 Secure Shell (SSH) Protocol
by J. Michael Stewart,
Denise Kinsey
Network Security, Firewalls, and VPNs, 3rd Edition
Secure Shell (SSH) Protocol
by J. Michael Stewart,
Denise Kinsey
Network Security, Firewalls, and VPNs, 3rd Edition
- Cover
- Title Page
- Copyright Page
- Dedication
- Brief Contents
- Contents
- Preface
- Acknowledgments
- About the Authors
- CHAPTER 1 Fundamentals of Network Security
- What Is Network Security?
- What Are You Trying to Protect?
- Goals of Network Security
- How Can You Measure the Success of Network Security?
- Why Are Written Network Security Policies Important?
- Who Is Responsible for Network Security?
- Enhancing the Security of Wired Versus Wireless LAN Infrastructures
- Internal and External Network Issues
- Common Network Security Components Used to Mitigate Threats
- TCP/IP Basics
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 1 ASSESSMENT
- CHAPTER 2 Network Security Threats
- Hackers and Their Motivation
- Favorite Targets of Hackers
- Threats from Internal Personnel and External Entities
- The Hacking Process
- Common IT Infrastructure Threats
- Malicious Code (Malware)
- Fast Growth and Overuse
- Wireless Versus Wired
- Eavesdropping
- Hijack and Replay Attacks
- Insertion Attacks
- Fragmentation Attacks
- Buffer Overflows
- Session Hijacking, Spoofing, and Man-in-the-Middle Attacks
- Covert Channels
- Network and Resource Availability Threats
- Hacker Tools
- Social Engineering
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 2 ASSESSMENT
- CHAPTER 3 Common Network Topologies and Infrastructures
- What Is a Network Topology?
- Types of Network Devices
- What Differentiates Logical and Physical Topologies?
- Differences Between Internet Protocol Version 4 (IPv4) and Internet Protocol Version 6 (IPv6)
- Examples of Network Infrastructures and Related Security Concerns
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 3 ASSESSMENT
- CHAPTER 4 Network Design Considerations
- Network Design and Defense in Depth
- Protocols
- Common Types of Addressing
- Controlling Communication Pathways
- Intrusion Detection Systems and Intrusion Prevention Systems
- Hardening Systems
- Equipment Selection
- Authentication, Authorization, and Accounting
- Communication Encryption
- Hosts: Local-Only or Remote and Mobile
- Redundancy
- Endpoint Security
- Risk Assessment and Management
- What Are Zones of Risk?
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 4 ASSESSMENT
- CHAPTER 5 Firewall Fundamentals
- What Is a Firewall?
- Why Do You Need a Firewall?
- How Firewalls Work and What Firewalls Do
- Types of Firewalls
- Individual and SOHO Firewall Options
- Uses for Host Software Firewalls
- Uses for Commercial Software Network Firewalls
- Uses for Hardware/Appliance Firewalls
- Next-Generation Firewalls
- What Are Virtual Firewalls?
- Dual-Homed and Triple-Homed Firewalls
- Ingress and Egress Filtering
- Types of Filtering
- Selecting the Right Firewall for Your Needs
- The Difference Between Buying and Building a Firewall
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 5 ASSESSMENT
- CHAPTER 6 Firewall Implementation
- Examining Your Network and Its Security Needs
- Proper Firewall Implementation Procedure
- Constructing, Configuring, and Managing a Firewall
- pfSense
- pfSense Requirements
- Planning a Firewall Implementation with pfSense
- Installing the pfSense Firewall
- Configuring a Firewall with pfSense
- Elements of Firewall Deployment
- Testing and Troubleshooting
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 6 ASSESSMENT
- CHAPTER 7 Firewall Deployment Considerations
- Common Security Strategies for Firewall Deployments
- Authentication, Authorization, and Accounting
- Placement of Network Hardware Firewalls
- Benefit and Purpose of Reverse Proxy
- Use and Benefit of Port Forwarding
- Considerations for Selecting a Bastion Host OS
- Monitoring and Logging
- Understanding and Interpreting Firewall Logs and Alerts
- Intrusion Detection Systems and Intrusion Prevention Systems
- Security Event and Information Management
- Evaluating Needs and Solutions in Designing Security
- What Happens When Security Gets in the Way of Doing Business?
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 7 ASSESSMENT
- CHAPTER 8 Configuring Firewalls
- Firewall Rules
- Composing Firewall Rules
- Ordering Firewall Rules
- What Should You Allow and What Should You Block?
- Essential Elements of a Firewall Policy
- Limitations of Firewalls
- Improving Performance
- The Downside of Encryption with Firewalls
- Firewall Enhancements
- Management Interfaces
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 8 ASSESSMENT
- CHAPTER 9 VPN Fundamentals
- What Is a Virtual Private Network?
- What Are the Benefits of Deploying a VPN?
- What Are the Limitations of a VPN?
- What Are Effective VPN Policies?
- VPN Deployment Models and Architecture
- Tunnel Versus Transport Mode
- The Relationship Between Encryption and VPNs
- What Is VPN Authentication?
- What Is VPN Authorization?
