1
BASICS OF SECURITY AND CRYPTOGRAPHY
AL-SAKIB KHAN PATHAN
Contents
1.1 The Perimeter of Cryptography in Practice
1.2 Things That Cryptographic Technologies Cannot Do
Keywords
Asymmetri
Cipher
Cryptography
Cryptology
Key
Plaintext
Private
Public
Security
Symmetric
To begin with, the purpose of this book is not to delve into the history of cryptography or to analyze the debate on the first occurrence of the technique in communications technologies. Instead, we aim to clarify various basic terminologies to give lucid understanding of the subject matter. Throughout the book, we will see various approaches to utilizing cryptographic techniques along with practical codes; however, the intent of this first chapter is to set the basics for the rest of the content.
The formal definition of cryptography could be noted in various ways; however, one is enough if that sums up all the associated meanings. Cryptography is basically the science that employs mathematical logic to keep the information secure (a formal definition is mentioned later in this chapter for quick reference). It enables someone to securely store sensitive information or transmit information securely through in secure networks to keep it from being hacked, masqueraded, or altered. The history of cryptography starts from the ancient era when it was practiced by secret societies or by troops in battlefields. The necessity of such an approach increased with time. In the current information era, there is indeed no time at which information security is not necessary, and hence cryptography stands with strength among various essential technologies. From military to civilian or from government to individual, information security is tremendously necessary. Consequently, several algorithms are proposed, and they are implemented with various hardware. The basic idea of a cryptographic algorithm is to scramble information in such a way that illegitimate entities cannot unearth the concealed information. Cryptographic algorithms are also used to preserve the integrity of a message.
There are various terminologies/words or set of words that are often associated with the fields of cryptography. Here, let us learn the basic definitions of the major terminologies that may be frequently used in the relevant fields and within this book.
Plaintext: This is the information that a sender wants to transmit to a receiver. A synonym of this is cleartext.
Encryption: Encryption is the process of encoding messages (or information) in such a way that eavesdroppers or hackers cannot read it, but authorized parties can. In an encryption scheme, the message or information (i.e., plaintext) is encrypted using an encryption algorithm, turning it into an unreadable ciphertext.
Ciphertext: Ciphertext (sometimes spelled cyphertext) is the result of encryption performed on plaintext using an algorithm, called a cipher.
Cipher: A cipher (sometimes spelled cypher) is an algorithm for performing encryption or decryption—a series of well-defined steps that can be followed as a procedure. A relatively less common term is encipherment. A cipher is also called a cryptoalgorithm.
Decryption: This is the process of decoding the encrypted text (i.e., ciphertext) and getting it back in the plaintext format.
Cryptographic key: Generally, a key or a set of keys is involved in encrypting a message. An identical key or a set of identical keys is used by the legitimate party to decrypt the message. A key is a piece of information (or a parameter) that determines the functional output of a cryptographic algorithm or cipher. Sometimes key means just some steps or rules to follow to twist the plaintext before transmitting it via a public medium (i.e., to generate ciphertext).
Stream cipher: A stream cipher is a method of encrypting text (to produce ciphertext) in which a cryptographic key and algorithm are applied to each binary digit in a data stream, one bit at a time. This method is not much used in modern cryptography. A typical operational flow diagram of stream cipher is shown in Figure 1.1.
Block cipher: A block cipher is a method of encrypting text (to produce ciphertext) in which a cryptographic key and algorithm are applied to a block of data (for example, 64 contiguous bits) at once as a group rather than one bit at a time. A sample diagram for a block cipher operation is shown in Figure 1.2. The feedback mechanism shown with a dotted line is optional but may be used to strengthen the process. A stronger mode is cipher feedback (CFB), which combines the plain block with the previous cipher block before encrypting it.
Cryptology: Cryptology is the general area of mathematics, such as number theory, and the application of formulas and algorithms, that underpin cryptography and cryptanalysis.
