Chapter 13
Linux and macOS
IN THIS CHAPTER
![]() Examining Linux and macOS testing tools
Examining Linux and macOS testing tools
![]() Port-scanning hosts
Port-scanning hosts
![]() Gleaning information without logging in
Gleaning information without logging in
![]() Exploiting common vulnerabilities when logged in to Linux and macOS
Exploiting common vulnerabilities when logged in to Linux and macOS
![]() Minimizing Linux and macOS security risks
Minimizing Linux and macOS security risks
Linux hasn’t made inroads onto the enterprise desktop the way that Windows has, but its offshoot, macOS, certainly has. Both Linux and Macs are prevalent in enterprises, so you need to make sure that they fall within the scope of your security testing. A common misconception is that Linux and macOS (and its predecessor, OS X) are more secure than Windows. More and more often, however, these operating systems (OSes) are shown to be susceptible to the same types of security vulnerabilities that afflict Windows, so you can’t let your guard down.
Criminal hackers are increasingly attacking Linux and macOS because of their popularity and growing use in today’s network environment. Because some versions of Linux are free (in the sense that you don’t have to pay for the base operating system), many organizations are installing Linux for their web servers and email servers in the hope of saving money and having a more-secure system. Linux has grown in popularity for other reasons as well, including the following:
- Abundant resources are available, including books, websites, and developer and consultant expertise.
- There’s a lower risk that Linux will be hit with as much malware as Windows and its applications have to deal with. Linux excels when it comes to security, but things probably won’t stay that way.
- Buy-in has increased among Unix vendors, including IBM, HP, and Oracle.
- Unix and Linux have become easier to use.
On the workstation side, OS X and macOS are mainstream in business today. These OSes are based on Unix/Linux cores and are susceptible to many of the Linux flaws that I discuss in this chapter.
Based on what I see in my work, Linux is less vulnerable to common security flaws (especially in terms of missing third-party patches for Adobe, Java, and similar companies’ programs) than Windows. When comparing any current distribution of Linux, such as Ubuntu and Red Hat/Fedora, with Windows 7 or Windows 10, I tend to find more weaknesses in the Windows systems. Chalk this fact up to widespread use, more features, or uneducated users, but a lot more can happen in a Windows environment.
That said, Linux certainly isn’t flawless. In addition to the password attacks I cover in Chapter 8, certain remote and local attacks against Linux-based systems are possible. In this chapter, I show you some security issues in the Linux operating system and outline some countermeasures to plug the holes so that you can keep the bad guys out. Don’t let the title of this chapter fool you; a lot of this information applies to all flavors of Unix.
Understanding Linux Vulnerabilities
Vulnerabilities and attacks against Linux are creating business risks in a growing number of organizations, especially e-commerce companies, network and IT/security vendors, and cloud service providers that rely on Linux for many of their systems (including their own products). When Linux and macOS systems are hacked, the victim organizations can experience the same side effects as their Windows-using counterparts, including:
- Leaks of sensitive information.
- Cracked passwords.
- Corrupted or deleted databases.
- Systems taken offline.
Choosing Tools
You can use many Linux-based security tools to test your Linux and macOS systems. Some tools are much better than others. I find that my Windows-based commercial tools do as good a job as any. My favorites are:
- Kali Linux (
https://www.kali.org) toolset on a bootable DVD or.isoimage file. - NetScanTools Pro (
https://www.netscantools.com) for port scanning, OS enumeration, and more. -
Nexpose (
https://www.rapid7.com/products/nexpose) for detailed port scanning, OS enumeration, and vulnerability testing. A tool such as Nexpose can perform pretty much all the security testing you need to find flaws in Linux. Another popular commercial alternative is offered by Qualys (
A tool such as Nexpose can perform pretty much all the security testing you need to find flaws in Linux. Another popular commercial alternative is offered by Qualys (www.qualys.com). - Nmap (
https://nmap.org) for OS fingerprinting and detailed port scanning. - Nessus (
www.tenable.com/products/nessus-vulnerability-scanner) for OS fingerprinting, port scanning, and vulnerability testing.
Many other Linux hacking and testing tools are available at SourceForge (https://sourceforge.net). Find a set of tools — preferably as few as possible — that can do the job you need to do and that you feel comfortable working with. As I've said before, you often (not always) get what you pay for.
