on the network. In Chapter 8, “Network Perimeter Security,” we talked about some of the security tools, such as firewalls, that could be used to protect the network. But what connects it all together? Usually the wired network. Now let’s get into the nitty-gritty of the wired network. Not only are the devices wired to the network targets for attack, but the wires could be targets as well. Some attacks could come from inside the network, whereas other attacks could be external. Let’s start with some of the common vulnerabilities to network devices.
Network Device Vulnerabilities
Devices that reside on your network might include switches, routers, firewalls, NIDS/NIPS appliances, and more. Each of these devices can be vulnerable in its default state. Most devices are sold with simple default accounts and blank or weak passwords. In some cases, it’s easy for users to escalate their privileges to gain access to resources that they normally would not have access to. Some devices and computers can be the victim of backdoors that programmers did not remove, or forgot to remove, which enable access for attackers. And of course, a good network administrator will protect against network attacks such as denial-of-service. Let’s go through each of these one by one and show how to protect against these vulnerabilities to help mitigate risk.
Default Accounts
Many of the networking devices available to organizations are initially installed with a default set of user credentials; this is the default account. The default account might be called administrator, or admin, or something else similar. If possible, this default account should be changed to a new name, because attackers are aware of default account names. This also applies to computers and servers, as we mentioned in Chapter 4, “OS Hardening and Virtualization.” By renaming the default account, or by removing it altogether, you add a layer of security that makes it more difficult for an attacker to figure out which account has administrative access to the device. One example of this is the SOHO router. Historically, these devices were set up by default with the username admin and a blank password. This is one of the first things you should change before you connect it to the Internet—that is, if the device doesn’t prompt you to do it automatically. And a lot of these devices allow a separate user account as well, which might have varying levels of access depending on the device. This should either be set with a complex password or be disabled altogether.
If any guest accounts exist, it is recommended that you disable these accounts. And again, this applies to network devices and computers. The guest account will usually not be enabled, but you should always check this just in case. Of course, more important than the account name or the username is the password. If you have to use a guest account, set a complex password!
Weak Passwords
Passwords should be as complex as possible. A weak password can be cracked by an attacker in a short time. Many network devices come stock with no password at all; so, your first order of business should be to create a complex password. It is common knowledge that a strong password is important for protecting a user account, whether the account is with a bank, at work, or elsewhere. The same goes for network devices. But what is a strong password? Many organizations define a strong password as a password with at least eight (even ten) characters, including at least one uppercase letter, one number, and one special character. The best passwords have the same requirements but are 15 characters or more. Many password checker programs are available on the Internet; for example, the Password Meter or Kaspersky’s password checker.
Let’s look at Table 9-1, which gives some examples of weak passwords and strong passwords based on the criteria of a typical password checker.
Table 9-1 Weak, Strong, and Stronger Passwords
| Password | Strength of Password |
| Prowse | Weak |
| DavidProwse | Medium (also known as “good”) |
| |ocrIan7 | Strong |
| This1sV#ryS3cure | Very strong (also known as “best”) |
Note
Be aware that password checking programs can change their criteria over time. Also, never actually use a password that was entered into a checker! The purpose of the checker is to demonstrate the strength of a password so that you know what criteria to use for other passwords in the future.
The first password in Table 9-1 is weak; even though it has an uppercase P, it is only 6 characters in length. The second password is only medium strength; it has 11 characters but only 2 uppercase characters, and nothing else is special about it. However, notice the third password is using the pipe symbol instead of the letter L. This is a special character that shares the backslash key on the keyboard. Because the third password has a special character, an uppercase I, and a number, and is 8 characters in total, it is considered to be a strong password by the password checker. In the last password, we have 16 characters, including 3 uppercase letters, 2 numbers, and 1 special character. These methods make for an extremely strong password that would take a powerful desktop computer many years to crack.
Employ elastic thinking! Remember—a strong password this year might be a weak password next year. That’s because computers increase in power and efficiency all the time (see Moore’s Law). And let’s not forget to mention that a botnet can use the collective power of many systems to brute-force a password much faster than one system could. That’s something to keep in mind if you are the security admin for an organization that has high-profile employees.
Privilege Escalation
When an attacker exploits a bug or other flaw in an operating system or application in order to gain protected access to resources, it is known as privilege escalation. The original developer does not intend for the attacker to gain higher levels of access, but probably doesn’t enforce a need-to-know policy properly and/or hasn’t validated the code of the application appropriately. This technique is used by attackers to gain access to protected areas of operating systems, or to applications; for example, if a particular user can read another user’s e-mail without authorization. Other programs, such as Cisco Unified Communications Manager (CallManager), have also been the victim of privilege escalations, although patches are regularly released if issues like these are discovered. Buffer overflows are used on Windows computers to elevate privileges as well. To bypass digital rights management (DRM) on games and music, attackers use a method known as jailbreaking, another type of privilege escalation, most commonly found on mobile devices. Malware also attempts to exploit privilege escalation vulnerabilities, if any exist on the system. Privilege escalation can also be attempted on network devices. Generally, the fix for this is simply to update the device and to check on a regular basis if any updates are available. For example, a typical SOHO router has a user account and an admin account. If a device like this isn’t properly updated, an attacker can take advantage of a bug in the firmware to elevate the privileges of the user account. Couple this with the fact that a person forgot to put a password on the user account (or disable it) and your network could be in for some “fun.” It is also possible on some devices to encrypt the firmware component. Following are a couple different types of privilege escalation:
![]() Vertical privilege escalation: When a lower privileged user accesses functions reserved for higher privileged users; for example, if a standard user can access functions of an administrator. This is also known as privilege elevation and is the most common description. To protect against this, update the network device firmware. In the case of an operating system, it should again be updated, and usage of some type of access control system is also advisable; for example, User Account Control (UAC).
Vertical privilege escalation: When a lower privileged user accesses functions reserved for higher privileged users; for example, if a standard user can access functions of an administrator. This is also known as privilege elevation and is the most common description. To protect against this, update the network device firmware. In the case of an operating system, it should again be updated, and usage of some type of access control system is also advisable; for example, User Account Control (UAC).
![]() Horizontal privilege escalation: When a normal user accesses functions or content reserved for other normal users; for example, if one user reads another’s e-mail. This can be done through hacking or by a person walking over to other people’s computers and simply reading their e-mail! Always have your users lock their computer (or log off) when they are not physically at their desk!
Horizontal privilege escalation: When a normal user accesses functions or content reserved for other normal users; for example, if one user reads another’s e-mail. This can be done through hacking or by a person walking over to other people’s computers and simply reading their e-mail! Always have your users lock their computer (or log off) when they are not physically at their desk!
There is also privilege de-escalation, when high privileged but segregated users can downgrade their access level to access normal users’ functions. Sneaky admins can attempt this to glean confidential information from an organization. It’s a two-way street when it comes to security; you should think three-dimensionally when securing your network!
Back Doors
A backdoor is a way of bypassing normal authentication in a system, securing illegal remote access to a computer, or gaining access to a cryptosystem through circumvention of the normal system of rules.
As mentioned in Chapter 2, “Computer Security Systems Part I,” backdoors were originally used by developers as a legitimate way of accessing an application, but quickly became known to attackers and utilized as an illegitimate means of gaining access to the system. The beauty of the backdoor attack is that the attacker can easily remain undetected. Backdoors can take the form of programs such as remote access Trojans (RATs), or could be accessed via a rootkit.
Backdoors are less common nowadays, because their practice is usually discouraged by software manufacturers and by makers of network devices. So, as long as the design of the application or device was secure (and tested), attackers should not be able to gain access via the backdoor.
Network Attacks
Denial-of-service and many other network attacks can wreak havoc on your network devices. It is important to keep abreast of these latest attacks and to verify that all systems and network devices are updated accordingly. Use smart network intrusion prevention systems (NIPSs) to identify new attacks and prevent them from causing trouble on your networks. For more information on denial-of-service attacks and other types of network attacks, see the section “Malicious Attacks” in Chapter 7.
Other Network Device Considerations
Some network administrators use remote ports on their network devices to remotely administer those devices. These ports can be used maliciously as well. If the remote port is not to be used, it should be disabled. If it is to be used, a strong authentication system should be employed, and data encryption should be considered. This applies to routers, switches, servers, and PBX equipment. For more specific ways to protect your network devices, see the section “Network Design” in Chapter 6.
