Chapter 2
Internetworking
The following topics are covered in this chapter:
- Understanding the Host-to-Host Communications Model
- Understanding Host-to-Host Communications
- OSI Reference Model
- OSI Model Layers and Their Functions
- Encapsulation and De-Encapsulation
- Peer-to-Peer Communication
- TCP/IP Suite
Welcome to the exciting world of internetworking. This chapter will really help you review your understanding of basic internetworking by focusing on how to connect networks using Cisco routers and switches. First, you need to know exactly what an internetwork is, right? You create an internetwork when you connect two or more networks via a router and configure a logical network addressing scheme with a protocol such as IP or IPv6.
I’ll be reviewing the following topics in this chapter:
- Internetworking basics
- Network segmentation
- How bridges, switches, and routers are used to physically and logically segment a network
- How routers are employed to create an internetwork
I’m also going to dissect the Open Systems Interconnection (OSI) model and describe each part to you in detail because you really need a good grasp of it for the solid foundation upon which you’ll build your Cisco networking knowledge. The OSI model has seven hierarchical layers that were developed to enable different networks to communicate reliably between disparate systems. Because this book is centering upon all things CCNA, it’s crucial for you to understand the OSI model as Cisco sees it, so that’s how I’ll be presenting the seven layers to you.
After you finish reading this chapter, you’ll encounter 20 review questions and three written labs. These are given to you to really lock the information from this chapter into your memory. So don’t skip them!
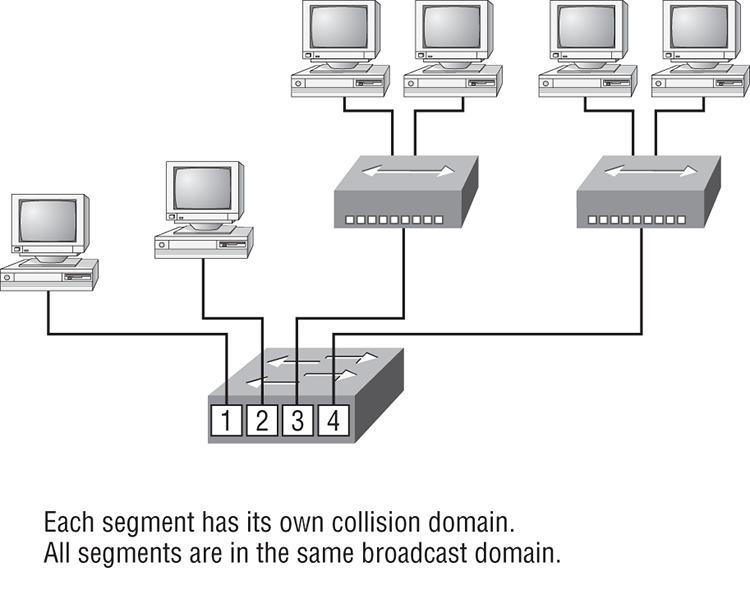
Internetworking Basics
It’s likely that at some point user response will dwindle to a slow crawl as your network grows and grows. And with all that growth, your LAN’s traffic congestion will reach epic proportions. The answer is to break up a really big network into a number of smaller ones—something called network segmentation. You do this by using devices like routers, switches, and bridges. Figure 2-1 displays a network that’s been segmented with a switch so that each network segment connected to the switch is now a separate collision domain. But make note of the fact that this network is still one broadcast domain.
Figure 2-1: A switch can replace the hub, breaking up collision domains.
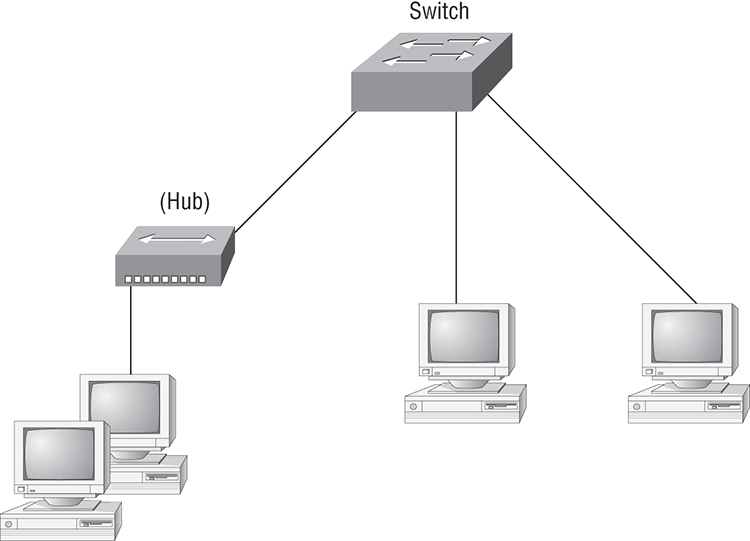
Keep in mind that the hub used in Figure 2-1 just extended the one collision domain from the switch port. Here’s a list of some of the things that commonly cause LAN traffic congestion:
- Too many hosts in a broadcast or collision domain
- Broadcast storms
- Too much multicast traffic
- Low bandwidth
- Adding hubs for connectivity to the network
Take another look at Figure 2-1—hubs don’t segment a network; they just connect network segments. So basically, it’s an inexpensive way to connect a couple of PCs together, which is great for home use and troubleshooting, but that’s about it!
Now, routers are used to connect networks and route packets of data from one network to another. Cisco became the de facto standard of routers because of its high-quality router products, great selection, and fantastic service. Routers, by default, break up a broadcast domain—the set of all devices on a network segment that hear all the broadcasts sent on that segment. Figure 2-2 shows a router in our little network that creates an internetwork and breaks up broadcast domains.
The network in Figure 2-2 is a pretty cool network. Each host is connected to its own collision domain, and the router has created two broadcast domains. And don’t forget that the router provides connections to WAN services as well! The router uses something called a serial interface for WAN connections, specifically, a V.35 physical interface on a Cisco router.
Figure 2-2: Routers create an internetwork.

Breaking up a broadcast domain is important because when a host or server sends a network broadcast, every device on the network must read and process that broadcast—unless you’ve got a router. When the router’s interface receives this broadcast, it can respond by basically saying, “Thanks, but no thanks,” and discard the broadcast without forwarding it on to other networks. Even though routers are known for breaking up broadcast domains by default, it’s important to remember that they break up collision domains as well.
There are two advantages of using routers in your network:
- They don’t forward broadcasts by default.
- They can filter the network based on layer 3 (Network layer) information (e.g., IP address).
