Appendix J. Topics from Previous Editions
Cisco changes the exams, renaming the exams on occasion, and changing the exam numbers every time it changes the exam with a new blueprint, even with a few name changes over the years. As a result, the current CCNA 200-301 exam serves as the eighth separate version of CCNA in its 20-plus year history. At every change to the exams, we create new editions of the books to match the new exam.
We base the books’ contents on Cisco’s exam topics; that is, the book attempts to cover the topics Cisco lists as exam topics. However, the book authoring process does create some challenges, particularly with the balance of what to include in the books and what to leave out.
For instance, when comparing a new exam to the old, I found Cisco had removed some topics—and I might want to keep the content in the book. There are a few reasons why. Sometimes I just expect that some readers will still want to read about that technology. Also, more than a few schools use these books as textbooks, and keeping some of the older-but-still-relevant topics can be a help. And keeping the old material available on each book’s companion website takes only a little extra work, so we do just that.
Some of the older topics that I choose to keep on the companion website are small, so I collect them into this appendix. Other topics happen to have been an entire chapter in a previous edition of the books, so we include those topics each as a separate appendix. Regardless, the material exists here in this appendix, and in the appendices that follow, for your use if you have a need. But do not feel like you have to read this appendix for the current exam.
The topics in this appendix are as follows:
IPv4 Address Types
Bandwidth and Clock Rate on Serial Interfaces
Using traceroute to Isolate the Problem to Two Routers
Troubleshooting Static IPv6 Routes
Default Routes with SLAAC on Router Interfaces
Note
The content under the heading “IPv4 Address Types” was most recently published for the 100-105 Exam in 2016, in Chapter 20 of the Cisco CCNA ICND1 100-105 Official Cert Guide.
IPv4 Address Types
The IPv4 address space includes three major categories of addresses: unicast, broadcast, and multicast. For the current exam, Cisco lists one exam topic that asks you to compare and contrast these address types. To help you make those comparisons, this section explains multicast addressing, while pulling together the key ideas about unicast and broadcast IP addresses that have already been introduced, to pull the ideas together.
You may be wondering why this topic about IPv4 address types sits at the end of a chapter about DHCP and IP networking on hosts. Honestly, I could have put this topic in several chapters. The main reason it is here is that you have already seen the IP broadcast addresses in action, including the 255.255.255.255 local broadcast as shown in this chapter.
Review of Unicast (Class A, B, and C) IP Addresses
Unicast IP addresses are those Class A, B, and C IP addresses assigned to hosts, router interfaces, and other networking devices. Because most discussions about IP addressing refer to unicast IP addresses, most of us just refer to them as IP addresses, and leave out the word unicast.
Just to be complete and define the concept, unicast addresses identify one interface on one device to IP. Just like your postal address gives the post office an address to use to send letters to your one specific house or apartment, a unicast IP address gives the IP network an address to use to send packets to one specific host. However, with IP, instead of addressing the device, unicast addresses identify individual interfaces. For example:
A router with four LAN interfaces, and two WAN interfaces, has six unicast addresses, each in a different subnet, one for each interface.
A PC with both an Ethernet network interface card (NIC) and a wireless NIC would have two unicast IPv4 addresses, one for each interface.
IP Broadcast Addresses
Broadcast IPv4 addresses give IP a way to send one packet that the network delivers to multiple hosts. IPv4 defines several types of broadcast addresses, with each type being used to reach a different set of hosts. These different broadcast IP addresses give different overhead protocols like DHCP the ability to efficiently reach all hosts in a specific part of the network. The following list reviews the three IP broadcast address types:

Local broadcast address: 255.255.255.255. Used to send a packet on a local subnet, knowing that routers will not forward the packet as is. Also called a limited broadcast.
Subnet broadcast address: One reserved address for each subnet, namely the numerically highest number in the subnet, as discussed in Chapter 13, “Analyzing Subnet Masks.” A packet sent to a subnet broadcast address can be routed to the router connected to that subnet, and then sent as a data-link broadcast to all hosts in that one subnet. Also called an all-hosts broadcast to emphasize that all hosts in a subnet are reached, and also called a directed broadcast.
