Due to the rapid development in smartphones and their applications resulting from the development of technology and communication, and due to their ease of mobility, cost, and energy consumption, smartphones have replaced computers in many uses. The WhatsApp (WA) application is considered to be the largest messaging application around the world and an important source of information; recently they added a new algorithm that works on end-to-end encryption features, which creates a major challenge for forensic investigators and analysts. This chapter explains how to extract the encryption key from WA, encrypt databases, and extract valuable artifacts that are presented and stored in the Android and iOS systems, as a way to present and analyze artifacts extracted from the latest version of WA to discover traces of new and valuable evidence and artifacts to help investigators and forensic analysts in the investigation. This means using many tools, devices, and types of software for portable devices specializing in digital forensics; many tools used in this chapter were used on a free-trial basis.
WA Architecture
WA Experiment
Tools Used in the Examination Process for iOS
Tools Used in the Acquisition Process for Android
iOS Analysis Stage
Android Analysis Stage
Examination on a Backup Taken by iTunes
Examination on a Backup Taken from the Connected Device
Forensic Tools Comparison
WA Architecture
After the rapid and exponential development in communication technology and the Internet, also accelerated development in smartphones and their data connectivity like 3G and 4G. Social networking and instant messaging (IM) companies developed their mobile applications. The mobile forensic method divides the investigation process into four stages: seizure, acquisition, analysis, and reporting. Here, the mobile forensic process was used in an investigation over iOS and Android smartphones, where a digital crime was assumed to be committed through WA. First, during the seizure stage, the smartphones were identified, preserved, documented, secured, and disconnected from all types of networks. The acquisition stage was completed by the phone’s imaging process and the hash value (MD5) was calculated. The analysis stage was completed by accessing chat details and logs, call logs, and multimedia to determine the evidence. The investigation process was carried out according to a legal framework and approved procedures that regulate the process by monitoring its stages to ensure that evidence is protected from alteration or destruction, and to ensure that the witness’s report is admissible in court. Finally, the investigation process and evidence were reported. In conclusion, WA forensic artifacts could be analyzed and discovered successfully using the mobile forensic process.
WA is a popular IM application in smartphones. WA allows users to exchange text messages, images, video files, audio files, document files, pdf files, and many others. WA allows users to create user groups to send messages and files to all group members. WA also allows the user to control personal profile information such as name, profile photo, and information about the user [8]. WA messaging is done in end-to-end encryption, and therefore no man-in-the-middle can read messages between two WA users [9]. WA stores its data in the mobile phone’s internal memory. WA automatically connects to the phone contacts database, detects the contacts that use the WA application, and adds them to its database. The WA application also includes a procedure named “com.whatsapp”, which is a procedure for operating the external media management service and the messaging service that runs in the background, as this procedure works when turning on the smartphone [10]. WA used the SQLite database “ChatStorage.sqlit” to save messages that were exchanged between users and other information from the user activities on WA [11].
Among the many IM applications on smartphones, WA has become the most popular IM application [2]. According to a statistic made by Statista in October 2020 for the most popular and widespread IM application based on the number of active users per month [3], WA is the most used by 2 billion active users, followed by Facebook Messenger (1.3 billion), WeChat (1.206 billion), QQ (648 million), Snapchat (433 million), and Telegram (400 million active users).
Cybercrime is increasing exponentially and in various ways and for different purposes, including personal fund gain, commercial competition, theft of intellectual property, personal theft, bullying, harassment, money laundering, terrorism, and so on. It’s always necessary to legally deal with cybercrimes, investigate them, and prosecute cybercriminals [4]. As well, there must be specialized laws to define the tools and types of cybercrime. Therefore, specialized law enforcement agencies must be founded to investigate and present it to the judiciary. Additionally, the penal laws must be developed to address this type of crime [5].
Most countries around the world are issuing cybercrime laws. Specialized law enforcement agencies are also being founded to investigate this type of crime [6]. The state of Palestine, like many other countries, has issued a cybercrime law by Decree No. 10 of 2018. This law defines activities, tools, and terminology related to cybercrime, and determines the law enforcement agencies that are responsible for the investigation and prosecution of cybercrime and the penalties for these crimes [7].

