Chapter 8
Passwords
IN THIS CHAPTER
![]() Identifying password vulnerabilities
Identifying password vulnerabilities
![]() Examining password-hacking tools and techniques
Examining password-hacking tools and techniques
![]() Hacking operating system passwords
Hacking operating system passwords
![]() Hacking password-protected files
Hacking password-protected files
![]() Protecting your systems from password hacking
Protecting your systems from password hacking
Password hacking is one of the easiest and most common ways that attackers obtain unauthorized network, computer, or application access. You often hear about it in the headlines, and study after study, such as the Verizon Data Breach Investigations Report, reaffirms that weak passwords are at the root of many security problems. I have trouble wrapping my head around the fact that I’m still talking about (and businesses are suffering from) weak passwords, but that fact is a reality. As an information security testing professional, you can certainly do your part to minimize the risks.
Although strong passwords — ideally, longer, stronger passphrases, which are difficult to crack (or guess) — are easy to create and maintain, network administrators and users often neglect this aspect of password management. Therefore, passwords are among the weakest links in the information security chain. Passwords rely on secrecy. After a password is compromised, its original owner isn’t the only person who can access the system with it. That’s when accountability goes out the window and bad things start happening.
External attackers and malicious insiders have many ways to obtain passwords. They can glean passwords simply by asking for them or by looking over the shoulders of users (shoulder surfing) while they type their passwords. Hackers can also obtain passwords from local computers by using password-cracking software. To obtain passwords from across a network, attackers can use remote cracking utilities, keyloggers, or network analyzers.
This chapter demonstrates how easily the bad guys can gather password information from your network and computer systems. I outline common password vulnerabilities and describe countermeasures that help prevent these vulnerabilities from being exploited on your systems. If you perform the tests and implement the countermeasures outlined in this chapter, you’ll be well on your way to securing your systems’ passwords.
Understanding Password Vulnerabilities
When you balance the cost of security and the value of the protected information, the combination of a user ID and a secret password is usually adequate. Passwords create a false sense of security, however, as the bad guys know, and they attempt to crack passwords as a step toward breaking into computer systems.
One big problem with relying solely on passwords for security is that more than one person can know them. Sometimes, multiple people knowing a password is intentional; often, it’s not. The tough part is that there’s no way of knowing who, besides the password’s owner, knows a password.
Here are the two general types of password vulnerabilities:
- Organizational or user vulnerabilities: Include lack of password policies that are enforced within the organization and lack of security awareness on the part of users
- Technical vulnerabilities: Include weak encryption methods and unsecure storage of passwords on computer systems
I explore these classifications in more detail in the following sections.
Before computer networks and the Internet, the user’s physical environment was an additional layer of password security that worked pretty well. Now that most computers have network connectivity, that protection is gone. Chapter 7 provides details on managing physical security in this age of networked computers and mobile devices.
Organizational password vulnerabilities
It’s human nature to want convenience, especially for remembering five, ten, or dozens of passwords for work and daily life. This desire for convenience makes passwords among the easiest barriers for an attacker to overcome. Almost 3 trillion (yes, trillion with a t and 12 zeros) eight-character password combinations are possible by using the 26 letters of the alphabet and the numerals 0 through 9. Strong passwords are easy to remember and difficult to crack. Most people, however, focus only on the easy-to-remember part. Users like to use such passwords as password, their login names, abc123, or no password at all! Don’t laugh; I’ve seen these blatant weaknesses and guarantee that they’re on any given network at this very moment.
Unless users are educated and reminded about using strong passwords, their passwords usually are:
- Easy to guess: Passwords such as “password” or “letmein” are more common that people think.
- Seldom changed: Many people are not required to change their passwords periodically and consistently over time.
-
Reused for many security points: When bad guys crack one password, they often can access other systems and websites with that same password and username.
 Using the same password across multiple systems and websites is nothing but a breach waiting to happen. Everyone is guilty of this practice, but that doesn’t make it right. Do what you can to protect your own credentials, and spread the word to your users about how this practice can get you into a real bind.
Using the same password across multiple systems and websites is nothing but a breach waiting to happen. Everyone is guilty of this practice, but that doesn’t make it right. Do what you can to protect your own credentials, and spread the word to your users about how this practice can get you into a real bind. - Written down: Generally, the more complex a password is, the more difficult it is to crack. When users create complex passwords, however, they’re more likely to write them down. External attackers and malicious insiders can find these passwords and use them against you and your business.
Technical password vulnerabilities
You can often find these serious technical vulnerabilities after exploiting organizational password vulnerabilities:
-
Password encryption schemes are weak. Hackers can break weak password storage mechanisms by using cracking methods that I outline in this chapter. Many vendors and developers believe that passwords are safe as long as they don’t publish the source code for their encryption algorithms. Wrong! A persistent, patient attacker usually can crack this so-called security by obscurity (a security measure that’s hidden from plain view but can be easily overcome) fairly quickly. After the code is cracked, it’s distributed across the Internet and becomes public knowledge.