In some cases, a network administrator uses the Telnet program to access network equipment remotely from another site or from within the local area network. This practice should be shunned because Telnet by default is not secure; it does not encrypt data, including passwords, and default implementations of Telnet have no authentication scheme that ensures that communications will not be intercepted. In addition, most Telnet programs have other vulnerabilities and risk associated with them. Instead of using Telnet, administrators should opt for another protocol such as Secure Shell (SSH).
Cable Media Vulnerabilities
The most commonly overlooked item in a network is the cabling. The entire cabling infrastructure (or cabling plant) includes the cables themselves, network jacks, patch panels, punch blocks, and so on. You need to think about what types of cabling you are using, what vulnerabilities they have, and how to combat those vulnerabilities in an attempt to reduce risk. Following are three types of cabling that you might have implemented in your network:
![]() Twisted-pair: A copper-based cable with four pairs of wires (for a total of eight wires), each of which is twisted together along the length of the cable. It is the most common type of network cable; it sends electrical signals to transfer data and uses RJ45 plugs to connect to ports on hosts. The most common security problem with twisted-pair cable is crosstalk, which we discuss later.
Twisted-pair: A copper-based cable with four pairs of wires (for a total of eight wires), each of which is twisted together along the length of the cable. It is the most common type of network cable; it sends electrical signals to transfer data and uses RJ45 plugs to connect to ports on hosts. The most common security problem with twisted-pair cable is crosstalk, which we discuss later.
![]() Fiber-optic: A glass/plastic-based cable that sends light (photons) instead of electricity. It is composed of one or more thin strands known as fibers that transfer the data. Generally, this is the most secure type of cable that can be used in a network. It is not susceptible to EMI, RFI, or data emanations (all of which are discussed shortly) and is the least susceptible cable to wiretapping. The two main categories of fiber-optic cables are single-mode (for the longest distances) and multimode (for shorter distances but longer than twisted-pair). Examples of places where fiber-optic cables are used include high-bandwidth networking technologies such as Fibre Channel (FCoE and FCIP) that use SC and LC connectors.
Fiber-optic: A glass/plastic-based cable that sends light (photons) instead of electricity. It is composed of one or more thin strands known as fibers that transfer the data. Generally, this is the most secure type of cable that can be used in a network. It is not susceptible to EMI, RFI, or data emanations (all of which are discussed shortly) and is the least susceptible cable to wiretapping. The two main categories of fiber-optic cables are single-mode (for the longest distances) and multimode (for shorter distances but longer than twisted-pair). Examples of places where fiber-optic cables are used include high-bandwidth networking technologies such as Fibre Channel (FCoE and FCIP) that use SC and LC connectors.
![]() Coaxial: A less used copper-based cable that has a single copper core. Although not used for connections to hosts anymore, you might see it used with special connections, perhaps for the Internet or for video. In smaller companies’ networks, it is common to see an RG-6 cable used for the Internet connection. The most common security risk with coaxial cable is data emanation, which we discuss later.
Coaxial: A less used copper-based cable that has a single copper core. Although not used for connections to hosts anymore, you might see it used with special connections, perhaps for the Internet or for video. In smaller companies’ networks, it is common to see an RG-6 cable used for the Internet connection. The most common security risk with coaxial cable is data emanation, which we discuss later.
Each of these cables has its own inherent vulnerabilities; let’s talk about a few of these now.
Interference
Interference is anything that disrupts or modifies a signal traveling along a wire. There are many types of interference, but you should know about only a few for the exam, including the following:
![]() Electromagnetic interference (EMI): A disturbance that can affect electrical circuits, devices, and cables due to electromagnetic conduction or radiation. Just about any type of electrical device can cause EMI: TVs, microwaves, air-conditioning units, motors, unshielded electrical lines, and so on. Copper-based cables and network devices should be kept away from these electrical devices if at all possible. If not possible, shielded cables can be used, for example, shielded twisted-pair (STP). Or the device that is emanating EMI can be shielded. For example, an air-conditioning unit could be boxed in with aluminum shielding in an attempt to keep the EMI generated by the AC unit’s motor to a minimum. In addition, electrical cables should be BX (encased in metal) and not Romex (not encased in metal); most municipalities require this to meet industrial and office space building code. EMI can also be used in a mischievous manner, known as radio jamming. But the methods listed here can help defend against this as well.
Electromagnetic interference (EMI): A disturbance that can affect electrical circuits, devices, and cables due to electromagnetic conduction or radiation. Just about any type of electrical device can cause EMI: TVs, microwaves, air-conditioning units, motors, unshielded electrical lines, and so on. Copper-based cables and network devices should be kept away from these electrical devices if at all possible. If not possible, shielded cables can be used, for example, shielded twisted-pair (STP). Or the device that is emanating EMI can be shielded. For example, an air-conditioning unit could be boxed in with aluminum shielding in an attempt to keep the EMI generated by the AC unit’s motor to a minimum. In addition, electrical cables should be BX (encased in metal) and not Romex (not encased in metal); most municipalities require this to meet industrial and office space building code. EMI can also be used in a mischievous manner, known as radio jamming. But the methods listed here can help defend against this as well.
![]() Radio frequency interference (RFI): Interference that can come from AM/FM transmissions and cell towers. It is often considered to be part of the EMI family and is sometimes referred to as EMI. The closer a business is to one of these towers, the greater the chance of interference. The methods mentioned for EMI can be employed to help defend against RFI. In addition, filters can be installed on the network to eliminate the signal frequency broadcast by a radio tower, though this usually does not affect standard-wired Ethernet networks. Wireless signals from wireless networks and cell phones can interfere with speakers and other devices; try to keep speakers and monitors away from cell phones and wireless network adapters. Try to keep wireless access points away from computers, printers, monitors, and speakers; and switches, routers, and other network equipment.
Radio frequency interference (RFI): Interference that can come from AM/FM transmissions and cell towers. It is often considered to be part of the EMI family and is sometimes referred to as EMI. The closer a business is to one of these towers, the greater the chance of interference. The methods mentioned for EMI can be employed to help defend against RFI. In addition, filters can be installed on the network to eliminate the signal frequency broadcast by a radio tower, though this usually does not affect standard-wired Ethernet networks. Wireless signals from wireless networks and cell phones can interfere with speakers and other devices; try to keep speakers and monitors away from cell phones and wireless network adapters. Try to keep wireless access points away from computers, printers, monitors, and speakers; and switches, routers, and other network equipment.
Another common type of interference is crosstalk, discussed next.
Crosstalk
Crosstalk is when a signal transmitted on one copper wire creates an undesired effect on another wire; the signal “bleeds” over, so to speak. This first occurred when telephone lines were placed in close proximity to each other. Because the phone lines were so close, the signal could jump from one line to the next intermittently. If you have ever heard another conversation while talking on your home phone (not cell phones mind you) you have been the victim of crosstalk. This can happen with connections made by a modem as well, causing considerable havoc on the data transfer.
Note
With cell phones, crosstalk is also known as co-channel interference, or CCI.
To combat crosstalk, you can use twisted-pair cable. This helps when regular analog signals are sent across the wires and applies only to standard POTS connections and computer modems that use POTS connections. The beauty of the twists in twisted-pair cabling is that the signal has less chance of leaking to other wires, in comparison to straight wires next to each other and bundled together. If the signals are digital—for example, Ethernet data transfers or Voice over IP—you already have an environment less susceptible to crosstalk, in comparison to an analog environment. Data can still bleed over to other wires, but it is less common because the twists of the wires have been precisely calculated by the manufacturer. Sometimes crosstalk occurs due to bunches of cables bundled too tightly, which could also cause crimping or other damage to the cable. If this is the case, a trusty continuity tester will let you know which cable has failed; normally this will have to be replaced. When it comes to twisted-pair cabling, crosstalk is broken down into two categories: near end crosstalk (NEXT) and far end crosstalk (FEXT). NEXT is when measured interference occurs between two pairs in a single cable, measured on the cable end nearest the transmitter. FEXT is when like interference occurs but is measured at the cable end farthest from the transmitter.
If crosstalk is still a problem, even though twisted-pair cable has been employed and digital data transmissions have been implemented, shielded twisted-pair (STP) could be used. Although twisting individual pairs can minimize crosstalk between wire pairs within a cable, shielding an entire cable minimizes crosstalk between cables. Normally, companies opt for regular twisted-pair cabling, which is unshielded (also known as UTP), but sometimes, too much interference exists in the environment to send data effectively, and STP must be utilized.
