Being able to launch a SCEP task remotely is great, but any anti-virus administrator worth his or her salt needs to be at least a little bit paranoid. Therefore, this recipe will walk you through the process of using SCEP's reporting capabilities to verify that your commands have been executed successfully. Something as vital to network security as malware event remediation should never be a "fire and forget" scenario.
In this recipe, we will be verifying that definition update command has been completed by using SCCM 2012's reporting function. It is important to remember that although SCCM 2012 is designed to have faster reporting capabilities than previous versions, nothing in SCCM is instant. So, if you have just followed the preceding recipe to force an unscheduled definition update, wait a few minutes before running a report.
In order to complete this recipe, you'll need to utilize an account that has at least the SCEP administrator's SCCM role assigned to it. You will also need access to your SCCM server's reporting capability.
Follow these steps:
- Log into your SCCM CAS server and launch your SCCM 2012 management console.
- Navigate to
Monitoring|Overview|Reporting|Reports|Endpoint Protectionand launch the Computer Malware Details report, as shown in the following screenshot: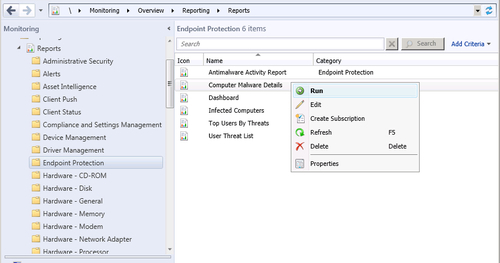
- The report will open with the bottom three fields empty. In the first field titled Device Filter, simply enter a
%sign and press Tab to move to the next field. - The Collection Name field should now become available. If you know the collection name from memory, simply type it in. Otherwise, click on the Values button and select a collection with your target system as a member from the list.
- The Computer Name field should now be available; you can either type the name of the target machine, or click on the Values button and select it from the list.
- Click on the View Report button to run the report.
- Once the report is complete, locate the Antimalware Definition Version field and compare it to the newest definition that is available from your Update Source, as shown in the following screenshot:
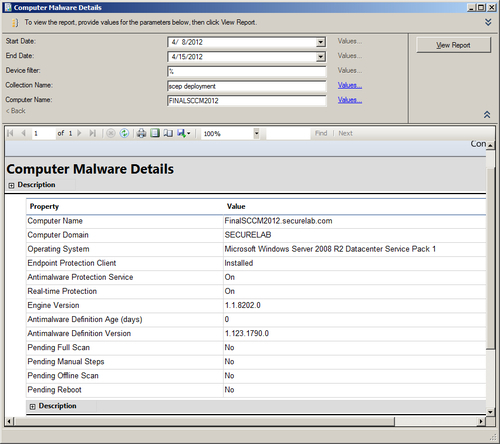
Although the name of the Computer Malware Details report may be a bit misleading, it is the best place to quickly check the definition status of a single client. It is essentially an amalgamation of the computer details report and the malware details report that were part of SCEPs predecessor, Forefront Endpoint Protection.
The process for confirming the definition version your update source currently possesses varies based on your chosen update source. If you are using SCCM as the primary update source, then I suggest following the first recipe in this chapter, Checking that your SCCM server has up-to-date SCEP definitions, to check the version number of the SCEP definition that your SCCM server is currently pushing out.