Gathering Information About Your System Vulnerabilities
You can scan your Linux and macOS systems and gather information from both outside (if the system is a publicly accessible host) and inside your network. That way, you can see what the bad guys see from both directions.
System scanning
Linux services, called daemons, are the programs that run on a system and serve up various services and applications for users.
- Internet services — such as the Apache web server (httpd), Telnet (telnetd), and FTP (ftpd) — may give away too much information about the system, including software versions, internal IP addresses, and usernames. This information could allow hackers to exploit a known weakness in the system.
- TCP and UDP small services — such as echo, daytime, and chargen — may be enabled by default and don’t need to be.
The vulnerabilities inherent in your Linux systems depend on what services are running. You can perform basic port scans to glean information about what’s running.
The NetScanTools Pro results in Figure 13-1 show many potentially vulnerable services on this Linux system, such as the services of SSH, DNS, and TFTP.
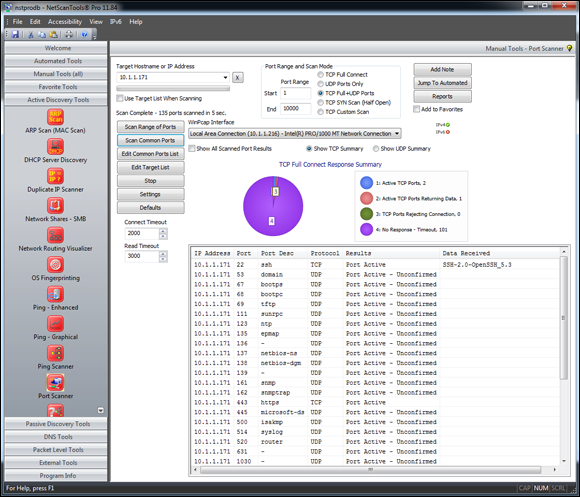
FIGURE 13-1: Port scanning a Linux host with NetScanTools Pro.
In addition to NetScanTools Pro, you can run a vulnerability scanner such as Nexpose against the system to try to gather more information. Note all the missing patches in this macOS High Sierra system shown in Figure 13-2.
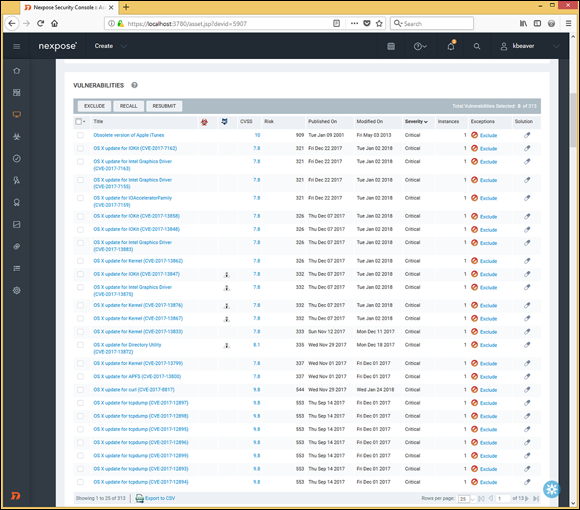
FIGURE 13-2: Using Nexpose to discover vulnerabilities in macOS.
Keep in mind that you’re going to find the most vulnerabilities in Linux and macOS by performing authenticated vulnerability scans, which is particularly important to do because it shows you what’s exploitable by users or malware on your systems. Even Linux and macOS are susceptible to malware! You’ll want to run such scans at least once per year or after any major application or OS upgrades on your workstations and servers.
Figure 13-3 shows the awesome feature of Nexpose that allows you to test your login credentials before kicking off a vulnerability scan of your network.
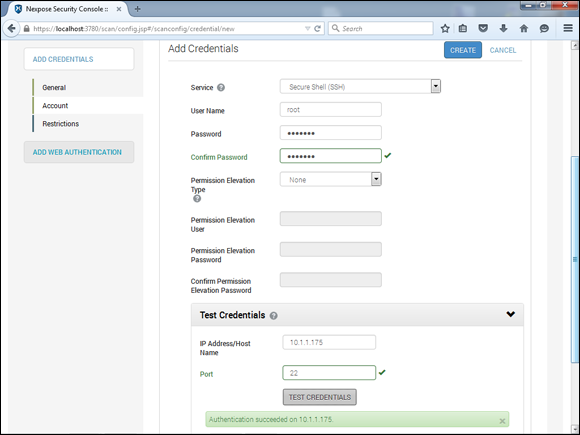
FIGURE 13-3: Using the Test Credentials feature as part of the Nexpose scan configuration.
