Privacy and Security in Healthcare
Abstract
This chapter discusses the fundamental concepts of security and privacy and their impact on the healthcare industry. It will also review the relationship between privacy and security for healthcare organizations when managing and safeguarding healthcare information. General privacy and security principles in relation to specific healthcare industry standards will also be discussed.
Keywords
Introduction
Security Fundamentals
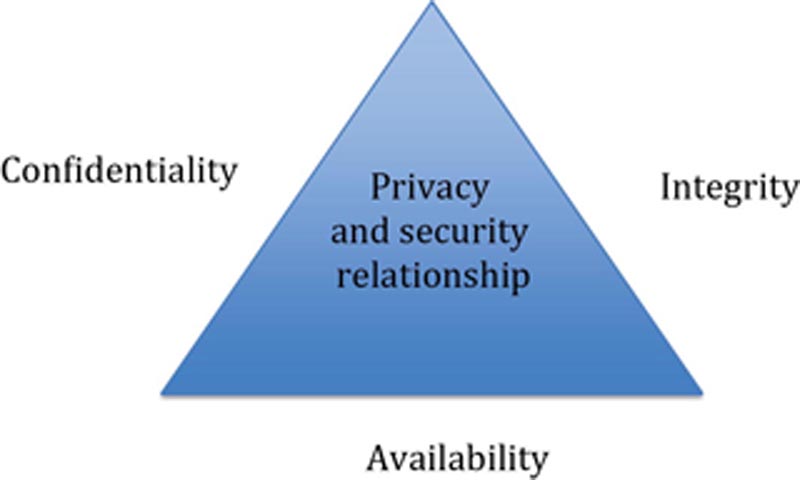
Confidentiality
Integrity
Availability
Security principles
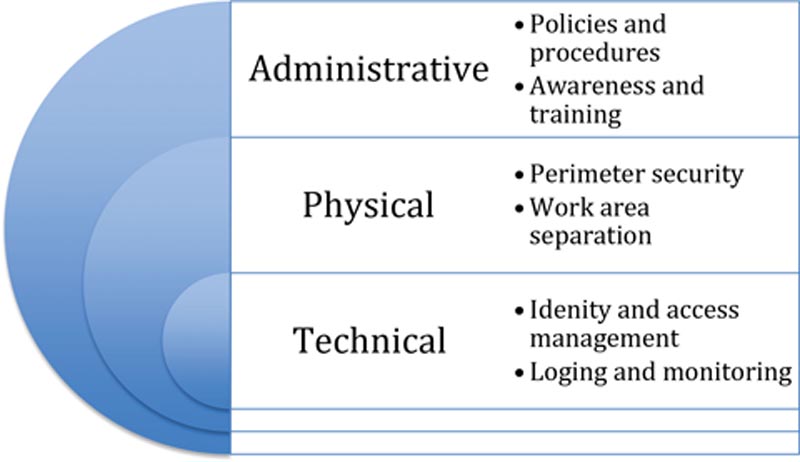
Access Control
Data Encryption
Secret Key Encryption
Public Key Encryption
Hash Functions
Table 4.1
Common Encryption Algorithms
| Encryption Type | Strengths | Weakness | Example |
| Symmetric | • Faster than asymmetric systems
• Difficult to break when large key size is used
| • Requires secure mechanism to deliver keys
• Key management is difficult due to high volume of keys
• Cannot perform nonrepudiation
| • AES
• 3DES
|
| Asymmetric | • Stronger key distribution
• Improved scalability
• Provides integrity, authenticity, and nonrepudiation functions
| • Slower than symmetric systems
• Mathematically intense work factor
| • RSA
• DSA
|
| Hash function | • One-way efficiency
• Provides file/message integrity
| • Does not support confidentiality