Cryptography: Cryptography and cryptology are often used as synonyms. However, a better understanding is that cryptology is the umbrella term under which comes cryptography and cryptanalysis. Cryptography is the science of information security. Cryptography includes techniques such as micro-dots, merging words with images, and other ways of hiding information in storage or transit. In today’s computer-centric world, cryptography is most of the time associated with scrambling plaintext into ciphertext, and then back again (i.e., decryption). Individuals who practice this field are known as cryptographers.
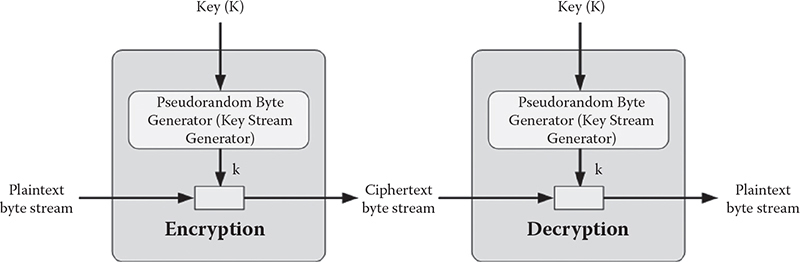
Figure 1.1 Operational diagram for a stream cipher.
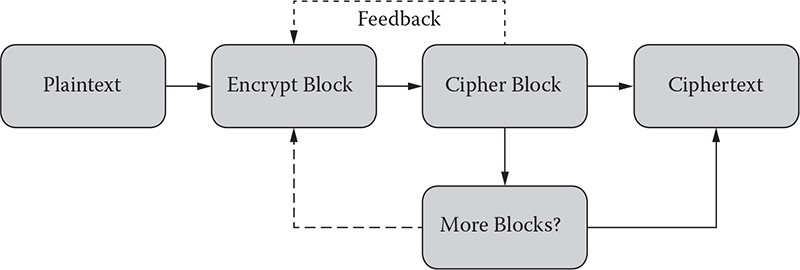
Figure 1.2 Sample operational diagram of a block cipher.
Cryptanalysis: Cryptanalysis refers to the study of ciphers, ciphertext, or cryptosystems (that is, secret code systems) with the goal of finding weaknesses in these that would permit retrieval of the plaintext from the ciphertext, without necessarily knowing the key or the algorithm used for that. This is also known as breaking the cipher, ciphertext, or cryptosystem.
Cryptosystem: This is the shortened version of cryptographic system. A cryptosystem is a pair of algorithms that take a key and convert plaintext to ciphertext and back.
Symmetric cryptography: Symmetric cryptography (or symmetric key encryption) is a class of algorithms for cryptography that use the same cryptographic keys for both encryption of plaintext and decryption of ciphertext. Figure 1.3 shows the overview of the steps in symmetric cryptography.
Symmetric key ciphers are valuable because
• It is relatively inexpensive to produce a strong key for these types of ciphers.
• The keys tend to be much smaller in size for the level of protection they afford.
• The algorithms are relatively inexpensive to process.
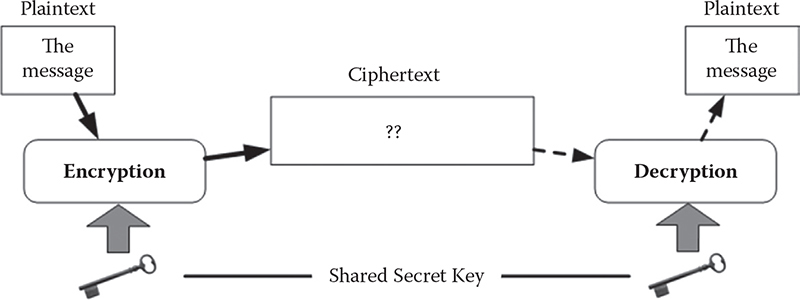
Figure 1.3 Operational model of symmetric cryptography.
