Third-Party Risk Management
Abstract
This chapter discusses the importance and purpose of managing risk associated with third parties. This includes understanding the definition of third parties, risk assessment and management activities, and requirements for maintaining a third-party inventory, applying security standards and practices, determining assessment requirements, and addressing incident response and connectivity requirements.
Keywords
Introduction
Knowledge Areas
Definition of third parties
Inventory
Management standards and practices
Risk assessment
Assessment and audit support
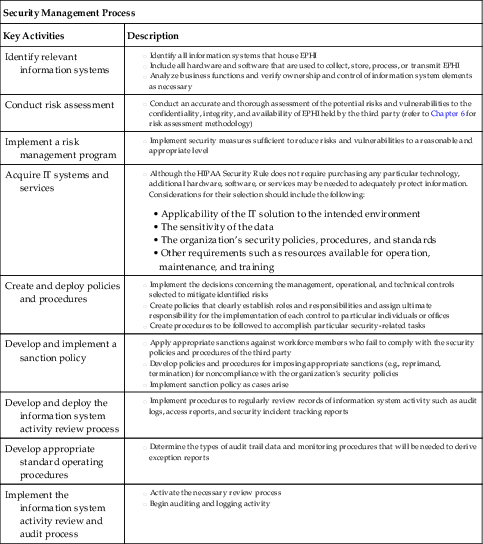
| Security Management Process | |
| Key Activities | Description |
| Identify relevant information systems | |
| Conduct risk assessment | |
| Implement a risk management program | |
| Acquire IT systems and services | • Applicability of the IT solution to the intended environment
• The sensitivity of the data
• The organization’s security policies, procedures, and standards
• Other requirements such as resources available for operation, maintenance, and training
|
| Create and deploy policies and procedures | |
| Develop and implement a sanction policy | |
| Develop and deploy the information system activity review process | |
| Develop appropriate standard operating procedures | |
| Implement the information system activity review and audit process | |
| Assigned Security Responsibilities | |
| Key Activities | Description |
| Select a security official to be assigned responsibility for HIPAA security | |
| Assign and document the individual’s responsibility | |

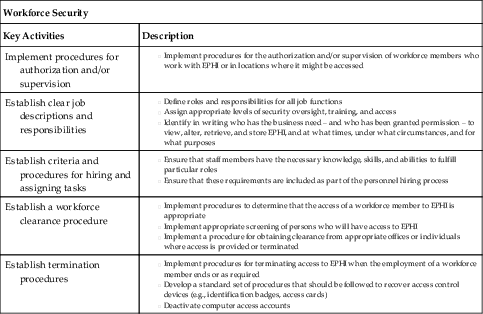
| Workforce Security | |
| Key Activities | Description |
| Implement procedures for authorization and/or supervision | |
| Establish clear job descriptions and responsibilities | |
| Establish criteria and procedures for hiring and assigning tasks | |
| Establish a workforce clearance procedure | |
| Establish termination procedures | |
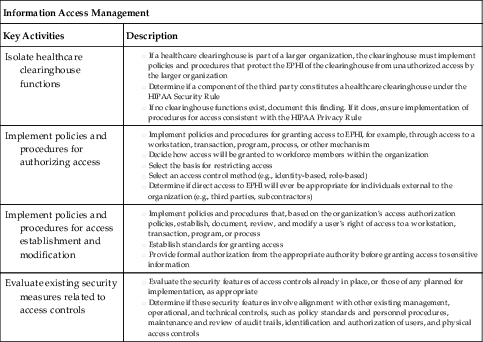
| Information Access Management | |
| Key Activities | Description |
| Isolate healthcare clearinghouse functions | |
| Implement policies and procedures for authorizing access | |
| Implement policies and procedures for access establishment and modification | |
| Evaluate existing security measures related to access controls | |
Communication of Findings
Incident notification and response
Internal Processes for Incident Response
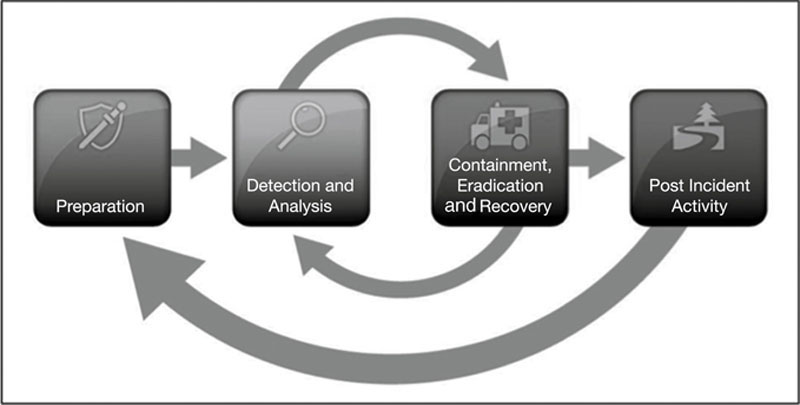
Incident Response Relationship Between Covered Entity and Third Party
Breach Identification, Notification, and Initial Response
Establishing connectivity
Trust
Safeguards
Connection Agreements
Promoting awareness of requirements
Information Flow Mapping and Scope
Data Sensitivity and Classification
Privacy Requirements
Security Requirements
Risks Associated With Third Parties
Risk remediation
Key terms
| Term | Definition |
| Chain of custody | Documenting the preservation of evidence from the time it is collected to the time it is presented in court |
| Covered entity | The primary entity such as a health plan, healthcare clearinghouse, and certain healthcare providers who maintains a direct relationship with patients |
| Third party | Also referred to as business associates, a person or entity that performs certain functions or activities that involve the use or disclosure of protected health information on behalf of, or provides services to, a covered entity. Third parties can also be subcontractors that create, receive, maintain, or transmit protected health information on behalf of another business associate |
| Incident response | Process to help organizations minimize loss or theft of information, disruption of services, and reduce overall risk associated with incidents |
| Level of trust | Assessed based on the results of the covered entity’s risk assessment, identified deficiencies, and status of remediation plans |
| Connection agreement | Used to define and mutually agree on the type of connectivity that will be established between the parties |
| HIPAA Privacy Rule | Requires appropriate safeguards to protect the privacy of personal health information, and sets limits and conditions on the uses and disclosures that may be made of such information without patient authorization |