Data Emanation
Data emanation (or signal emanation) is the electromagnetic (EM) field generated by a network cable or network device, which can be manipulated to eavesdrop on conversations or to steal data. Data emanation is sometimes also referred to as eavesdropping, although this is not accurate.
Data emanation is the most commonly seen security risk when using coaxial cable, depending on the type of coaxial cable, but can also be a security risk for other copper-based cables. There are various ways to tap into these EM fields to get unauthorized access to confidential data. To alleviate the situation, there are several solutions. For example, you could use shielded cabling or run the cabling through metal conduits. You could also use electromagnetic shielding on devices that might be emanating an electromagnetic field. This could be done on a small scale by shielding the single device or on a larger scale by shielding an entire room, perhaps a server room; this would be an example of a Faraday cage. If an entire room is shielded, electromagnetic energy cannot pass through the walls in either direction. So, if a person attempts to use a cell phone inside the cage, it will not function properly, because the signal cannot go beyond the cage walls. More important, devices such as cell phones, motors, and wireless access points that create electromagnetic fields and are outside the cage cannot disrupt electromagnetic-sensitive devices that reside inside the cage. Server rooms and cabling should be protected in some way, especially if the data that travels through them is confidential. Studies are constantly done about signal emanations and how to contain them. A group of standards known as TEMPEST refers to the investigations of conducted emissions from electrical and mechanical devices, which could be compromising to an organization.
Tapping into Data and Conversations
This is a huge subject, and we could talk about it for days without scratching the surface. One item of note: ANY system can be tapped or hacked. It’s just the lengths you must go to that can vary; it depends on the network, cabling, and security precautions already in place.
The term “tapping” originates from the days when an attacker would use a tool (such as a vampire tap) to physically bite into a wire or cable so that the attacker could monitor the network. Today, “tapping” takes on a whole new meaning. Wiretapping can mean any one of the following and more:
![]() Connecting to a punch block, or RJ11 jack with a butt set: A butt set (or lineman’s handset) is a device that looks similar to a phone but has alligator clips that can connect to the various terminals used by phone equipment, enabling a person to test a new line or listen in to a conversation. The device is used primarily by telecommunications technicians but can obviously be used for malicious purposes as well. There are analog versions of this device (for POTS systems) and digital versions (for digital systems such as VoIP and so on) that act as packet capturing devices (sniffers). To protect against this, keep all punch blocks and other phone equipment in a physically secure server room or wiring closet. Although expensive, there are also lockable RJ11 jacks, but it would probably be less costly to install a network of cameras in the building, especially if your organization wants them for other purposes as well.
Connecting to a punch block, or RJ11 jack with a butt set: A butt set (or lineman’s handset) is a device that looks similar to a phone but has alligator clips that can connect to the various terminals used by phone equipment, enabling a person to test a new line or listen in to a conversation. The device is used primarily by telecommunications technicians but can obviously be used for malicious purposes as well. There are analog versions of this device (for POTS systems) and digital versions (for digital systems such as VoIP and so on) that act as packet capturing devices (sniffers). To protect against this, keep all punch blocks and other phone equipment in a physically secure server room or wiring closet. Although expensive, there are also lockable RJ11 jacks, but it would probably be less costly to install a network of cameras in the building, especially if your organization wants them for other purposes as well.
![]() Plugging in to an open port of a twisted-pair network: This could be either at an RJ45 wall plate or in the server room (not as easy) at an open port of a hub or switch. Unused ports, whether on a hub or switch or at a computer station’s RJ45 jack, should be disabled. Also, central connecting devices such as hubs and switches should be locked in the server room, and only properly authenticated individuals should have access.
Plugging in to an open port of a twisted-pair network: This could be either at an RJ45 wall plate or in the server room (not as easy) at an open port of a hub or switch. Unused ports, whether on a hub or switch or at a computer station’s RJ45 jack, should be disabled. Also, central connecting devices such as hubs and switches should be locked in the server room, and only properly authenticated individuals should have access.
![]() Splitting the wires of a twisted-pair connection: This can be done anywhere along a cable but would disrupt communications for that individual computer or segment while it is being done. By cutting the twisted-pair cable and soldering a second twisted-pair cable to the appropriate wires (for example, Ethernet 568B networks use the orange and green pairs of wires by default), a person could eavesdrop on all communications on that segment. Cables should not be exposed if at all possible. Cable runs should be above the drop ceiling and inside the walls, perhaps run in conduit. It is understandable that computers need to connect to RJ45 jacks by way of patch cables; if a computer suddenly loses its connection to the network, an alert can be sent to junior administrators, prompting them to investigate why it occurred.
Splitting the wires of a twisted-pair connection: This can be done anywhere along a cable but would disrupt communications for that individual computer or segment while it is being done. By cutting the twisted-pair cable and soldering a second twisted-pair cable to the appropriate wires (for example, Ethernet 568B networks use the orange and green pairs of wires by default), a person could eavesdrop on all communications on that segment. Cables should not be exposed if at all possible. Cable runs should be above the drop ceiling and inside the walls, perhaps run in conduit. It is understandable that computers need to connect to RJ45 jacks by way of patch cables; if a computer suddenly loses its connection to the network, an alert can be sent to junior administrators, prompting them to investigate why it occurred.
![]() Using a spectral analyzer to access data emanations: Spectral analyzers can measure the composition of electrical waveforms at specific frequencies (for example, 100 MHz, or 250 MHz on a twisted-pair network). These can also decode encrypted transmissions. These types of devices should not be allowed in the building (unless used by authorized personnel). A metal detector could be used at the entrance of the building, and again, video cameras can help detect this, and perhaps even prevent mischievous people from attempting to do so, just because they think they might be under surveillance.
Using a spectral analyzer to access data emanations: Spectral analyzers can measure the composition of electrical waveforms at specific frequencies (for example, 100 MHz, or 250 MHz on a twisted-pair network). These can also decode encrypted transmissions. These types of devices should not be allowed in the building (unless used by authorized personnel). A metal detector could be used at the entrance of the building, and again, video cameras can help detect this, and perhaps even prevent mischievous people from attempting to do so, just because they think they might be under surveillance.
![]() Using a passive optical splitter for fiber-optic networks: This is a more expensive device and would need access to a cable. Plus, the process of getting it to work is difficult. (And again, this would disrupt communications for a time.) The preceding listed methods apply to defending against this as well. Because it is difficult to implement an optical splitter properly, this could cause chromatic dispersion on the particular fiber segment. Chromatic dispersion (and subsequent loss of data) could also occur if the fiber-optic cable is too long. Administrators could monitor the network for dispersion and have alerts sent to them in the case that it occurs. The most common example of chromatic dispersion is the rainbow. For example, if light is sent through a prism, the light will be refracted (dispersed) into the rainbow of colors. Although not exactly how it would occur on a fiber-optic cable, if this were to happen, data transmissions would fail.
Using a passive optical splitter for fiber-optic networks: This is a more expensive device and would need access to a cable. Plus, the process of getting it to work is difficult. (And again, this would disrupt communications for a time.) The preceding listed methods apply to defending against this as well. Because it is difficult to implement an optical splitter properly, this could cause chromatic dispersion on the particular fiber segment. Chromatic dispersion (and subsequent loss of data) could also occur if the fiber-optic cable is too long. Administrators could monitor the network for dispersion and have alerts sent to them in the case that it occurs. The most common example of chromatic dispersion is the rainbow. For example, if light is sent through a prism, the light will be refracted (dispersed) into the rainbow of colors. Although not exactly how it would occur on a fiber-optic cable, if this were to happen, data transmissions would fail.
A quick word about wiring “closets.” Generally, a commercial office building will have two types of wiring frameworks. First, there are intermediate distribution frame (IDF) rooms, usually one per floor. These rooms are where all the cabling for that floor is terminated—for example, twisted-pair cables are punched down here, either to patch panels or punch blocks, depending on the architecture. All IDF rooms then connect (in one way or another) to the second type, the main distribution frame (MDF) room, often on the first floor or in the basement. The MDF is where circuits merge and connect out to external ISPs, and other network providers. Both types of rooms are vulnerable attack points. Historically, MDF rooms have been better protected than IDF rooms, but today organizations are increasing security on both and treating them the same way they would treat data centers or high-end server rooms. Basic security such as a door lock is not enough. (Watch some DEF CON videos for quick proof of that.) Security admins should consider methods such as multifactor authentication, possibly including biometrics, and active surveillance systems. We’ll discuss more about physical security in Chapter 10, “Physical Security and Authentication Models.” However, an attacker might try to exploit IDF and MDF vulnerabilities from within and from without. By connecting to SNMP-monitored systems, such as power distribution units (PDUs), UPSs, and environmental devices, an attacker can circumnavigate other security safeguards that might be in place. Consider the security implications of SNMP carefully. We’ll discuss that topic more in Chapter 13, “Monitoring and Auditing.”