Four router functions in your network can be listed as follows:
- Packet switching
- Packet filtering
- Internetwork communication
- Path selection
Unlike layer 2 switches, which forward or filter frames, routers (or layer 3 switches) use logical addressing and provide what is called packet switching. Routers can also provide packet filtering by using access lists, and when routers connect two or more networks together and use logical addressing (IP or IPv6), this is called an internetwork. Last, routers use a routing table (map of the internetwork) to make path selections and to forward packets to remote networks.
Conversely, switches aren’t used to create internetworks (they do not break up broadcast domains by default); they’re employed to add functionality to a network LAN. The main purpose of a switch is to make a LAN work better—to optimize its performance—providing more bandwidth for the LAN’s users. And switches don’t forward packets to other networks as routers do. Instead, they only “switch” frames from one port to another within the switched network. Okay, you may be thinking, “Wait a minute, what are frames and packets?” I’ll tell you all about them later, in Chapter 3, “Ethernet Technologies,” I promise!
By default, switches break up collision domains. This is an Ethernet term used to describe a network scenario wherein one particular device sends a packet on a network segment, forcing every other device on that same segment to pay attention to it. If at the same time a different device tries to transmit, leading to a collision, both devices must retransmit, one at a time. Not very efficient! This situation is typically found in a hub environment where each host segment connects to a hub that represents only one collision domain and only one broadcast domain. By contrast, each and every port on a switch represents its own collision domain.
The term bridging was introduced before routers and hubs were implemented, so it’s pretty common to hear people referring to bridges as switches and vice versa. That’s because bridges and switches basically do the same thing—break up collision domains on a LAN (in reality, you cannot buy a physical bridge these days, only LAN switches, but they use bridging technologies, so Cisco still refers to them as multiport bridges).
So what this means is that a switch is basically just a multiple-port bridge with more brainpower, right? Well, pretty much, but there are differences. Switches do provide this function, but they do so with greatly enhanced management ability and features. Plus, most of the time, bridges had only 2 or 4 ports. Yes, you could get your hands on a bridge with up to 16 ports, but that’s nothing compared to the hundreds available on some switches!
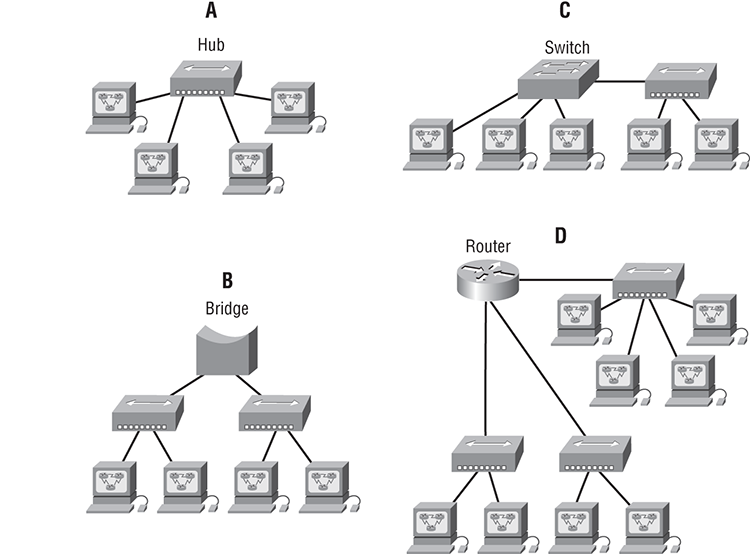
Figure 2-3 shows how a network would look with all these internetwork devices in place. Remember that the router will not only break up broadcast domains for every LAN interface, it will break up collision domains as well.
Figure 2-3: Internetworking devices
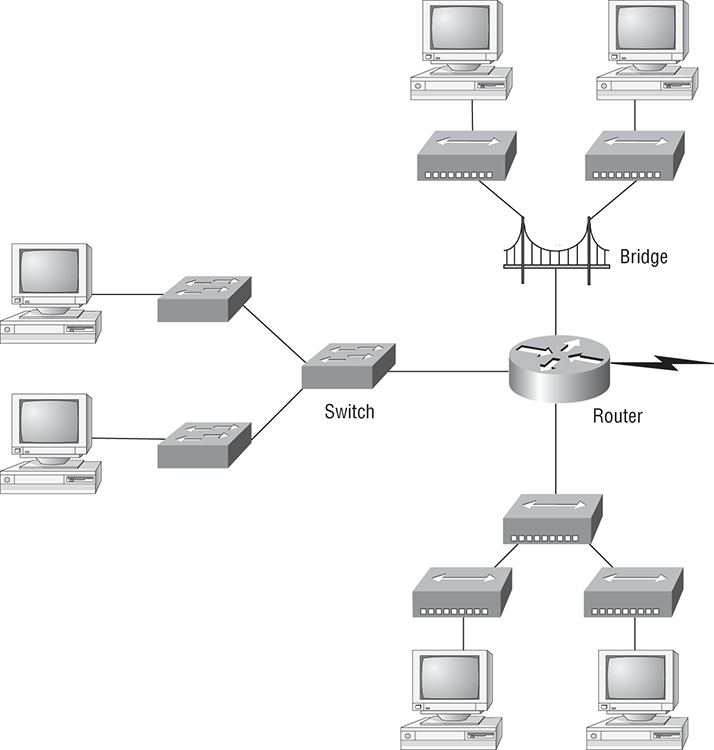
When you looked at Figure 2-3, did you notice that the router is found at center stage and that it connects each physical network together? We have to use this layout because of the older technologies involved—bridges and hubs.
On the top internetwork in Figure 2-3, you’ll notice that a bridge was used to connect the hubs to a router. The bridge breaks up collision domains, but all the hosts connected to both hubs are still crammed into the same broadcast domain. Also, the bridge only created two collision domains, so each device connected to a hub is in the same collision domain as every other device connected to that same hub. This is actually pretty lame, but it’s still better than having one collision domain for all hosts.
Notice something else: the three hubs at the bottom that are connected also connect to the router, creating one collision domain and one broadcast domain. This makes the bridged network look much better indeed!
The best network connected to the router is the LAN switch network on the left. Why? Because each port on that switch breaks up collision domains. But it’s not all good—all devices are still in the same broadcast domain. Do you remember why this can be a really bad thing? Because all devices must listen to all broadcasts transmitted, that’s why. And if your broadcast domains are too large, the users have less bandwidth and are required to process more broadcasts, and network response time will slow to a level that could cause office riots.
Once we have only switches in our network, things change a lot! Figure 2-4 shows the network that is typically found today.