WA transmission

WA database structure
This chapter aims to explore the artifacts in WA on iOS and Android platforms and the use of tools related to the digital investigation to access digital evidence in WA by extracting messages and calls, analyzing them, and linking them in a chronological sequence to reach the digital evidence of the case.
Old versions of WA used the SQLite database “msgstore.db” to save messages that were exchanged between users; this database was unencrypted. Because unencrypting the database led to easy access to the details of the messages stored in it, to bypass this problem and to achieve better protection for users’ privacy, an encryption mechanism was developed for the WA database on the Android platform using an advanced encryption algorithm (AES) with an encryption key (192-bit length). As a result, the database name has changed to msgstore.db.crypt, msgstore.db.crypt5, msgstore.db.crypt7, and msgstore.db.crypt8. In recent versions of WA, the AES algorithm was used with a 256-bit key and the database became msgstore.db.crypt12 [10].
Research studies mostly deal with forensic methodologies on various mobile applications, such as forensic analysis of contact lists, SMS messages, and social media. Some researchers have compared several analysis tools by applying them to the analysis of processes for obtaining WA messages and files on Android platforms. Other researchers determined different artifacts on Android platforms generated by WA such as contacts database, messages database, and the database encryption key (Shidek, Cahyani, and Wardana, 2020). Another study focused on the decryption of WA encrypted databases. The researcher used five different tools to achieve the study’s goals; these tools are WA key, db extractor, WA viewer, WA extract, SQLite spy, and Android backup extractor. Some of these tools are written in python code, so a python compiler is also needed in their experiment [12]. A comparison study between two forensic tools for examining iPhone devices was also done [13]. The study showed a comparison between Elcomsoft iOS forensic toolkit and Oxygen 2012 in terms of the ability of these tools to examine nonjailbreak and jailbreak iPhones [13]. This study focused on mobile forensic investigation in WA on iOS and Android platforms using a variety of digital forensic tools.
WA Experiment
To achieve the aim of our case, a forensic examination was conducted on Android and iOS smartphones. An assumed scenario was used to simulate the case to implement the mobile forensic stages, then analyze the evidence extracted from WA, and finally, write a mobile forensic analysis report.
The assumed scenario is that a public sector employee in the Public Services Office seeks to request a bribe from a citizen to complete the processing of the citizen’s documents via WA messages. While bribery is one of the corruption crimes in the public sector, the anticorruption commission is the specialized entity to address this type of crime according to local laws in your country. Furthermore, the mobile device is a digital tool used to facilitate this type of traditional crime [7].