Some organizations and government agencies require the use of a protected distribution system (PDS) for wired connections. These approved circuits use all of the techniques mentioned previously in this section to secure the unencrypted transmission of classified information. It is all-encompassing: cables, terminals, and other equipment, including safeguards for electrical, electromagnetic, and acoustical concerns.
Keep in mind that the Security+ exam does not go too far in depth for this subject, but realize that you might get a question on wiretapping, and remember that any network can be hacked! It is more common to attempt hacking into wireless networks. So, let’s delve into the basics of that immense subject next.
Securing Wireless Networks
Wireless networks pose a whole new set of problems for a network administrator. Wireless access points (WAPs) and wireless network adapters need to be secure from attackers that could be just about anywhere as long as they’re within range of the wireless network. Several points we cover can help you secure your WAP, wireless network adapters, and any other wireless devices. In this section, you learn how to watch out for wireless transmission vulnerabilities that you should be aware of, including Wi-Fi, Bluetooth, and RFID.
Wireless Access Point Vulnerabilities
The wireless access point is the central connecting device for wireless network adapters that might exist in PCs, laptops, handheld computers, mobile devices, and other computers. You need to secure any broadcasts that the WAP might make and verify that transmissions are encrypted with a strong encryption technique. It’s also important to watch out for rogue access points and round up any nomads on your network.
The Administration Interface
The first thing you should look at when it comes to WAPs is the administration interface, or console. The act of accessing the administration interface is sometimes referred to as “romming” into the access point. By default, most access points have a blank password or a simple and weak password (for example, “password” or “admin”). The first step you want to take is to access the administration interface and modify the password; change it to a complex password. Next, consider disabling remote administration if it is not necessary. Your organization might require it, but it depends on several factors. If you are dead set on leaving it enabled, be completely sure that the remote administration password is complex.
SSID Broadcast
The service set identifier (SSID) is one of several broadcasts that a WAP makes. It identifies the network and is the name of the WAP used by clients to connect to the wireless network. It is on by default. After all your clients have been connected to the wireless network, consider disabling the SSID broadcast. Though there will still be ways for attackers to get into your WAP, this at least provides a preliminary level of security. The average user cannot see the SSID and cannot connect to the wireless network. In the future if you need to add clients, simply enable the SSID temporarily, connect the client, and then disable the SSID. This might not be a factor if you are in a large building. But if you are in a smaller structure, the WAP’s broadcast range may leak out beyond your organization’s property. You can also try reducing the transmitter power of the WAP. Although not all WAPs have this function, some do and it can help to fine-tune the area that the WAP serves.
Note
It wasn’t mentioned yet, but clients can still connect to a wireless network that is not broadcasting the SSID. This can be done manually within the proprietary third-party wireless adapter settings or, in Windows, by first starting the WLAN AutoConfig service (wlansvc) and then accessing the Managing Wireless Networks link within the Network and Sharing Center. However, the person connecting must know the SSID, the type of encryption being used, and the encryption key. Some third-party wireless software applications won’t allow for this to be manually entered. If that is the case, and the user needs to connect manually, the third-party software should be disabled and the client should connect using Windows.
Just remember, by default when the SSID broadcast is disabled, no new wireless clients can connect, unless they do so manually.
Rogue Access Points
Rogue APs can be described as unauthorized wireless access points/routers that allow access to secure networks. Sometimes companies lose track of the WAPs on their network. Keep track of all your devices with network documentation. Use network mapping programs and Microsoft Visio to detect and document any rogue APs. Older WAPs, especially ones with weak encryption, should be updated, disabled, or simply disconnected from the network. Some companies may have a dozen WAPs and additional wireless devices such as repeaters, and it may be difficult to keep track of these. In this case, a network mapping program can be one of your best friends. In addition, you can search for rogue APs with a laptop or handheld computer with Windows’ wireless application, the wireless network adapter’s built-in software, or third-party applications such as AirMagnet or NetStumbler. If traffic from a rogue AP does enter your network, a NIDS or NIPS solution can be instrumental in detecting and preventing that data and data that comes from other rogue devices. Organizations commonly perform site surveys to detect rogue APs, and other unwanted wireless devices. We’ll discuss more details about site surveys later in this chapter.
Evil Twin
An evil twin is a rogue, counterfeit, and unauthorized wireless access point that uses the same SSID name as a nearby wireless network, often public hotspots. Like an evil twin antagonist found in many sci-fi books, the device is identical in almost all respects to the authorized WAP. While the antagonist in the sci-fi book usually has a beard or goatee, the WAP is controlled by a person with the same types of motives as the bearded evil twin. One of these motives is phishing. For example, an attacker might attempt to fool wireless users at an Internet café to connect to the counterfeit WAP to gain valuable information and passwords from the users. If the user is unlucky enough to connect to the evil twin, all the information within the session can easily be recorded and digested later on by the attacker. This attack can also be enacted upon organizations. To protect against this, virtual private networks (VPNs) can be implemented that require external authentication outside the WAP. Administrators should scan the network often for rogue APs that might be evil twins. Users in general should be trained not to send passwords, credit card numbers, and other sensitive information over wireless networks.
Weak Encryption
Weak encryption or no encryption can be the worst thing that can happen to a wireless network. This can occur for several reasons—for example, if someone wanted to connect an older device or a device that hasn’t been updated, and that device can run only a weaker, older type of encryption. It’s important to have strong encryption in your network; as of this writing, Wi-Fi Protected Access 2 (WPA2) is the best wireless protocol you can use. It can be used with TKIP or, better yet, AES. Remember that the encryption level of the WAP and the encryption level of the network adapters that connect to it need to be the same. Table 9-2 defines some of the available wireless protocols and encryption types.
| Wireless Protocol | Description | Encryption Level (Key Size) |
| WEP | Wired Equivalent Privacy (Deprecated) |
64-bit Also 128-bit but uncommon |
| WPA | Wi-Fi Protected Access | 128-bit |
| WPA2 | Wi-Fi Protected Access Version 2 | 256-bit |
| TKIP | Temporal Key Integrity Protocol (Deprecated) Encryption protocol used with WEP and WPA |
128-bit |
| CCMP | Counter Mode with Cipher Block Chaining Message Authentication Code (CBC-MAC) Protocol Encryption protocol used with WPA2 Addresses the vulnerabilities of TKIP Meets requirements of IEEE 802.11i |
128-bit |
| AES | Advanced Encryption Standard Encryption protocol used with WPA/WPA2 Strongest encryption method in this table |
128-bit, 192-bit, and 256-bit |
| WTLS | Wireless Transport Layer Security | Based on TLS |
WEP is the weakest type of encryption; WPA is stronger, and WPA2 is the strongest of the three. However, it is better to have WEP as opposed to nothing. If this is the case, use encryption keys that are difficult to guess, and consider changing those keys often. Some devices can be updated to support WPA, whether it is through a firmware upgrade or through the use of a software add-on. Figure 9-1 shows a typical WAP with WPA2 and AES configured; AES is the cipher type. The pre-shared key (PSK) used to enable connectivity between wireless clients and the WAP is a complex passphrase. PSK is automatically used when you select WPA-Personal in the Security Mode section. The other option is WPA-Enterprise, which uses a RADIUS server in this WAP. So, if you ever see the term “WPA2-PSK,” that means that the WAP is set up to use the WPA2 protocol with a pre-shared key, and not an external authentication method such as RADIUS.
The Wireless Transport Layer Security (WTLS) protocol is part of the Wireless Application Protocol (WAP) stack used by mobile devices. It enables secure user sessions—for instance, banking transactions—using algorithms such as RSA, ECC, Triple DES, and MD5 or SHA, all of which are described in Chapter 14, “Encryption and Hashing Concepts.”
Wi-Fi Protected Setup
Wi-Fi Protected Setup (WPS) is in of itself a security vulnerability. Created originally to enable users easy connectivity to a wireless access point, it was later suggested by all major manufacturers that it be disabled (if possible). In a nutshell, the problem with WPS was the eight-digit code. It effectively worked as two separate smaller codes that collectively could be broken by a brute-force attack within hours.