Password cracking utilities take advantage of weak password encryption. These utilities do the grunt work and can crack any password, given enough time and computing power.
- Programs store their passwords in memory, unsecured files, and easily accessed databases.
- Unencrypted databases provide direct access to sensitive information to anyone who has database access, whether or not they have a business need to know the information.
- User applications display passwords on the screen while the user is typing.
The National Vulnerability Database (an index of computer vulnerabilities managed by the National Institute of Standards and Technology) currently identifies more than 4,000 password-related vulnerabilities! You can search for these issues at https://nvd.nist.gov/vuln/search to find out how vulnerable some of your systems may be from a password perspective.
Cracking Passwords
Password cracking is one of the most enjoyable hacks for the bad guys, because it fuels their sense of exploration and desire to figure out a problem. You may not have a burning desire to explore everyone’s passwords, but it helps to approach password cracking with this mindset.
Where should you start testing the passwords on your systems? Generally, any user’s password works. After you obtain one password, you can often obtain others — including administrator and root passwords.
Administrator passwords are the pot of gold. With unauthorized administrative access, you (or a criminal hacker) can do virtually anything on the system. When looking for your organization’s password vulnerabilities, I recommend first trying to obtain the highest level of access possible (such as domain administrator) through the most discreet method possible. That’s often what the criminals do.
You can use low-tech ways and high-tech ways to exploit vulnerabilities to obtain passwords. You can deceive users into divulging passwords over the telephone; observe what a user has written down on a piece of paper; or capture passwords directly from a computer, over a network, and via the Internet with the tools I cover in the following sections.
Cracking passwords the old-fashioned way
A hacker can use low-tech methods to crack passwords. These methods include using social engineering techniques such as phishing, shoulder surfing, and guessing passwords from information that he knows about the user.
Social engineering
The most popular low-tech method for gathering passwords is social engineering, which I cover in detail in Chapter 6. Social engineering takes advantage of the trusting nature of human beings to gain information that later can be used maliciously. A common social engineering technique is conning people into divulging their passwords. A well-crafted phishing email using a phishing platform such as LUCY is all it takes to get people to provide their login credentials. It sounds ridiculous, but I see it all the time.
TECHNIQUES
To obtain a password through social engineering, ask for it. You can simply call a user and tell him that he has some important-looking emails stuck in the mail queue, and you need his password to log in and free them. Many hackers and rogue insiders use this technique to try to get information.
Another way to get users to divulge their passwords is to send a phishing email requesting that information. I’ve found that asking users to confirm their understanding of and compliance with internal security policies by submitting their login credentials to a phishing website is all it takes. I cover email phishing in detail in Chapter 6.
A common weakness that can facilitate such social engineering is when staff members’ names, phone numbers, and email addresses are posted on your company website. Social media sites such as LinkedIn, Facebook, and Twitter can also be used against a company because these sites can reveal employees’ names and contact information.
COUNTERMEASURES
User awareness and consistent security training are great defenses against social engineering. Security tools are a good fail-safe if they monitor for such emails and web browsing at the host level, on the network perimeter, or in the cloud. Train users to spot attacks (such as suspicious phone calls or deceitful phishing emails) and to respond effectively. The best response is to refuse to give out any information and alert the appropriate information security manager in the organization. Also, take that staff directory off your website or at least remove IT staff members’ information.
Shoulder surfing
Shoulder surfing (the act of looking over someone’s shoulder to see what the person is typing) is an effective, low-tech password hack.
TECHNIQUES
To mount this attack, the bad guys must be near their victims (or nearby with binoculars or similar siting tool) and not look obvious. They simply collect the password by watching the user’s keyboard or screen when he logs in. An attacker with a good eye might even watch whether the user is glancing around his desk for a reminder of the password or the password itself. Security cameras or a webcam can even be used for such attacks. Coffee shops and airplanes provide ideal conditions for shoulder surfing.
You can try shoulder-surfing yourself. Walk around the office, and perform random spot checks. Go to users’ desks, and ask them to log in to their computers, the network, or even their email applications. Just don’t tell them what you’re doing beforehand, because they may attempt to hide what they’re typing or where they’re looking for their password — two things that they should’ve been doing all along! Just be careful doing this test, and respect other people’s privacy.
COUNTERMEASURES
Encourage users to be aware of their surroundings, and tell them not to enter their passwords when they suspect that someone is looking over their shoulders. Instruct users that if they suspect someone is looking over their shoulders while they’re logging in, they should politely ask the person to look away or, when necessary, hurl an appropriate epithet to show the offender that they’re serious. It may be easiest to lean into the shoulder surfer’s line of sight to keep him from seeing any typing and/or the screen itself. 3M Privacy Filters (https://www.3m.com/3M/en_US/privacy-screen-protectors-us) work well, but surprisingly, I rarely see them being used.
Inference
Inference is guessing passwords from information you know about a user, such as her date of birth, favorite television show, or phone number. It sounds silly, but criminals often determine their victims’ passwords by guessing them.
