Information Governance and Risk Management
Abstract
This chapter discusses the foundational principles required to implement and maintain an effective information governance and risk management program. This includes understanding how healthcare organizations manage risk through adoption of security and privacy programs, risk management methodologies, information risk management life cycle frameworks, and other risk management activities.
Keywords
Introduction
Knowledge Areas
Industry Resources
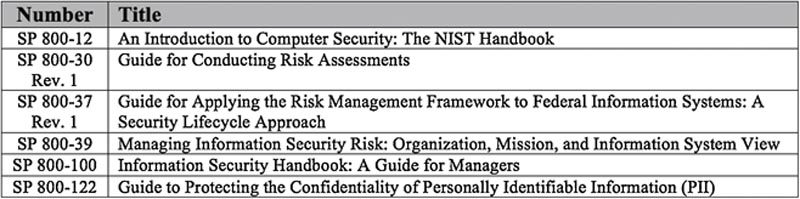
National Institute of Standards and Technology
International Organization for Standardization
ISO/IEC 27002:2005
ISO 27799:2008
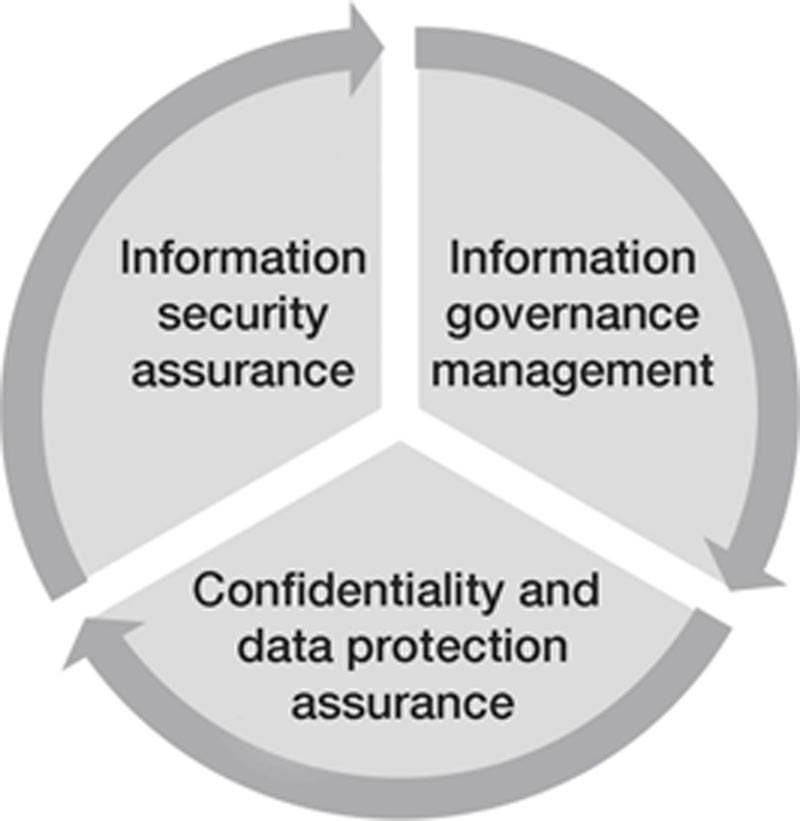
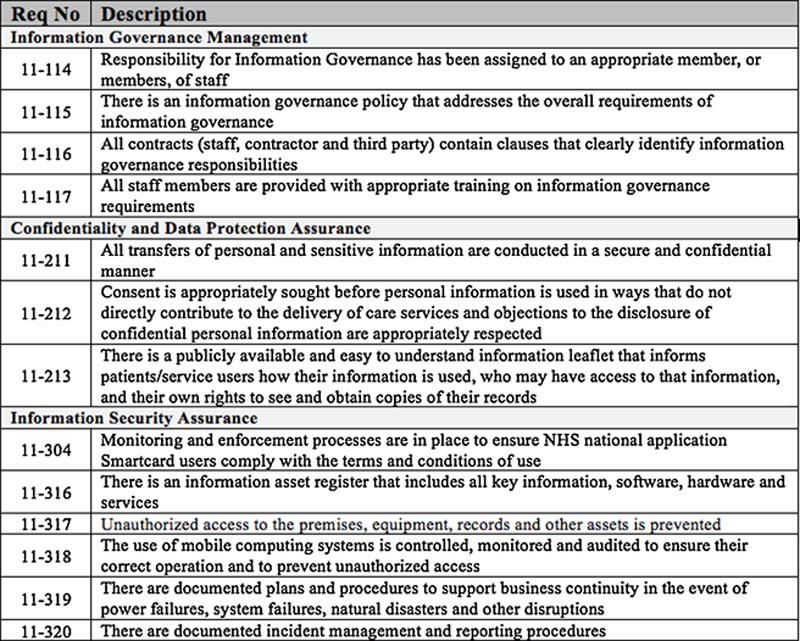
National Health Service
Understanding security and privacy governance
Information Governance
Head of Agency (CEO)
Risk Executive (Function)
Chief Information Officer (CIO)
Information Owner/Steward
Senior Information Security Officer
Authorizing Official
Authorizing Official Designated Representative
Common Control Provider
Information System Owner
Information System Security Officer
Information Security Architect
Information System Security Engineer
Security Control Assessor
Governance Structures
NIST Structure
Centralized Governance
Decentralized Governance
Hybrid Governance
National Health Service Structure
Understanding risk management methodology
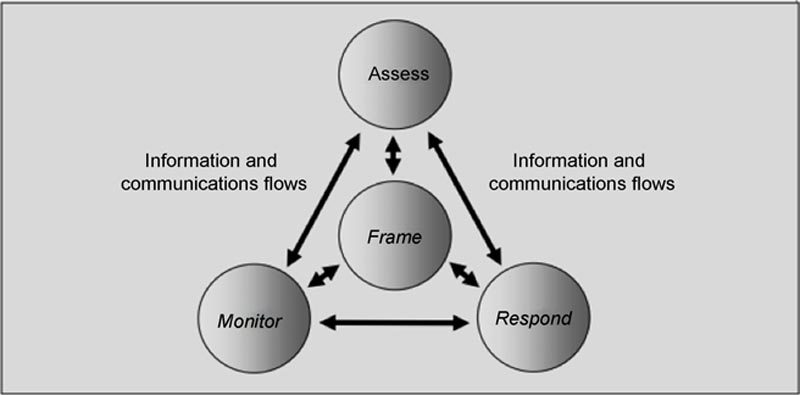
Framing
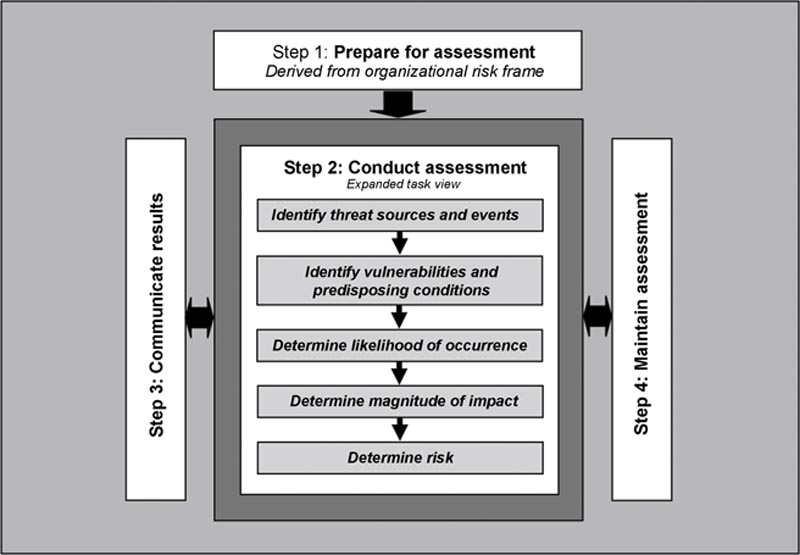
Assessment
Response
Monitoring
Risk Assessment Approach
Quantitative and Qualitative Analysis
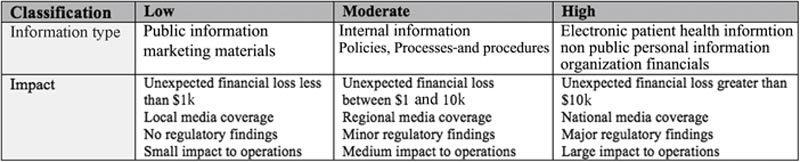
Asset Identification and Valuation
Threats
Vulnerability
Controls

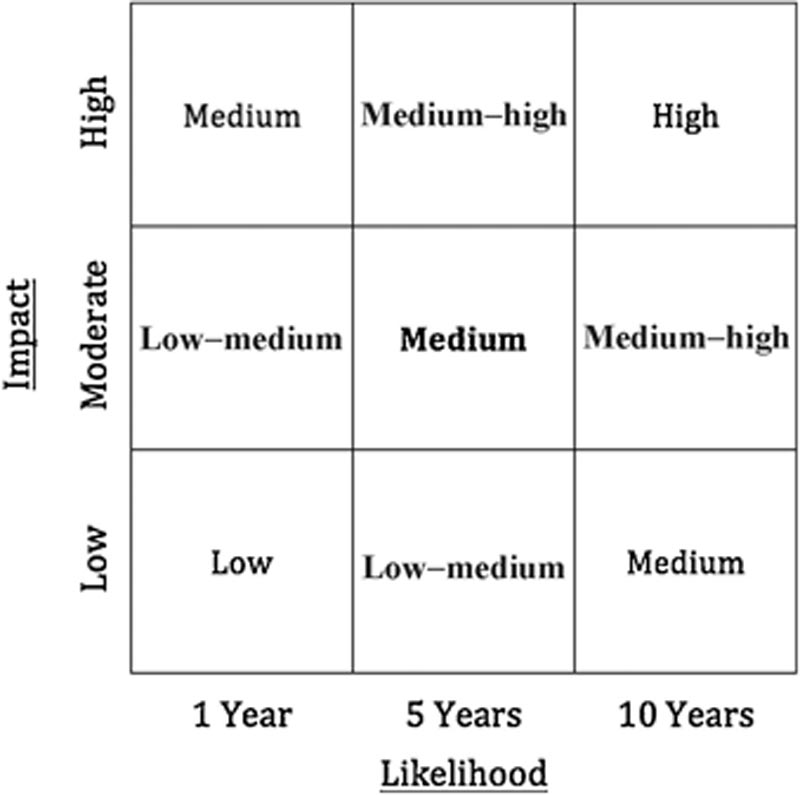
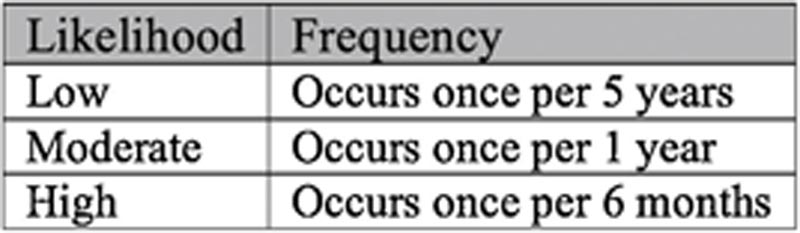
Likelihood
Impact
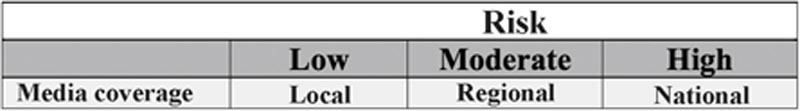
Risk

Risk Treatment
Information risk management life cycle and activities
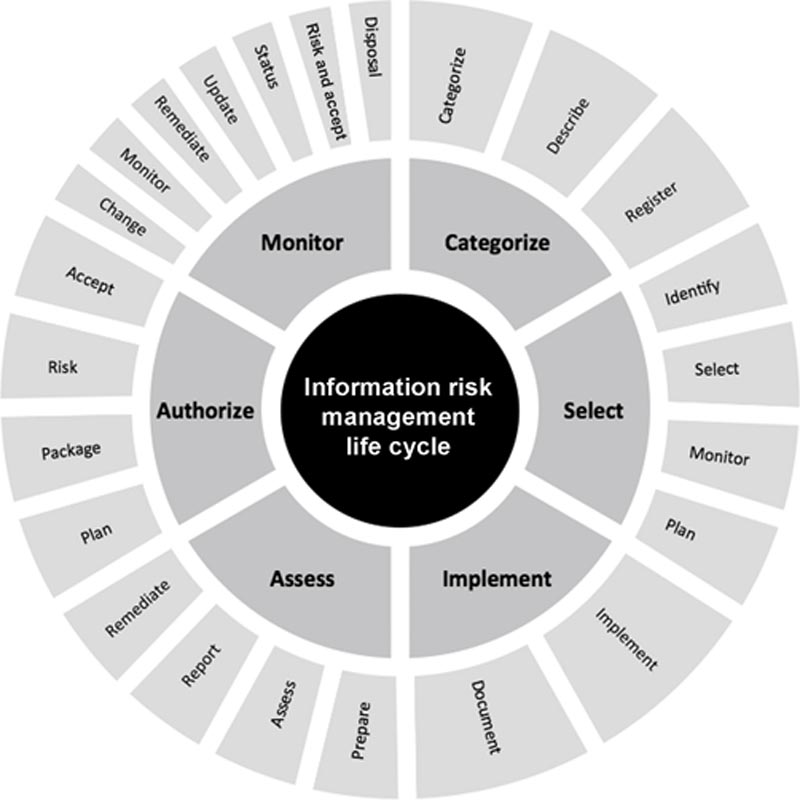
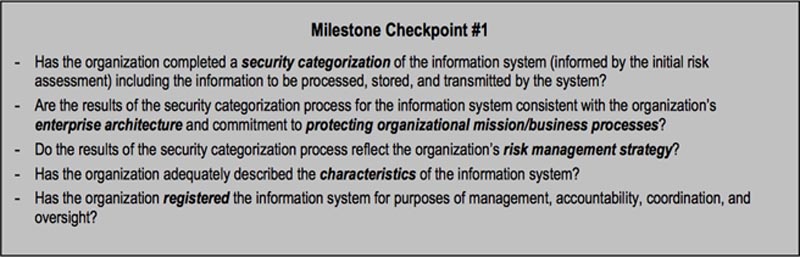
Step 1: Categorize Information Systems
Categorize
Describe
Register
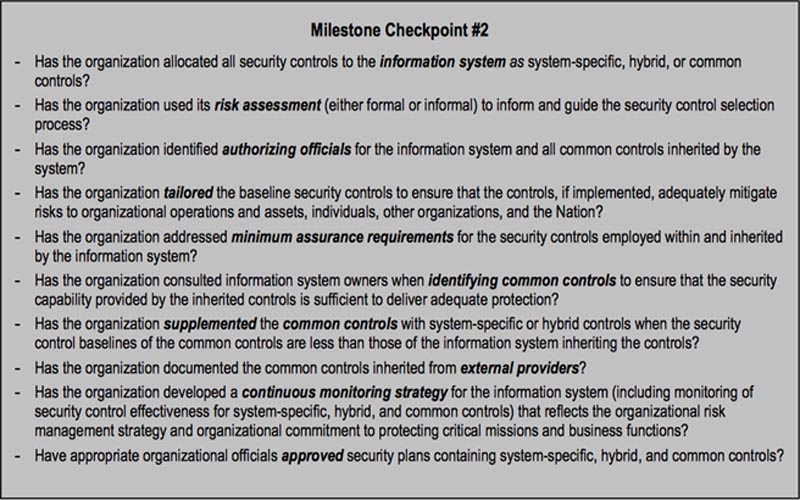
Step 2: Select Security Controls
Identify
Select
Monitor
Plan
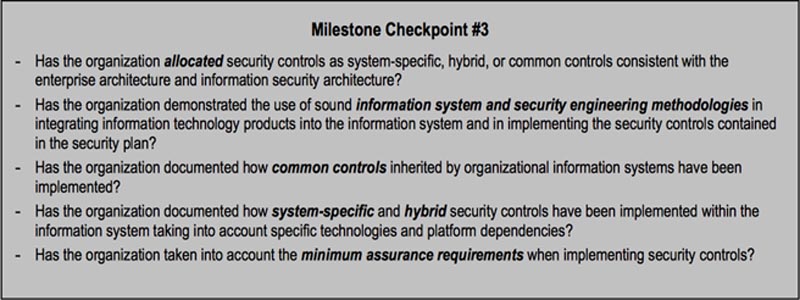
Step 3: Implement Security Controls
Implement
Document
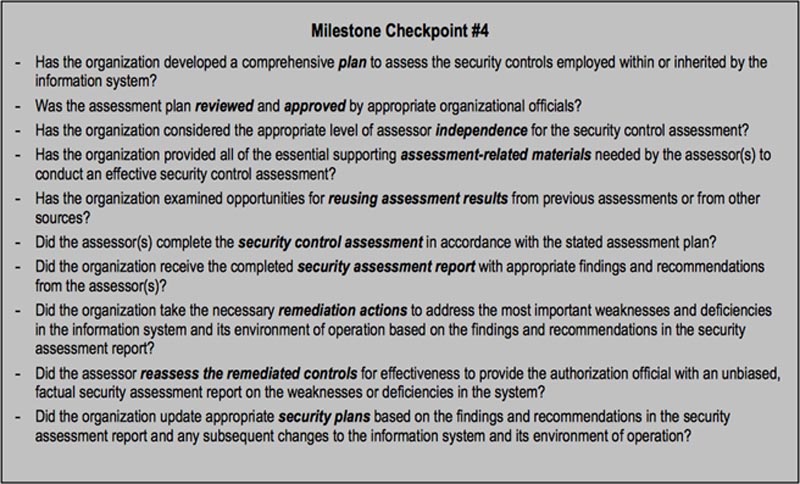
Step 4: Assess Security Controls
Prepare
Assess
Report
Remediate
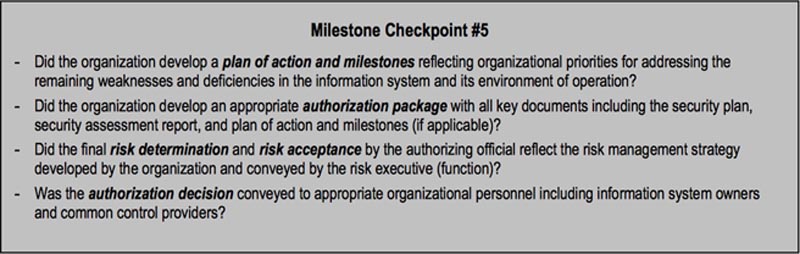