Figure 2-4: Switched networks creating an internetwork

Okay, here I’ve placed the LAN switches at the center of the network world so the router is connecting only logical networks together. If I implemented this kind of setup, I’ve created virtual LANs (VLANs), something I’m going to tell you about in Chapter 11, “Layer 2 Switching Technologies.” So don’t stress. But it is really important to understand that even though you have a switched network, you still need a router (or layer 3 switch) to provide your inter-VLAN communication, or internetworking. Don’t forget that!
Obviously, the best network is one that’s correctly configured to meet the business requirements of the company it serves. LAN switches with routers, correctly placed in the network, are the best network design. This book will help you understand the basics of routers and switches so you can make good, informed decisions on a case-by-case basis.
Let’s go back to Figure 2-3. Looking at the figure, how many collision domains and broadcast domains are in this internetwork? Hopefully, you answered nine collision domains and three broadcast domains! The broadcast domains are definitely the easiest to see because only routers break up broadcast domains by default. And since there are three connections, that gives you three broadcast domains. But do you see the nine collision domains? Just in case that’s a no, I’ll explain. The all-hub network is one collision domain; the bridge network equals three collision domains. Add in the switch network of five collision domains—one for each switch port—and you’ve got a total of nine.
Now, in Figure 2-4, each port on the switch is a separate collision domain and each VLAN is a separate broadcast domain. But you still need a router for routing between VLANs. How many collision domains do you see here? I’m counting 10—remember that connections between the switches are considered a collision domain!
So now that you’ve gotten an introduction to internetworking and the various devices that live in an internetwork, it’s time to head into internetworking models.
Internetworking Models
When networks first came into being, computers could typically communicate only with computers from the same manufacturer. For example, companies ran either a complete DECnet solution or an IBM solution—not both together. In the late 1970s, the Open Systems Interconnection (OSI) reference model was created by the International Organization for Standardization (ISO) to break this barrier.
The OSI model was meant to help vendors create interoperable network devices and software in the form of protocols so that different vendor networks could work with each other. Like world peace, it’ll probably never happen completely, but it’s still a great goal.
The OSI model is the primary architectural model for networks. It describes how data and network information are communicated from an application on one computer through the network media to an application on another computer. The OSI reference model breaks this approach into layers.
In the following section, I am going to explain the layered approach and how we can use this approach to help us troubleshoot our internetworks.
The Layered Approach
A reference model is a conceptual blueprint of how communications should take place. It addresses all the processes required for effective communication and divides these processes into logical groupings called layers. When a communication system is designed in this manner, it’s known as layered architecture.
Think of it like this: you and some friends want to start a company. One of the first things you’ll do is sit down and think through what tasks must be done, who will do them, the order in which they will be done, and how they relate to each other. Ultimately, you might group these tasks into departments. Let’s say you decide to have an order-taking department, an inventory department, and a shipping department. Each of your departments has its own unique tasks, keeping its staff members busy and requiring them to focus on only their own duties.
In this scenario, I’m using departments as a metaphor for the layers in a communication system. For things to run smoothly, the staff of each department will have to trust and rely heavily upon the others to do their jobs and competently handle their unique responsibilities. In your planning sessions, you would probably take notes, recording the entire process to facilitate later discussions about standards of operation that will serve as your business blueprint, or reference model.
Once your business is launched, your department heads, each armed with the part of the blueprint relating to their own department, will need to develop practical methods to implement their assigned tasks. These practical methods, or protocols, will need to be compiled into a standard operating procedures manual and followed closely. Each of the various procedures in your manual will have been included for different reasons and have varying degrees of importance and implementation. If you form a partnership or acquire another company, it will be imperative that its business protocols—its business blueprint—match yours (or at least be compatible with it).
Similarly, software developers can use a reference model to understand computer communication processes and see what types of functions need to be accomplished on any one layer. If they are developing a protocol for a certain layer, all they need to concern themselves with is that specific layer’s functions, not those of any other layer. Another layer and protocol will handle the other functions. The technical term for this idea is binding. The communication processes that are related to each other are bound, or grouped together, at a particular layer.
Advantages of Reference Models
The OSI model is hierarchical, and the same benefits and advantages can apply to any layered model. The primary purpose of all such models, especially the OSI model, is to allow different vendors’ networks to interoperate.
Advantages of using the OSI layered model include, but are not limited to, the following:
- It divides the network communication process into smaller and simpler components, thus aiding component development, design, and troubleshooting.
- It allows multiple-vendor development through standardization of network components.
- It encourages industry standardization by defining what functions occur at each layer of the model.
- It allows various types of network hardware and software to communicate.
- It prevents changes in one layer from affecting other layers, so it does not hamper development.
The OSI Reference Model
One of the greatest functions of the OSI specifications is to assist in data transfer between disparate hosts—meaning, for example, that they enable us to transfer data between a Unix host and a PC or a Mac.
The OSI isn’t a physical model, though. Rather, it’s a set of guidelines that application developers can use to create and implement applications that run on a network. It also provides a framework for creating and implementing networking standards, devices, and internetworking schemes.
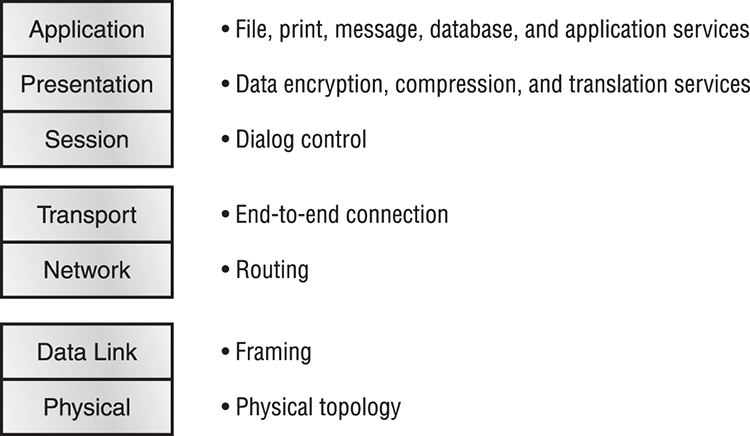
The OSI has seven different layers, divided into two groups. The top three layers define how the applications within the end stations will communicate with each other and with users. The bottom four layers define how data is transmitted end to end. Figure 2-5 shows the three upper layers functions, and Figure 2-6 shows the four lower layers functions.
When you study Figure 2-5, understand that the user interfaces with the computer at the Application layer and also that the upper layers are responsible for applications communicating between hosts. Remember that none of the upper layers knows anything about networking or network addresses. That’s the responsibility of the four bottom layers.