| • SHA 1
• MD5
|

Training and Awareness

Logging and Monitoring
| Term | Description | HIPAA Reference |
| Log-in monitoring | Monitoring system log-in and access for discrepancies. The requirement applies to “log-in attempts” including both failed and successful log-ins | 164.308(a)(5)(ii)(C) |
| Audit controls | Cover audit logging and other audit trails on systems that deal with sensitive health information | 164.312(b) |
| Information system activity review | Regularly reviews records of information system activity such as audit logs, access reports, and security incident tracking | 164.308(a)(1)(ii)(D) |
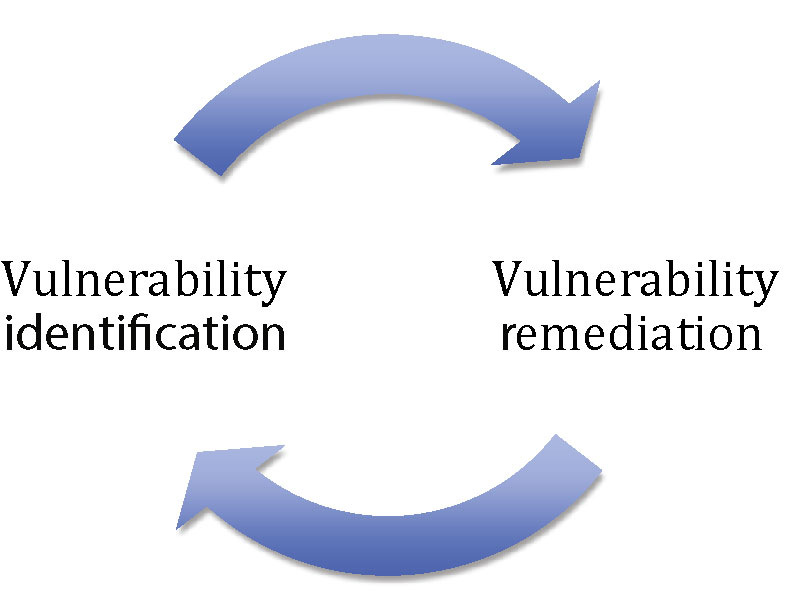
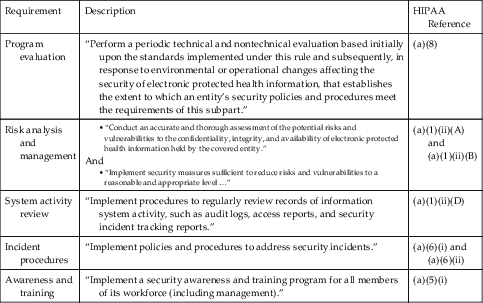
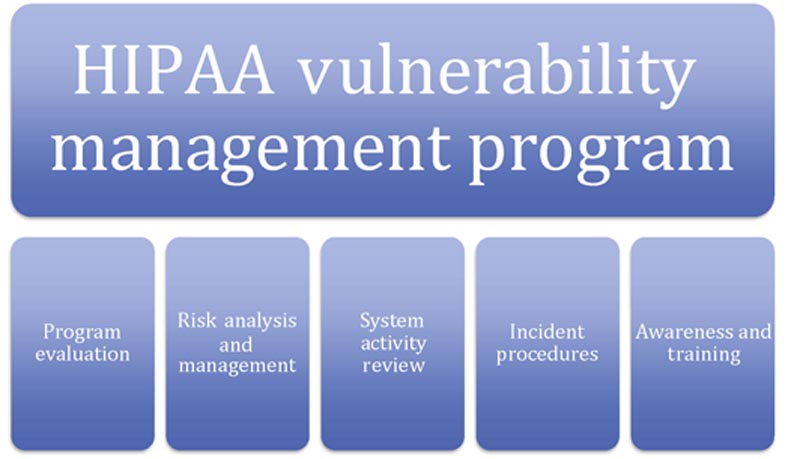
Vulnerability Management
| Requirement | Description | HIPAA Reference |
| Program evaluation | “Perform a periodic technical and nontechnical evaluation based initially upon the standards implemented under this rule and subsequently, in response to environmental or operational changes affecting the security of electronic protected health information, that establishes the extent to which an entity’s security policies and procedures meet the requirements of this subpart.” | (a)(8) |
| Risk analysis and management | • “Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the covered entity.”