Mobile forensic process
In the seizure stage, a reasonable and specific search warrant from a legal authority such as the Public Prosecution must be issued. The digital evidence must be determined in the search warrant. Seizures are done by law enforcement personnel trained in the digital evidence seizure process or experts in digital investigation accompanied by judicial officials to ensure that digital evidence is protected and preserved. At this stage, the adopted procedures in the seizure process must be adhered to, and the laws related to privacy and the rights of individuals must be observed. Judicial seizure officers work at this stage to secure the crime scene and document it in writing and photography. The seized devices are also documented in the seizure report, where the name of the owner, the make, the model, the serial number, IMEI, and any other information distinguishing the seized device are documented, in addition to photographing the seizures. Work is being done to preserve the seized devices in their original condition. In addition to disconnecting the communication signals from the devices, all wireless networks must be disconnected to prevent any alteration or destruction of the digital evidence.
The data processing and verification of the evidence are then carried out on backup and imaging data on the smartphone using forensic tools. In this study, the FINALMobile forensic tool was used to implement the data imaging process. This process is carried out in the acquisition stage.
In the data acquisition process, a logical acquisition from a seized smartphone was used, where a backup of the data was taken from the internal memory. The backup data image was saved in the storage media to protect it and perform an analysis process later. When this process is completed, the acquisition process information is saved and documented in a report. This information includes investigator information, acquiring time and information, and image information, which includes a file name, file size, and the MD5 hash value for the file.
The investigator used the image taken in the previous stage to perform the analysis process to obtain more evidence related to the crime. Evidence is collected and verified by exploring and reading the conversations stored in the WA database. Before beginning the analysis stage, the investigator checks the integrity of the evidence image by recalculating the image hash value (MD5) and comparing it with a hash value calculated in the acquisition process.
- [1].
According to the complaint from the victim to the Palestinian Anticorruption Commission, the investigation department issued a search warrant from the anticorruption prosecution against the suspect based on the law by decree no. 7 of 2010 on anticorruption and the law by decree no. 10 of 2018 on cybercrime.
- [2].
The judicial officers in the investigation department have requested technical assistance from digital investigation experts to participate in the implementation of the digital evidence seizure process based on the law by decree no. 10 of 2018 on cybercrime.
Seizure Stage
- 1.
The reporting agency: Anticorruption commission/Digital Forensic Department.
- 2.
Case identifier: Investigative Case No: 20/2021. (Assumption); Digital Forensic Case No.: 7/2021. (Assumption)
- 3.
Forensic investigator: Job ID NO.: 00046. Name Shadi Zakarneh.
- 4.
Identity of the submitter: Anticorruption commission/Investigation Department.
- 5.
Date of the evidence receipt: 20/04/2021.
- 6.
Details of the seized devices: All details related to the seized iPhone are described in Table 9-1 and the details for the seized Android device are described in Table 9-2.
The Seized iPhone Device Details
Device category | Smartphone |
|---|---|
The owner | The mobile is owned individually by XYZ |
Make | Apple iPhone 11 |
Model no. | MWM42HB/A |
Serial no. | F4GZW027N73H |
IMEI | 356562105937766 |
MEID | 35656210593776 |
ICCID | 899702812233269067083 |
iOS version | 14.4.2 |
Internal storage | 128 GB |
External storage | No |
SIM carrier | Jawwal |
Passcode | The mobile passcode is: 989429 “Provided by the suspect” |
Front color | Black, See Appendix 1 |
Back color | Yellow, See Appendix 1 |
Power state | Power ON |
Battery charge percentage | 79% |
The Seized Android Device Details
Device category | Smartphone |
|---|---|
The owner | The mobile is owned individually by YYYY |
Make | Samsung |
Model No. | Galaxy J6 SM-J600F |
Serial No. | RF8KA38324A |
IMEI | 356423092355498 |
Android version | Android 10 with Knox version 3.5 |
Internal storage | 32 GB |
External storage | No |
SIM carrier | Jawwal |
Passcode | 12345 provided by the suspect |
Front color | Black |
Back color | Black |
Power state | Power ON |
Battery charge percentage | 95% |
Mobile external case | No Damages, No Scratches |
Device Photographs | See Appendix 4 |
Chain of custody documentation: While the seized device was documented. The device is labeled with the owner’s name, investigative case no., digital forensic case no., and receipt date. Then the device is preserved in a protected area until the next stage of the examination. This information is also recorded in the digital forensic lab record with the name of the digital forensic examiner.
Acquisition Stage
The process of forensic investigation of mobile devices is not very different from that for laptops, but some of the tools that are used in mobile forensics are somewhat different, as most mobile operating systems are closed, so it becomes difficult to understand the file system and the structure of phones. Many open source Android tools used in digital forensics are available for users, both for purchase and for free, to allow you to begin data extraction, backup operations, and so on.
This stage takes place according to the direct access warrant from the anti-corruption prosecution based on article no. 32 (paragraph 4) in the law by decree no. 10 of 2018 on cybercrime. In the data acquisition process from the seized iPhone device, the iTunes backup tool and Belkasoft forensic tool will be used. While the mobile is unlocked, the iTunes backup acquisition will be used. An iPhone USB cable will be used for connecting the mobile device to the forensic workstation. Alsom in the acquisition for the Android seized device, the ADBs backup command-line tools, the Belkasoft forensic tool, the MOBILedit tool, and the FINALMobile forensic tool will be used. A Samsung mini-USB cable will be used for connecting the mobile device to the forensic workstation. Besides, storage media will be used to store the acquired evidence image. The goal of the examination and the data needed for the investigation must be identified beforehand, and the documentation information for this stage includes the following:

Due to the access warrant issued by the public prosecution (based on the law by decree no. 10 of 2018 on article no. 32 paragraph 4), the acquisition stage was conducted. When the device was unlocked, logical acquisition was used.
Tools Used in the Examination Process for iOS
This stage was conducted using different forensic tools: in the beginning, iTunes software for backing up the device, and then other tools were used for evidence acquisition from iTunes backup. Enigma Recovery Software, DB Browser for SQLite, and iBackup Viewer.
iTunes Backup for iOS
- 1.
When iTunes connected to the suspected device and the iPhone information was viewed, the automatic synchronization was disabled, the backup was determined to be on this computer, and the encrypted local backup was disabled to get an unencrypted backup as shown in Figure 9-4.

iTunes backup settings
- 2.In the final process, the backup started and created in the default folder in Windows 10 as follows:
Backup folder path:
(C:UsersExamplePathAppDataRoamingApple ComputerMobileSyncBackup).
The folder name was 00008030-000338D2149A802E. Because the suspected device is a new device, the backup folder name length was 24 ASCII characters.
Backup size: 36.03 GB.
The full backup is the stored name of the archive chosen, which can be redesigned so that the file system is from a complete copy to a new volume, where it can be returned in many cases in case of data loss or other problems. One of the disadvantages of this copy technique is that it is very slow in the copying process and requires a large amount of memory, as its strategy is to repeat and update files all the time, so the other copy will have less and smaller space, but the recovery process may need longer than normal.
iOS Acquisition Using Enigma Recovery Software

Engima Recovery saved scan explore
iOS Acquisition Using DB Browser for SQLite

Browsing data from SQLite (iOS)
/ sdcard/WhatsApp/Databases
/ sdcard/WhatsApp/media
/ sdcard/WhatsApp/Backups

WA database

Extracting database
Open WA database
Comparison of Artifacts of WA Discovered by Different Tools
iOS | Android | |||
|---|---|---|---|---|
Internal storage & no rooting | SDcard & No rooting & WhatCrypt | Internal storage & no rooting | SDcard & No rooting & WhatCrypt | |
Msgstore.db | Found encrypted | Found encrypted | Found encrypted | Found encrypted |
Wa.db | Not found | Not found | Found | Found |
Phone number | Found | Found | Found | Found |
Messages | Found | Found | Found | Found |
Media files | Found | Found | Found | FOUND |
Contact card | Found | Found | Found | Found |
Deleted messages | Not found | Not found | Not found | Not found |
Deleted media | Not found | Not found | Not found | Not found |
iOS Acquisition Using iBackup Viewer Pro

iBackup Viewer exploring data for app store
iOS Acquisition Using Belkasoft Evidence Center
- 1.
In the Belkasoft evidence center, the new case was created, and then the mobile image was chosen to load the iTunes backup folder. The data and applications that need to be searched are selected as the result of reading and acquiring the image is shown in Figure 9-11.

Belkasoft backup reading and acquiring results
Tools Used in the Acquisition Process for Android
Before the logical acquisition, the developer options and USB debugging were enabled.
Android Acquisition Using ADB Command-Line Tools
- 1.
The examiner identified the suspect’s device and reviewed the details with the details recorded during the seizure stage.
- 2.
ADB command-line tool was used to back up the device as shown in Figure 9-12.

ADB command lines to back up Android devices
- 3.
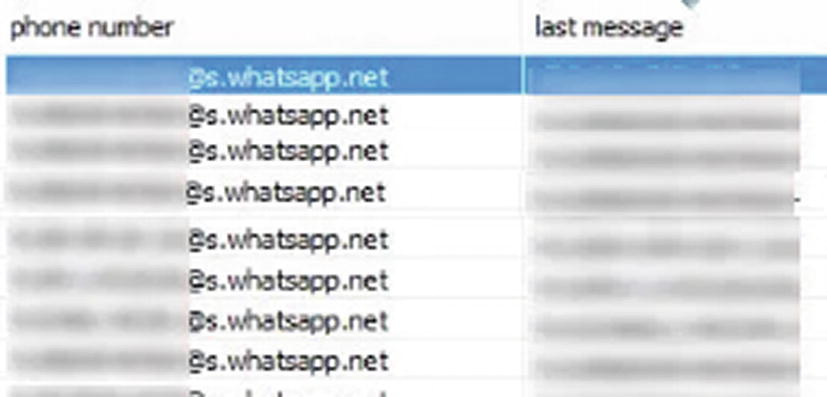
After the backup process is completed, the resulting backup.ab file is converted to a backup.tar file to be used with forensic software tools as shown in Figure 9-13.
Convert backup.ab file to backup.tar file
Android Acquisition Using Belkasoft