Step 5: Authorize Information System
Plan
Package
Risk
Accept
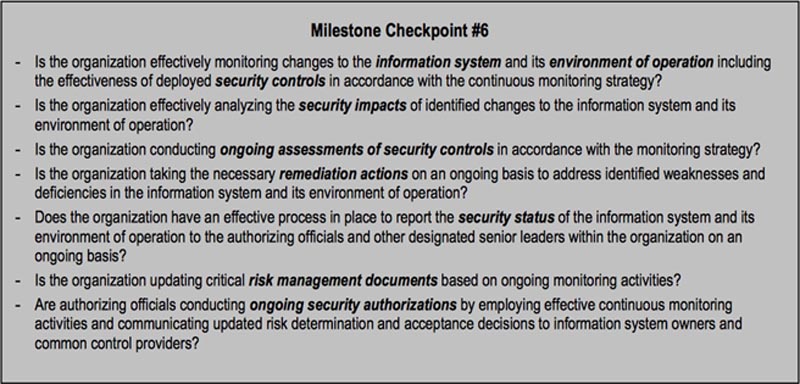
Step 6: Monitoring Security Controls
System Change
Monitor
Remediate
Update
Status
Risk and Accept
Disposal
Exception Handling
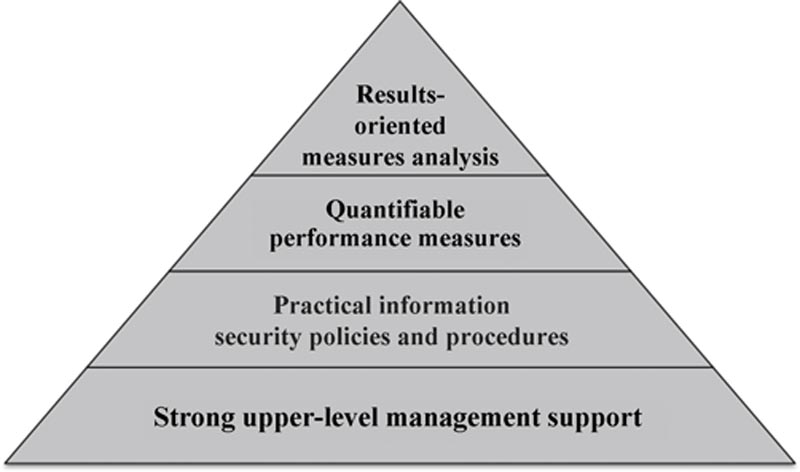
Reporting and Metrics
Key terms
| Term | Definition |
| CIA | Confidentiality, integrity, and availability |
| PII | Personally identifiable information |
| PHI | Personal health information |
| NIST | National Institute of Standards and Technology |
| FIPS | Federal Information Processing Standards |
| ISO | International Organization for Standardization |
| Information governance | Structure (or framework) consisting of policies, processes, procedures, behaviors, and technologies designed to assist with managing information throughout its life cycle in a manner consistent with stakeholder expectations |
| Administrative safeguards | Actions, policies, and procedures involved in the selection, development, implementation, and maintenance of security measures |
| Physical safeguards | Physical measures to protect the organization’s electronic information systems, data in physical form, buildings, and equipment from natural and environmental hazards and unauthorized intrusion |
| Technical safeguards | Technology and associated technical standards for its use to protect and control access to information |
| Head of agency | Highest-level official within an organization with overall responsibility for providing information security protections |
| Risk executive | Individual or group who ensures risk is viewed from an organization-wide perspective and risk is managed consistently |
| Chief Information Officer | Organizational official responsible for designating senior information security officer, maintaining policies and procedures, overseeing security personnel, and assisting and coordinating with senior officials regarding security matters |
| Information owner/steward | Organizational official with statutory, management, or operational authority for specified information and the responsibility for establishing the policies and procedures governing its generation, collection, processing, dissemination, and disposal |
| Senior information security officer | Also known as Chief Information Security Officer (CISO) or Chief Security Officer (CSO), is an organizational official responsible for carrying out security responsibilities and serving as primary liaison for Chief Information Officer |