What’s the big deal about this feature, you say? Well, first, it can be a whole lot of hassle to think that you’re entering the proper login credentials into the scanner, only to find out hours later that the logins weren’t successful, which can invalidate the scan you ran. It can also be a threat to your budget (or wallet, if you work for yourself) if you’re charged by the scan only to discover that you have to rescan hundreds or even thousands of network hosts. I’ve been down that road many times, and it’s a real pain, to say the least.
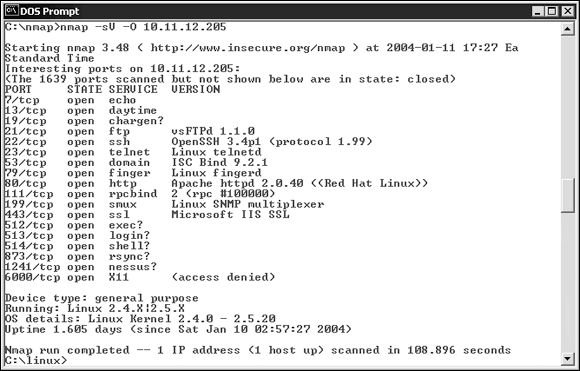
FIGURE 13-4: Using Nmap to determine the OS kernel version of a Linux server.
The Windows-based NetScanTools Pro can also determine the version of Linux that’s running, as shown in Figure 13-5.
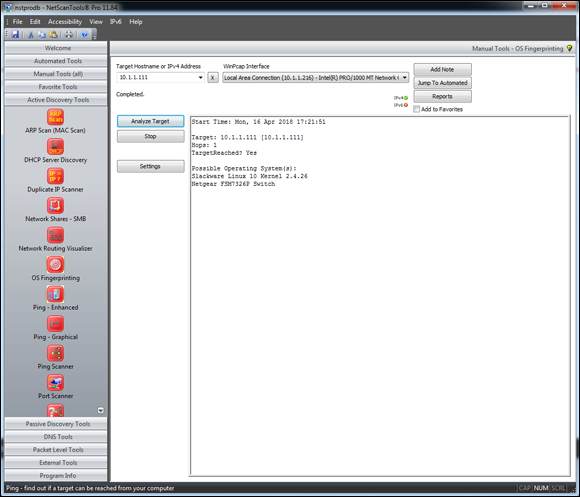
FIGURE 13-5: Using NetScanTools Pro to determine that Slackware Linux is likely running.
Countermeasures against system scanning
Although you can’t prevent system scanning, you can implement the following countermeasures to keep the bad guys from gleaning too much information about your systems and using it against you somehow:
- Protect the systems with either:
- A firewall, such as iptables, that’s built into the OS
- A host-based intrusion prevention system (IPS) such as PortSentry (
https://sourceforge.net/projects/sentrytools), a local agent such as Snare (https://www.snaresolutions.com/products/snare-agents), or McAfee Host Intrusion Prevention for Server (https://www.mcafee.com/us/products/host-ips-for-server.aspx) that ties into a larger security incident and event management system that monitors for and correlates network events, anomalies, and breaches.
- Disable the services you don’t need, including RPC, HTTP, FTP, Telnet, and the small UDP and TCP services — anything for which you don’t have a true business need. This practice keeps the services from showing up in a port scan, which gives an attacker less information (and presumably less incentive to break in to your system).
- Make sure that the latest software updates are installed to reduce the chance of exploitation if an attacker determines what services you’re running.
Finding Unneeded and Unsecured Services
When you know which daemons and applications are running — such as FTP, Telnet, and a web server — it’s nice to know exactly which versions are running so that you can look up their associated vulnerabilities and decide whether to turn them off. The National Vulnerability Database site (https://nvd.nist.gov) is a good resource for looking up vulnerabilities.
Searches
Several security tools can uncover vulnerabilities in your Linux systems. These tools may not identify all applications down to the version number, but they’re a powerful way of collecting system information.
Vulnerabilities
Be especially mindful of these common security weaknesses in Linux systems:
- Anonymous FTP, especially if it isn’t configured properly, can allow an attacker to download and access files on your system.
- Telnet and FTP are vulnerable to network analyzer captures of the clear text user ID and password that the applications use. Their logins can also be brute-force attacked.