And• “Implement security measures sufficient to reduce risks and vulnerabilities to a reasonable and appropriate level …”
| (a)(1)(ii)(A) and (a)(1)(ii)(B) |
| System activity review | “Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.” | (a)(1)(ii)(D) |
| Incident procedures | “Implement policies and procedures to address security incidents.” | (a)(6)(i) and (a)(6)(ii) |
| Awareness and training | “Implement a security awareness and training program for all members of its workforce (including management).” | (a)(5)(i) |
Systems Recovery
Segregation of Duties
Least Privilege
Business Continuity and Disaster Recovery
Data Retention and Destruction
General privacy principles
12 Privacy Principles
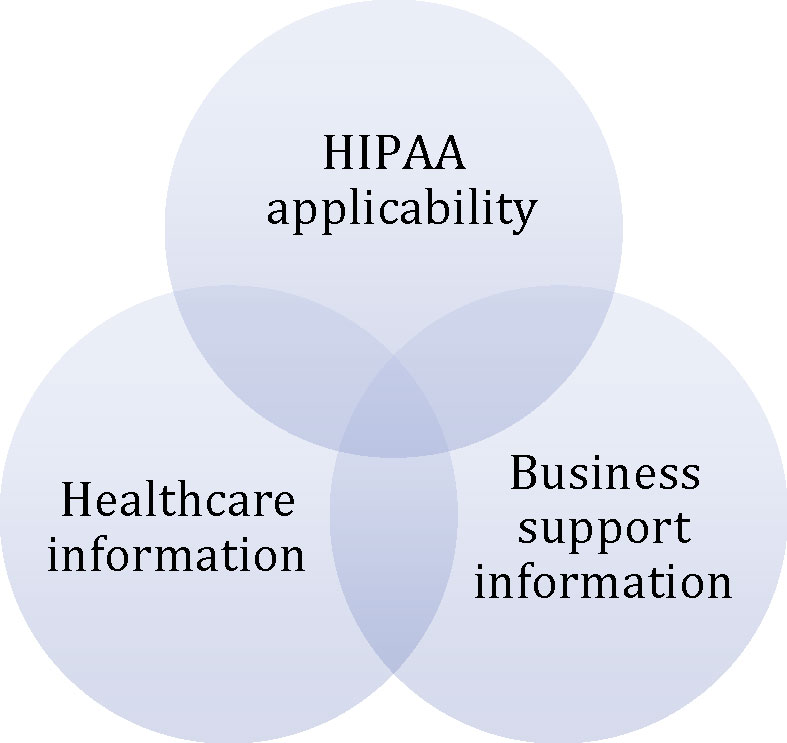
Data Privacy Standards
Organization for Economic Co-Operation and Development Privacy Principles
Generally Accepted Privacy Principles
Personal Information Protection and Electronic Documents Act
UK Data Protection Act 1998
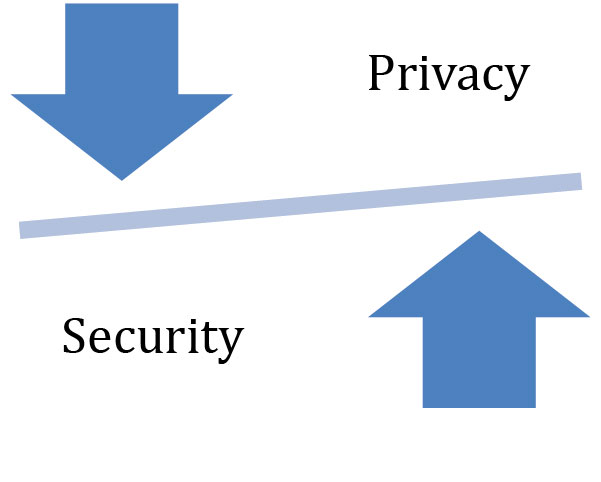
Relationship between privacy and security
The disparate nature of sensitive data and handling implications
Protected Health Information
Data De-Identification
Data Anonymization
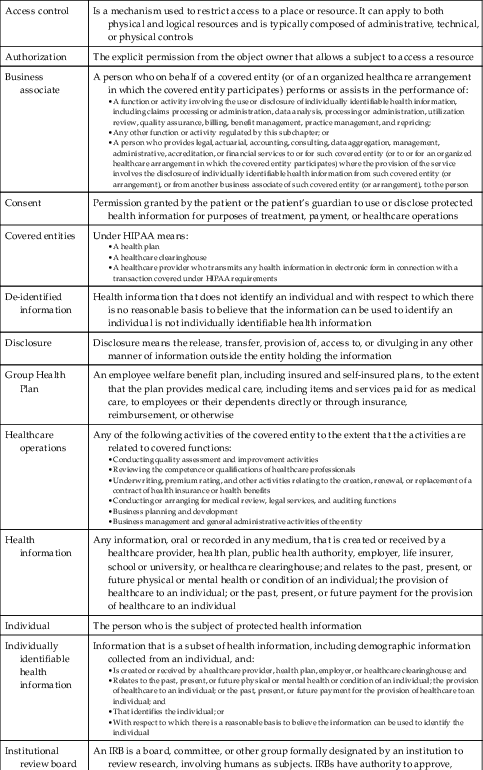
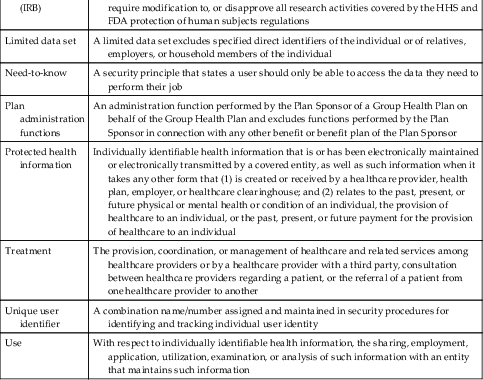
Key terms
| Access control | Is a mechanism used to restrict access to a place or resource. It can apply to both physical and logical resources and is typically composed of administrative, technical, or physical controls |
| Authorization | The explicit permission from the object owner that allows a subject to access a resource |
| Business associate | A person who on behalf of a covered entity (or of an organized healthcare arrangement in which the covered entity participates) performs or assists in the performance of: • A function or activity involving the use or disclosure of individually identifiable health information, including claims processing or administration, data analysis, processing or administration, utilization review, quality assurance, billing, benefit management, practice management, and repricing;
• Any other function or activity regulated by this subchapter; or
• A person who provides legal, actuarial, accounting, consulting, data aggregation, management, administrative, accreditation, or financial services to or for such covered entity (or to or for an organized healthcare arrangement in which the covered entity participates) where the provision of the service involves the disclosure of individually identifiable health information from such covered entity (or arrangement), or from another business associate of such covered entity (or arrangement), to the person
|
| Consent | Permission granted by the patient or the patient’s guardian to use or disclose protected health information for purposes of treatment, payment, or healthcare operations |
| Covered entities | Under HIPAA means: • A health plan
• A healthcare clearinghouse
• A healthcare provider who transmits any health information in electronic form in connection with a transaction covered under HIPAA requirements
|
| De-identified information | Health information that does not identify an individual and with respect to which there is no reasonable basis to believe that the information can be used to identify an individual is not individually identifiable health information |
| Disclosure | Disclosure means the release, transfer, provision of, access to, or divulging in any other manner of information outside the entity holding the information |
| Group Health Plan | An employee welfare benefit plan, including insured and self-insured plans, to the extent that the plan provides medical care, including items and services paid for as medical care, to employees or their dependents directly or through insurance, reimbursement, or otherwise |
| Healthcare operations | Any of the following activities of the covered entity to the extent that the activities are related to covered functions: • Conducting quality assessment and improvement activities