Figure 2-5: The upper layers

Figure 2-6: The lower layers
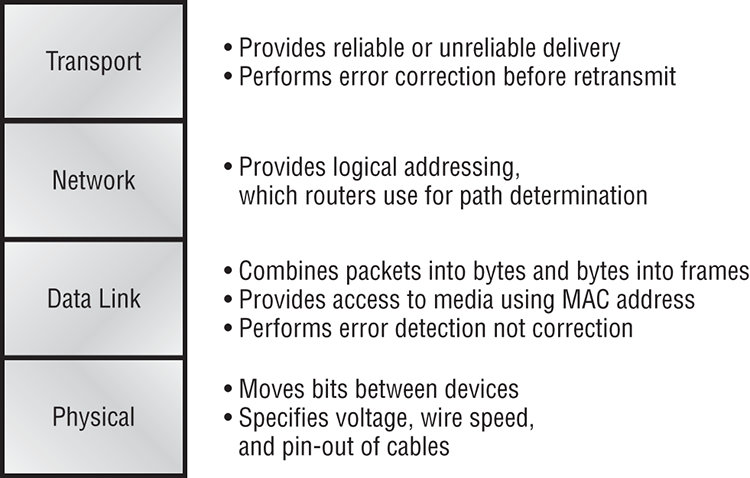
In Figure 2-6, you can see that it’s the four bottom layers that define how data is transferred through a physical wire or through switches and routers. These bottom layers also determine how to rebuild a data stream from a transmitting host to a destination host’s application.
The following network devices operate at all seven layers of the OSI model:
- Network management stations (NMSs)
- Web and application servers
- Gateways (not default gateways)
- Network hosts
Basically, the ISO is pretty much the Emily Post of the network protocol world. Just as Ms. Post wrote the book setting the standards—or protocols—for human social interaction, the ISO developed the OSI reference model as the precedent and guide for an open network protocol set. Defining the etiquette of communication models, it remains today the most popular means of comparison for protocol suites.
As mentioned, the OSI reference model has the following seven layers:
- Application layer (layer 7)
- Presentation layer (layer 6)
- Session layer (layer 5)
- Transport layer (layer 4)
- Network layer (layer 3)
- Data Link layer (layer 2)
- Physical layer (layer 1)
Figure 2-7 shows a summary of the functions defined in Figure 2-5 and Figure 2-6 at layer of the OSI model.
With this in hand, you’re now ready to explore each layer’s function in detail.
Figure 2-7: Layer functions
The Application Layer
The Application layer of the OSI model marks the spot where users actually communicate to the computer. This layer comes into play only when it’s apparent that access to the network is going to be needed soon. Take the case of Internet Explorer (IE). You could uninstall every trace of networking components from a system, such as TCP/IP, NIC card, and so on, and you could still use IE to view a local HTML document—no problem. But things would definitely get messy if you tried to do something like view an HTML document that must be retrieved using HTTP or nab a file with FTP or TFTP. That’s because IE will respond to requests such as those by attempting to access the Application layer. And what’s happening is that the Application layer is acting as an interface between the actual application program—which isn’t at all a part of the layered structure—and the next layer down by providing ways for the application to send information down through the protocol stack. In other words, IE doesn’t truly reside within the Application layer—it interfaces with Application layer protocols when it needs to deal with remote resources.
The Application layer is also responsible for identifying and establishing the availability of the intended communication partner and determining whether sufficient resources for the intended communication exist.
These tasks are important because computer applications sometimes require more than only desktop resources. Often, they’ll unite communicating components from more than one network application. Prime examples are file transfers and email as well as enabling remote access, network management activities, client/server processes, and information location. Many network applications provide services for communication over enterprise networks, but for present and future internetworking, the need is fast developing to reach beyond the limits of current physical networking.
The Presentation Layer
The Presentation layer gets its name from its purpose: it presents data to the Application layer and is responsible for data translation and code formatting.
This layer is essentially a translator and provides coding and conversion functions. A successful data-transfer technique is to adapt the data into a standard format before transmission. Computers are configured to receive this generically formatted data and then convert the data back into its native format for actual reading (for example, EBCDIC to ASCII). By providing translation services, the Presentation layer ensures that data transferred from the Application layer of one system can be read by the Application layer of another one.
The OSI has protocol standards that define how standard data should be formatted. Tasks like data compression, decompression, encryption, and decryption are associated with this layer. Some Presentation layer standards are involved in multimedia operations too.
The Session Layer
The Session layer is responsible for setting up, managing, and then tearing down sessions between Presentation layer entities. This layer also provides dialog control between devices, or nodes. It coordinates communication between systems and serves to organize their communication by offering three different modes: simplex, half duplex, and full duplex. To sum up, the Session layer basically keeps different applications’ data separate from other applications’ data.
The Transport Layer
The Transport layer segments and reassembles data into a data stream. Services located in the Transport layer segment and reassemble data from upper-layer applications and unite it into the same data stream. They provide end-to-end data transport services and can establish a logical connection between the sending host and destination host on an internetwork.
Some of you are probably familiar with TCP and UDP already. (But if you’re not, no worries—I’ll tell you all about them in Chapter 4.) If so, you know that both work at the Transport layer and that TCP is a reliable service and UDP is not. This means that application developers have more options because they have a choice between the two protocols when working with TCP/IP protocols.
The Transport layer is responsible for providing mechanisms for multiplexing upper-layer applications, establishing sessions, and tearing down virtual circuits. It also hides details of any network-dependent information from the higher layers by providing transparent data transfer.
The Transport layer can be connectionless or connection oriented. However, Cisco is mostly concerned with you understanding the connection-oriented portion of the Transport layer. The following sections will provide the skinny on the connection-oriented (reliable) protocol of the Transport layer.
Flow Control
Data integrity is ensured at the Transport layer by maintaining flow control and by allowing applications to request reliable data transport between systems. Flow control prevents a sending host on one side of the connection from overflowing the buffers in the receiving host—an event that can result in lost data. Reliable data transport employs a connection-oriented communications session between systems, and the protocols involved ensure that the following will be achieved:
- The segments delivered are acknowledged back to the sender upon their reception.
- Any segments not acknowledged are retransmitted.
- Segments are sequenced back into their proper order upon arrival at their destination.
- A manageable data flow is maintained in order to avoid congestion, overloading, and data loss.
Connection-Oriented Communication
In reliable transport operation, a device that wants to transmit sets up a connection-oriented communication session with a remote device by creating a session. The transmitting device first establishes a connection-oriented session with its peer system, which is called a call setup or a three-way handshake. Data is then transferred; when the transfer is finished, a call termination takes place to tear down the virtual circuit.
Figure 2-8 depicts a typical reliable session taking place between sending and receiving systems. Looking at it, you can see that both hosts’ application programs begin by notifying their individual operating systems that a connection is about to be initiated. The two operating systems communicate by sending messages over the network confirming that the transfer is approved and that both sides are ready for it to take place. After all of this required synchronization takes place, a connection is fully established and the data transfer begins (this virtual circuit setup is called overhead!).
