In this exercise, we will learn how to sniff data packets for a given wireless network. For the sake of simplicity, we will look at packets without any encryption.
Follow these instructions to get started:
- Switch on the access point we named
Wireless Lab. Let it remain configured to use no encryption. - We will first need to find the channel on which the
Wireless Labaccess point is running. To do this, open a terminal and runairodump-ng --bssid <mac> wlan0mon, where <mac> is the MAC address of our access point. Let the program run, and shortly you should see your access point shown on the screen along with the channel it is running on. - We can see from the preceding screenshot that our access point
Wireless Labis running on channel 11. Note that this may be different for your access point.In order to sniff data packets going to and from this access point, we need to lock our wireless card on the same channel, that is channel 11. To do this, run the
iwconfig wlan0mon channel 11command and then runiwconfig wlan0monto verify it. You should see theFrequency: 2.462 GHzvalue in the output. This corresponds to channel 11.
- Now fire up Wireshark and start sniffing on the
wlan0moninterface. After Wireshark has started sniffing the packets, apply a filter for thebssidof our access point as shown in the following screenshot usingwlan.bssid == <mac>in the filter area. Use the appropriate MAC address for your access point.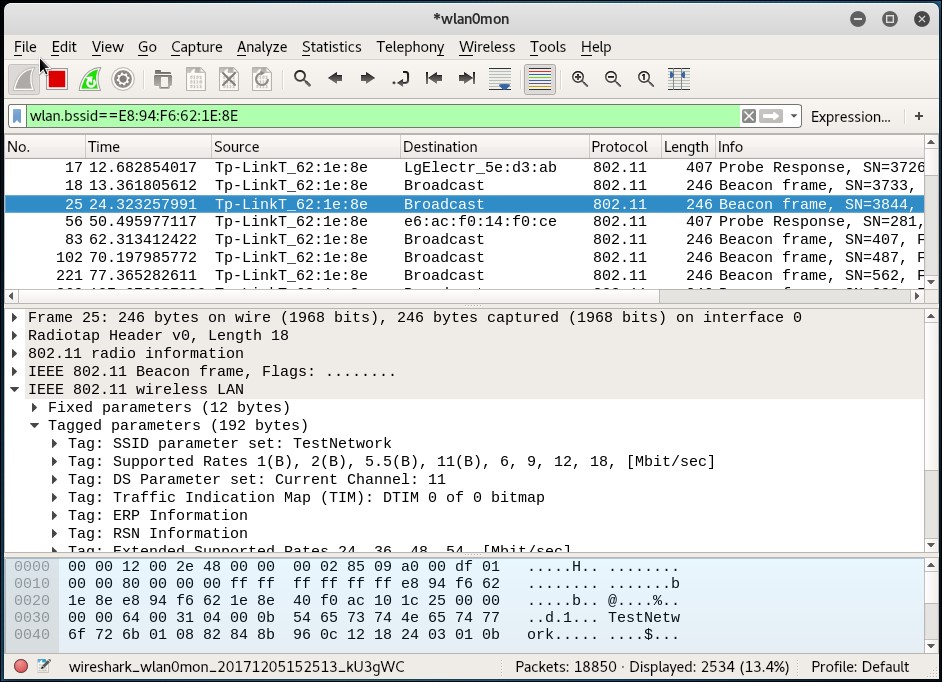
- In order to see the data packets for our access point, add the following to the filter
(wlan.bssid == <mac>) && (wlan.fc.type_subtype == 0x20). Open your browser on the client laptop and type the URL of the access point in the management interface. In my case, as we have seen in Chapter 1, Wireless Lab Setup, it ishttp://192.168.0.1. This will generate data packets that Wireshark will capture. - Packet sniffing allows us to analyze unencrypted data packets very easily. This is the reason why we need to use encryption in wireless.
We have just sniffed data packets over the air with Wireshark using various filters. As our access point is not using any encryption, we are able to see all the data in plain text. This is a major security issue as anyone within RF range of the access point can see all the packets if he uses a sniffer such as Wireshark.
Use Wireshark to analyze the data packets further. You will notice that a DHCP request is made by the client and, if a DHCP server is available, it responds with an address. Then you will find ARP packets and other protocol packets on the air. This is a nice and simple way to do passive host discovery on the wireless network. It is important to be able to see a packet trace and reconstruct how applications on the wireless host are communicating with the rest of the network. One of the interesting features Wireshark provides is the ability to follow a stream. This allows you to view multiple packets together, that are part of a TCP exchange, in the same connection.
Also, try logging into www.gmail.com or any other popular website and analyze the data traffic generated.
We will now see a demonstration of how to inject packets into a wireless network.