- Old versions of sendmail and OpenSSL have many security issues, including denial of service (DoS) flaws that can take systems offline.
- R-services such as rlogin, rdist, rexecd, rsh, and rcp are especially vulnerable to attacks that rely on trust.
Many web servers run on Linux, so you can’t overlook the importance of checking for weaknesses in Apache as well as Tomcat or other applications. A common Linux vulnerability, for example, is that usernames can be determined via Apache when it doesn’t have the UserDir directive disabled in its httpd.conf file. You can exploit this weakness manually by browsing to well-known user folders such as http://www.your~site.com/user_name or, better, by using a vulnerability scanner such as Netsparker (https://www.netsparker.com) or Nexpose to enumerate the system automatically. Either way, you may be able to find out which Linux users exist and then launch a web password cracking attack. You can also access system files (including /etc/passwd) via vulnerable CGI and PHP code. I cover hacking web applications in Chapter 15.
Likewise, File Transfer Protocol (FTP) often runs unsecured on Linux systems. I've found Linux systems with anonymous FTP enabled that were sharing sensitive health-care and financial information to everyone on the local network. Talk about a lack of accountability! Don’t forget to look for the simple stuff. When testing Linux, you can dig deep into the kernel and do this or that to carry out some über-complex exploit, but the little things usually get you. Look for the low-hanging fruit on your network, as that stuff will get you into the most trouble the quickest.
Tools
The following tools can perform in-depth analysis beyond port scanning to enumerate your Linux systems and see what others can see:
- Nmap can check for specific versions of the services loaded, as shown in Figure 13-6. Simply run Nmap with the
-sVcommand-line switch. -
netstatshows the services running on a local machine. Enter this command while logged in:netstat –anp - List Open Files (
lsof) displays processes that are listening and files that are open on the system.

FIGURE 13-6: Using Nmap to check application versions.
Countermeasures against attacks on unneeded services
You can and should disable the unneeded services on your Linux systems, which is one of the best ways to keep your Linux system secure. Like reducing the number of entry points (such as open doors and windows) in your house, the more entry points you eliminate, the fewer places an intruder can break in.
Disabling unneeded services
The best method of disabling unneeded services depends on whether the daemon is loaded in the first place. You have several places to disable services, depending on the version of Linux you're running.
INETD.CONF (OR XINETD.CONF)
If it makes good business sense to do so (that is, if you don’t need the services), disable unneeded services by commenting out the loading of daemons you don’t use. Follow these steps:
-
Enter the following command at the Linux prompt:
ps -auxThe process ID (PID) for each daemon, including inetd, is listed onscreen. In Figure 13-7, the PID for the sshd (Secure Shell daemon) is 646.
- Make note of the PID for inetd.
-
Open
/etc/inetd.confin the Linux text editor vi by entering the command:vi /etc/inetd.confor
/etc/xinetd.conf - When you have the file loaded in vi, enable the insert (edit) mode by pressing I.
-
Move the cursor to the beginning of the line of the daemon that you want to disable, such as httpd (web server daemon), and type # at the beginning of the line.
This step comments out the line and prevents it from loading when you reboot the server or restart inetd. It’s also good for record keeping and change management.
-
To exit vi and save your changes, press Esc to exit the insert mode, type :wq, and then press Enter.
This step tells vi that you want to write your changes and quit.
-
Restart inetd by entering this command with the inetd PID:
kill –HUP PID

FIGURE 13-7: Viewing the PIDs for running daemons by using ps -aux.
CHKCONFIG
If you don’t have an inetd.conf file (or if it's empty), your version of Linux is probably running the xinetd program — a more-secure replacement for inetd — to listen for incoming network application requests. You can edit the /etc/xinetd.conf file in this case. For more information on the use of xinetd and xinetd.conf, enter man xinetd or man xinetd.conf at a Linux command prompt. If you're running Red Hat 7.0 or later, you can run the /sbin/chkconfig program to turn off the daemons you don’t want to load.
You can also enter chkconfig --list at a command prompt to see what services are enabled in the xinetd.conf file.
If you want to disable a specific service, such as snmp, enter the following:
chkconfig --del snmpd
Access control
TCP Wrappers can control access to critical services that you run, such as FTP and HTTP. This program controls access for TCP services and logs their use, helping you control access via host name or IP address and track malicious activities.
You can find more information about TCP Wrappers at ftp://ftp.porcupine.org/pub/security/index.html.