Network broadcast address: One reserved address for each classful network, namely the numerically highest number in the network. Used to send one packet to all hosts in that one network. Also called an all-subnets broadcast, referring to the fact that the packet reaches all subnets in a network.
This chapter has already shown how a local broadcast works, sending the message over the same subnet in which it was first transmitted, but no further. However, the other two types are a little more interesting.
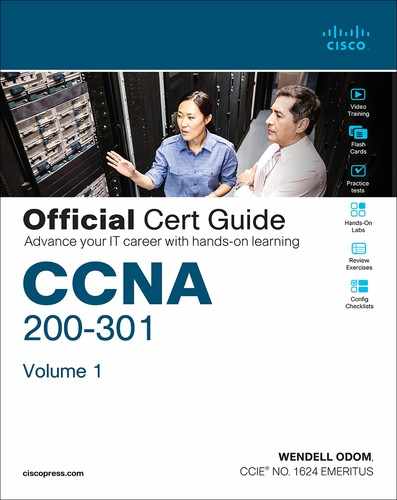
Subnet and network broadcasts provide a way to send packets to all hosts in a subnet or network (respectively) while reducing waste. For instance, with a subnet broadcast, routers forward the packet just like any other IP packet going to that subnet. When that packet arrives at the router connected to that subnet, the last router then encapsulates the packet in a LAN broadcast, so that all hosts receive a copy. Figure J-1 shows the idea.
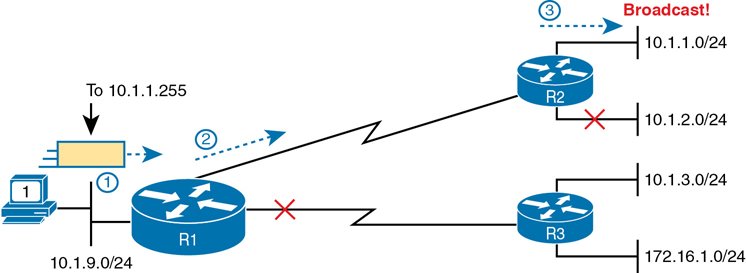
Figure J-1 Example of a Subnet Broadcast to 10.1.1.255
The figure shows two key points. R1 does not flood or broadcast the frame to all other routers, instead routing it to the next router (R2 in this case) so that the packet reaches subnet 10.1.1.0/24. R2, connected to subnet 10.1.1.0/24, forwards the packet onto the LAN, but encapsulates the packet in an Ethernet broadcast frame, so that it reaches all hosts in the subnet.
The figure shows the intended use of the subnet broadcast address; however, it presents a security issue today. Many attacks start with a ping to subnet broadcast addresses, hoping to get many hosts to reply. Cisco changed the IOS default many years ago to disable the forwarding of subnet broadcasts onto a connected subnet (that is, it disables Step 3 in Figure J-1). That default setting is based on the no ip directed-broadcast interface subcommand.
A network broadcast packet (a packet with a network broadcast address as the destination) works in a similar way. To reach all subnets, however, the routers create copies of the packet and flood it so it reaches all subnets inside the classful network. On any LAN interfaces, the packet is forwarded in a LAN broadcast, just as shown in Step 3 of Figure J-1.
IPv4 Multicast Addresses (Class D Addresses)
Multicast IP addresses and the related protocols help solve a similar problem as compared to broadcast addresses, but mainly for applications, and without the same security issues experienced by broadcast addresses. To see how it works, consider this example. A video application may be designed to show live video feeds. If 10 people at the same remote site in the same subnet want to watch the same video at the same time, the application could be designed so that the application sent the same video data 10 times, once to each client in the same subnet. An application designed to use Class D multicast addresses could send 1 packet, which the routers would route across the WAN, and then deliver a copy to all 10 hosts in the destination subnet.
When using multicast, all the hosts still use their individual unicast IP address for their normal traffic, while also using the same multicast IPv4 address for the multicast application. Any server or client that happens to use an application designed to take advantage of IP multicast then also uses the Class D multicast addresses that the application chooses to use. You can think of a Class D address more as a multicast group—in fact, it is often called that—because hosts join the group so that they can receive the packets sent by the multicast application.
Class D addresses begin with a first octet of between 224 and 239, with some ranges reserved for various purposes. Much of the Class D address space is set aside for a company to deploy one of these multicast applications, and then pick an address from the Class D range, and configure it to be used by a multicast application.