There isn’t much that can be done to prevent the problem other than disabling WPS altogether in the WAP’s firmware interface or, if WPS can’t be disabled, upgrading to a newer device. In summary, WPS is a deprecated and insecure technology that should not be allowed on a wireless network.
Ad Hoc Networks
Ad hoc networks allow for wireless connections between clients without any centralized WAP or wireless LAN (WLAN) controller. This is inherently insecure. Most organizations have written policies that disallow ad hoc networks for Wi-Fi and other wireless technologies. In most scenarios, security admins should disable ad hoc functionality on Windows clients and other client operating systems, wireless devices, mobile computers, WAPs, and so on. Enough said.
VPN over Open Wireless
VPN connections are meant to be secure sessions accomplished through an encrypted tunnel. They are best secured in a wired environment, but sometimes a wireless VPN connection is required. Some devices offer this but in an inherently insecure manner—this is known as VPN over open wireless, with “open” being the operative word, meaning insecure and unencrypted. In most business scenarios this is unacceptable, and should be scanned for with a wireless scanning utility. Just the presence of a VPN is not enough; some kind of encryption is necessary, whether it be Point-to-Point Tunneling Protocol (PPTP), IPsec, or another secure protocol.
For example, in a standard Cisco wireless VPN configuration, the wireless client initiates a tunnel to a VPN server (a Cisco router), but it is done in a pass-through manner via a wireless LAN (WLAN) controller. (A Lightweight Access Point is often also part of the solution.) It’s the router that must be set up properly, and in this scenario IPsec should be installed and configured. That will allow for the encryption of session data between the wireless client and the WLAN controller.
In other scenarios, especially in smaller offices or home offices, a single device will act as the all-in-one solution. Though wireless VPN connections are uncommon in SOHO environments, this solution presents only a single layer of defense and it can be easy to forget to initiate the proper encryption. There are many authentication mechanisms and possibilities, and several ways to encrypt the session. The key here is to remember to have clients authenticate in a secure manner, and handshake on an encryption protocol that will protect the data. We discuss authentication and concepts such as VPN in more depth in Chapter 10.
Wireless Access Point Security Strategies
Strategic placement of a WAP is vital. Usually, the best place for a WAP is in the center of the building. This way, equal access can be given to everyone on the perimeter of the organization’s property, and there is the least chance of the signal bleeding over to other organizations. If needed, attempt to reduce the transmission power levels of the antenna, which can reduce the broadcast range of the WAP. Also, to avoid interference in the form of EMI or RFI, keep WAPs away from any electrical panels, cables, devices, motors, or other pieces of equipment that might give off an electromagnetic field. If necessary, shield the device creating the EM field, or shield the access point itself. Sheesh, I am starting to sound bossy! (Must be those two years I spent as a building contractor....)
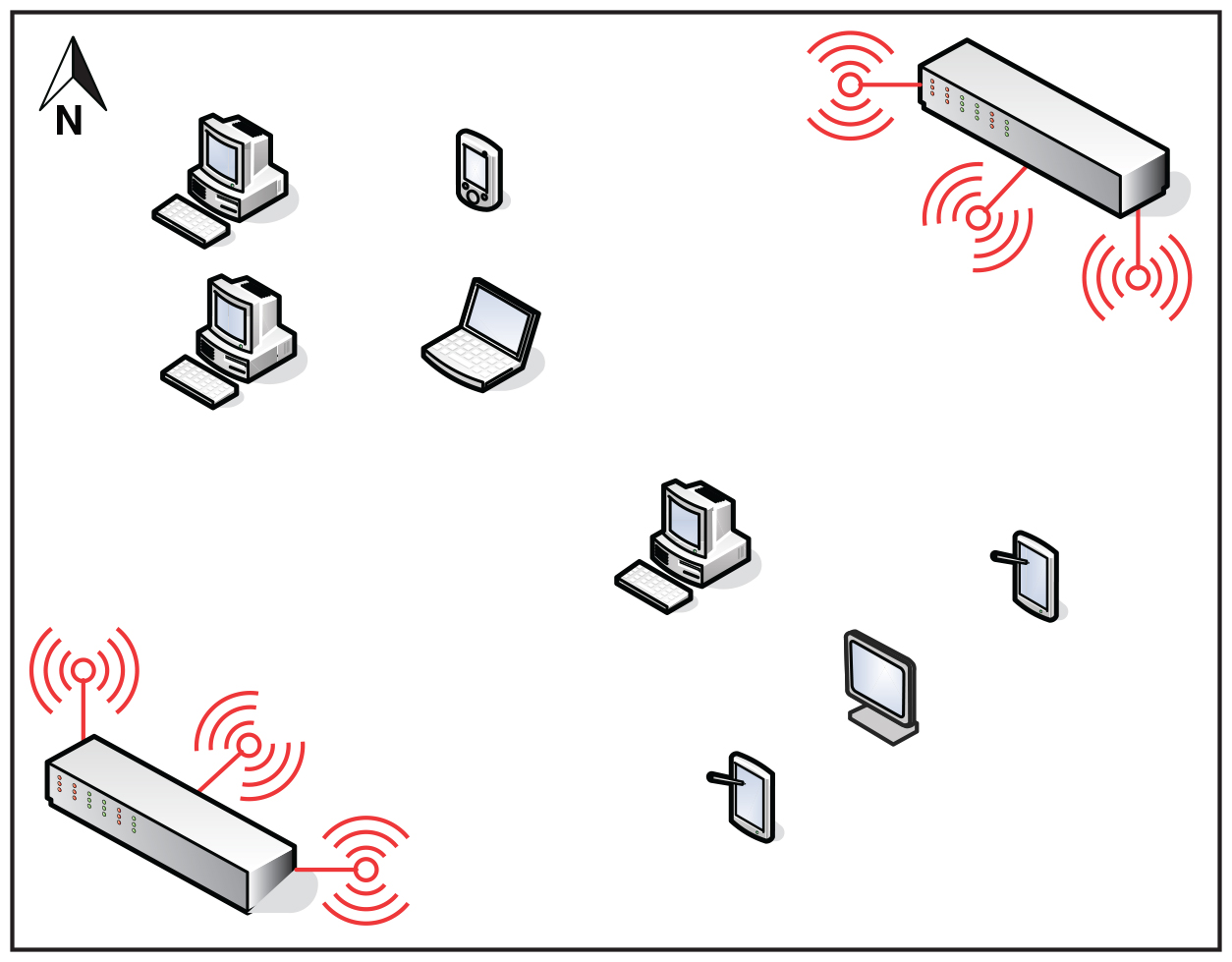
Anyway, in order to really know how to best arrange and secure your wireless connections, you need to understand the different wireless systems and antenna types available. The most common wireless system is point-to-multipoint. This system is commonly used in WLANs where a single central device (such as a SOHO wireless router) will connect to multiple other wireless devices that could be located in any direction. Specifically, it makes use of omnidirectional antennas such as vertical omnis, ceiling domes, and so on. A typical wireless router might have two, three, four, or more vertical omnidirectional antennas. For example, a SOHO 802.11n wireless router might have three antennas that use multiple-input multiple-output (MIMO) technology to combine multiple data streams for significantly higher data throughput (up to eight streams for 802.11ac). These antennas can be rotated so that they are parallel to each other, or at an angle to each other; for example, 180 degrees is often a good configuration to, in essence, “sweep” the area for wireless transmissions. However, you might choose a different method. For example, you might have 100 computers on one floor and two WAPs to work with. The best method might be to position them at vertical angles from each other. One would be in the building’s northeast corner and the other in the southwest corner. Then, each set of three antennas could be positioned in a 90-degree sweep as shown in Figure 9-2. As long as the building isn’t larger than the range of the antennas, then this should allow for excellent wireless coverage.
Note
Speaking of 802.11ac and 802.11n, channel selection and channel width selection can impact performance and security as well. 5-GHz frequency bands usually offer better performance than 2.4-GHz bands, but both can be monitored over-the-air by attackers. Some WAPs can be set to auto-configure, seeking the least used wireless frequencies/channels, which can be great for performance, but might be a security risk. Consider using less common channel numbers, and perhaps a narrower channel; for example, 40 MHz instead of 80 MHz for 802.11ac. And remember to reduce antenna power levels as much as possible. Once again, you must test carefully, and then balance performance and security for optimal organization efficiency.
There are also more simplistic point-to-point wireless systems where only two points need to be connected; these points are usually fixed in location. In this case you would use directional anten207nas; for example, a parabolic antenna (dish) or a Yagi antenna.