While the information is being transferred between hosts, the two machines periodically check in with each other, communicating through their protocol software to ensure that all is going well and that the data is being received properly.
Figure 2-8: Establishing a connection-oriented session
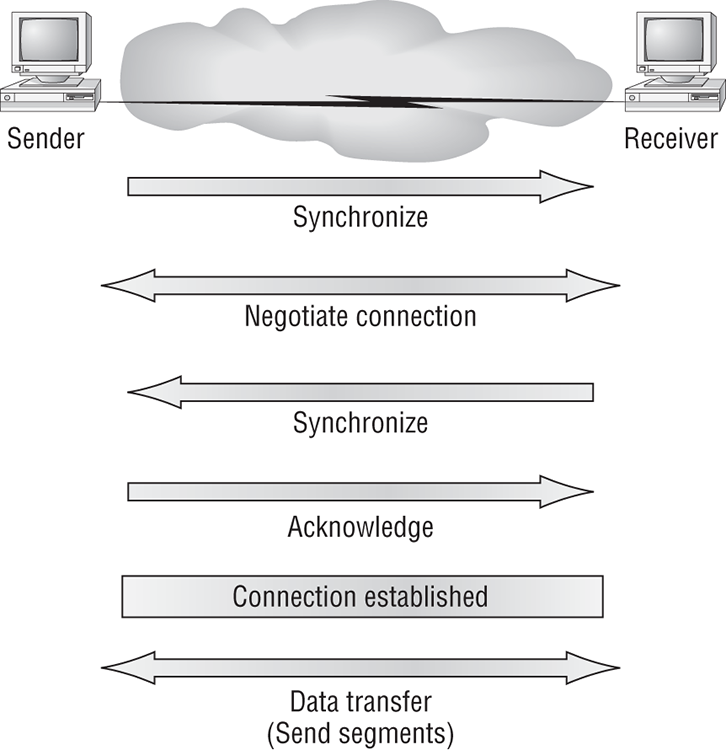
Here’s a summary of the steps in the connection-oriented session—the three-way handshake—pictured in Figure 2-9:
- The first “connection agreement” segment is a request for synchronization.
- The next segments acknowledge the request and establish connection parameters—the rules—between hosts. These segments request that the receiver’s sequencing is synchronized here as well so that a bidirectional connection is formed.
- The final segment is also an acknowledgment. It notifies the destination host that the connection agreement has been accepted and that the actual connection has been established. Data transfer can now begin.
Figure 2-9: The three-way handshake

Sounds pretty simple, but things don’t always flow so smoothly. Sometimes during a transfer, congestion can occur because a high-speed computer is generating data traffic a lot faster than the network can handle transferring. A bunch of computers simultaneously sending datagrams through a single gateway or destination can also botch things up nicely. In the latter case, a gateway or destination can become congested even though no single source caused the problem. In either case, the problem is basically akin to a freeway bottleneck—too much traffic for too small a capacity. It’s not usually one car that’s the problem; there are simply too many cars on that freeway.
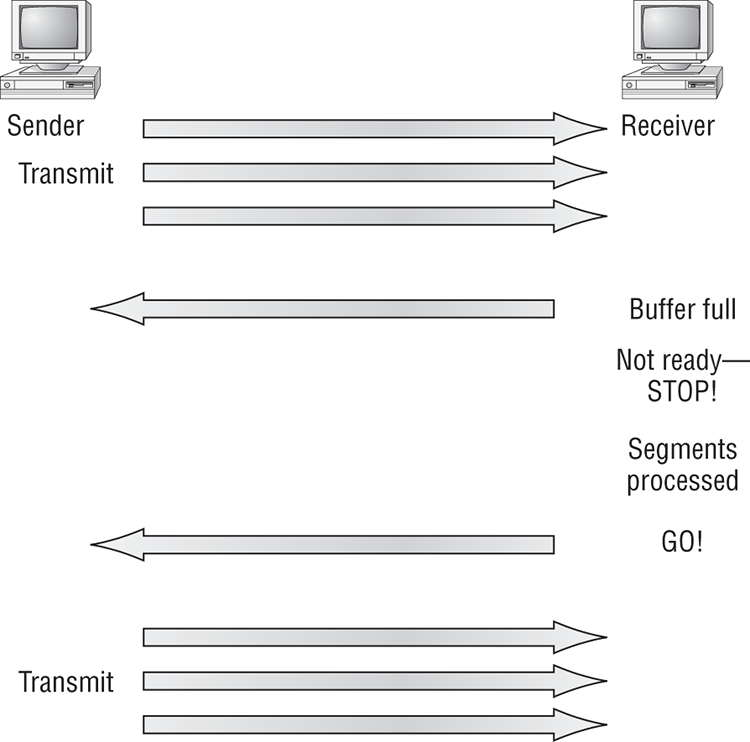
Okay, so what happens when a machine receives a flood of datagrams too quickly for it to process? It stores them in a memory section called a buffer. But this buffering action can solve the problem only if the datagrams are part of a small burst. If not, and the datagram deluge continues, a device’s memory will eventually be exhausted, its flood capacity will be exceeded, and it will react by discarding any additional datagrams that arrive.
No huge worries here, though. Because of the transport function, network flood control systems really work quite well. Instead of dumping data and allowing data to be lost, the transport can issue a “not ready” indicator to the sender, or source, of the flood (as shown in Figure 2-10). This mechanism works kind of like a stoplight, signaling the sending device to stop transmitting segment traffic to its overwhelmed peer. After the peer receiver processes the segments already in its memory reservoir—its buffer—it sends out a “ready” transport indicator. When the machine waiting to transmit the rest of its datagrams receives this “go” indictor, it resumes its transmission.
Figure 2-10: Transmitting segments with flow control
In fundamental, reliable, connection-oriented data transfer, datagrams are delivered to the receiving host in exactly the same sequence they’re transmitted—and the transmission fails if this order is breached! If any data segments are lost, duplicated, or damaged along the way, a failure will occur. This problem is solved by having the receiving host acknowledge that it has received each and every data segment.
A service is considered connection-oriented if it has the following characteristics:
- A virtual circuit is set up (e.g., a three-way handshake).
- It uses sequencing.
- It uses acknowledgments.
- It uses flow control.
Windowing
Ideally, data throughput happens quickly and efficiently. And as you can imagine, it would be slow if the transmitting machine had to wait for an acknowledgment after sending each segment. But because there’s time available after the sender transmits the data segment and before it finishes processing acknowledgments from the receiving machine, the sender uses the break as an opportunity to transmit more data. The quantity of data segments (measured in bytes) that the transmitting machine is allowed to send without receiving an acknowledgment for them is called a window.