| Authorizing official | Senior official or executive with the authority to formally assume responsibility for operating an information system at an acceptable level of risk to organizational operations and assets, individuals, other organizations, and the Nation |
| Authorizing official designated representative | Organizational official who acts on behalf of an authorizing official to coordinate and conduct the required day-to-day activities associated with the security authorization process |
| Common control provider | Individual, group, or organization responsible for the development, implementation, assessment, and monitoring of common controls (i.e., security controls inherited by information systems) |
| Information system owner | Organizational official responsible for the procurement, development, integration, modification, operation, maintenance, and disposal of an information system |
| Information system security officer | Also known as information security officer (ISO), is an individual responsible for ensuring that the appropriate operational security posture is maintained for an information system and, as such, works in close collaboration with the information system owner |
| Information security architect | Individual, group, or organization responsible for ensuring that the information security requirements necessary to protect the organization’s core missions and business processes are adequately addressed in all aspects of enterprise architecture including reference models, segment and solution architectures, and the resulting information systems supporting those missions and business processes |
| Information system security engineer | Individual, group, or organization responsible for conducting information system security engineering activities |
| Security control assessor | Individual, group, or organization responsible for conducting a comprehensive assessment of the management, operational, and technical security controls employed within or inherited by an information system to determine the overall effectiveness of the controls |
| Centralized governance | Authority, responsibility, and decision-making power are vested solely within central bodies |