Select data source connect with the device
- 3.
Then ADB backup was created; after the backup process was completed, the investigator selected the data type to be analyzed. Now the acquired data is ready for the analysis stage.
Android Acquisition Using FINALMobile Forensic Software
- 1.
The model of the mobile device is selected.
- 2.
The logical acquisition method using Samsung backup protocol is selected as shown in Figure 9-15.

Acquisition method in FINALMobile forensic
- 3.
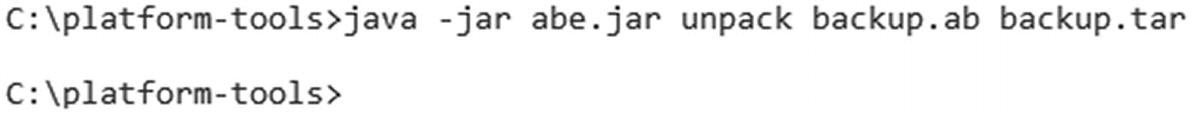
In the preparation for ADB backup, the FINALMobile forensic selects the apps to downgrade due to database encryption in order to decrypt the SQLite database as shown in Figure 9-16.
Selecting apps to downgrade in FINALMobile forensic
- 4.
During the acquisition process, the FINALMobile forensic downgraded WA from version 2.21.12.21 to version 2.11.414 to decrypt the WA SQLite database and back it up as shown in Figure 9-17.

FINALMobile forensic downgraded WA to an older version
- 5.
When the acquisition process is completed, the FINALMobile forensic restores the original WA to the mobile as shown in Figure 9-18.

FINALMobile forensic restoring the original WA version
Android Acquisition Using MOBILedit

Logical acquisition using MOBILedit forensic
WA Analysis Tools for iOS

WA version from Manifest.plist file
iOS Analysis Using Belkasoft

WA folders and database files
Subfolder Descriptions under the WA Folder
Folder Name | Details |
|---|---|
Biz | This includes SQLite database “Biz.sqlite”; this database includes information and business account profiles. |
Librarypreferences | This folder includes a plist file with the name “group.net.whatsapp.WhatsApp.shared.plist”; this file includes information about the WA account such as full user name, user current status, own device ID, and own jabber ID, which is the same as account ID shown in Figure 9-34. |
Mediaprofile | This folder contains images and thumb files for the profile pictures for the friends of this account. |
Messagemedia | This folder contains subfolders with the names of the ID accounts of the friend’s users; under these subfolders the multimedia is exchanged between the user and the friends such as images, videos, and audio messages. |
Stickers | Contains sticker images. |
WAIPC | Includes extensions for notification service and other services. |
- 1.
Emoji.sqlite: contains WA emoji information.
- 2.
Stickers.sqlite: contains WA sticker information.
- 3.
ChateStorage.sqlite: contains tables for information and contents of chats between the user and friends in the table “ZWAMESSAGE” and all information about groups and group members in the tables “ZWAGROUPINFO”, “ZWAGROUPMEMBER”, and “ZWAGROUPMEMBERCHANGE” as shown in Figure 9-22.

ChatStorage.sqlite database contents
- 4.
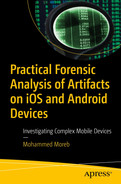
ContactsV2.sqlite: contains information about the friend’s users like the WA account and their status text as shown in Figure 9-23.

ContactsV2.sqlite database contents
- 5.
Callhistory.sqlite: contains the WA call logs as shown in Figure 9-24.