Securing the .rhosts and hosts.equiv Files
Linux and all the flavors of Unix are file-based OSes. Practically everything that’s done on the system involves the manipulation of files, which is why so many attacks against Linux are at the file level.
Hacks using the hosts.equiv and .rhosts files
If hackers can capture a user ID and password by using a network analyzer or can crash an application and gain access via a buffer overflow, one thing they look for is what users are trusted by the local system. For that reason, it’s critical to assess these files yourself. The /etc/hosts.equiv and .rhosts files list this information.
hosts.equiv
The /etc/hosts.equiv file won't give away root access information, but it does specify which accounts on the system can access services on the local host. If tribe were listed in this file, for example, all users on the tribe system would be allowed access. As with the .rhosts file, external hackers can read this file and then spoof their IP address and host name to gain unauthorized access to the local system. Attackers can also use the names located in the .rhosts and hosts.equiv files to look for the names of other computers to exploit.
.rhosts
The highly important $home/.rhosts files in Linux specify which remote users can access the Berkeley Software Distribution (BSD) r-commands (such as rsh, rcp, and rlogin) on the local system without a password. This file is in a specific user's (including root’s) home directory, such as /home/jsmith. A .rhosts file may look like this:
tribe scott
tribe eddie
+tribe geoff
This file allows users Scott and Eddie on the remote-system tribe to log in to the local host with the same privileges as the local user. If a plus sign (+) is entered in the remote-host and user fields, any user from any host could log in to the local system. The hacker can add entries into this file by using either of these tricks:
- Manipulating the file manually.
- Running a script that exploits an unsecured Common Gateway Interface (CGI) script on a web-server application that's running on the system.
This configuration file is a prime target for a malicious attack. On most Linux systems I’ve tested, these files aren’t enabled by default. But a user can create one in his or her home directory on the system intentionally or accidentally, which can create a major security hole in the system.
Countermeasures against .rhosts and hosts.equiv file attacks
Use both of the following countermeasures to prevent hacker attacks against the .rhosts and hosts.equiv files in your Linux system.
Disabling commands
A good way to prevent abuse of these files is to disable the BSD r-commands. You can disable these commands in two ways:
- Comment out the lines starting with
shell,login, andexecininetd.conf. - Edit the
rexec,rlogin, andrshfiles located in the/etc/xinetd.ddirectory. Open each file in a text editor, and changedisable=notodisable=yes, as shown in Figure 13-8.

FIGURE 13-8: The rexec file showing the disable option.
- Enter setup at a command prompt.
- Enter system-config-services.
- Select the appropriate services.
- Click Disable.
Blocking access
A couple of countermeasures can block rogue access of the .rhosts and hosts.equiv files:
- Block spoofed addresses at the firewall, as I outline in Chapter 9.
- Set the read permissions for each file's owner only.
.rhosts: Enter this command in each user’s home directory:chmod 600 .rhostshosts.equiv: Enter this command in the/etcdirectory:chmod 600 hosts.equiv
You can also use Open Source Tripwire (http://sourceforge.net/projects/tripwire) to monitor these files and alert you when access is obtained or changes are made.
Assessing the Security of NFS
The Network File System (NFS) is used to mount remote file systems (similar to shares in Windows) from the local machine. Given the remote access nature of NFS, it certainly has its fair share of hacks. I cover additional storage vulnerabilities and hacks in Chapter 16.
NFS hacks
If NFS was set up improperly or its configuration was been tampered with — namely, the /etc/exports file, which contains a setting that allows the world to read the entire file system — remote hackers can easily obtain remote access and do anything they want on the system. Assuming that no access control list is in place, all it takes is a line, such as the following, in the /etc/exports file:
/ rw
This line says that anyone can mount the root partition remotely in a read-write fashion. The following conditions must also be true:
- The NFS daemon (nfsd) must be running, along with the portmap daemon that would map NFS to RPC.
- The firewall must allow the NFS traffic through.
- The remote systems that are allowed into the server running the NFS daemon must be placed in the
/etc/hosts.allowfile.
This remote-mounting capability is easy to misconfigure. It's often related to a Linux administrator’s misunderstanding what it takes to share NFS mounts and resorting to the easiest way to get it working. If someone can gain remote access, the system is theirs.
Countermeasures against NFS attacks
The best defense against NFS hacking depends on whether you need the service running.
- If you don’t need NFS, disable it.