As an example, imagine the video application uses Class D address 226.1.1.1. Figure J-2 illustrates the process by which the application at the server on the left sends one multicast packet with destination address 226.1.1.1. Note that for this process to work, the hosts with * beside them registered with their local routers to notify the routers that the host wants to receive packets destined to multicast address 226.1.1.1. When the action in this figure begins, the routers collectively know which subnets have hosts that want a copy of multicasts sent to 226.1.1.1, and which subnets do not.
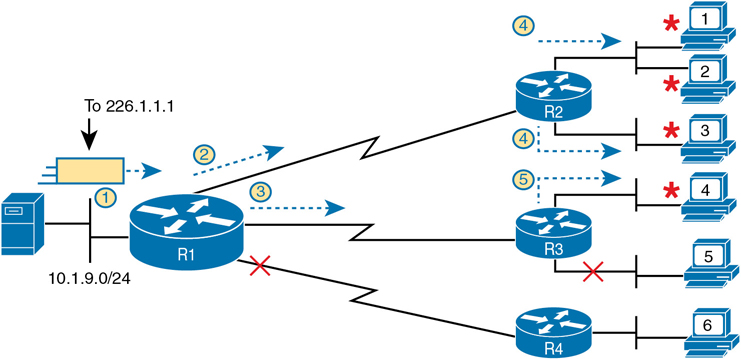
Figure J-2 Example of a Multicast Packet Flow for Three Registered Hosts
Following the steps in the figure:
The server on the left generates and sends a multicast packet.
Router R1 replicates the packet to send a copy to both R2…
…and to R3. R1 does not replicate and send a copy to R4, because there are no hosts near R4 listening for packets sent to 226.1.1.1.
R2 processes the multicast packet received from R1, and because of the earlier host registration process, R2 knows that at least one host off both its LAN interfaces are listening for packets sent to 226.1.1.1. R2 therefore forwards a copy of the packet out each of its LAN interfaces.
R3 receives the multicast packet from R1, and uses the same kind of logic as R2. However, R3 knows from the earlier host registration process that only one of its LAN interfaces connects to a subnet with hosts listening for packets sent to 226.1.1.1, so R3 forwards a copy of the packet out that one interface only.
As you can see from this example, the server sent one packet and the routers replicated the packet so it reached all the correct locations in the network.
As another comparison between unicast and multicast addresses, note that multicast addresses may be used as destination IP addresses only, whereas unicast addresses may be used as both the destination and source address. For instance, consider the packets in the example shown in Figure J-2. All those packets flow from one host, so the packet uses a unicast IP address of that host’s unicast IP address.
Finally, to complete one more comparison between unicast IP addressing and multicast IP addressing, think about that last hop router in the example shown in Figure J-1. If a router such as R2 or R3 had forwarded a unicast IP packet, the router would look in its ARP cache to find the unicast IP address for the destination in that connected subnets, and the associated unicast MAC address. That will not work when forwarding a multicast packet with a multicast (Class D) destination IP address.
To encapsulate a multicast IP packet over an Ethernet LAN, IP multicast calculates the destination MAC address with a simple process. The process copies the last 23 bits of the IP address behind a reserved 25-bit prefix to form the 48-bit destination MAC address. The resulting MAC address, called a multicast MAC address, begins with hex 01005E. So, the multicast IP packet, encapsulated in the multicast Ethernet frame, is forwarded out the router interface onto the LAN. At that point, the switches take one of the following approaches to forwarding the frame so that all hosts who want a copy of the frame get a copy:
Flood the multicast frame as if it were a broadcast
Use other Ethernet multicast features that flood the frame only to those same devices that registered to receive a copy
If you feel like these few pages probably left out some detail; indeed, several books have been written about IP multicast all to itself. The topic is indeed large. For this book’s purposes, know the main comparison points with unicast addressing. Multicast addressing gives applications that need to communicate the same data at the same time to multiple hosts a much more efficient way to do that. If the application is written to make use of IP multicast, the application can consume much less traffic in the network, as compared to using unicast IP addresses and sending every host a copy of the packet.