The best defense against an inference attack is to educate users to create secure passwords that don’t include information that can be associated with them. Absent certain password complexity filters, it’s not always easy to enforce this practice with technical controls, so you need a sound security policy and ongoing security awareness and training to remind users of the importance of creating secure passwords.
Weak authentication
External attackers and malicious insiders can obtain — or avoid having to use — passwords by taking advantage of older or unsecured operating systems that don’t require passwords to log in. The same goes for a phone or tablet that isn’t configured to use passwords.
BYPASSING AUTHENTICATION
On older operating systems (such as Windows 9x) that prompt for a password, you can press Esc on the keyboard to get right in. Okay, it’s hard to find any Windows 9x systems these days, but the same goes for any operating system — old or new — that’s configured to bypass the login screen. After you’re in, you can find other passwords stored in such places as dialup and VPN connections and in screen savers. Such passwords can be cracked easily with tools such as ElcomSoft’s Proactive System Password Recovery (https://www.elcomsoft.com/pspr.html) or Cain & Abel (www.oxid.it/cain.html). These weak systems can serve as trusted machines — meaning that people assume they’re secure — and provide good launching pads for network-based password attacks as well.
COUNTERMEASURES
The only true defense against weak authentication is to ensure that your operating systems require a password upon boot. To eliminate this vulnerability, at least upgrade to Windows 7, if not Windows 10, or use the most recent versions of Linux or one of the various flavors of Unix, including macOS X and Chrome OS.
Cracking passwords with high-tech tools
High-tech password cracking involves using a program that tries to guess a password by determining all possible password combinations. These high-tech methods are mostly automated after you access the computer and password database files.
The main password-cracking methods are dictionary attacks, brute-force attacks, and rainbow attacks. You find out how these methods work in the following sections.
Password-cracking software
You can try to crack your organization’s operating system and application passwords with various password-cracking tools:
-
Brutus (
www.hoobie.net/brutus) cracks logons for HTTP, FTP, Telnet, and more. -
Cain & Abel (
www.oxid.it/cain.html) cracks LM and NT LanManager (NTLM) hashes, Windows RDP passwords, Cisco IOS and PIX hashes, VNC passwords, RADIUS hashes, and lots more. (Hashes are cryptographic representations of passwords.) -
ElcomSoft Distributed Password Recovery (
https://www.elcomsoft.com/edpr.html) cracks Windows, Microsoft Office, PGP, Adobe, iTunes, and numerous other passwords in a distributed fashion, using up to 10,000 networked computers at one time. Also, this tool uses the same graphics processing unit (GPU) video acceleration as the ElcomSoft Wireless Auditor tool, which allows for cracking speeds up to 50 times faster. (I talk about the ElcomSoft Wireless Auditor tool in Chapter 10.) -
ElcomSoft System Recovery (
https://www.elcomsoft.com/esr.html) cracks or resets Windows user passwords, sets administrative rights, and resets password expirations, all from a bootable CD. This tool is great for demonstrating what can happen when laptop computers don’t have full disk encryption. -
John the Ripper (
www.openwall.com/john) cracks hashed Linux/Unix and Windows passwords. -
ophcrack (
http://ophcrack.sourceforge.net) cracks Windows user passwords, using rainbow tables from a bootable CD. Rainbow tables are precalculated password hashes that can speed the cracking process by comparing these hashes with the hashes obtained from the specific passwords being tested. -
Proactive Password Auditor (
https://www.elcomsoft.com/ppa.html) runs brute-force, dictionary, and rainbow cracks against extracted LM and NTLM password hashes. -
Proactive System Password Recovery (
https://www.elcomsoft.com/pspr.html) recovers practically any locally stored Windows passwords, such as logon passwords, WEP/WPA passphrases, SYSKEY passwords, and RAS/dialup/VPN passwords. -
pwdump3 (
www.openwall.com/passwords/windows-pwdump) extracts Windows password hashes from the SAM (Security Accounts Manager) database. -
RainbowCrack (
http://project-rainbowcrack.com) cracks LanManager (LM) and MD5 hashes quickly by using rainbow tables. -
THC-Hydra (
https://tools.kali.org/password-attacks/hydra) cracks logons for HTTP, FTP, IMAP, SMTP, VNC, and many more.
To understand how the preceding password-cracking programs generally work, you need to understand how passwords are encrypted. Passwords typically are encrypted when they’re stored on a computer, using an encryption or one-way hash algorithm such as SHA2 or MD5. Then hashed passwords are represented as fixed-length encrypted strings that always represent the same passwords with exactly the same strings. These hashes are irreversible for all practical purposes, so in theory, passwords can never be decrypted. Furthermore, certain passwords, such as those in Linux, have a random value called a salt added to them to create a degree of randomness. This value prevents the same password used by two people from having the same hash value.
Password-cracking utilities take a set of known passwords and run them through a password-hashing algorithm. The resulting encrypted hashes are compared at lightning speed with the password hashes extracted from the original password database. When a match is found between the newly generated hash and the hash in the original database, the password has been cracked. The process is that simple.