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 9 ASSESSMENT
- CHAPTER 10 VPN Management
- VPN Management Best Practices
- Build in Redundancy
- Choose the Right VPN Product for Your Environment
- Develop a VPN Policy
- Prohibit Split Tunneling
- Ensure Client Security
- Practice Vulnerability Management
- Use Multifactor Authentication
- Document Your Implementation Plan
- Monitor VPN Availability
- Perform Regular Reviews, Backups, and Updates
- Developing a VPN Policy
- Developing a VPN Deployment Plan
- VPN Threats and Exploits
- Commercial Versus Open-Source VPNs
- Differences Between Personal and Enterprise VPNs
- Balancing Anonymity and Privacy
- Protecting VPN Security to Support Availability
- The Importance of User Training
- VPN Troubleshooting
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 10 ASSESSMENT
- VPN Management Best Practices
- CHAPTER 11 VPN Technologies
- Differences Between Software and Hardware Solutions
- Differences Between Layer 2 and Layer 3 VPNs
- Internet Protocol Security (IPSec)
- Layer 2 Tunneling Protocol (L2TP)
- Secure Sockets Layer (SSL)/Transport Layer Security (TLS)
- Secure Shell (SSH) Protocol
- Establishing Performance and Stability for VPNs
- Using VPNs with Network Address Translation (NAT)
- Types of Virtualization
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 11 ASSESSMENT
- CHAPTER 12 VPN Implementation
- Operating System–Based VPNs
- VPN Appliances
- Remote Desktop Protocol
- Using Remote Control Tools
- Using Remote Access
- Remote Desktop Services
- Microsoft DirectAccess
- DMZ, Extranet, and Intranet VPN Solutions
- Internet Café VPNs
- Online Remote VPN Options
- The Tor Application
- Planning a VPN Implementation
- VPN Implementation Best Practices
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 12 ASSESSMENT
- CHAPTER 13 Firewall Security Management
- Best Practices for Firewall Management
- Security Measures in Addition to a Firewall
- Mitigating Firewall Threats and Exploits
- Concerns Related to Tunneling Through or Across a Firewall
- Testing Firewall Security
- Important Tools for Managing and Monitoring a Firewall
- Troubleshooting Firewalls
- Detecting Firewall Threats and Responding to Incidents
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 13 ASSESSMENT
- CHAPTER 14 Best Practices for Network Security Management
- Essentials of Network Security Management
- Network Security Management Tools
- Limiting Network Access and Implementing Encryption
- Physical Security
- Techniques for Preventing and Deterring Incidents
- Incident Response
- Fail-Secure, Fail-Open, and Fail-Close Options
- Network Security Assessments and Testing
- Change Management
- Compliance Auditing
- Network Security Troubleshooting
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 14 ASSESSMENT
- CHAPTER 15 Emerging Technology and Regulatory Considerations
- What the Future Holds for Network Security, Firewalls, and VPNs
- Resource Sites for Network Security, Firewalls, and VPNs
- Tools for Network Security, Firewalls, and VPNs
- The Vanishing Network Perimeter
- Potential Uses of Security Technologies
- Regulations and Compliance
- Specialized Firewalls Available
- Emerging Network Security Technologies
- CHAPTER SUMMARY
- KEY CONCEPTS AND TERMS
- CHAPTER 15 ASSESSMENT
- APPENDIX A Answer Key
- APPENDIX B Standard Acronyms
- Glossary of Key Terms
- References
- Index
Secure Shell (SSH) Protocol
The Secure Shell (SSH) protocol is a method for secure remote login and other secure network services over a public network such as the Internet. SSH services a number of applications across multiple platforms including UNIX, Windows, Mac, and Linux.
You can use SSH:
- For login to a shell on a remote host, replacing the need for telnet and rlogin (see FIGURE 11-3 for an example of an application that uses SSH for this application)
- For executing a single command on a remote host, replacing the need for rsh
- For file transfers to a remote host
- In combination with rsync to back up, copy, and mirror files securely
- In conjunction with the OpenSSH server and client to create a full VPN connection
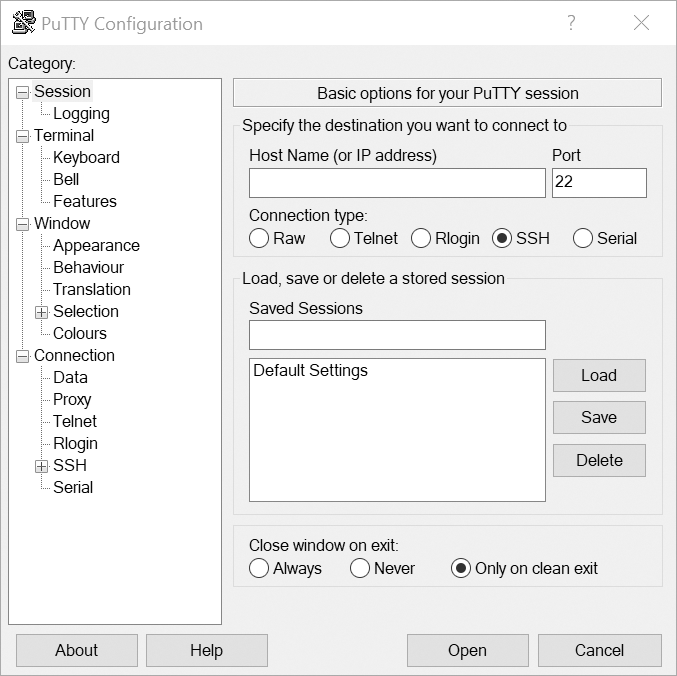
FIGURE 11-3 PuTTY is an application, providing terminal emulation, that leverages SSH to provide secure connections to hosts.
Courtesy of PuTTY.
The SSH protocol consists of three major components:
- TLS provides server authentication, confidentiality, and integrity with perfect forward secrecy (use of an independent session key for every web session a user starts in order to protect data)
- User Authentication Protocol (UAP), which authenticates the client to the server
- Connection Protocol, which multiplexes the encrypted tunnel into several logical channels
For more information on SSH, see http://tools.ietf.org/html/rfc4251.
-
No Comment
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.