Information Risk Assessment
Abstract
This chapter discusses the importance and purpose of conducting information risk assessments. This includes identifying assessment control procedures, the process for conducting a risk assessment, and the process to respond and remediate risk.
Keywords
Introduction
Knowledge Areas
Understanding risk assessment
Key Terms
Life Cycle and Continuous Monitoring
Tools, Resources, and Techniques
NIST Guide for Conducting Risk Assessments
ISO/IEC 27005:2011
Desired Outcomes
Role of Internal and External Audit
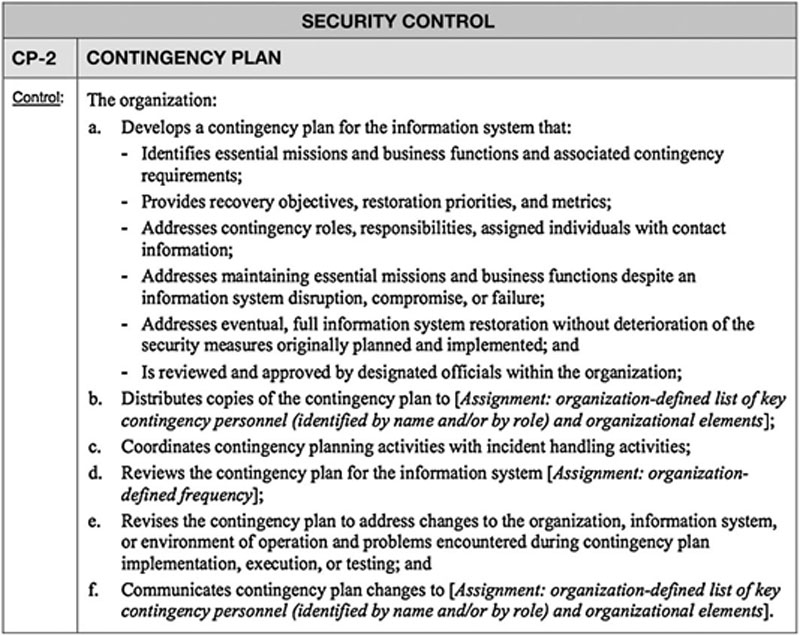
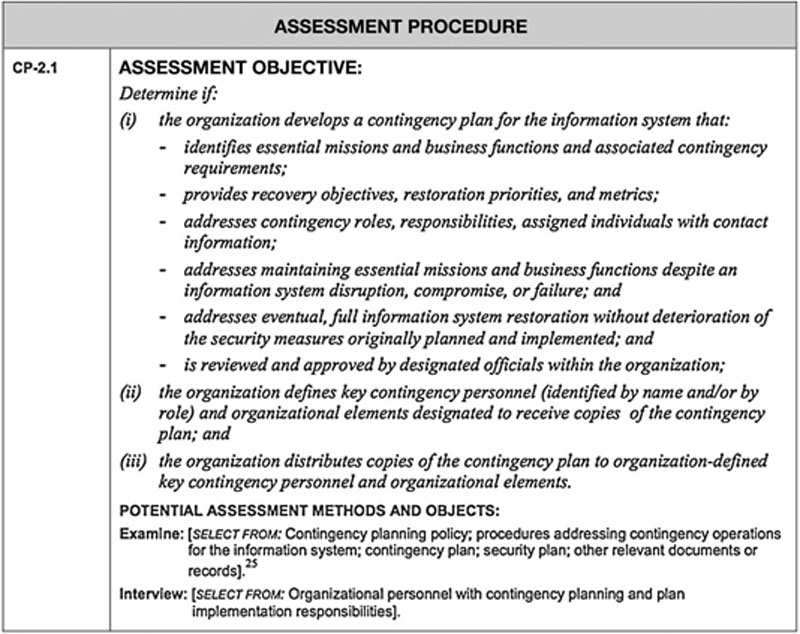
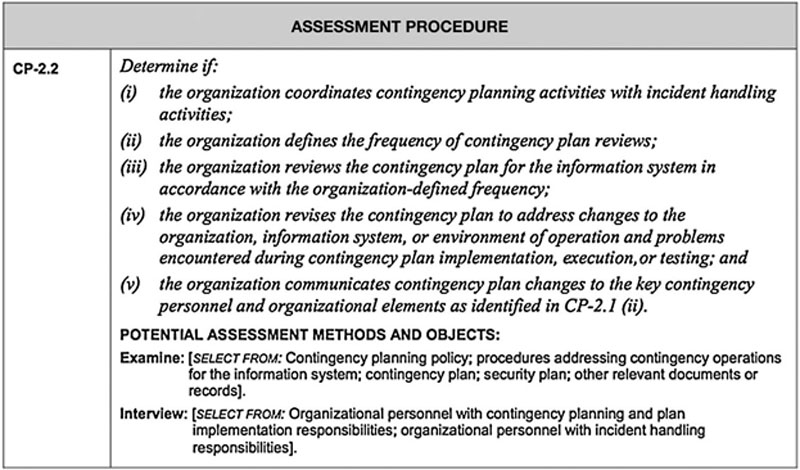
Assessment procedures
Assessment Objective
Assessment Object
Assessment Methods
NIST Example
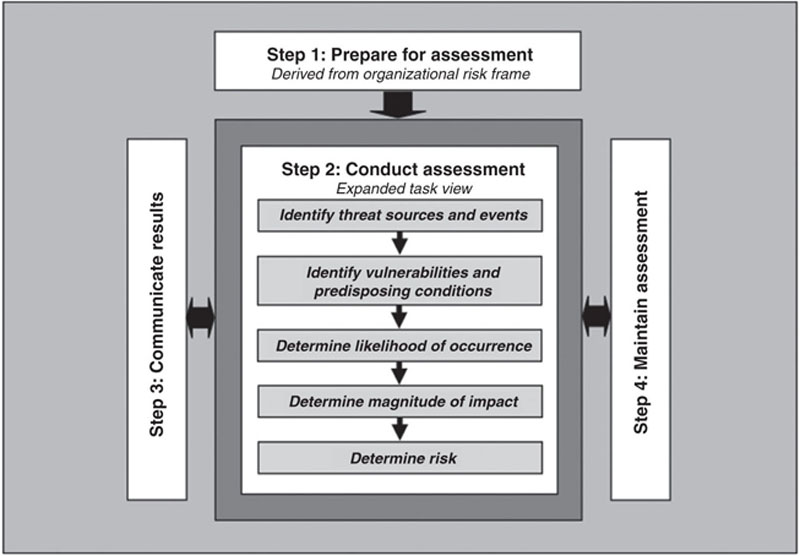
Risk assessment process
Risk Assessment Hierarchy
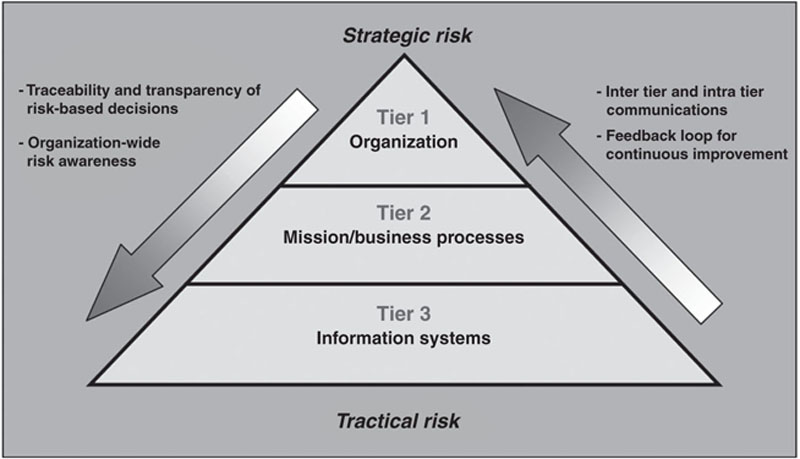
Tier 1: Organizational Level
Tier 2: Mission/Business Process
Tier 3: Information System
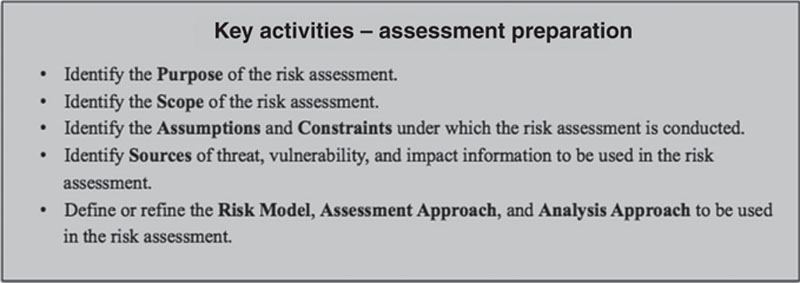
Step 1: Prepare
Task 1-1: Identify Purpose
Task 1-2: Identify Scope