Other password-cracking programs attempt to log on by using a predefined set of user IDs and passwords. This method is how many dictionary-based cracking tools work, such as Brutus (www.hoobie.net/brutus) and SQLPing3 (www.sqlsecurity.com/downloads). I cover cracking web application and database passwords in chapters 15 and 16.
Passwords that are subjected to cracking tools eventually lose. You have access to the same tools as the bad guys. These tools can be used for both legitimate security assessments and malicious attacks. You want to find password weaknesses before the bad guys do. In this section, I show you some of my favorite methods for assessing Windows and Linux/Unix passwords.
Dictionary attacks
Dictionary attacks quickly compare a set of known dictionary-type words — including many common passwords — against a password database. This database is a text file with hundreds, if not thousands, of dictionary words, typically listed in alphabetical order. Suppose that you have a dictionary file that you downloaded from one of the sites in the following list. The English-dictionary file at the Purdue University site contains one word per line starting with 10th, 1st all the way to zygote.
Many password-cracking utilities use a separate dictionary that you create or download from the Internet. Here are some popular sites that house dictionary files and other miscellaneous word lists:
Don’t forget to use other language files as well, such as Spanish and Klingon.
Brute-force attacks
Brute-force attacks can crack practically any password, given sufficient time. Brute-force attacks try every combination of numbers, letters, and special characters until the password is discovered. Many password-cracking utilities let you specify such testing criteria as the character sets, password length to try, and known characters (for a mask attack). Sample Figure 8-1 shows some example brute-force password-cracking options.
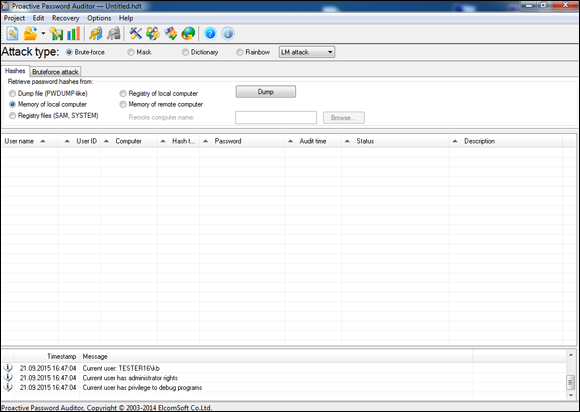
FIGURE 8-1: Brute-force password-cracking options in Proactive Password Auditor.
Can an expiring password deter a hacker’s attack and render password cracking software useless? Yes. After the password is changed, the cracking must start again if the hacker wants to test all the possible combinations. This scenario is one reason why it’s a good idea to change passwords periodically. Still, I’m not a big fan of forcing users to change their passwords often. Shortening the change interval can reduce the risk of passwords being cracked but can also be politically unfavorable in your business and end up creating the opposite of the effect you’re going for. You have to strike a balance among security, convenience, and usability. In many situations, I don’t think it’s unreasonable to require password changes every 6 to 12 months or (especially) after a suspected compromise. Keep in mind that there is a direct relationship between password change interval and password length. The longer the interval is the longer the password needs to be.
Rainbow attacks
A rainbow password attack uses rainbow cracking to crack various password hashes for LM, NTLM, Cisco PIX, and MD5 much more quickly and with extremely high success rates (near 100 percent). Password cracking speed is increased in a rainbow attack because the hashes are precalculated; thus, they don’t have to be generated individually on the fly, as they are in dictionary and brute-force cracking methods.
If you have a good set of rainbow tables, such as those offered via the ophcrack site and Project RainbowCrack (http://project-rainbowcrack.com), you can crack passwords in seconds, minutes, or hours versus the days, weeks, or even years required by dictionary and brute-force methods.
Cracking Windows passwords with pwdump3 and John the Ripper
The following steps use two of my favorite utilities to test the security of current passwords on Windows systems:
- pwdump3 (to extract password hashes from the Windows SAM database)
- John the Ripper (to crack the hashes of Windows and Linux/Unix passwords)
The following test requires administrative access to your Windows stand-alone workstation or the server:
-
Create a new directory called
passwordsat the root of your Windows C: drive. -
Download and install a decompression tool, if you don’t already have one:
 7-Zip (
7-Zip (https://www.7-zip.org) is a free decompression tool. Windows also includes built-in zip-file handling, albeit a bit kludgy. -
Download, extract, and install the following software into the
passwordsdirectory you created, if you don’t already have it on your system:-
pwdump3: Download the file from
www.openwall.com/passwords/microsoft-windows-nt-2000-xp-2003-vista-7. -
John the Ripper: Download the file from
www.openwall.com/john.
-
pwdump3: Download the file from
-
Enter the following command to run pwdump3 and redirect its output to a file called
cracked.txt:c:passwordspwdump3 >; cracked.txtThis file captures the Windows SAM password hashes that are cracked with John the Ripper. Figure 8-2 shows the contents of the
cracked.txtfile that contains the local Windows SAM database password hashes. -
Enter the following command to run John the Ripper against the Windows SAM password hashes to display the cracked passwords:
c:passwordsjohn cracked.txtThis process — shown in Figure 8-3 — can take seconds or days, depending on the number of users and the complexity of their associated passwords. My Windows example took only five seconds to crack five weak passwords.
