Using the set lsnrctl command listener, we may dynamically change and override parameters. An attacker may use this capability for his own advantage by launching a series of DoS attacks against the database. The simplest DoS attack example is to simply stop the listener. Other DoS attacks can be produced by setting the listener trace (for example set listener trace to overwrite system01.dbf - set trc_file '/u01/HACKDB/system01.dbf')or log files to overwrite data files or redo logs, or they can be used to generate scripts in a desired location that may be used later.
- The format of parameter is
ADMIN_RESTRICTION_listener_name. In our case we will disable the fly administration of the listener namedLISTENER. Open$ORACLE_HOME/network/admin/listener.oraand enableADMIN_RESTRICTION_LISTENERas follows:ADMIN_RESTRICTION_LISTENER=ON - Reload the listener configuration as follows:
[oracle@nodeorcl1 ~]$ lsnrctl reload ............................................................................................................................. The command completed successfully [oracle@nodeorcl1 ~]$
In this example we used a scenario involving access to the Oracle account. By having permissions to modify listener.ora the attacker could also deactivate the listener protection. Therefore it should be highly recommended that listener security should also be correlated with an IDS system, as Tripwire presented in Chapter 1, Operating System Security, to trace any modification in the configuration files. You should also take into consideration to lock out the listener.ora by turning it into an immutable file. To see how to turn a file to immutable, refer to Using immutable files to prevent modification recipe in Chapter 1, Operating System Security.
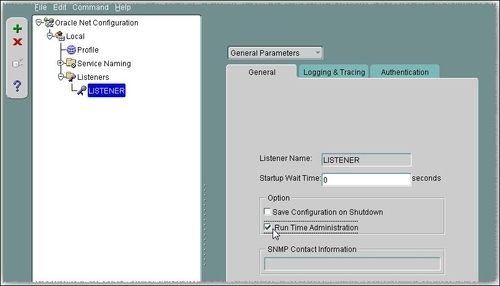
To set the ADMIN_RESTRICTION parameter using Network Manager (netmgr), navigate to LISTENER in the left-hand side pane and in the list box go to General Parameters. In the General tab check the Run Time Administration checkbox. Navigate to File and Save Network Configuration and reload the configuration.