CallHistory.sqlite database contents
Another way to view WA chats is by using the Belkasoft evidence center, in the case explorer and under the instant messengers, and the investigator can browse WA messages from the case explorer.
iOS Analysis Using Magnet AXIOM Examine

Magnet AXIOM Examine & WA chat artifact classification

WA chat log

WA chat groups

WA chat details in the preview pane

WA folder in the file system
As in the Belkasoft evidence center, the investigator can explore the files and folders under the WA folder and show and export the media files that are exchanged between the user and their friends. But for SQLite databases, the investigator needs a third-party tool to explore the contents.
Using Magnet AXIOM Examine, in the artifacts module, the message lists on WA were reviewed, the details of the existing messages were read, and in addition, WA contacts were reviewed in the WA groups list. The exchanged media was also reviewed, including images, files, and audio messages from the messagemedia folder under the WA folder using the examination on a file system. These media can be reviewed when exploring the details of the chat messages.
iOS Analysis Using FINALMobile Forensic

FINALMobile forensic acquisition result
iOS Analysis Using Enigma Recovery Tool

WA chat details in Enigma Recovery tool
Using the Enigma Recovery tool, the message lists on WA were reviewed; the details of the existing messages were read.
iOS Analysis Using iBackup Viewer Tool
WA Analysis Tools for Android
The analysis stage was conducted with the different acquisition methods and using different forensic tools such as Belkasoft evidence center, MOBILedit forensic, and FINALMobile forensic tools. The analysis of the backup file taken by the ADB command-line tool didn’t have any files or data related to WA because the acquired device is unrooted. This was clarified by analyzing the backup file on the Belkasoft evidence center, as well as in the FINALMobile forensic as shown previously.