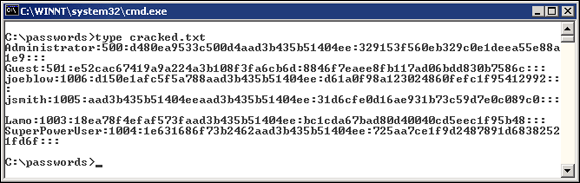
FIGURE 8-2: Output from pwdump3.
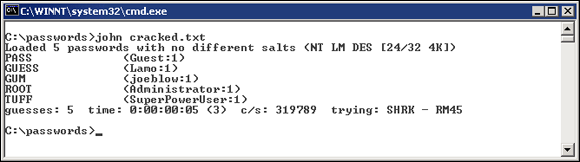
FIGURE 8-3: Cracked password file hashes with John the Ripper.
Cracking Unix/Linux passwords with John the Ripper
John the Ripper can also crack Unix/Linux passwords. You need root access to your system and to the password (/etc/passwd) and shadow password (/etc/shadow) files. Perform the following steps to crack Unix/Linux passwords:
-
Download the Unix source files from
www.openwall.com/john. -
Extract the program by entering the following command (with the current filename):
[root@localhost kbeaver]#tar -zxf john-1.8.0.tar.xz You can also crack Unix or Linux passwords on a Windows system by using the Windows/DOS version of John the Ripper.
You can also crack Unix or Linux passwords on a Windows system by using the Windows/DOS version of John the Ripper. -
Change to the
/srcdirectory that was created when you extracted the program, and enter the following command:make generic -
Change to the
/rundirectory, and enter the following command to use the unshadow program to combine thepasswdandshadowfiles and copy them to the filecracked.txt:./unshadow /etc/passwd /etc/shadow > cracked.txt The unshadow process won’t work with all Unix variants.
The unshadow process won’t work with all Unix variants. -
Enter the following command to start the cracking process:
./john cracked.txtWhen John the Ripper is complete (which could take some time), the output is similar to the results of the preceding Windows process (refer to Figure 8-3).
After completing the preceding Windows or Unix/Linux steps, you can force users to change passwords that don’t meet specific password policy requirements, create a new password policy, or use the information to update your security awareness program. Just do something.
Cracking password-protected files
Do you wonder how vulnerable password-protected word-processing, spreadsheet, and zip files are when users send them into the wild blue yonder? Wonder no more. Some great utilities can show how easily passwords are cracked.
Cracking files
Most password-protected files can be cracked in seconds or minutes. You can demonstrate this “wow factor” security vulnerability to users and management. Here’s a hypothetical scenario that could occur in the real world:
- Your chief financial officer (CFO) wants to send some confidential financial information in a Microsoft Excel spreadsheet to a company board member.
- She protects the spreadsheet by assigning it a password during the file-save process in Excel.
- For good measure, she uses WinZip to compress the file and adds another password to make it really secure.
-
The CFO sends the spreadsheet as an email attachment, assuming that the email will reach its destination.
The financial adviser’s network has content filtering, which monitors incoming emails for keywords and file attachments. Unfortunately, the financial firm’s network administrator is looking in the content-filtering system to see what’s coming in.
- This rogue network administrator finds the email with the confidential attachment, saves the attachment, and realizes that it’s password-protected.
- The network administrator remembers a great password-cracking tool called Advanced Archive Password Recovery (
www.elcomsoft.com/archpr.html) that can help him, so he proceeds to use it to crack the password.
Cracking password-protected files is as simple as that! Now all that the rogue network administrator must do is forward the confidential spreadsheet to his buddies or to the company’s competitors.
I recommend performing these file-password-cracking tests on files that you capture with a content-filtering or network-analysis tool. This method is a good way to determine whether your users are adhering to policy and using adequate passwords to protect the sensitive information that they’re sending.
Countermeasures
The best defense against weak file password protection is requiring your users to use a stronger form of file protection, such as Pretty Good Privacy (PGP) or the Advanced Encryption Standard (AES) encryption that’s built into WinZip when necessary. Ideally, you don’t want to rely on users to make decisions about what they should use to secure sensitive information, but relying on them is better than nothing. Stress that a file encryption mechanism, such as a password-protected zip file, is secure only if users keep their passwords confidential and never transmit or store them in unsecure clear text (such as in a separate email).
If you’re concerned about unsecure email transmissions, consider using a content-filtering system or a data loss prevention system to block all outbound email attachments that aren’t protected on your email server.
Understanding other ways to crack passwords
Over the years, I’ve found other ways to crack (or capture) passwords technically and through social engineering.
Keystroke logging
One of the best techniques for capturing passwords is remote keystroke logging — the use of software or hardware to record keystrokes as they’re typed.