• Reviewing the competence or qualifications of healthcare professionals
• Underwriting, premium rating, and other activities relating to the creation, renewal, or replacement of a contract of health insurance or health benefits
• Conducting or arranging for medical review, legal services, and auditing functions
• Business planning and development
• Business management and general administrative activities of the entity
|
| Health information | Any information, oral or recorded in any medium, that is created or received by a healthcare provider, health plan, public health authority, employer, life insurer, school or university, or healthcare clearinghouse; and relates to the past, present, or future physical or mental health or condition of an individual; the provision of healthcare to an individual; or the past, present, or future payment for the provision of healthcare to an individual |
| Individual | The person who is the subject of protected health information |
| Individually identifiable health information | Information that is a subset of health information, including demographic information collected from an individual, and: • Is created or received by a healthcare provider, health plan, employer, or healthcare clearinghouse; and
• Relates to the past, present, or future physical or mental health or condition of an individual; the provision of healthcare to an individual; or the past, present, or future payment for the provision of healthcare to an individual; and
• That identifies the individual; or
• With respect to which there is a reasonable basis to believe the information can be used to identify the individual
|
| Institutional review board (IRB) | An IRB is a board, committee, or other group formally designated by an institution to review research, involving humans as subjects. IRBs have authority to approve, require modification to, or disapprove all research activities covered by the HHS and FDA protection of human subjects regulations |
| Limited data set | A limited data set excludes specified direct identifiers of the individual or of relatives, employers, or household members of the individual |
| Need-to-know | A security principle that states a user should only be able to access the data they need to perform their job |
| Plan administration functions | An administration function performed by the Plan Sponsor of a Group Health Plan on behalf of the Group Health Plan and excludes functions performed by the Plan Sponsor in connection with any other benefit or benefit plan of the Plan Sponsor |
| Protected health information | Individually identifiable health information that is or has been electronically maintained or electronically transmitted by a covered entity, as well as such information when it takes any other form that (1) is created or received by a healthcare provider, health plan, employer, or healthcare clearinghouse; and (2) relates to the past, present, or future physical or mental health or condition of an individual, the provision of healthcare to an individual, or the past, present, or future payment for the provision of healthcare to an individual |
| Treatment | The provision, coordination, or management of healthcare and related services among healthcare providers or by a healthcare provider with a third party, consultation between healthcare providers regarding a patient, or the referral of a patient from one healthcare provider to another |
| Unique user identifier | A combination name/number assigned and maintained in security procedures for identifying and tracking individual user identity |
| Use | With respect to individually identifiable health information, the sharing, employment, application, utilization, examination, or analysis of such information with an entity that maintains such information |
Practice Exam
1. Which element of CIA security model is least important?
a. Availability – Data security is the primary concern; as long as the data are secure, availability does not matter.