Whatever you implement, it’s a good idea to perform a wireless site survey. There are three kinds of wireless surveys you might perform, each with its own purpose, and all of which are usually based on software that collects WLAN data and signal information (though hardware can also be used to measure radio frequencies). A passive site survey listens to WLAN traffic and measures signal strength. An active survey actually sends and receives data to measure data transfer rate, packet loss, and so on. A predictive survey is a simulated survey based on real data such as the WAP to be used, the distance between the average computer and WAP, and so on.
Surveys can be instrumental in uncovering nonaggressive interference such as neighboring radio waves and electrical equipment (RFI and EMI, mentioned earlier). Surveys can also be used to locate aggressive jamming techniques often caused by wireless signal jammers. A signal jammer can easily be purchased online and can be used to initiate a denial-of-service attack to the wireless network. This is done by creating random noise on the channel used by the WAP, or by attempting to short out the device with powerful radio signals. The right wireless software (such as NetStumbler) can be used to locate signal jammers in or around your building so that you can remove them. Wireless software can also be used to identify potential wireless replay attacks that might exist within the network infrastructure.
Many WAPs come with a built-in firewall. If the firewall is utilized, the stateful packet inspection (SPI) option and NAT filtering should be enabled. The WAP might also have the capability to be configured for MAC filtering (a basic form of network access control), which can filter out which computers can access the wireless network. The WAP does this by consulting a list of MAC addresses that have been previously entered. Only the network adapters with those corresponding MAC addresses can connect; everyone else cannot join the wireless network. In some cases, a device might broadcast this MAC table. If this is the case, look for an update for the firmware of the WAP, and again, attempt to fine-tune the broadcast range of the device so that it does not leak out to other organizations. Because MAC filtering and a disabled SSID can be easily circumvented using a network sniffer, it is very important to also use strong encryption, and possibly consider other types of network access control (such as 802.1X) and external authentication methods (such as RADIUS).
Some WAPs also support isolation. AP isolation (also known as isolation mode) means that each client connected to the WAP will not be able to communicate with any other clients connected to the WAP. Each client can still access the Internet (or other network that the WAP is connected to), but every wireless user will be segmented from the other wireless users.
It is also possible to include the IEEE 802.1X standard for port-based network access control that can provide for strong authentication. For a WAP to incorporate this kind of technology, it must also act as a router, which adds the duty of wireless gateway to the WAP.
Another option is to consider encryption technologies on the application layer, such as SSL, SSH, or PGP; these and others can help to secure data transmissions from attackers that have already gained access to the wireless network. For more information on encryption types, see the section “Security Protocols” in Chapter 15, “PKI and Encryption Protocols.” When it comes down to it, authentication and a strong wireless protocol such as WPA2 with AES are the two security precautions that will best help to protect against network attacks.
We briefly mentioned wireless LAN controllers. If your organization has or needs multiple WAPs, a smart method is to wire them each to a WLAN controller. This device acts as a switch for all the WAPs, thus increasing data transfer speeds between them, and more importantly, centralizes the management of security options. Most of the WAP functionality is handed off to the controller. If this controller is physically stored in a server room or data center, the access to its functionality becomes inherently more secure (especially if a Faraday cage is implemented). In this scenario, the WAP devices are considered “thin access points” because of the reduced functionality. Contrast this to the typical “fat access point” that contains all functionality. Because the fat access point must be located close to users to be functional, it creates more potential for attackers to gain access to it. Most midsized companies and virtually all enterprise networks use WLAN controllers.
Finally, another option is to not run wireless at all. It’s tough to hack into a wireless network that doesn’t exist! Some companies opt for this, as strange and difficult as it may seem, because they have deduced that the costs of implementation, administration, maintenance, and security outweigh the benefits of having a wireless network. (Personally, my home is cabled up 100 percent—bedrooms, bathrooms, attic, you name it...but I still use wireless devices!) However, if you decide to go down the anti-wireless road, make sure that any devices that enable wireless access have those wireless functions disabled. This includes wireless access points, laptops, and other mobile devices that have wireless adapters, and any Bluetooth, infrared, or other wireless transmitters.
Wireless Transmission Vulnerabilities
Because wireless networks can transmit information through air or space, data emanations are everywhere and can easily be identified by people using the right tools. One deed that can be considered an attack on wireless networks is known as war-driving; this is the act of searching for wireless networks by a person in a vehicle, through the use of a device with a wireless antenna, often a particularly strong antenna. A basic example of this would be a person in a car with a laptop, utilizing the freely downloadable NetStumbler software. When war-drivers find a network, they can attempt to crack the password or passphrase to gain access to the wireless network. This might be done by guessing; you’d be surprised how much this works. It is estimated that more than 40 percent of wireless networks are unprotected. It could also be done with dictionary or brute-force attacks. You can find more information on password cracking in the section “Assessing Vulnerability with Security Tools” in Chapter 12, “Vulnerability and Risk Assessment.”
Ways to protect against war-driving include hiding the SSID of the WAP, proper positioning of the WAP, decreasing the power levels to the point where the signal doesn’t leak past the organization’s building, using strong encryption, and changing the passphrase (encryption key) at regular intervals.
An interesting item connected with public Wi-Fi is war-chalking. This is the act of physically drawing symbols in public places that denote open, closed, or protected wireless networks. This is done by attackers to let other attackers know about open wireless networks. However, some organizations use the symbols as well to let people know that they have an open wireless network available to the public. In this case, the symbols will be professionally presented. Various symbols are used including the open node (two half circles back to back), the closed node (a closed circle), and a circle with a W, which stands for a WEP- or WPA-encrypted network.
IV attacks are another vulnerability of wireless networks. The IV attack is a type of related-key attack, which is when an attacker observes the operation of a cipher using several different keys, and finds a mathematical relationship between those keys, allowing the attacker to ultimately decipher data. IV stands for initialization vector, a random fixed-sized input that occurs in the beginning of every WEP or WPA packet. For WEP, the IV size was small (24-bit) and led to many successful attacks on WEP. This is why WEP is considered to be deprecated and insecure. The best way to prevent IV attacks is to use stronger wireless protocols such as WPA2 and AES.
We’ve mentioned DoS attacks several times in this book already. These can be run against WAPs in a variety of ways. One way is through the use of spoofed MAC addresses. If an attacker emulates a large number of wireless clients, each with a different spoofed MAC address, and never allows authentication for these clients to finish, then legitimate clients will no longer be able to be serviced by the WAP, because all of the session spots will have been taken. This is a type of denial-of-service due to incomplete authentication. It can be prevented by configuring expiration timeouts for all sessions that have not had activity for a certain period of time. It can also be prevented by updating the WAP and implementing wireless frame protection. (Different providers will have different names for this; for example, Cisco Management Frame Protection.) Another type of wireless-based DoS is the Wi-Fi disassociation attack—also known as Wi-Fi deauthentication attack. The attacker targets a user that is connected to a Wi-Fi network by using a wireless scanner. Then the attacker forces that user’s system to deauthenticate using special software, and then re-authenticate to the WAP. By capturing the packets during the authentication process, the attacker can find out the SSID or ESSID of the WAP and possibly WPA/WPA2 handshake information. After that, the attacker will attempt to find out the WPA passphrase using a dictionary attack. This sounds more difficult in theory than it actually is. Using automated software tools, this can all be accomplished by an attacker in under a minute. These types of “deauth” attacks can be prevented by using WPA2, by using complex passphrases, and by implementing technologies such as management frame protection by Cisco, which adds a hash value to management frames of information, such as the ones used by WPA/WPA2.
We previously pointed out that a WAP can fall victim to brute-force attacks if WPS is used. The key of the WAP can also be compromised by a brute-force attack known as an exhaustive key search. This can be prevented by limiting the number of times a password/passphrase can be tried, using time delays between attempts, and requiring complex answers during the authentication process. Also, as a corrective security control, attacking IP addresses can be blacklisted. We’ll discuss brute-force/exhaustive key searches more in Chapter 14.
Bluetooth and Other Wireless Technology Vulnerabilities
Bluetooth, RFID, and NFC are not wireless networking technologies in the general sense the way Wi-Fi is. But anything that has two or more wireless devices that communicate with each other could technically be considered a wireless network. So, I decided to place these technologies here. “It seemed the proper way....”