LOGGING TOOLS
With keystroke-logging tools, you can assess the log files of your application to see what passwords people are using:
- Keystroke-logging applications can be installed on the monitored computer. I recommend that you check out Spector 360 by SpectorSoft (
www.spector360.com). Dozens of such tools are available on the Internet. - Hardware-based tools, such as KeyGhost (
www.keyghost.com), fit between the keyboard and the computer or replace the keyboard.
COUNTERMEASURES
The best defense against the installation of keystroke-logging software on your systems is to use an antimalware program or a similar endpoint protection software that monitors the local host. It’s not foolproof but can help. As with physical keyloggers, you’ll need to inspect each system visually.
Weak password storage
Many legacy and stand-alone applications — such as email, dial-up network connections, and accounting software — store passwords locally, which makes them vulnerable to password hacking. By performing a basic text search, I’ve found passwords stored in clear text on the local hard drives of machines. You can automate the process even further by using a program called FileLocator Pro (https://www.mythicsoft.com). I cover file and related storage vulnerabilities in Chapter 16.
SEARCHING
You can try using your favorite text-searching utility — such as the Windows search function, findstr, or grep — to search for password or passwd on your computer’s drives. You may be shocked to find what’s on your systems. Some programs even write passwords to disk or leave them stored in memory.
COUNTERMEASURES
The only reliable way to eliminate weak password storage is to use only applications that store passwords securely. This practice may not be practical, but it’s your only guarantee that your passwords are secure. Another option is to instruct users not to store their passwords when prompted.
Before upgrading applications, contact your software vendor to see how it manages passwords, or search for a third-party solution.
Network analyzer
A network analyzer sniffs the packets traversing the network, which is what the bad guys do if they can gain control of a computer, tap into your wireless network, or gain physical network access to set up their network analyzer. If they gain physical access, they can look for a network jack on the wall and plug right in.
TESTING
Figure 8-4 shows how crystal-clear passwords can be through the eyes of a network analyzer. This figure shows how Cain & Abel (www.oxid.it/cain.html) can glean thousands of passwords going across the network in a matter of a couple of hours. As you can see in the left pane, these clear text password vulnerabilities can apply to FTP, web, Telnet, and more. (The actual usernames and passwords are blurred to protect them.)
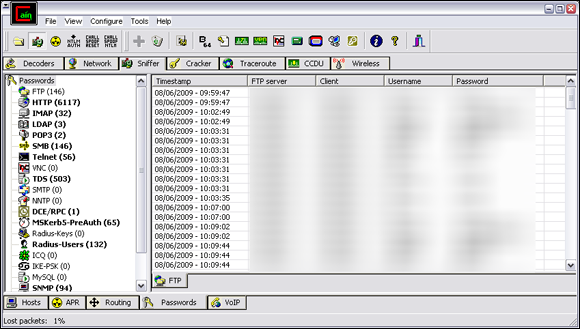
FIGURE 8-4: Using Cain & Abel to capture passwords going across the network.
Cain & Abel is a password-cracking tool that also has network analysis capabilities. You can also use a regular network analyzer, such as the commercial products Omnipeek (https://www.savvius.com) and CommView (https://www.tamos.com/products/commview), as well as the free open-source program Wireshark (https://www.wireshark.org). With a network analyzer, you can search for password traffic in various ways. To capture POP3 password traffic, for example, you can set up a filter and a trigger to search for the PASS command. When the network analyzer sees the PASS command in the packet, it captures that specific data.
Network analyzers require you to capture data on a hub segment of your network or via a monitor/mirror/span port on a switch. Otherwise, you can’t see anyone else’s data traversing the network — just yours. Check your switch’s user guide to see whether it has a monitor or mirror port and for instructions on how to configure it. You can connect your network analyzer to a hub on the public side of your firewall. You’ll capture only those packets that are entering or leaving your network — not internal traffic. I cover this type of network infrastructure hacking in detail in Chapter 9.
COUNTERMEASURES
Here are some good defenses against network analyzer attacks:
-
Use switches on your network, not hubs. Ethernet hubs are things of the past, but I still see them in use occasionally. If you must use hubs on network segments, a program like sniffdet (
http://sniffdet.sourceforge.net) for Unix/Linux-based systems and PromiscDetect (http://ntsecurity.nu/toolbox/promiscdetect) for Windows can detect network cards in promiscuous mode (accepting all packets, whether they’re destined for the local machine or not). A network card in promiscuous mode signifies that a network analyzer may be running on the network. - Make sure that unsupervised areas, such as an unoccupied lobby or training room, don’t have live network connections. An Ethernet port is all someone needs to gain access to your internal network.
- Don’t let anyone without a business need gain physical access to your switches or to the network connection on the public side of your firewall. With physical access, a hacker can connect to a switch monitor port or tap into the unswitched network segment outside the firewall and then capture packets.
Weak BIOS passwords
Most computer BIOS (basic input/output system) settings allow power-on passwords and/or setup passwords to protect the computer’s hardware settings that are stored in the CMOS chip. Here are some ways around these passwords:
- You usually can reset these passwords by unplugging the CMOS battery or by changing a jumper on the motherboard.