Forensic investigation using Belkasoft evidence center

WA database files viewed in MOBILedit

Details of a deleted WA message in FINALMobile forensic
Forensic Tools Comparison on iOS Platform
Different tools were used for the acquisition and analysis of iPhone 11 for investigating WA messages. A backup using iTunes was taken and used for the examination and analysis using Belkasoft evidence center, Magnet AXIOM Examine, FINALMobile forensic, Enigma Recovery, and iBackup Viewer. In the acquisition phase, not all of these tools support the acquisition from the connected device directly. The other tool supports the acquisition from the connected device using iTunes backup or logical backup, while the logical backup needs to jailbreak the device to conduct the process. The assumed case in this study is about a cybercrime committed via WA application, and the analysis using these tools focuses on WA data and files. It was clear that there are differences between all of these tools in the examination process and in the way to view and present the evidence from WA.
Examination on a Backup Taken by iTunes
Using the Belkasoft evidence center, the WA databases and files were examined and reviewed by exploring the file system. The database contents include message details, contacts information, groups, and other information opened and reviewed by a built-in SQLite viewer in Belkasoft. The SQLite viewer views the data and structure for the databases as database tables. The other contents of the chats, like media, are viewed from the folders in the file system.
Using Magnet AXIOM Examine, the WA folders, files, and database are reviewed from the file system. In addition, the valuable data for WA is viewed from the artifacts easily and classified for a quick examination. The Magnet AXIOM viewed the contents of the WA database and the contents of the chat messages viewed in a user interface similar to the WA interface. Using a FINALMobile forensic, the tool can’t view the needed data from WA for the investigation. Using Enigma Recovery and WA viewer, the data is viewed as you see in the WA application.
Examination on a Backup Taken from the Connected iPhone Device
The tools used to back up the connected device are Belkasoft evidence center, Magnet AXIOM Examine, FINALMobile forensic tool, and Enigma Recovery. The backup option used is the iTunes Backup because the device needs to be jailbroken for the logical backup to be conducted.
Forensic Tool Comparison on iOS Platform
Belkasoft | Magnet AXIOM | FINALMobile Forensic | Enigma Recovery | iBackup Viewer | |
|---|---|---|---|---|---|
Acquisition from iTunes software backup | Yes | Yes | Yes | Yes | Yes |
Acquisition from the connected device using iTunes option | Yes | Yes | Yes | Yes | No |
Acquisition using logical backup | Yes, but needs to jailbreak the device | Yes, but needs to jailbreak the device | Yes, but needs to jailbreak the device | No | No |
WA data and files | Data and files viewed and the database contents reviewed. The results are the same from iTunes software backup and the connected device backup | Data and files viewed and the database contents were also reviewed | Not successful | Chat messages only reviewed | Chat messages only reviewed |
SQLite database for WA and other apps | Viewing SQLite database data in SQLite Viewer viewing live and deleted data, and flag the deleted rows with deleted column | Viewing SQLite database data in SQLite Viewer viewing live and deleted data, and flag the deleted rows with deleted column | Viewing the data not successful | View all the data including deleted data and flag the deleted with red color and recycle bin icon | View the live data only |
According to the comparison as shown in Table 9-5, and due to the investigation on WA on the iOS platform, the valuable artifacts and evidence can be extracted using Belkasoft evidence center and Magnet AXIOM Examine. This does not mean that these two programs are the best in mobile digital investigation, but regarding the assumed case in this study, the best results were taken from these two programs.
Forensic Tools Comparison on Android Platform
Different tools were used for the acquisition and analysis of Samsung Galaxy J6 with Android 10 and Knox security features for investigating WA messages. The acquisition stage was conducted using ADB command-line tools, and the analysis on the resulting backup file was conducted using Belkasoft evidence center and FINALMobile forensic. Another acquisition process was conducted using forensic tools such as Belkasoft evidence center, MOBILedit, and FINALMobile forensic. The acquired backup using ADB command-line tool was not useful for the assumed case study as the investigation on WA, because during the analysis stage the investigator found there is no data or files related to WA in the backup file due to the inaccessible storage location for WA on the unrooted device.
Forensic Tools Comparison on Android Platform
Belkasoft | MOBILedit | FINALMobile Forensic | |
|---|---|---|---|
Acquisition from ADB command-line backup | Yes | No | Yes |
Acquisition from the connected device ADB backup option | Yes | Yes | Yes |
WA files and folders from ADB command-line tools backup | No WA files or folders viewed | -- | No WA files or folders viewed |
WA files and folders from the forensic software backup | No WA files or folders viewed | WA folder and subfolders, files are viewed | WA folder and subfolders, files are viewed |