So the size of the window controls how much information is transferred from one end to the other. While some protocols quantify information by observing the number of packets, TCP/IP measures it by counting the number of bytes.
As you can see in Figure 2-11, there are two window sizes—one set to 1 and one set to 3.
When you’ve configured a window size of 1, the sending machine waits for an acknowledgment for each data segment it transmits before transmitting another. If you’ve configured a window size of 3, it’s allowed to transmit three data segments before an acknowledgment is received.
Figure 2-11: Windowing
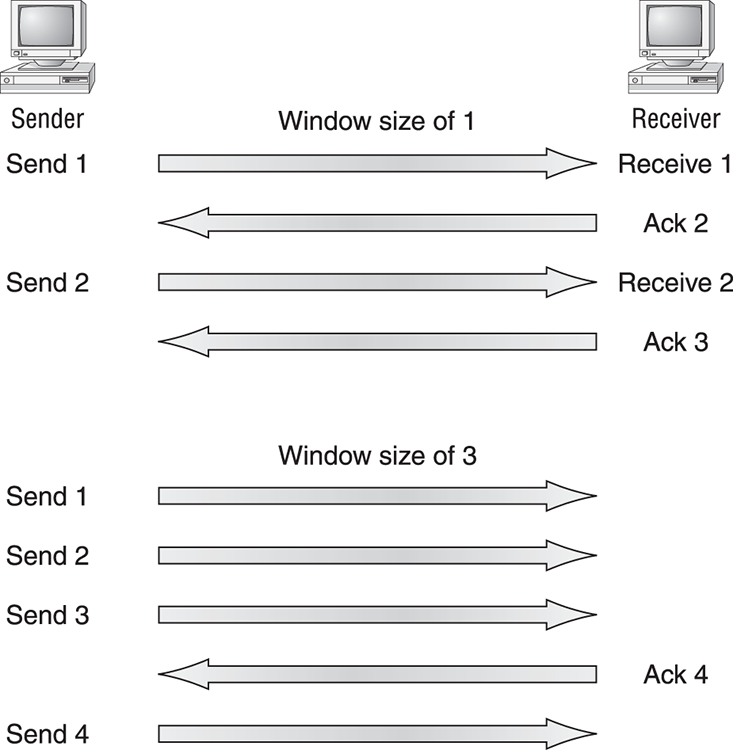
In this simplified example, both the sending and receiving machines are workstations. In reality, this is not done in simple numbers but in the amount of bytes that can be sent.
Acknowledgments
Reliable data delivery ensures the integrity of a stream of data sent from one machine to the other through a fully functional data link. It guarantees that the data won’t be duplicated or lost. This is achieved through something called positive acknowledgment with retransmission—a technique that requires a receiving machine to communicate with the transmitting source by sending an acknowledgment message back to the sender when it receives data. The sender documents each segment measured in bytes; it then sends and waits for this acknowledgment before sending the next segment round of bytes. When it sends a segment, the transmitting machine starts a timer and retransmits if it expires before an acknowledgment is returned from the receiving end.
In Figure 2-12, the sending machine transmits segments 1, 2, and 3.
Figure 2-12: Transport layer reliable delivery

The receiving node acknowledges it has received them by requesting segment 4 with an ACK 4. When it receives the acknowledgment, the sender then transmits segments 4, 5, and 6. If segment 5 doesn’t make it to the destination, the receiving node acknowledges that event with a request for the segment to be resent. The sending machine will then resend the lost segment and wait for an acknowledgment, which it must receive in order to move on to the transmission of segment 7.
The Network Layer
The Network layer (also called layer 3) manages device addressing, tracks the location of devices on the network, and determines the best way to move data, which means that the Network layer must transport traffic between devices that aren’t locally attached. Routers (layer 3 devices) are specified at the Network layer and provide the routing services within an internetwork.
It happens like this: First, when a packet is received on a router interface, the destination IP address is checked. If the packet isn’t destined for that particular router, it will look up the destination network address in the routing table. Once the router chooses an exit interface, the packet will be sent to that interface to be framed and sent out on the local network. If the router can’t find an entry for the packet’s destination network in the routing table, the router drops the packet.
Two types of packets are used at the Network layer: data and route updates.
Figure 2-13 shows an example of two routing tables.
Figure 2-13: Routing table used in a router

The routing table used in a router includes the following information:
And as I mentioned earlier, routers break up broadcast domains, which means that by default, broadcasts aren’t forwarded through a router. Do you remember why this is a good thing? Routers also break up collision domains, but you can also do that using layer 2 (Data Link layer) switches. Because each interface in a router represents a separate network, it must be assigned unique network identification numbers, and each host on the network connected to that router must use the same network number. Figure 2-14 shows how a router works in an internetwork.
Figure 2-14: A router in an internetwork

Here are some points about routers that you should really commit to memory:
- Routers, by default, will not forward any broadcast or multicast packets.
- Routers use the logical address in a Network layer header to determine the next hop router to forward the packet to.
- Routers can use access lists, created by an administrator, to control security on the types of packets that are allowed to enter or exit an interface.
- Routers can provide layer 2 bridging functions if needed and can simultaneously route through the same interface.
- Layer 3 devices (routers in this case) provide connections between virtual LANs (VLANs).
- Routers can provide quality of service (QoS) for specific types of network traffic.
The Data Link Layer
The Data Link layer provides the physical transmission of the data and handles error notification, network topology, and flow control. This means that the Data Link layer will ensure that messages are delivered to the proper device on a LAN using hardware addresses and will translate messages from the Network layer into bits for the Physical layer to transmit.
The Data Link layer formats the message into pieces, each called a data frame, and adds a customized header containing the hardware destination and source address. This added information forms a sort of capsule that surrounds the original message in much the same way that engines, navigational devices, and other tools were attached to the lunar modules of the Apollo project. These various pieces of equipment were useful only during certain stages of space flight and were stripped off the module and discarded when their designated stage was complete. Data traveling through networks is similar.
Figure 2-15 shows the Data Link layer with the Ethernet and IEEE specifications. When you check it out, notice that the IEEE 802.2 standard is used in conjunction with and adds functionality to the other IEEE standards.
Figure 2-15: Data Link layer

It’s important for you to understand that routers, which work at the Network layer, don’t care at all about where a particular host is located. They’re only concerned about where networks are located and the best way to reach them—including remote ones. Routers are totally obsessive when it comes to networks. And for once, this is a good thing! It’s the Data Link layer that’s responsible for the actual unique identification of each device that resides on a local network.