- Password-cracking utilities for BIOS passwords are available on the Internet and from computer manufacturers.
- If gaining access to the hard drive is your ultimate goal, you can remove the hard drive from the computer and install it in another one, and you’re good to go. This technique is a great way to prove that BIOS/power-on passwords are not effective countermeasures for lost or stolen laptops.
Tons of variables exist for hacking and hacking countermeasures depending on your hardware setup. If you plan to hack your own BIOS passwords, check for information in your user manual, or refer to the BIOS password-hacking guide I wrote at http://searchenterprisedesktop.techtarget.com/tutorial/BIOS-password-hacking. If protecting the information on your hard drives is your ultimate goal, full (sometimes referred to as whole) disk is the best way to go. I cover mobile-related password cracking in depth in Chapter 11. The good news is that newer computers (within the past five years or so) use a new type of BIOS called unified extensible firmware interface (UEFI), which is much more resilient to boot-level system cracking attempts. Still, a weak password may be all it takes for the system to be exploited.
Weak passwords in limbo
Bad guys often exploit user accounts that have just been created or reset by a network administrator or help desk. New accounts may need to be created for new employees or even for security testing purposes. Accounts may need to be reset if users forget their passwords or if the accounts have been locked out because of failed attempts.
WEAKNESSES
Here are some reasons why user accounts can be vulnerable:
- When user accounts are reset, they’re often assigned an easily cracked or widely-known password (such as the user’s name or the word password). The time between resetting the user account and changing the password is a prime opportunity for a break-in.
- Many systems have default accounts or unused accounts with weak passwords or no passwords at all. These accounts are prime targets.
COUNTERMEASURES
The best defenses against attacks on passwords in limbo are solid help-desk policies and procedures that prevent weak passwords from being available at any given time during the new-account-generation and password-reset processes. Following are perhaps the best ways to overcome this vulnerability:
- Require users to be on the phone with the help desk or to have a help-desk member perform the reset at the user’s desk.
- Require that the user immediately log in and change the password.
- If you need the ultimate in security, implement stronger authentication methods, such as challenge/response questions, smart cards, or digital certificates.
- Automate password reset functionality via self-service tools on your network so that users can manage most of their password problems without help from others.
I cover mobile-related password cracking in Chapter 11 and website/application password cracking in Chapter 15.
General Password Cracking Countermeasures
A password for one system usually equals passwords for many other systems because many people use the same (or at least similar) passwords on every system they use. For this reason, you may want to consider instructing users to create different passwords for different systems, especially on the systems that protect sensitive information. The only downside is that users have to keep multiple passwords and, therefore, may be tempted to write them down, which can negate any benefits.
Storing passwords
If you have to choose between weak passwords that your users can memorize and strong passwords that your users must write down, I recommend having readers write down passwords and store the information securely. Train users to store their written passwords in a secure place — not on keyboards or in easily cracked password-protected computer files (such as spreadsheets). Users should store a written password in any of these locations:
- A locked file cabinet or office safe
- A disk secured with full (whole) disk encryption, which can prevent an intruder from accessing the operating system and passwords stored on the system. (Just know that this technique isn’t foolproof, as I outline in Chapter 11.)
- A secure password management tool such as LastPass (
https://www.lastpass.com) or the open-source program Password Safe (https://pwsafe.org).
Again, as I mention earlier, applications such as these aren’t impervious to attack, so be careful.
Creating password policies
As an IT or security professional, you should show users the importance of securing their passwords. Here are some tips on how to do that:
- Demonstrate how to create secure passwords. Refer to passwords as passphrases, because people tend to take passwords literally and use only words, which can be less secure.
- Show what can happen when weak passwords are used or passwords are shared.
- Diligently build user awareness of social engineering attacks.
Enforce (or at least encourage the use of) a strong password-creation policy that includes the following criteria:
- Use uppercase and lowercase letters, special characters, and numbers. Never use only numbers. Such passwords can be cracked quickly.
- Misspell words or create acronyms from a quote or a sentence. ASCII, for example, is an acronym for American Standard Code for Information Interchange that can be used as part of a password.
- Use punctuation characters to separate words or acronyms.
- Change passwords every 6 to 12 months or immediately if they’re suspected of being compromised. Any change more frequent introduces an inconvenience that serves only to create more vulnerabilities.
- Use different passwords for each system. This practice is especially important for network infrastructure hosts, such as servers, firewalls, and routers. It’s okay to use similar passwords; just make them slightly different for each type of system, such as SummerInTheSouth-Win10 for Windows systems and Linux+SummerInTheSouth for Linux systems.
- Use variable-length passwords. This trick can throw off attackers because they won’t know the required minimum or maximum length of passwords and must try all password-length combinations.
- Don’t use common slang words or words that are in a dictionary.
- Don’t rely completely on similar-looking characters, such as 3 instead of E, 5 instead of S, or ! instead of 1. Password-cracking programs and dictionaries are available to help check for this practice.
- Don’t reuse the same password within at least four to five password changes.