Organizational Applicability
Effectiveness Time Frame
Architectural/Technology Considerations
Task 1-3: Identify Assumptions and Constraints
Threat Sources
Threat Events
Vulnerabilities and Predisposing Conditions
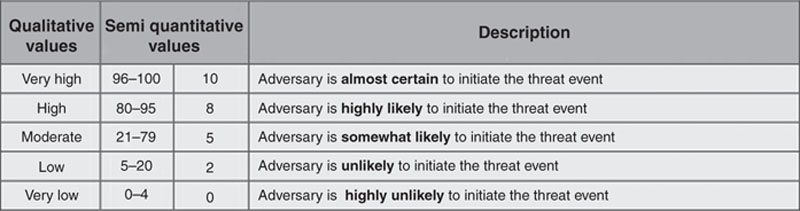
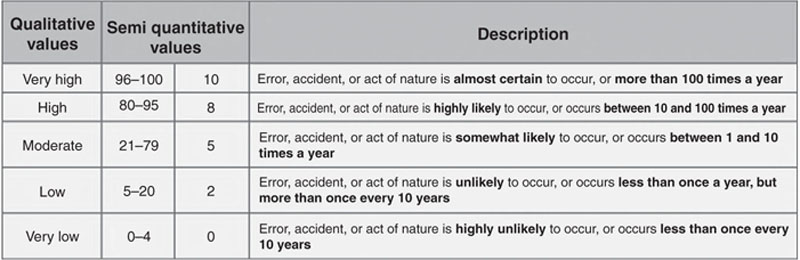
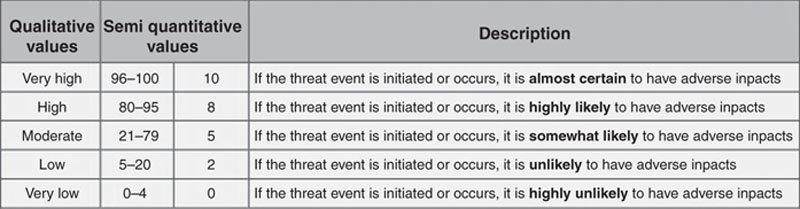
Likelihood
Impacts
Risk Tolerance and Uncertainty
Analytic Approach
Task 1-4: Identify Information Sources
Task 1-5: Identify Risk Model and Analytic Approach
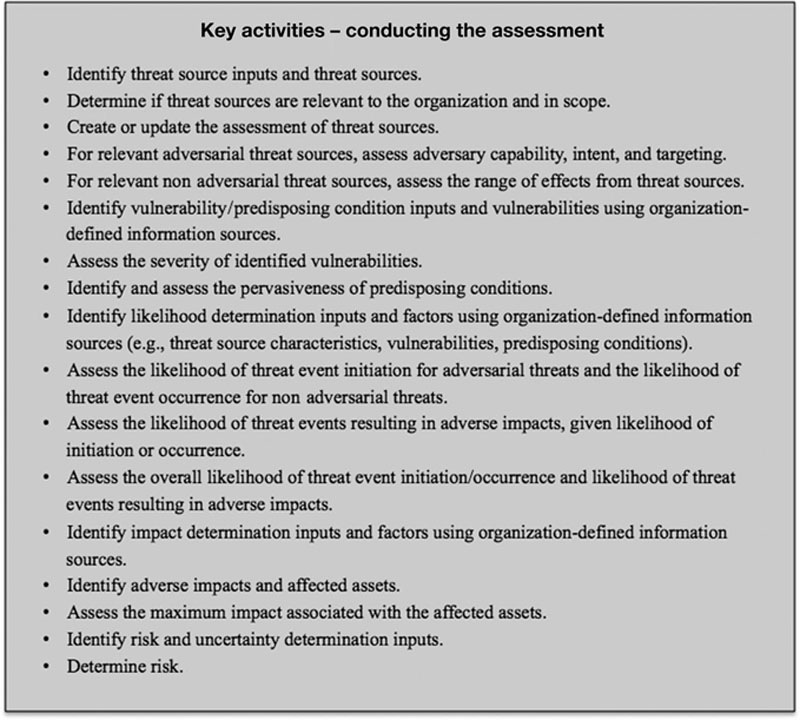
Step 2: Conduct the Assessment
Task 2-1: Identify Threat Sources
Task 2-2: Identify Threat Events
Task 2-3: Identify Vulnerabilities and Conditions
Task 2-4: Determine Likelihood
Task 2-5: Determine Impact
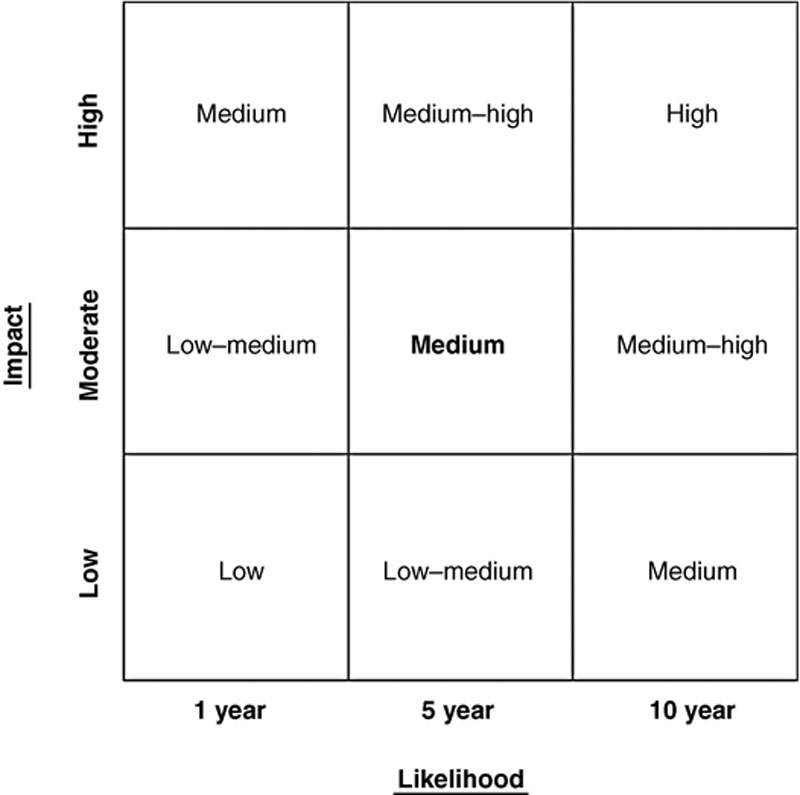
Task 2-6: Determine Risk
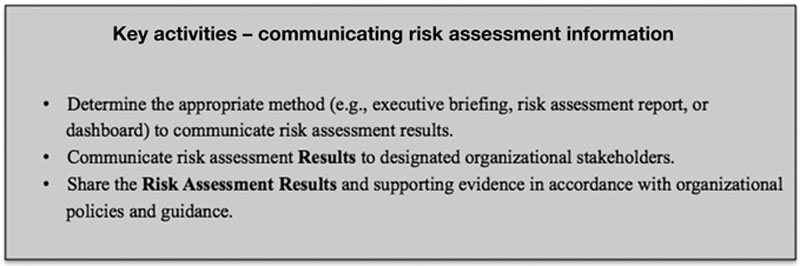
Step 3: Communicating Risk Assessment Information
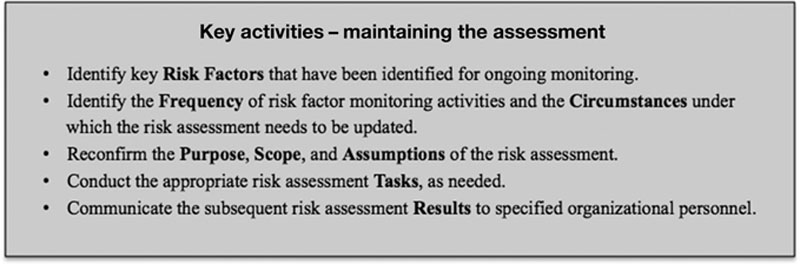
Step 4: Maintaining the Assessment
Task 4-1: Monitor Risk Factors
Task 4-2: Update Risk Assessment
Risk response and remediation
Risk Response Identification