| Decentralized governance | Authority, responsibility, and decision-making power are vested in and delegated to individual subordinate organizations within the parent organization |
| Hybrid governance | Authority, responsibility, and decision-making power are distributed between a central body and individual subordinate organizations |
| Framing | Understand the environment in which the organization operates and its risk tolerance (or appetite) to ensure risk is appropriately framed |
| Assessment | Identify threats, vulnerabilities, potential impact (harm) and likelihood harm will occur for the purpose of determining risk |
| Response | How an organization should respond to risk once identified |
| Monitoring | Monitoring of risk over time for the purpose of evaluating control effectiveness, identifying system and environment changes that create risk, and ensuring risk responses are implemented in alignment with business objectives, regulatory requirements, and security and privacy policies, standards, and guidelines |
| Quantitative analysis | Analysis largely involving numbers (e.g., $10,000, $50,000, $100,000), visible properties, and statistics and a set of methods, principles, or rules for assessing risk |
| Qualitative analysis | Involves non-numerical categories or levels (e.g., low, moderate, high) and can be more effective when communicating with stakeholders. May also involve data such as themes, trends, or patterns of human behavior |
| Single loss expectancy (SLE) | Loss in monetary (e.g., dollars) terms associated with occurrence of a single event |
| Annual rate of occurrence (ARO) | Anticipated frequency that a single loss expectancy event is projected to occur in a 12-month period |
| Annual loss expectancy (ALE) | Expected loss over a 12-month period based on the single loss expectancy (SLE) of an event and the annual rate of occurrence (ARO) |
| Tangible loss | Involves direct (real) value of physical assets including revenue and server or facility costs |
| Intangible loss | Involves indirect value such as brand, reputation, and loss of prospective customers and intellectual property |
| Threat | Any event with the potential to adversely impact the confidentiality, integrity, or availability of information systems through unauthorized access, destruction, disclosure, or modification of information, or denial of service |