- Use password-protected screen savers. Unlocked screens are a great way for systems to be compromised. You could have the strongest passwords and best full disk encryption in the world, but none of that matters if the computer is left unattended with the screen unlocked.
- Don’t share passwords. To each his or her own!
- Avoid storing user passwords in an unsecured central location, such as an unprotected spreadsheet on a hard drive. This practice is an invitation to disaster. Use a password manager to store user passwords if you’re willing to do so. (I’m not yet.)
Taking other countermeasures
Here are some other password hacking countermeasures that I recommend:
- Enable security auditing to help monitor and track password attacks. You can’t possibly manage this part of your security program if you’re not looking out for attacks.
-
Test your applications to make sure they aren’t storing passwords indefinitely in memory or writing them to disk. A good tool for this is WinHex (
www.winhex.com/winhex/index-m.html). I’ve used this tool to search a computer’s memory for keywords such as password, pass=, login, and so on, and have come up with some passwords that the developers thought were cleared from memory. Some password-cracking Trojan-horse applications are transmitted through worms or simple email attachments. Such malware can be lethal to your password-protection mechanisms if they’re installed on your systems. The best defense is malware protection or whitelisting software from Webroot, McAfee, or Bit9.
Some password-cracking Trojan-horse applications are transmitted through worms or simple email attachments. Such malware can be lethal to your password-protection mechanisms if they’re installed on your systems. The best defense is malware protection or whitelisting software from Webroot, McAfee, or Bit9. - Keep your systems patched. Passwords are reset or compromised during buffer overflows or other denial of service (DoS) conditions.
-
Know your user IDs. If an account has never been used, delete or disable the account until it’s needed. You can determine unused accounts by manual inspection or by using a tool such as DumpSec (https://
www.systemtools.com/somarsoft/?somarsoft.com), a tool that can enumerate the Windows operating system and gather user IDs and other information.
As the security manager in your organization, you can enable account lockout to prevent password-cracking attempts. Account lockout is the ability to lock user accounts for a certain time after a certain number of failed login attempts has occurred. Most operating systems (and some applications) have this capability. Don’t set it too low (fewer than five failed logins), and don’t set it too high to give a malicious user a greater chance of breaking in. Somewhere between 5 and 50 may work for you. I usually recommend a setting of around 10 or 15. Consider the following when configuring account lockout on your systems:
- To use account lockout to prevent any possibilities of a user DoS condition, require two different passwords, and don’t set a lockout time for the first one if that feature is available in your operating system.
- If you permit autoreset of the account after a certain period — often referred to as intruder lockout — don’t set a short time period. Thirty minutes often works well.
A failed login counter can increase password security and minimize the overall effects of account lockout if the account experiences an automated attack. A login counter can force a password change after a certain number of failed attempts. If the number of failed login attempts is high and has occurred over a short period, the account has likely experienced an automated password attack.
Other password-protection countermeasures include:
- Stronger authentication methods: Examples are challenge/response, smart cards, tokens, biometrics, and digital certificates.
- Automated password reset: This functionality lets users manage most of their password problems without getting others involved. Otherwise, this support issue becomes expensive, especially for larger organizations.
- Password-protected system BIOS: This countermeasure is especially important on servers and laptops that are susceptible to physical security threats and vulnerabilities.
Securing Operating Systems
You can implement various operating-system security measures to ensure that passwords are protected.
Windows
The following countermeasures can help prevent password hacks on Windows systems:
- Some Windows passwords can be gleaned by reading the clear text or crackable cipher text from the Windows Registry. Secure your registries by doing the following:
- Allow only administrator access.
- Harden the operating system by using well-known hardening best practices, such as those from SANS (
https://www.sans.org/critical-security-controls), NIST (https://csrc.nist.gov), the Center for Internet Security Benchmarks/Scoring Tools (https://www.cisecurity.org), and the ones outlined in Network Security For Dummies, by Chey Cobb (John Wiley & Sons, Inc.).
- Keep all SAM database backup copies secure.
-
Disable the storage of LM hashes in Windows for passwords that are shorter than 15 characters.
You can, for example, create and set the NoLMHash registry key to a value of 1 under
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlLsa. - Use local or group security policies to help eliminate weak passwords on Windows systems before they’re created.
- Disable null sessions in your Windows version or enable the Windows Firewall.
- In Windows XP and later versions, enable the Do Not Allow Anonymous Enumeration of SAM Accounts and Shares option in the local security policy.
Chapter 12 covers Windows hacks that you need to understand and test in more detail.
Linux and Unix
The following countermeasures can help prevent password cracks on Linux and Unix systems:
- Ensure that your system is using shadowed MD5 passwords.
- Help prevent the creation of weak passwords. You can use the built-in operating system password filtering (such as cracklib in Linux) or a password-auditing program (such as npasswd or passwd+).
- Check your
/etc/passwdfile for duplicate root UID entries. Hackers can exploit such entries to gain backdoor access.
Chapter 13 explains the Linux hacks and how to test Linux systems for vulnerabilities.