Like any wireless technology, Bluetooth is vulnerable to attack as well. Bluejacking and bluesnarfing are two types of vulnerabilities to Bluetooth-enabled devices. Bluetooth is also vulnerable to conflicts with other wireless technologies. For example, some WLAN (or Wi-Fi) standards use the 2.4-GHz frequency range, as does Bluetooth, and even though Bluetooth uses frequency hopping, conflicts can occur between 802.11g or 802.11b networks and Bluetooth personal area networks (PANs). To avoid this, use Bluetooth version 1.2 devices or greater, which employ adaptive frequency hopping, improving resistance to radio interference. Also, consider placing Bluetooth access points (if they are used) and WLAN access points in different areas of the building. Some companies have policies governing Bluetooth usage; in some cases, it is not allowed if 802.11 standards are in place, and in some cases a company will enforce rules that say Bluetooth can be used only outside the building. In other cases, a company will put its 802.11 devices on specific channels or use WLAN standards that use the 5-GHz range.
Bluetooth-equipped devices can use near field communication (NFC), which allows two mobile devices (or a mobile device and a stationary computer) to be automatically paired and transmit data. NFC is not limited to Bluetooth, but Bluetooth is probably the most common technology used to transmit data wirelessly over short distances. Of course, even though the distance is short, it can still be eavesdropped on. In addition, NFC is a data transmission protocol, but not necessarily secure. Data can be destroyed by use of a jammer, and users are also at risk of replay attacks. At the writing of this book, NFC does not offer preventive security in this aspect, but a user can prevent these attacks by only using applications that offer SSL/TLS or other secure channels during an NFC session.
Bluejacking
Bluejacking is the sending of unsolicited messages to Bluetooth-enabled devices such as mobile phones and tablets. Bluejacking is usually harmless, but if it does occur, it may appear that the Bluetooth device is malfunctioning. Originally, bluejackers would send only text messages, but with newer Bluetooth-enabled mobile devices, it is possible to send images and sounds as well. Bluejacking is used in less-than-reputable marketing campaigns. Bluejacking can be stopped by setting the affected Bluetooth device to “undiscoverable” or by turning off Bluetooth altogether.
Bluesnarfing
I know what you are thinking: The names of these attacks are starting to get a bit ridiculous! I guarantee it will improve as we progress through the rest of this book! Anyway, bluesnarfing is the unauthorized access of information from a wireless device through a Bluetooth connection. Generally, bluesnarfing is the theft of data (calendar information, phonebook contacts, and so on). It is possible to steal other information as well, but to pilfer any of this data, a pairing must be made between the attacking Bluetooth device and the Bluetooth victim. Ways of discouraging bluesnarfing include using a pairing key that is not easy to guess; for example, stay away from 0000 or similar default Bluetooth pairing keys! Otherwise, Bluetooth devices should be set to “undiscoverable” (only after legitimate Bluetooth devices have been set up, of course), or Bluetooth can be turned off altogether, especially in areas that might be bluesnarfing playgrounds, such as Times Square in New York City. Bluesnarfing is considered by some to be a component of bluejacking, but for the exam, try to differentiate between the two.
More details about how to protect phones, laptops, and other devices that use Bluetooth can be found in Chapter 3, “Computer Systems Security Part II.”
RFID and NFC
Radio-frequency identification (RFID) has many uses, but it all boils down to identifying and tracking tags that are attached to objects. In the security world that generally means authentication.
As with any wireless technology, RFID is susceptible to attack. For example, some RFID tags can be affected by skimming, man-in-the-middle (MITM) attacks, sniffing, eavesdropping/replaying, spoofing, and jamming (DoS). From an authentication standpoint, the attacker is using these attacks to try to find out the passcode. An RFID tag can also be reverse engineered if the attacker gets possession of it. Finally, power levels can be analyzed to find out passwords. On some RFID tags, correct passcodes emit a different level of power than incorrect passcodes. To prevent these attacks, a security admin (or team) should consider newer generation RFID devices, encryption, chip coatings, filtering of data, and multifactor authentication methods. Encryption is one of the best methods. Included in this prevention method are rolling codes, which are generated with a pseudorandom number generator (PRNG), and challenge-response authentication (CRA), where the user (or user’s device) must present the valid response to the challenge.
RFID ranges vary depending on the EM band used—from 10 cm up to 200 meters. Many authentication readers can be as much as 1 meter, which is enough to facilitate skimming of information by attackers. One way to avoid this is to use newer RFID proximity readers and keys—ones that use lower frequencies—from respectable companies. Another way is to utilize the set of protocols called near field communication (NFC). NFC generally requires that communicating devices be within 4 cm of each other, which makes skimming of information difficult. If an employee uses a smartphone to enter a building instead of an RFID device, then NFC should be implemented. NFC has obvious benefits for contactless payment systems or any other non-contact-oriented communications between devices. However, for optimal security, use contact-oriented readers and cards.
More Wireless Technologies
Let’s not forget about cellular connections. Many companies don’t allow cellular access, meaning 2G, 3G, 4G, LTE, and so on. These are often denied within company premises, and instead the company will rely on Wi-Fi methods; for example Wi-Fi calling. This is common in choose your own device (CYOD) and corporate-owned, personally enabled (COPE) environments. But if cellular is necessary in a bring your own device (BYOD) environment, then security can be increased by using newer devices, updating the devices’ OS, updating the preferred roaming list (PRL), updating identification technologies (such as IMEI and IMSI), and using a VPN for data connections over cellular. Use these methods for employees who must be on the road as well. And if there are foreseeable instances where cellular is not available for mobile employees, be sure that they understand the risks of open Wi-Fi networks and that they should avoid them as much as possible.
We talked about GPS in Chapter 3. Remember that the usage of GPS should be examined carefully. Weigh the benefits of GPS against the exploitable vulnerabilities inherent to the system. Disable it whenever possible. Also, consider disabling other GPS and geolocation-related technologies. For example, geotagging is when geographical identification information, such as latitude and longitude coordinates, is added to photographs, websites, SMS messages, and more. It is common in social media and can be a great tool, but it can also be an easy way for attackers to zero in on high-profile executives and other employees of an organization. Consider a geofence—a virtual fence defining the boundaries of an actual geographical area. Geofencing is an excellent way to be alerted to users entering and exiting an organization’s physical premises and can provide security for wireless networks by defining the physical borders and allowing or disallowing access based on the physical location of the user, or more accurately, the user’s computer or mobile device!
Some organizations rely on satellite communications (SATCOM): sometimes for long distance communications, and sometimes for communicating between buildings in a campus. Either way, it is important to understand that SATCOM devices can be at risk if their firmware is not updated. Exploits could include the installation of malicious firmware and the execution of arbitrary code. Updating may require physical access to the parabolic antenna using a laptop or terminal device. But remember, the easier it is to access these antennas, the more likely they can be hacked by a malicious individual. Of course, in some cases these antennas can be hacked remotely as well. Secure planning is necessary when it comes to physical access, firewalling (if possible), and especially updating.
Remember this: wireless technologies are always “evolving.” But anything is hackable, given time and ingenuity. When it comes to over-the-air tech, be ever vigilant—know the latest exploits, and prepare a worthy defense.
Chapter Review Activities
Use the features in this section to study and review the topics in this chapter.
Chapter Summary
If we all operated computers that never made any connections to other systems, we could say that those computers were pretty secure. What a wonderful world it would be, and for many end users, that was the world...in 1986. Today’s computers usually require networking connections; otherwise they become useless. These past four chapters have shown that the majority of security concerns are network related...not all, but a huge chunk. Now here’s a newsflash that even some technicians don’t think of—disable the wired or wireless networking connection when the computer is not in use. Yes! In some cases, this method is feasible today. For example, configure a mobile device to go to airplane mode while you are sleeping. A good rule of thumb for end users is that, unless they have a server, their computers should sleep when the users sleep. As another example, configure an unused server to effectively shut down its network interface automatically between the hours of 2 a.m. and 7 a.m. (if there is little activity then). This kind of mentality can add up over time, and equate to a cleaner and more efficiently running network.
However, that is somewhat of a utopian mindset when it comes to the hardcore company that needs to do business 24/7. Therefore, we have to employ the measures discussed in this chapter. We focused on the wired and wireless connections of networks. Devices that control these wired and wireless networks often have weak security when it comes to account names and especially passwords. If you can change the administrator account name (or create a secondary admin account and disable the first) and set a complex password, you will have implemented the most important layer of security. And by complex, I mean COMPLEX! (That was me practically yelling the word.)