Comparing and Contrasting IP Address Types
The last few pages reviewed unicast and broadcast addresses, and explained the core concepts behind IP multicast addresses. Table J-1 summarizes the key comparison points mentioned throughout this section for convenient study.
Table J-1 Comparisons of Unicast, Broadcast, and Multicast IP Addresses
|
Unicast |
Broadcast |
Multicast |
|---|---|---|---|
Primarily used for data sent by the most common user apps (web, email, chat, and so on) |
Yes |
No |
No |
Assigned to hosts with DHCP |
Yes |
No |
No |
Uses Class A, B, and C addresses |
Yes |
No |
No |
Primarily used by overhead protocols (DHCP, ARP) to send one message to more than one device |
No |
Yes |
No |
Used as destination IP address only |
No |
Yes |
Yes |
Primarily used by applications that send the same data at the same time to multiple clients |
No |
No |
Yes |
Uses Class D addresses |
No |
No |
Yes |
Note
The content under the heading “Bandwidth and Clock Rate on Serial Interfaces” was most recently published for the 100-105 Exam in 2016, in Chapter 17 of the CCENT/CCNA ICND1 100-105 Official Cert Guide.
Bandwidth and Clock Rate on Serial Interfaces
WAN serial links can run at a wide variety of speeds. To deal with the wide range of speeds, routers physically slave themselves to the speed as dictated by the CSU/DSU through a process called clocking. As a result, routers can use serial links without the need for additional configuration or autonegotiation to sense the serial link’s speed. The CSU/DSU knows the speed, the CSU/DSU sends clock pulses over the cable to the router, and the router reacts to the clocking signal.
To build a serial link in a home lab, the routers can use serial interface cards that normally use an external CSU/DSU, and make a serial link, without requiring the expense of two CSU/DSUs. Figure J-3 shows the concept. To make it work, the link uses two serial cables—one a DTE cable and the other a DCE cable—which swap the transmit and receive pair on the cables.
Figure J-3 Serial Link in Lab
Using the correct cabling works, as long as you add one command: the clock rate interface subcommand. This command tells that router the speed at which to transmit bits on a serial link like the one shown in Figure J-3. The clock rate command is not needed on real serial links, because the CSU/DSU provides the clocking. When you create a serial link in the lab using cables, without any real CSU/DSUs on the link, the router with the DCE cable must supply that clocking function, and the clock rate command tells the router to provide it.
Note
Newer router IOS versions automatically add a default clock rate 2000000 command on serial interfaces that have a DCE cable connected to them. While helpful, this speed might be too high for some types of back-to-back serial cables, so consider using a lower speed in lab.
Example J-1 shows the configuration of the clock rate command. The end of the example verifies that this router can use the clock rate command with the show controllers command. This command confirms that R1 has a V.35 DCE cable connected.
Example J-1 Router R1 Configuration with the clock rate Command
R1# show running-config ! lines omitted for brevity interface Serial0/0/0 ip address 172.16.4.1 255.255.255.0 clock rate 2000000 ! interface Serial0/0/1 ip address 172.16.5.1 255.255.255.0 clock rate 128000 ! lines omitted for brevity R1# show controllers serial 0/0/1 Interface Serial0 Hardware is PowerQUICC MPC860 DCE V.35, clock rate 128000 idb at 0x8169BB20, driver data structure at 0x816A35E4 ! Lines omitted for brevity
Note
The clock rate command does not allow just any speed to be configured. However, the list of speeds does vary from router to router.
Some people confuse the router bandwidth command with the clock rate command. The clock rate command sets the actual Layer 1 speed used on the link, if no CSU/DSU is used, as just described. Conversely, every router interface has a bandwidth setting, either by default or configured. The bandwidth of the interface is the documented speed of the interface, which does not have to match the actual Layer 1 speed used on the interface.
That bandwidth setting does not impact how fast the interface transmits data. Instead, routers use the interface bandwidth setting as both documentation and as input to some other processes. For instance, the Open Shortest Path First (OSPF) and Enhanced Interior Gateway Routing Protocol (EIGRP) routing protocols base their routing protocol metrics on the bandwidth by default.