- If you need NFS, implement the following countermeasures:
- Filter NFS traffic at the firewall — typically UDP port 111 (the port-mapper port) if you want to filter all RPC traffic.
- Add network access control lists to limit access to specific hosts.
- Make sure that your
/etc/exportsand/etc/hosts.allowfiles are configured properly to keep the world outside your network.
Checking File Permissions
In Linux, special file types allow programs to run with the file owner's rights: SetUID (for user IDs) and SetGID (for group IDs).
SetUID and SetGID are required when a user runs a program that needs full access to the system to perform its tasks. When a user invokes the passwd program to change his or her password, for example, the program is loaded and run without root’s or any other user’s privileges. This is done so that the user can run the program and the program can update the password database without the root account’s being involved in the process.
File permission hacks
By default, rogue programs that run with root privileges can be easily hidden. An external attacker or malicious insider might do this to hide hacking files, such as rootkits, on the system. This can be done with SetUID and SetGID coding in hacking programs.
Countermeasures against file permission attacks
You can test for rogue programs by using both manual and automated testing methods.
Manual testing
The following commands can identify and print to the screen SetUID and SetGID programs:
- Programs that are configured for SetUID:
find / -perm -4000 –print - Programs that are configured for SetGID:
find / -perm -2000 –print - Files that are readable by anyone in the world:
find / -perm -2 -type f –print - Hidden files:
find / -name ".*"
You probably have hundreds of files in each of these categories, so don’t be alarmed. When you discover files with these attributes set, you need to make sure that they’re supposed to have those attributes by researching in your documentation or on the Internet or by comparing them with a known-secure system or data backup.
Automatic testing
You can use an automated file integrity monitoring program to alert you when these types of changes are made. This practice is what I recommend; it’s a lot easier than manual checks on an ongoing basis. Security controls can include:
- A change-detection application, such as Open Source Tripwire, can help you keep track of what changed and when.
- A file-monitoring program such as COPS (point your web browser to
ftp://ftp.cerias.purdue.edu/pub/tools/unix/scanners/cops), finds files that have changed in status, such as a new SetUID or removed SetGID.
Finding Buffer Overflow Vulnerabilities
RPC and other vulnerable daemons are common targets for buffer-overflow attacks. Buffer-overflow attacks are how hackers often get in to modify system files, read database files, and more.
Attacks
In a buffer-overflow attack, the attacker manually sends strings of information to the victim Linux machine or writes a script that does so. These strings contain the following:
- Instructions to the processor to do nothing.
- Malicious code to replace the attacked process.
exec ("/bin/sh")creates a shell command prompt, for example. - A pointer to the start of the malicious code in the memory buffer.
If an attacked application (such as FTP or RPC) is running as root, this situation can give attackers root permissions in their remote shells. Specific examples of vulnerable software running on Linux are Samba, MySQL, and Mozilla Firefox. Depending on the version, this software can be exploited with commercial or free tools such as Metasploit (https://www.metasploit.com) to obtain remote command prompts, add backdoor user accounts, change ownership of files, and more. I cover Metasploit in Chapter 12.
Countermeasures against buffer overflow attacks
Three main countermeasures can help prevent buffer-overflow attacks:
- Disable unneeded services.
- Protect your Linux systems with a firewall or a host-based IPS.
-
Enable another access control mechanism, such as TCP Wrappers, that authenticates users with a password.
 Don't just enable access controls via an IP address or host name, which can easily be spoofed.
Don't just enable access controls via an IP address or host name, which can easily be spoofed.
As always, make sure that your systems have been updated with the latest kernel and software updates.
Checking Physical Security
Some Linux vulnerabilities involve the bad guy’s being at the system console — something that’s entirely possible given the insider threats that every organization faces.
Physical security hacks
If an attacker is at the system console, anything goes, including rebooting the system (even if no one is logged in) by pressing Ctrl+Alt+Delete. After the system is rebooted, the attacker can start it in single-user mode, which allows him to zero out the root password or possibly read the entire shadow password file. I cover password cracking in Chapter 8.
Countermeasures against physical security attacks
Edit your /etc/inittab file, and comment out (place a # sign in front of) the line that reads ca::ctrlaltdel:/sbin/shutdown -t3 -r now, shown in the last line of Figure 13-9. These changes prevent someone from rebooting the system by pressing Ctrl+Alt+Delete. Be forewarned that this change also prevents you from legitimately pressing Ctrl+Alt+Delete.