| Vulnerability | Sometimes referred to as exposure, any weakness in an information system such as servers, networks, and infrastructure that could be intentionally or unintentionally exploited by a threat |
| Controls | Sometimes referred to as safeguards, they are techniques, methods, policies, standards, processes, procedures, guidelines, and physical devices designed to reduce the vulnerability of an information asset or likelihood of successful vulnerability exploitation by a threat |
| Likelihood | Estimate of the likelihood (or probability) a threat will be motivated and capable of successfully exploiting a vulnerability |
| Impact | Expected harm or damage to an organization resulting from the successful exploitation of a vulnerability |
| Risk | Measure of the extent to which an organization is threatened by a particular event |
| Risk acceptance | Decision to accept a particular risk and its associated losses assuming it falls within an organization’s risk tolerance |
| Risk transfer | Decision to fully or partially transfer a particular risk and its associated losses to a third party such as vendor or insurance company |
| Risk mitigation | Decision to reduce vulnerabilities through implementation of additional administrative, physical, and/or technical safeguards |
| Risk avoidance | Decision to avoid taking actions or activities that would create new risk for the organization |
| Information risk management | Continuous life cycle beginning from the point information is created and ending when information is disposed, destroyed, or no longer requires protection |
| Information system development life cycle (SDLC) | Involves five phases including initiation (concept/requirements definition), development/acquisition, implementation, operation/maintenance, and disposal |
Practice Exam
1. A structure consisting of policies, processes, procedures, behaviors, and technologies designed to assist with managing information throughout its life cycle is defined as:
a. Administrative safeguards
b. Privacy and security governance
c. Physical safeguards
d. Information governance
2. Actions, policies, and procedures involved in the selection, development, implementation, and maintenance of security measures are defined as:
a. Administrative safeguards
b. Privacy and security governance
c. Physical safeguards
d. Information governance
3. The Chief Information Officer is:
a. The highest-level official within an organization with overall responsibility for providing information security protections