For a host to send packets to individual hosts on a local network as well as transmit packets between routers, the Data Link layer uses hardware addressing. Each time a packet is sent between routers, it’s framed with control information at the Data Link layer, but that information is stripped off at the receiving router and only the original packet is left completely intact. This framing of the packet continues for each hop until the packet is finally delivered to the correct receiving host. It’s really important to understand that the packet itself is never altered along the route; it’s only encapsulated with the type of control information required for it to be properly passed on to the different media types.
The IEEE Ethernet Data Link layer has two sublayers:
The switches and bridges I talked about near the beginning of the chapter both work at the Data Link layer and filter the network using hardware (MAC) addresses. We will look at these in the following section.
Switches and Bridges at the Data Link Layer
Layer 2 switching is considered hardware-based bridging because it uses specialized hardware called an application-specific integrated circuit (ASIC). ASICs can run up to gigabit speeds with very low latency rates.
Bridges and switches read each frame as it passes through the network. The layer 2 device then puts the source hardware address in a filter table and keeps track of which port the frame was received on. This information (logged in the bridge’s or switch’s filter table) is what helps the machine determine the location of the specific sending device. Figure 2-16 shows a switch in an internetwork.
The real estate business is all about location, location, location, and it’s the same way for both layer 2 and layer 3 devices. Though both need to be able to negotiate the network, it’s crucial to remember that they’re concerned with very different parts of it. Primarily, layer 3 machines (such as routers) need to locate specific networks, whereas layer 2 machines (switches and bridges) need to eventually locate specific devices. So, networks are to routers as individual devices are to switches and bridges. And routing tables that “map” the internetwork are for routers as filter tables that “map” individual devices are for switches and bridges.
After a filter table is built on the layer 2 device, it will forward frames only to the segment where the destination hardware address is located. If the destination device is on the same segment as the frame, the layer 2 device will block the frame from going to any other segments. If the destination is on a different segment, the frame can be transmitted only to that segment. This is called transparent bridging.
Figure 2-16: A switch in an internetwork
When a switch interface receives a frame with a destination hardware address that isn’t found in the device’s filter table, it will forward the frame to all connected segments. If the unknown device that was sent the “mystery frame” replies to this forwarding action, the switch updates its filter table regarding that device’s location. But in the event the destination address of the transmitting frame is a broadcast address, the switch will forward all broadcasts to every connected segment by default.
All devices that the broadcast is forwarded to are considered to be in the same broadcast domain. This can be a problem; layer 2 devices propagate layer 2 broadcast storms that choke performance, and the only way to stop a broadcast storm from propagating through an internetwork is with a layer 3 device—a router.
The biggest benefit of using switches instead of hubs in your internetwork is that each switch port is actually its own collision domain. (Conversely, a hub creates one large collision domain.) But even armed with a switch, you still don’t break up broadcast domains by default. Neither switches nor bridges will do that. They’ll simply forward all broadcasts instead.
Another benefit of LAN switching over hub-centered implementations is that each device on every segment plugged into a switch can transmit simultaneously—at least, they can as long as there is only one host on each port and a hub isn’t plugged into a switch port. As you might have guessed, hubs allow only one device per network segment to communicate at a time.
The Physical Layer
Finally arriving at the bottom, we find that the Physical layer does two things: it sends bits and receives bits. Bits come only in values of 1 or 0—a Morse code with numerical values. The Physical layer communicates directly with the various types of actual communication media. Different kinds of media represent these bit values in different ways. Some use audio tones, while others employ state transitions—changes in voltage from high to low and low to high. Specific protocols are needed for each type of media to describe the proper bit patterns to be used, how data is encoded into media signals, and the various qualities of the physical media’s attachment interface.
The Physical layer specifies the electrical, mechanical, procedural, and functional requirements for activating, maintaining, and deactivating a physical link between end systems. This layer is also where you identify the interface between the data terminal equipment (DTE) and the data communication equipment (DCE). (Some old phone-company employees still call DCE data circuit-terminating equipment.) The DCE is usually located at the service provider, while the DTE is the attached device. The services available to the DTE are most often accessed via a modem or channel service unit/data service unit (CSU/DSU).
The Physical layer’s connectors and different physical topologies are defined by the OSI as standards, allowing disparate systems to communicate. The CCNA objectives are interested only in the IEEE Ethernet standards.
Hubs at the Physical Layer
A hub is really a multiple-port repeater. A repeater receives a digital signal and reamplifies or regenerates that signal and then forwards the digital signal out all active ports without looking at any data. An active hub does the same thing. Any digital signal received from a segment on a hub port is regenerated or reamplified and transmitted out all other ports on the hub. This means all devices plugged into a hub are in the same collision domain as well as in the same broadcast domain. Figure 2-17 shows a hub in a network.
Figure 2-17: A hub in a network

Hubs, like repeaters, don’t examine any of the traffic as it enters and is then transmitted out to the other parts of the physical media. Every device connected to the hub, or hubs, must listen if one device transmits. A physical star network—where the hub is a central device and cables extend in all directions out from it—is the type of topology a hub creates. Visually, the design really does resemble a star, whereas Ethernet networks run a logical bus topology, meaning that the signal has to run through the network from end to end.
Summary
Whew!—You made it through! You’re now armed with a ton of fundamental information; you’re ready to build upon it and are well on your way to certification.
I started by discussing simple, basic networking and the differences between collision and broadcast domains.
I then discussed the OSI model—the seven-layer model used to help application developers design applications that can run on any type of system or network. Each layer has its special jobs and select responsibilities within the model to ensure that solid, effective communications do, in fact, occur. I provided you with complete details of each layer and discussed how Cisco views the specifications of the OSI model.
In addition, each layer in the OSI model specifies different types of devices, and I described these different devices used at each layer.
Remember that hubs are Physical layer devices and repeat the digital signal to all segments except the one from which it was received. Switches segment the network using hardware addresses and break up collision domains. Routers break up broadcast domains (and collision domains) and use logical addressing to send packets through an internetwork.
Exam Essentials
Written Labs
In this section, you’ll complete the following labs to make sure you’ve got the information and concepts contained within them fully dialed in:
You can find the answers in Appendix A.
Written Lab 2.1: OSI Questions
Answer the following questions about the OSI model:
1. Which layer chooses and determines the availability of communicating partners along with the resources necessary to make the connection, coordinates partnering applications, and forms a consensus on procedures for controlling data integrity and error recovery?
2. Which layer is responsible for converting data packets from the Data Link layer into electrical signals?
3. At which layer is routing implemented, enabling connections and path selection between two end systems?
4. Which layer defines how data is formatted, presented, encoded, and converted for use on the network?
5. Which layer is responsible for creating, managing, and terminating sessions between applications?
6. Which layer ensures the trustworthy transmission of data across a physical link and is primarily concerned with physical addressing, line discipline, network topology, error notification, ordered delivery of frames, and flow control?