Evaluation of Alternatives
Risk Response Decision
Risk Response Implementation
Types of Controls
Controls Related to Time
Preventative
Detective
Corrective
Key terms
| Term | Definition |
| Assessment procedure | Consists of a set of assessment objectives, each with an associated set of potential assessment methods and assessment objects |
| Assessment objective | Includes a set of determination statements related to the security control under assessment |
| Assessment objects | Identify the specific items being assessed and include specifications, mechanisms, activities, and individuals |
| Assessment methods | Define the nature of the assessor actions and include examine, interview, and test |
| Examine method | The process of reviewing, inspecting, observing, studying, or analyzing one or more assessment objects (i.e., specifications, mechanisms, or activities) |
| Interview method | The process of holding discussions with individuals or groups of individuals within an organization to, once again, facilitate assessor understanding, achieve clarification, or obtain evidence |
| Test method | The process of exercising one or more assessment objects (i.e., activities or mechanisms) under specified conditions to compare actual with expected behavior |
| Preventative controls | Designed to be implemented prior to a threat event and reduce and/or avoid the likelihood and potential impact of a successful threat event |
| Detective controls | Designed to detect a threat event while it is occurring |
| Corrective controls | Designed to mitigate or limit the potential impact of a threat event once it has occurred and recover to normal operations |
Practice Exam
1. Risk assessments are not:
a. One-time activities with the hope of providing long-term and definitive information
b. Performed periodically throughout the information life cycle
c. Designed to protect the confidentiality, integrity, and availability of information
d. Designed to guide and inform decision makers in their response to risks
2. NIST’s Special Publication 800-30:
a. Provides guidance for assessing the security controls in federal information systems and organizations and building effective security assessment plans
b. Provides guidance for conducting risk assessments of healthcare information systems and organizations
c. Provides guidance for interconnecting information technology systems
d. Provides guidance for conducting risk assessments of federal information systems and organizations
3. The intent of a risk assessment is to inform decision makers and support risk responses by identifying all of the following except:
a. Relevant threats to an organization
b. Internal and external vulnerabilities
c. Potential impact resulting from a vulnerability exploiting a threat
d. Likelihood that impact will occur or be realized
4. An assessment procedure consists of:
a. A set of assessment objectives
b. An associated set of potential assessment methods
c. An associated set of assessment objects
d. All of the above
5. Assessment methods define the nature of the assessor actions and include all of the following methods except:
a. Interview
b. Evaluate
c. Examine
d. Test
6. The four steps to assessing information security risk include all of the following except:
a. Prepare for the assessment.