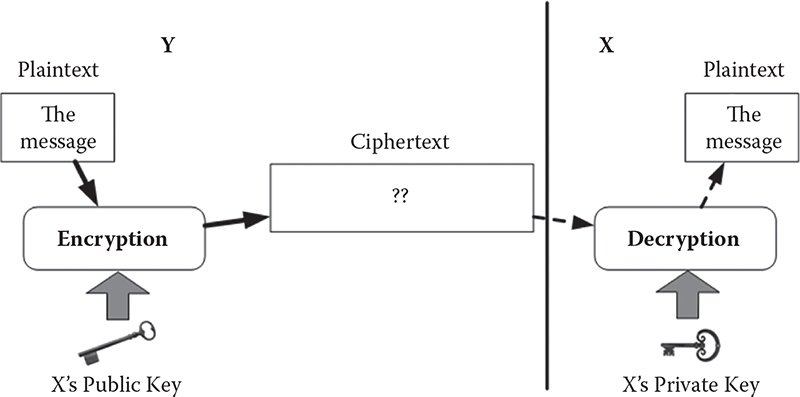
Figure 1.4 Operational model of asymmetric key cryptography or public-key cryptography. The public key and the private key of user X are mathematically linked.
Public-key cryptography or asymmetric cryptography: Public-key cryptography (PKC), also known as asymmetric cryptography, refers to a cryptographic algorithm that requires two separate keys, one of which is secret (or private) and the other public. Although different, the two parts of this key pair are mathematically linked. Figure 1.4 shows a pictorial view of PKC operations.
Public-key cryptography enables the following:
Encryption and decryption, which allow two communicating parties to disguise data that they send to each other. The sender encrypts, or scrambles, the data before sending them via a communication medium (or such). The receiver decrypts, or unscrambles, the data after receiving them. While in transit, the encrypted data are not understood by an intruder (or illegitimate third party).
Nonrepudiation (formally defined later), which prevents:
– The sender of the data from claiming, at a later date, that the data were never sent.
– The data from being altered.
Digital signature: A digital signature is an electronic signature that can be used to authenticate the identity of the sender of a message or the signer of a document, and possibly to ensure that the original content of the message or document that has been sent is unchanged. Digital signatures are usually easily transportable, cannot be imitated by someone else, and can be automatically timestamped.
Digital certificate: There is a difference between digital signature and digital certificate. A digital certificate provides a means of proving someone’s identity in electronic transactions. The function of it could be considered pretty much like a passport or driving license does in face-to-face interactions. For instance, a digital certificate can be an electronic “credit card” that establishes someone’s credentials when doing business or other transactions via the web. It is issued by a certification authority (CA). Typically, such a card contains the user’s name, a serial number, expiration dates, a copy of the certificate holder’s public key (used for encrypting messages and digital signatures), and the digital signature of the certificate-issuing authority so that a recipient can verify that the certificate is real.
Certification authority (CA): As understood from the definition above, a certification authority is an authority in a network that issues and manages security credentials and public keys for message encryption.
Now, let us talk about the general aspects and issues of security. Security, with its dimensions in fact, is a vast field of research. Information security basically tries to provide five types of functionalities:
Authentication
Authorization
Confidentiality or privacy
Integrity
Nonrepudiation
1.1 The Perimeter of Cryptography in Practice
Most of the time, cryptography is associated with the confidentiality (or privacy) of information only. However, except authorization, it can offer other four functions of security (i.e., authentication, confidentiality, integrity, and nonrepudiation). Let us now see what these terms mean in this context to talk about the functionalities that cryptography usually has or is supposed to provide.
Authentication: Authentication means the process of verification of the identity of the entities that communicate over a network. Without authentication, any user with network access can use readily available tools to forge originating Internet Protocol (IP) addresses and impersonate others. Therefore, cryptosystems use various mechanisms to authenticate both the originators and recipients of information. An example could be that a user needs to key in his or her login name and password for email accounts that are authenticated from the server.
Authorization: Authorization is a basic function of security that cryptography cannot provide. Authorization refers to the process of granting or denying access to a network resource or service. In other words, authorization means access control to any resource used for computer networks. Most of the computer security systems that we have today are based on a two-step mechanism. The first step is authentication, and the second step is authorization or access control, which allows the user to access various resources based on the user’s identity.