b. Confidentiality – HIPAA already ensures patient healthcare information, so we do not have to worry about confidentiality in the CIA security model.
c. Availability – Strong access controls already ensure information is only available to authorized healthcare employees.
d. None – All elements of the CIA security model are equally important.
2. Confidentiality is best accomplished by which of the following?
a. Encryption
b. Data backup systems
c. Logical system controls that enforce data validation
d. Vulnerability management
3. The three broad types of access control are:
a. Confidentiality, integrity, availability
b. Confidential, sensitive, public
c. Administrative, physical, technical
d. Discretionary, mandatory, role-based
4. Sensitive data should be encrypted:
a. At rest
b. In transit
c. Only when leaving the organization’s network
d. Both a and b
5. Security awareness training:
a. Only needs to be given to new employees
b. Does not need to be given since healthcare employees receive this training when they receive their healthcare training and certification
c. Should be given to all employees on an annual basis
d. Only needs to be given to employees who handle PHI
6. Audit logging:
a. Only needs to be performed 1 month prior to an audit
b. Should be performed in conjunction with monitoring
c. Does not need to be performed by covered entities (only healthcare organizations)
d. Does not need to be performed by healthcare organizations (only covered entities)
7. Vulnerability management includes:
a. Identification and remediation
b. A continuous process
c. Remediation only
d. Both a and b
8. Segregation of duties:
a. Does not apply to covered entities
b. Is not required when encryption is being used
c. Is designed to reduce the risk of system abuse
d. Only applies to larger organizations since having more employees increases the risk for system abuse
9. Business continuity:
a. Only applies to covered entities since they are businesses that support healthcare organizations rather than deliver patient healthcare services
b. Is composed of many technologies and processes that support the availability leg of the CIA triangle
c. Is optional for covered entities since they do not provide direct patient care
d. None of the above
10. Data destruction includes:
a. Shredding
b. Degaussing
c. None of the above
d. Both a and b
11. OECD focuses their mission on serving:
a. The United States
b. People around the world
c. The United Kingdom
d. North America
12. GAPP applies to:
a. Federal organizations in the United States and Canada
b. The United States and Canada
c. The United States only
d. Canada only
13. PIPEDA stands for:
a. Personal Information Protection and Electronic Documents Act
b. Privacy Information Protection and Electronic Document Act
c. Personal Information Protection and Electronic Data Act
d. Privacy Information Protection and Electronic Data Act
14. The UK DPA:
a. Involves the Information Commissioner’s Office
b. Has restrictions on data transfer outside of the European Economic Area
c. Contains eight specific data protection principles
d. All of the above
15. Consent/Choice is:
a. Not important in healthcare setting since healthcare organizations need to have PHI to perform service requested by the patient
b. Should be discussed with the patient prior to delivering any services
c. Is only relevant for healthcare-related research, not traditional patient care services
d. Only applies to US entities following GAAP
16. The accuracy privacy principle:
a. Requires organizations to maintain complete and reliable PHI
b. Is applicable to GAAP
c. Is applicable to PIPEDA
d. All of the above
17. Breach notification requirements:
a. Are only important for transborder data flows
b. Do not apply if the PHI was for testing and research purposes
c. Both a and b
d. None of the above
18. The relationship between privacy and security:
a. Is symbiotic and both are relevant to safeguarding PHI
b. Is not relevant since privacy and security are two separate and distinct disciplines
c. Is not relevant since privacy is more important than security
d. Is not relevant since security is more important than privacy
19. Under the HIPAA Privacy Rule, there are:
a. 18 possible identifiers of PHI
b. 81 possible identifiers of PHI
c. 8 possible identifies of PHI
d. No specific number as it depends on the organization’s use of PHI
20. De-identification and anonymization are:
a. Synonymous
b. Two methods for preventing disclosure of PHI
c. Both a and b
d. None of the above
Practice Exam Answers
1. d
2. a
3. c
4. d
5. c
6. b
7. d
8. c
9. b
10. d
11. b
12. b
13. a
14. d
15. b
16. d
17. d
18. a
19. a
20. b