Today’s complexity is multifaceted compared to last decade’s complexity. There are various reasons for this—which we will discuss more in later chapters—but in essence, having a 10-character password for normal environments and a 15-character password for highly confidential environments is now the status quo (as of the writing of this book). Add on numerals, uppercase letters, and special characters, and you have the beginnings of a virtually uncrackable password. But remember, password cracking programs (and the computers that run them) are always getting stronger and faster. For example, an eight-character password that was considered uncrackable in 1999 might only take a week to crack today with the use of a typical desktop computer. This progression is directly related to Moore’s Law, and as such will most likely continue. You might say: “But wait, Dave! Does this mean that, at some point, all passwords can be cracked?” Theoretically, yes, but that time probably won’t come soon. It is better to be safe than sorry, and so you might also want to incorporate multifactor authentication, of which we will speak to in the following chapter.
Devices should have their firmware updated often to help close backdoors and weed out privilege escalation attempts. These updates will often have patches for the various network attacks that we have mentioned in the past few chapters.
Wired connections are still the lifeblood of a company. Wireless is great, but you don’t run it in a server room or data center; and for stationary workstations, wired connections are king. The bulk of these connections are twisted-pair, which is inherently vulnerable to tapping. Use shielded cables to block EMI, resist wiretapping, and reduce data emanation and crosstalk. On a larger scale, consider shielding such as a Faraday cage or TEMPEST, especially in server rooms. Disable unused ports on switches and RJ45 wall terminals. Remove any network cabling that is not hidden from view, and, if you are really security conscious, consider using fiber-optic cabling. Your servers may already utilize this, but your clients probably do not. For computers that send the most confidential of information, a secure channel is great, but secure media (such as fiber-optic cabling) seals the deal.
Of course, when you have data that flies all over the air in your building, it can be more difficult to secure. It is more abstract, and not as easily measured. But it is still possible to secure a wireless network. It’s really all about scanning the wireless network. Is your SSID easy to find? Is it possible that you could hide the SSID? Are there other SSIDs that show up on your scan? Rogue APs and evil twins need to be sniffed out and eliminated immediately. But that isn’t as much a preventive security control as it is a detective security control. The real way to prevent issues on the wireless network is to employ encryption—strong encryption such as WPA2 and AES (with a PSK), or perhaps utilize a RADIUS server in combination with those. Get rid of WPS once and for all, and make sure that VPN connections made wirelessly are heavily encrypted. Consider setting wireless boundaries by implementing a geofence. Then it’s just a matter of doing a site survey, and maximizing your data transfer rate in a secure way by using smart placement techniques of your WAPs and antennas. These methods will help to reduce the chance of a successful war-driving attack, or IV attack, or a brute-force attempt.
And wireless is not limited to WLAN. You might have Bluetooth, IR, GSM, 4G, RFID, SATCOM, and the list goes on. All wireless transmissions should be thoroughly scanned and tested before they are allowed in your organization. But that’s another book (and certification) altogether. Where the Security+ certification expects a basic level of wireless security knowledge, other certifications such as the Certified Wireless Network Administrator (CWNA) take it to the next level and require in-depth knowledge of all wireless communications security techniques, especially WLAN. If your organization is highly dependent on its wireless communications, consider a wireless certification such as the CWNA to bolster your resume.
Every chapter in this book effectively deals with network security on some level. But these past four chapters are at the core of it. Remember the content in these chapters as you progress throughout the rest of the book—they build your foundation of networking and network security knowledge. Finally, when it comes to your network security, attempt to think outside the box. If necessary, take it to the next level and work out solutions that, even if they seem unorthodox, fit into your organization’s business model. You might surprise yourself and come up with some great answers that work very well for you and your organization.
Review Key Topics
Review the most important topics in the chapter, noted with the Key Topic icon in the outer margin of the page. Table 9-3 lists a reference of these key topics and the page number on which each is found.
Table 9-3 Key Topics for Chapter 9
| Key Topic Element | Description | Page Number |
| Table 9-1 | Weak, strong, and stronger passwords | 196 |
| Bulleted list | Privilege escalation types | 197 |
| Bulleted list | Cable types | 198 |
| Bulleted list | Interference types | 198 |
| Table 9-2 | Wireless protocols | 203 |
| Figure 9-1 | Wireless security configuration on a typical WAP | 204 |
| Figure 9-2 | Wireless point-to-multipoint layout | 206 |
| Figure 9-3 | Final network documentation | 212 |
Define Key Terms
Define the following key terms from this chapter, and check your answers in the glossary:
electromagnetic interference (EMI)
radio frequency interference (RFI)
protected distribution system (PDS)
Wired Equivalent Privacy (WEP)
Advanced Encryption Standard (AES)
Temporal Key Integrity Protocol (TKIP)
Wireless Transport Layer Security (WTLS)
Complete the Real-World Scenarios
Complete the Real-World Scenarios found on the companion website (www.pearsonitcertification.com/title/9780134846057). You will find a PDF containing the scenario and questions, and also supporting videos and simulations.
Review Questions
Answer the following review questions. Check your answers in Appendix A, “Answers to the Review Questions.”
1. Which of the following is the most secure protocol to use when accessing a wireless network?
A. WEP
B. WPA
C. WPA2
D. TKIP
2. What type of cabling is the most secure for networks?
A. STP
B. UTP
C. Fiber-optic
D. Coaxial
3. What should you configure to improve wireless security?
A. Enable the SSID
B. IP spoofing
C. Remove repeaters
D. MAC filtering
4. In a wireless network, why is an SSID used?
A. To secure the wireless access point
B. To identify the network
C. To encrypt data
D. To enforce MAC filtering
5. What is the most commonly seen security risk of using coaxial cable?
A. Data that emanates from the core of the cable
B. Crosstalk between the different wires
C. Chromatic dispersion
D. Jamming
6. Of the following, what is the most common problem associated with UTP cable?
A. Crosstalk
B. Data emanation
C. Chromatic dispersion
D. Vampire tapping
7. What two security precautions can best help to protect against wireless network attacks?
A. Authentication and WEP
B. Access control lists and WEP
C. Identification and WPA2
D. Authentication and WPA
8. Which of the following cables suffers from chromatic dispersion if the cable is too long?
A. Twisted-pair cable
B. Fiber-optic cable
C. Coaxial cable
D. USB cables
9. Which of the following cable media is the least susceptible to a tap?
A. Coaxial cable
C. Fiber-optic cable
D. CATV cable
10. Which of the following, when removed, can increase the security of a wireless access point?
A. MAC filtering
B. SSID
C. WPA
D. Firewall
11. A wireless network switch has connectivity issues but only when the air-conditioning system is running. What can be added to fix the problem?
A. Shielding
B. A wireless network
C. A key deflector
D. Redundant air-conditioning systems
12. Which of the following is the most secure type of cabling?
A. Unshielded twisted-pair
B. Shielded twisted-pair
C. Coaxial
D. Category 6
13. Which of the following is the least secure type of wireless encryption?
A. WEP 64-bit
B. WEP 128-bit
C. WPA with TKIP
D. WPA2 with AES
14. Which of the following is the unauthorized access of information from a Bluetooth device?
A. Bluejacking
B. Bluesnarfing
C. Deep Blue
D. The Blues Brothers
15. Which of the following can be described as the act of exploiting a bug or flaw in software to gain access to resources that normally would be protected?
A. Privilege escalation
B. Chain of custody
C. Default account
D. Backdoor
16. What does isolation mode on an AP provide?
A. Hides the SSID
B. Segments each wireless user from every other wireless user
C. Stops users from communicating with the AP
D. Stops users from connecting to the Internet
17. You scan your network and find a rogue AP with the same SSID used by your network. What type of attack is occurring?
A. War-driving
B. Bluesnarfing
C. Evil twin
D. IV attack
18. Which of the following is an unauthorized wireless router that allows access to a secure network?
A. Rogue AP
B. Evil twin
C. War-driving
D. AP isolation
19. Your boss asks you to limit the wireless signal of a WAP from going outside the building. What should you do?
A. Put the antenna on the exterior of the building.
B. Disable the SSID.
C. Enable MAC filtering.
D. Decrease the power levels of the WAP.
20. Which of the following should be considered to mitigate data theft when using Cat 6 wiring?
A. Multimode fiber
B. EMI shielding
C. CCTV
D. Passive scanning
21. Which of the following is a room or “closet” where wiring and circuits merge, creating a potential attack point?
A. SATCOM
B. NFC
C. MDF
D. TEMPEST