b. Responsible for designating a senior information security officer
c. Responsible for carrying out chief information security responsibilities
d. An organizational official with statutory, management, or operational authority for specified information and the responsibility for establishing the policies and procedures governing its generation, collection, processing, dissemination, and disposal
4. The organizational official responsible for the procurement, development, integration, modification, operation, maintenance, and disposal of an information system is:
a. Authorizing official
b. Information owner/steward
c. Information system owner
d. Chief Information Officer
5. NIST SP 800-39 outlines approaches to information security governance that include all of the following except:
a. Centralized
b. Hybrid
c. Decentralized
d. Uniform
6. The International Organization for Standardization:
a. Has published an information governance toolkit designed to enable organizations and partners to assess compliance with the various laws, policies, and standards associated with information governance
b. Is responsible for the SP 800 series (computer security) and SP 500 series (information technology) publications relating to computer security
c. Is responsible for publication of the 27002:2005 and 27799:2008 standards
d. a and c
7. Framing involves:
a. Understanding the environment in which the organization operates
b. Understanding risk tolerance to ensure risk is appropriately framed
c. Assessing risk to identify threats, vulnerabilities, potential impact, and likelihood of harm
d. Evaluating risk over time for the purpose of evaluating control effectiveness, identifying system and environment changes that create risk, and ensuring risk responses are implemented in alignment with business objectives, regulatory requirements, and security and privacy policies, standards, and guidelines
8. Qualitative assessments:
a. Involve non-numerical categories or levels (e.g., low, moderate, high) and can be more effective when communicating with stakeholders
b. Involve an analysis largely involving numbers (e.g., $10,000, $50,000, $100,000), visible properties, and statistics and a set of methods, principles, or rules for assessing risk
c. a and b
d. None of the above
9. Annual loss expectancy (ALE) is:
a. The anticipated frequency that a single loss expectancy (SLE) event is projected to occur in a 12-month period
b. The expected loss over a 12-month period based on the SLE of an event and the annual rate of occurrence (ARO)
c. ALE = SLE × ARO
d. b and c
10. A vulnerability is:
a. Any event with the potential to adversely impact the confidentiality, integrity, or availability of information systems through unauthorized access, destruction, disclosure, or modification of information, or denial of service
b. Any weakness in an information system such as servers, networks, and infrastructure that could be intentionally or unintentionally exploited by a threat
c. A measure of the extent to which an organization is threatened by a particular event
d. a and c
11. A risk is:
a. Any event with the potential to adversely impact the confidentiality, integrity, or availability of information systems through unauthorized access, destruction, disclosure, or modification of information, or denial of service
b. Any weakness in an information system such as servers, networks, and infrastructure that could be intentionally or unintentionally exploited by a threat
c. A measure of the extent to which an organization is threatened by a particular event
d. a and c
12. Risk treatment generally involves the following options:
a. Transfer, acceptance, mitigate, eliminate
b. Acceptance, transmit, mitigate, deflect
c. Avoid, transfer, eliminate, manage
d. Mitigate, transfer, acceptance, avoid
13. Which one of the following formulas is incorrect?
a. Managed risk = residual risk − inherent risk
b. SLE = asset value × exposure
c. ALE = SLE − ARO
d. a and c
14. Controls are:
a. Any weakness in an information system such as servers, networks, and infrastructure that could be intentionally or unintentionally exploited by a threat
b. Techniques, methods, policies, standards, processes, procedures, guidelines, and physical devices designed to increase the vulnerability of an information asset
c. Techniques, methods, policies, standards, processes, procedures, guidelines, and physical devices designed to decrease the vulnerability of an information asset
d. Techniques, methods, policies, standards, processes, procedures, guidelines, and physical devices designed to maintain the vulnerability of an information asset
15. Likelihood is:
a. The expected harm or damage to an organization resulting from the successful exploitation of a vulnerability