There is a clear difference between authentication and authorization. We see that if a user is authenticated, only then may he or she have access to any system. Again, an authenticated person may not be authorized to access everything in a system. Authentication is a relatively stronger aspect of security than authorization, as it comes before authorization. An example case could be as follows: An employee in a company needs an authentication code to identify him- or herself to the network server. There may be several levels of employees who have different access permissions to the resources kept in the server. All of the employees here need authentication to enter the server, but not everybody is authorized to use all the resources available in the system. If someone is authorized and accesses the protected resources, that person has already authenticated him- or herself correctly to the system. Someone who is not authorized to use the system (or server’s resources) but gets access illegally might have used tricks to deceive the system to authenticate him- or herself (which the server has accepted mistakenly). In any case, accessing of the protected materials needs authorization that covers authentication. Authentication, only by itself, may not have authorization associated with it for a particular network or system resource.
Confidentiality or privacy: It means the assurance that only authorized users can read or use confidential information. Without confidentiality, anyone with network access can use readily available tools to eavesdrop on network traffic and intercept valuable proprietary information. If privacy or confidentiality is not guaranteed, outsiders or intruders could steal the information that is stored in plaintext. Hence, cryptosystems use different techniques and mechanisms to ensure information confidentiality. When cryptographic keys are used on plaintext to create ciphertext, privacy is assigned to the information.
Integrity: Integrity is the security aspect that confirms that the original contents of information have not been altered or corrupted. If integrity is not ensured, someone might alter information or information might become corrupted, and the alteration could be sometimes undetected. This is the reason why many cryptosystems use techniques and mechanisms to verify the integrity of information. For example, an intruder might covertly alter a file, but change the unique digital thumbprint for the file, causing other users to detect the tampering by comparing the changed digital thumbprint to the digital thumbprint for the original contents.
Nonrepudiation: For information communication, assurance is needed that a party cannot falsely deny that a part of the actual communication occurred. Nonrepudiation makes sure that each party is liable for its sent message. If nonrepudiation is not ensured, someone can communicate and then later either falsely deny the communication entirely or claim that it occurred at a different time, or even deny receiving any piece of information. Hence, this aspect ensures accountability of each entity taking part in any communication event.
Now, the question is: How can we ensure nonrepudiation? To provide nonrepudiation, systems must provide evidence of communications and transactions that should involve the identities or credentials of each party so that it is impossible to refute the evidence. For instance, someone might deny sending an email message, but the messaging system adds a timestamp and digitally signs the message with the message originator’s digital signature. As the message contains a timestamp and a unique signature, there is strong evidence to identify both the originator of the message and the date and time of origin. If the message originator later denies sending the message, the false claim is easily refuted. Likewise, to provide nonrepudiation for mail recipients, mail systems might generate mail receipts that are dated and signed by the recipients.
1.2 Things That Cryptographic Technologies Cannot Do
Cryptographic technologies cannot provide solutions to all security issues. We previously have learned that they cannot provide the authorization aspect of security—that process is basically the task of the system or network operating system. In general, cryptography-based security systems provide sufficient security when used properly within the capabilities and limitations of the cryptographic technology. However, such a technology only provides part of the overall security for any network and information. The overall strength of any security system depends on many factors, such as the suitability of the technology, adequate security procedures and processes, and how well people use the procedures, processes, and technology. To put it in another way, security depends on the appropriate protection mechanism of the weakest link in the entire security system.
A company may have all the best cryptographic technologies installed in its computers and systems; however, all these protection efforts would collapse if someone (perhaps an intruder or an employee) can easily walk into offices and obtain valuable proprietary information that has been printed out as plaintext hard copy. Hence, one must not simply rely on cryptography-based security technologies to overcome other weaknesses and flaws in the security systems.
For example, if someone transmits valuable information as ciphertext over communications networks to protect confidentiality but stores the information as plaintext on the sender or receiver computer, it’s still a vulnerable situation. Those computers must be protected to make sure the information is actually protected or kept confidential, possibly keeping the information in encrypted format as well—maybe with passwords to access the computer or folders or such. Also, the entire network must have strong firewalls and maintain those in secure facilities. The latter tasks are not of cryptography or cryptographic technologies. When building a secure system, we have to take into consideration a lot of issues of security, which are often dependent on the requirements and settings of the system.
