While there are no foolproof ways to defend against JavaScript phishing, there are some basic strategies that we can adopt to avoid phishing.
Newer versions of web browsers typically contain upgrades or security fixes. To upgrade to newer versions of the particular web browsers you are using, you can simply visit the main website of the browser vendor. For instance, if you are using Google Chrome, you can visit https://www.google.com/chrome/browser/, while you can visit https://www.mozilla.org/en-US/firefox/new/ for Mozilla Firefox.
Some of the more notable ones include the removal of support to access a browser's history either via window.history or by accessing the user's local state: $("a:visited").
From the aforementioned types of phishing, you might have noticed that one common strategy used by phishing sites is the use of fake websites. Should you recognize a fake website, you can avoid the chances of being phished.
Here are tips to help you recognize real websites:
- Watch out for fake web addresses (URLs). Even websites that contain the name of the real website could be fake; having the word,
ebayin the URL does not mean that this is the real eBay website. Take, for instance,http://[email protected]/may have the wordebay, but it is fake, as the address has something between.comand the forward slash (/). eBay provides many more examples on their website: http://pages.ebay.com/help/account/recognizing-spoof.html. Have a look at the following screenshot: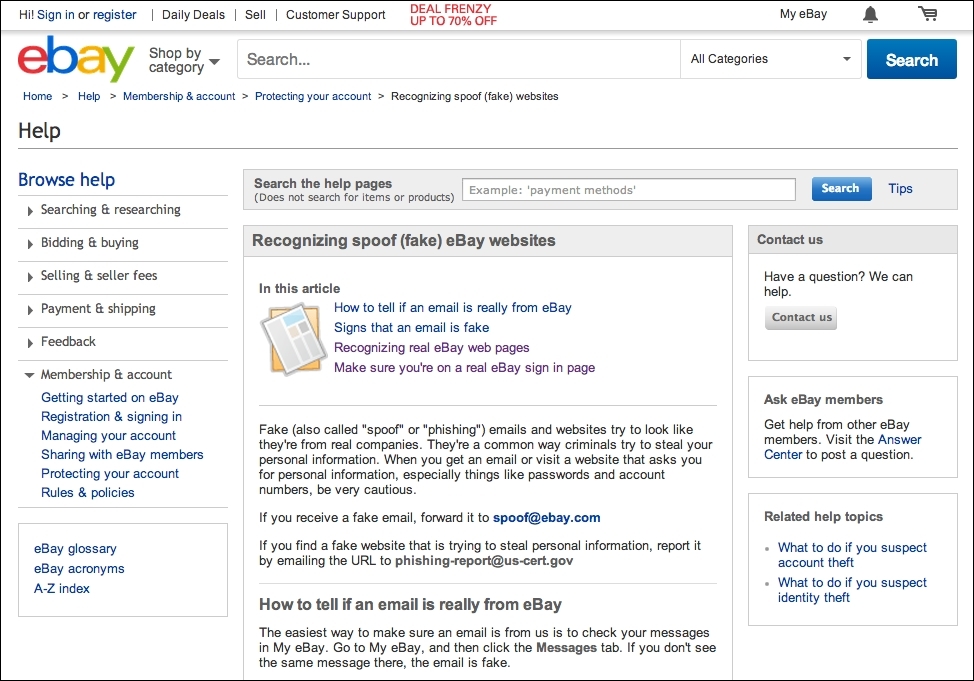
Real and authentic eBay website
- PayPal also has a comprehensive website going through the ins and outs of phishing, with regard to how to spot them and more, at the following link: https://www.paypal.com/webapps/mpp/security/antiphishing-canyouspotphishing.
Have a look at the following screenshot:

Real and authentic PayPal website
By protecting your sites against XSS and CSRF, you greatly reduce the risk of JavaScript security issues such as those covered in previous chapters.
You can design your website so that it avoids the use of pop ups and keeps your address bars. By not using pop ups, you reduce a possible imitation technique that can be used to perform phishing. An alternative to using pop ups would be to use certain techniques, such as the modal dialog boxes used in Bootstrap (http://getbootstrap.com/javascript/#modals).
Second, keeping address bars allows you and your users to check the URL for any discrepancies. Similarly, there is one fewer area that hijackers can exploit to phish you or your users.