b. The probability a vulnerability will be motivated and capable of exploiting a threat
c. A measure of the extent to which an organization is threatened by a particular event
d. None of the above
16. The categorization of information systems, selection, implementation, and assessment of security controls, authorization of information systems, and monitoring of security controls are steps included in the:
a. Information governance process
b. System development life cycle
c. IT governance process
d. Information risk management life cycle
17. Intangible loss involves:
a. Direct (real) value of physical assets including revenue and server or facility costs
b. Indirect value such as brand, reputation, and loss of prospective customers and intellectual property
c. Indirect value such as revenue and server or facility costs
d. None of the above
18. The information system development life cycle includes the following phases:
a. Initiation, development/acquisition, monitoring, disposal
b. Disposal, initiation, operational/maintenance, development/acquisition
c. Categorization, selection, implementation, authorization, monitoring
d. Selection, implementation, monitoring, disposal
19. Centralized governance is defined as:
a. Authority, responsibility, and decision-making powers that are distributed between a central body and individual subordinate organizations
b. Structure (or framework) consisting of policies, processes, procedures, behaviors, and technologies designed to assist with managing information throughout its life cycle in a manner consistent with stakeholder expectations
c. Authority, responsibility, and decision-making powers that are vested solely within central bodies
d. Authority, responsibility, and decision-making powers that are vested in and delegated to individual subordinate organizations within the parent organization
20. Risk transfer involves:
a. A decision to avoid taking actions or activities that would create new risk for the organization
b. Decision to accept a particular risk and its associated losses assuming it falls within an organization’s risk tolerance
c. Decision to reduce vulnerabilities through implementation of additional administrative, physical, and/or technical safeguards
d. None of the above
Practice Exam Answers
1. d
2. a
3. b
4. c
5. d
6. c
7. a
8. a
9. d
10. b
11. c
12. d
13. d
14. c
15. d
16. d
17. b
18. b
19. c
20. d