SQLite database for WA and other apps | There is a SQLite viewer in Belkasoft, but unencrypted databases only can be viewed. WA database not found in the backup to view it due to the encryption and because WA was not acquired in the backup | WA database files viewed in the system file as encrypted with the extension .db.crypt14. They can be exported but cannot be viewed with any SQLite viewer | While the WA downgraded in the acquisition stage, the WA database was decrypted and viewed using the internal SQLite viewer and can be exported and viewed with any external SQLite DB viewer |
Comparison of Operating Systems
OS Feature | Android OS | iOS | HarmonyOS |
|---|---|---|---|
Type of mobiles and devices support | Touchscreen mobile like Samsung, oneplus, Nokia, etc., TV, watch | iPhones, iPad, iWatch, etc. | Huawei and Honor phones, watches, fitness bands, and other IoT devices |
Architecture | Layered architecture | Layered architecture | Layered architecture |
File system types | FAT32, Ext3, and Ext4, exFAT, or NTFS | APFS and HFS+ | F2FS and Ext4 |
Security | Android uses the concept of user-authentication-gated cryptographic keys, which requires cryptographic key storage and service provider and user authenticators | iOS and iPadOS devices use a file encryption methodology called data protection, whereas the data on an Intel-based Mac is protected with a volume encryption technology called FileVault. | HarmonyOS’s microkernel design; we will see that this network system makes use of formal methods of verification. This allows the users to reshape the security of their primary systems and scale their frameworks from the ground up, over a Trusted Execution Environment (TEE). |
Kernel | A modified version of the Linux kernel | ARM variant of Darwin, derived from BSD, a UNIX-like kernel | Microkernel. |
Summary
WA is the most popular application for IM, where people can exchange text messages, audio files, video files, and documents. This research has focused on forensic investigation of WA on the iOS and Android platforms. The NIST digital forensic method is used in the research. The Belkasoft evidence center, FINALMobile forensic, MOBILedit, Magnet AXIOM, and other tools are used in the examination and analysis stages. The iTunes software was used to back up the seized iPhone and ADB logical backup was used to back up the seized Android mobile. In the analysis stage, the messages, photos, audio files, videos, and contacts are viewed and analyzed to determine the evidence related to the assumed crime. Another tool used for the acquisition and the examination is to show the differences and capabilities between these tools in the examination process and the results of extracting the digital evidence from WA on iOS and Android platforms. While jailbreak is needed for iOS or root for Android to conduct the file system acquisition, not all iOS versions can jailbreak, and not all Android versions can be rooted. Due to the comparison between the forensic tools used on iOS and Android platforms, FINALMobile forensic can downgrade the WA version to an older one with an unencrypted database, so all the data viewed and the deleted chats are recovered. To protect users, the operating system must enable features to prevent downgrading WA to keep and protect user privacy.
References
- [1].
R. Umar, I. Riadi, and G. M. Zamroni, “Mobile Forensic Tools Evaluation for Digital Crime Investigation,” Int. J. Adv. Sci. Eng. Inf. Technol., vol. 8, no. 3, pp. 949–955, 2018.
- [2].
Ubaidillah et al., “Analysis WhatsApp Forensic and Visualization in Android Smartphone with Support Vector Machine (SVM) Method,” J. Phys. Conf. Ser., vol. 1196, no. 1, 2019.
- [3].
J. Clement, “Most Popular Global Mobile Messaging Apps 2020,” Statista, 2020.
- [4].
I. Abdulai Sawaneh, “Examining the Effects and Challenges of Cybercrime and Cyber Security Within the Cyberspace of Sierra Leone,” Int. J. Intell. Inf. Syst., vol. 7, no. 3, p. 23, 2018.
- [5].
FBI’s Internet Crime Complaint Center, “2019 Internet Crime Report,” 2019 Internet Crime Rep., pp. 1–28, 2019.
- [6].
A. Shahbazi, “Technological Developments in Cyberspace and Commission of the Crimes in International Law and Iran,” J. Leg. Ethical Regul. Issues, vol. 22, no. 4, pp. 1–12, 2019.
- [7].
PNA, “Law by Decree No. 10 of 2018 on Cybercrime,” no. 10. pp. 1–15, 2018.
- [8].
S. Udenze and B. Oshionebo, “Investigating ‘WhatsApp’ for Collaborative Learning among Undergraduates,” Etkileşim, vol. 3, no. 5, pp. 24–50, 2020.
- [9].
H. Shidek, N. Cahyani, and A. A. Wardana, “WhatsApp Chat Visualizer: A Visualization of WhatsApp Messenger’s Artifact Using the Timeline Method,” Int. J. Inf. Commun. Technol., vol. 6, no. 1, p. 1, 2020.
- [10].
J. K. Alhassan, B. Abubakar, M. Olalere, M. Abdulhamid, and S. Ahmad, “Forensic Acquisition of Data from a Crypt 12 Encrypted Database of Whatsapp,” 2nd Int. Eng. Conf., October, 2017.
- [11].
R. Gyorödi, D. Zmaranda, V. Georgian, and C. Gyorödi, “A Comparative Study between Applications Developed for Android and iOS,” Int. J. Adv. Comput. Sci. Appl., vol. 8, no. 11, 2017.
- [12].
G. L. Jhala KY, “WhatsApp Forensics: Decryption of Encrypted WhatsApp Databases on Non Rooted Android Devices,” J. Inf. Technol. Softw. Eng., vol. 5, no. 2, pp. 2–5, 2015.
- [13].
T. Höne, K. Kröger, S. Luttenberger, and R. Creutzburg, “iPhone Examination with Modern Forensic Software Tools,” Mob. Multimedia/Image Process. Secur. Appl. 2012, vol. 8406, May, p. 84060R, 2012.
- [14].
PNA, “Anticorruption Law by Decree No. (7) 2010,” PNA, no. 7. pp. 1–9, 2010.