7. Which layer is used for reliable communication between end nodes over the network and provides mechanisms for establishing, maintaining, and terminating virtual circuits; transport-fault detection and recovery; and controlling the flow of information?
8. Which layer provides logical addressing that routers will use for path determination?
9. Which layer specifies voltage, wire speed, and pin-out of cables and moves bits between devices?
10. Which layer combines bits into bytes and bytes into frames, uses MAC addressing, and provides error detection?
11. Which layer is responsible for keeping the data from different applications separate on the network?
12. Which layer is represented by frames?
13. Which layer is represented by segments?
14. Which layer is represented by packets?
15. Which layer is represented by bits?
16. Which layer of the OSI model is associated with the reliable transmission of datagrams?
17. Which layer segments and reassembles data into a data stream?
18. Which layer provides the physical transmission of the data and handles error notification, network topology, and flow control?
19. Which layer manages device addressing, tracks the location of devices on the network, and determines the best way to move data?
20. What is the bit length and expression form of a MAC address?
Written Lab 2.2: Defining the OSI Layers and Devices
Fill in the blanks with the appropriate layer of the OSI or hub, switch, or router device.
| Description | Device or OSI Layer |
| This device sends and receives information about the Network layer. | |
| This layer creates a virtual circuit before transmitting between two end stations. | |
| This device uses hardware addresses to filter a network. | |
| Ethernet is defined at these layers. | |
| This layer supports flow control, sequencing, and acknowledgments. | |
| This device can measure the distance to a remote network. | |
| Logical addressing is used at this layer. | |
| Hardware addresses are defined at this layer. | |
| This device creates one big collision domain and one large broadcast domain. | |
| This device creates many smaller collision domains, but the network is still one large broadcast domain. | |
| This device can never run full duplex. | |
| This device breaks up collision domains and broadcast domains. |
Written Lab 2.3: Identifying Collision and Broadcast Domains
1. In the following exhibit, identify the number of collision domains and broadcast domains in each specified device. Each device is represented by a letter:
Review Questions
You can find the answers in Appendix B.
1. A receiving host has failed to receive all of the segments that it should acknowledge. What can the host do to improve the reliability of this communication session?
A. Send a different source port number.
B. Restart the virtual circuit.
C. Decrease the sequence number.
D. Decrease the window size.
2. Which layer of the OSI model is associated with the reliable transmission of datagrams?
A. Transport
B. Network
C. Data Link
D. Physical
3. Which layer 1 devices can be used to enlarge the area covered by a single LAN segment? (Choose two.)
A. Switch
B. NIC
C. Hub
D. Repeater
E. RJ45 transceiver
4. Segmentation of a data stream happens at which layer of the OSI model?
A. Physical
B. Data Link
C. Network
D. Transport
5. Which of the following describe the main router functions? (Choose four.)
A. Packet switching
B. Collision prevention
C. Packet filtering
D. Broadcast domain enlargement
E. Internetwork communication
F. Broadcast forwarding
G. Path selection
6. Routers operate at layer ___. LAN switches operate at layer ___. Ethernet hubs operate at layer ___. Word processing operates at layer ___.
A. 3, 3, 1, 7
B. 3, 2, 1, none
C. 3, 2, 1, 7
D. 2, 3, 1, 7
E. 3, 3, 2, none
7. Which statement describes the function of the OSI Transport layer?
A. It provides the connectivity and path selection between two host systems that may be located on geographically separated networks.
B. It defines how data is formatted for transmission and how access to the physical media is controlled.
C. It establishes, manages, and terminates sessions between two communicating hosts.
D. It segments data from the system of the sending host and reassembles the data into a data stream on the system of the receiving host.
8. Why does the data communication industry use the layered OSI reference model? (Choose two.)
A. It divides the network communication process into smaller and simpler components, thus aiding component development and design and troubleshooting.
B. It enables equipment from different vendors to use the same electronic components, thus saving research and development funds.
C. It supports the evolution of multiple competing standards and thus provides business opportunities for equipment manufacturers.
D. It encourages industry standardization by defining what functions occur at each layer of the model.
E. It provides a framework by which changes in functionality in one layer require changes in other layers.
9. What are two purposes for segmentation with a bridge?
A. To add more broadcast domains
B. To create more collision domains
C. To add more bandwidth for users
D. To allow more broadcasts for users
10. Which of the following is not a cause of LAN congestion?
A. Too many hosts in a broadcast domain
B. Adding switches for connectivity to the network
C. Broadcast storms
D. Low bandwidth
11. If a switch has three computers connected to it, with no VLANs present, how many broadcast and collision domains is the switch creating?
A. Three broadcast and one collision
B. Three broadcast and three collision
C. One broadcast and three collision
D. One broadcast and one collision
12. Which two layers of the OSI model relate to the transmission of bits over the wire and packet forwarding based on destination IP address? (Choose two.)
A. 4
B. 3
C. 2
D. 1
13. Which of the following are types of flow control? (Choose all that apply.)
A. Buffering
B. Cut-through
C. Windowing
D. Congestion avoidance
E. VLANs
14. If a hub has three computers connected to it, how many broadcast and collision domains is the hub creating?
A. Three broadcast and one collision
B. Three broadcast and three collision
C. One broadcast and three collision
D. One broadcast and one collision
15. What is the purpose of flow control?
A. To ensure that data is retransmitted if an acknowledgment is not received
B. To reassemble segments in the correct order at the destination device
C. To provide a means for the receiver to govern the amount of data sent by the sender
D. To regulate the size of each segment
16. Which definitions are used to describe data at Layers 1, 2, and 4 of the OSI model? (Choose three.)
A. Best-effort packet delivery
B. Packets
C. Frames
D. Bits
E. Segments
17. Which of the following is not a benefit of reference models such as the OSI model?
A. It allows changes on one layer to affect operations on all other layers as well.
B. It divides the network communication process into smaller and simpler components, thus aiding component development, design, and troubleshooting.
C. It allows multiple-vendor development through standardization of network components.
D. It allows various types of network hardware and software to communicate.
18. Which of the following devices do not operate at all levels of the OSI model?
A. Network management stations (NMSs)
B. Routers
C. Web and application servers
D. Network hosts
19. When an HTTP document must be retrieved from a location other than the local machine, what layer of the OSI model must be accessed first?
A. Presentation
B. Transport
C. Application
D. Network
20. Which layer of the OSI model offers three different modes of communication: simplex, half duplex, and full duplex?
A. Presentation
B. Transport
C. Application
D. Session