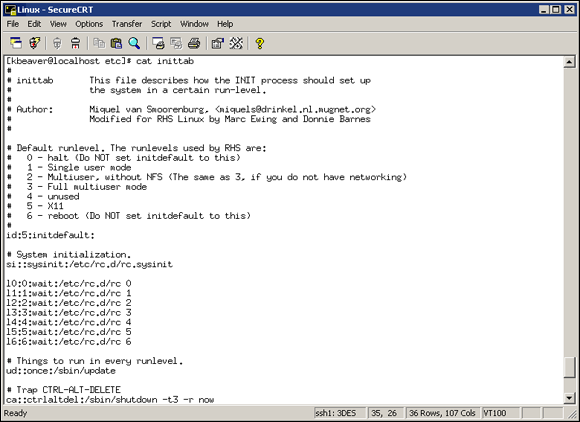
FIGURE 13-9: /etc/inittab showing the line that allows a Ctrl+Alt+Delete shutdown.
For Linux-based laptops, use disk-encryption software from WinMagic (https://www.winmagic.com) or Symantec EndPoint Encryption (https://www.symantec.com/products/endpoint-encryption). If you don't, when a laptop is lost or stolen, you could very well have a data breach on your hands, not to mention the state and federal compliance, and disclosure-law requirements that go along with it. Not good!
Performing General Security Tests
Assess critical and often-overlooked security issues on your Linux and macOS systems, such as the following:
- Misconfigurations or unauthorized entries in the shadow password files, which could provide covert system access.
- Password complexity requirements.
- Users equivalent to root.
- Suspicious automated tasks configured in cron, the script scheduler program.
- Signature checks on system binary files.
- Checks for rootkits.
- Network configuration, including measures to prevent packet spoofing and other DoS attacks.
- Permissions on system log files.
You can perform all these assessments manually or use an automated tool. Figure 13-10 shows the initiation of the Tiger security-auditing tool (www.nongnu.org/tiger), and Figure 13-11 shows a portion of the audit results. Talk about some great bang for no buck!

FIGURE 13-10: Running the Tiger security-auditing tool.

FIGURE 13-11: Partial output of the Tiger tool.
Alternatives to Tiger include Linux Security Auditing Tool (http://usat.sourceforge.net) and Bastille Unix (http://bastille-linux.sourceforge.net).
Patching
Ongoing patching is perhaps the best thing you can do to enhance and maintain the security of your Linux and macOS systems. Regardless of the Linux distribution you use, using a tool to assist in your patching efforts makes your job a lot easier.
Distribution updates
For Linux, the process is different in every distribution. You can use the following tools, based on your specific distribution:
-
Red Hat: The following tools update Red Hat Linux systems:
- RPM Packet Manager, which is the graphical user interface (GUI) application that runs in the Red Hat GUI desktop. It manages files with an
.rpmextension that Red Hat and other freeware and open-source developers use to package their programs. RPM Packet Manager was originally a Red Hatsystem but is now available for many versions of Linux. - up2date, a command-line, text-based tool that's included in Red Hat, Fedora, and CentOS.
- RPM Packet Manager, which is the graphical user interface (GUI) application that runs in the Red Hat GUI desktop. It manages files with an
- Debian: You can use the Debian package management system (dpkg) included with the OS to update Debian Linux systems.
- Slackware: You can use the Slackware Package Tool (pkgtool) included with the OS to update Slackware Linux systems.
- SUSE: SUSE Linux includes YaST2 software management.
For macOS, the updates are pushed to the computer locally, and unfortunately, it’s up to the user to install the updates by default.
Multiplatform update managers
Commercial patch-management tools have additional features, such as correlating patches with vulnerabilities and automatically deploying appropriate patches. Commercial tools that can help with Linux and macOS patch management include ManageEngine (https://www.manageengine.com/products/desktop-central/mac-management.html), GFI LanGuard (https://www.gfi.com/products-and-solutions/network-security-solutions/gfi-languard/specifications/patch-management-for-operating-systems), and KACE Systems Management Appliance (https://www.quest.com/products/kace-systems-management-appliance).
 If you don’t need to run a particular service, take the safe route: Turn it off! Just give people on the network ample warning of what you’re going to do in the event that someone needs the service for work.
If you don’t need to run a particular service, take the safe route: Turn it off! Just give people on the network ample warning of what you’re going to do in the event that someone needs the service for work.