b. Conduct the assessment.
c. Remediate assessment findings.
d. Maintain the assessment.
7. Which of the following is correct?
a. The Tier 1 context and the system development life cycle determine the purpose and define the scope of risk assessment activities at Tier 2.
b. At Tier 1, risk assessments support organizational strategies, policies, guidance, and processes for managing risk.
c. At Tier 3, risk assessments support the determination of mission/business process protection and resiliency requirements, and the allocation of those requirements to the enterprise architecture as part of mission/business segments (that support mission/business processes).
d. At Tier 3, risk assessments support organizational strategies, policies, guidance, and processes for managing risk.
8. Risk assessments include:
a. Assessment approaches (i.e., quantitative, qualitative)
b. Analysis approaches (i.e., threat-oriented, asset/impact-oriented, vulnerability-oriented)
c. All of the above
d. None of the above
9. Step 2 of the risk assessment process includes all of the following except:
a. Identifying threat sources relevant to the organization
b. Identifying risk model and analytic approach
c. Identifying vulnerabilities that could be exploited by threat sources through specific threat events
d. Determining adverse impacts resulting from vulnerability exploitation
10. Step 1 of the risk assessment process includes all of the following except:
a. Identifying threat sources relevant to the organization
b. Identifying purpose
c. Identifying risk model and analytic approach
d. Identifying scope
11. Risk monitoring provides organizations with the means to, on an ongoing basis:
a. Identify risk-impacting changes to organizational information systems and the environments in which those systems operate
b. Verify compliance
c. Determine the effectiveness of risk responses
d. All of the above
12. Three types of controls (or safeguards) include all of the following except:
a. Physical
b. Tactical
c. Administrative
d. Technical
13. Controls related to time generally fall into which of the following categories?
a. Corrective
b. Detective
c. Preventative
d. All of the above
14. The examine method of assessment is:
a. The process of exercising one or more assessment objects (i.e., activities or mechanisms) under specified conditions to compare actual with expected behavior
b. The process of reviewing, inspecting, observing, studying, or analyzing one or more assessment objects (i.e., specifications, mechanisms, or activities)
c. The process of holding discussions with individuals or groups of individuals within an organization to, once again, facilitate assessor understanding, achieve clarification, or obtain evidence
d. a and b
15. The interview method of assessment is:
a. The process of reviewing, inspecting, observing, studying, or analyzing one or more assessment objects (i.e., specifications, mechanisms, or activities)
b. The process of holding discussions with individuals or groups of individuals within an organization to, once again, facilitate assessor understanding, achieve clarification, or obtain evidence
c. The process of exercising one or more assessment objects (i.e., activities or mechanisms) under specified conditions to compare actual with expected behavior
d. None of the above
16. The test method of assessment is:
a. The process of holding discussions with individuals or groups of individuals within an organization to, once again, facilitate assessor understanding, achieve clarification, or obtain evidence
b. The process of reviewing, inspecting, observing, studying, or analyzing one or more assessment objects (i.e., specifications, mechanisms, or activities)
c. The process of exercising one or more assessment objects (i.e., activities or mechanisms) under specified conditions to compare actual with expected behavior
d. a, b, and c
Practice Exam Answers
1. a
2. d
3. c
4. d
5. b
6. c
7. a
8. c
9. b
10. a
11. d
12. b
13. d
14. d
15. b
16. c