| HIPAA Security Rule | Establishes national standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity |
Practice Exam
1. The HIPAA Privacy Rule applies only to covered (primary) entities including:
a. Health plans
b. Healthcare clearinghouses
c. Certain healthcare providers
d. All of the above
2. Under HIPAA, written contracts must be implemented to address:
a. Termination
b. Breach reimbursement
c. Event notification
d. a and c
3. Risk assessments are generally triggered when a third party will:
a. Store, process, and/or transmit personal health information
b. Store and/or process personal health information
c. Transmit and/or process personal health information
d. Transmit and/or store personal health information
4. Which NIST Special Publication describes the key administrative, physical, and technical controls and activities required under the HIPAA Security Rule?
a. 800-61 Revision 2
b. 800-39
c. 800-66 Revision 1
d. 800-30 Revision 1
5. Findings resulting from completed third-party assessments should be clearly communicated to:
a. Management at the covered entity
b. Management at the third party
c. a and b
d. None of the above
6. Incident response helps organizations to:
a. Reduce overall risk associated with incidents
b. Minimize disruption of services
c. Minimize loss or theft of information
d. All of the above
7. Which NIST Special Publication focuses on computer security incident response handling?
a. 800-61 Revision 2
b. 800-39
c. 800-66 Revision 1
d. 800-30 Revision 1
8. Under the HIPAA Breach Notification Rule, notification is generally required to the affected individuals, the Secretary, and in certain circumstances, the media within:
a. 30 days
b. 45 days
c. 60 days
d. 90 days
9. A covered entity’s level of trust for a third party can be assessed based on the results of:
a. Identified deficiencies
b. The covered entity’s risk assessment
c. Status of remediation plans
d. All of the above
10. Connection agreements with third parties can be used to:
a. Address administrative, physical, and technical safeguard requirements
b. Define and mutually agree on the type of connectivity established between parties
c. a and b
d. None of the above
11. To determine the value and risk associated with data, an organization must assess data:
a. Confidentiality requirements
b. Integrity requirements
c. Availability requirements
d. All of the above
12. The HIPAA Privacy Rule establishes:
a. National standards to protect individuals’ medical records and other personal health information and applies to health plans, healthcare clearinghouses, and those healthcare providers that conduct certain healthcare transactions electronically
b. National standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity
c. International standards to protect individuals’ medical records and other personal health information and applies to health plans, healthcare clearinghouses, and those healthcare providers that conduct certain healthcare transactions electronically
d. International standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity
13. The HIPAA Security Rule establishes:
a. National standards to protect individuals’ medical records and other personal health information and applies to health plans, healthcare clearinghouses, and those healthcare providers that conduct certain healthcare transactions electronically
b. National standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity
c. International standards to protect individuals’ medical records and other personal health information and applies to health plans, healthcare clearinghouses, and those healthcare providers that conduct certain healthcare transactions electronically
d. International standards to protect individuals’ electronic personal health information that is created, received, used, or maintained by a covered entity
14. Who is ultimately responsible for the protection of data entrusted to a healthcare organization?
a. Patient
b. Third party accessing, processing, or storing healthcare data
c. Primary healthcare organization
d. Department of Health and Human Services (HHS)
Practice Exam Answers
1. d
2. d
3. a
4. c
5. c
6. d
7. a
8. c
9. d
10. c
11. d
12. a
13. b
14. c