Example J-2 highlights the bandwidth setting on Router R1’s S0/0/1 interface, as configured in the previous example. In that previous example, the clock rate 128000 command sets the clock rate to 128 kbps, but it leaves the bandwidth command unset. As a result, IOS uses the default serial bandwidth setting of 1544, which means 1544 kbps—which is the speed of a T1 serial link.
Example J-2 Router Bandwidth Settings
R1# show interfaces s0/0/1
Serial0/0/1 is up, line protocol is up
Hardware is WIC MBRD Serial
Description: link to R3
Internet address is 10.1.13.1/24
MTU 1500 bytes, BW 1544 Kbit/sec, DLY 20000 usec,
reliability 255/255, txload 1/255, rxload 1/255
Encapsulation HDLC, loopback not set
The common mistake people make is to know about clock rate, but mistakenly think that the bandwidth setting is just another term for “clock rate.” It is not. Follow these rules to find these two interface settings:
To see the clock rate, look for the clock rate interface subcommand in the configuration, or use the show controllers serial number command (as shown in Example J-1.)
To see the bandwidth setting on an interface, look for the bandwidth interface subcommand in the configuration, or use the show interfaces [type number] command (as shown in Example J-2).
Note that using default bandwidth settings on most router interfaces makes sense, with the exception of serial interfaces. IOS defaults to a bandwidth of 1544 (meaning 1544 kbps, or 1.544 Mbps) for serial interfaces, regardless of the speed dictated by the provider or by a clock rate command in the lab. Most engineers set the bandwidth to match the actual speed, for example, using the bandwidth 128 interface subcommand on a link running at 128 kbps. On Ethernet 10/100 or 10/100/1000 interfaces, the router knows the speed used, and dynamically sets the Ethernet interface’s bandwidth to match.
Note
The content under the heading “Using traceroute to Isolate the Problem to Two Routers” was most recently published for the 100-105 Exam in 2016, in Chapter 23 of the Cisco CCNA ICND1 100-105 Official Cert Guide.
Using traceroute to Isolate the Problem to Two Routers
One of the best features of the traceroute command, as compared to ping, is that when it does not complete it gives an immediate clue as to where to look next. With ping, when the ping fails, the next step is usually to use more ping commands. With traceroute, it tells you what router to try to connect and look at the routes and in which direction.
Note
As a reminder, this book uses the term forward route for routes that send the packets sent by the ping or traceroute command, and reverse route for the packets sent back.
When a problem exists, a traceroute command results in a partial list of routers. Then the command either finishes with an incomplete list or it runs until the user must stop the command. In either case, the output does not list all routers in the end-to-end route, because of the underlying problem.
Note
In addition, the traceroute command may not finish even though the network has no problems. Routers and firewalls may filter the messages sent by the traceroute command, or the TTL Exceeded messages, which would prevent the display of portions or all or part of the path.
The last router listed in the output of a traceroute command’s output tells us where to look next to isolate the problem, as follows:
Connect to the CLI of the last router listed, to look at forward route issues.
Connect to the CLI of the next router that should have been listed, to look for reverse route issues.
To see why, consider an example based on the internetwork in Figure J-4. In this case, R1 uses an extended traceroute to host 5.5.5.5, with source IP address 1.1.1.1. This command’s output lists router 2.2.2.2, then 3.3.3.3, and then the command cannot complete.

Figure J-4 Messages That Cause the traceroute Command to List 2.2.2.2
First, Figure J-4 focuses on the first line of output: the line that lists first-hop router 2.2.2.2.
The figure shows the TTL=1 message at the top and the TTL Exceeded message back on the bottom. This first pair of messages in the figure must have worked, because without them, the traceroute command on R1 cannot have learned about a router with address 2.2.2.2. The first (top) message required R1 to have a route for 5.5.5.5, which sent the packets to R2 next. The TTL Exceeded message required that R2 have a route that matched address 1.1.1.1, to send the packets back to R1’s LAN IP address.
Next, Figure J-5 focuses on the messages that allow the second line of output on R1’s sample traceroute command: the line that correctly lists 3.3.3.3 as the next router in the route.

Figure J-5 Messages That Cause the traceroute Command to List 3.3.3.3
Following the same logic, the traceroute output lists 3.3.3.3 because the messages in Figure J-5 must have worked. For these messages to flow, the routes listed in Figure J-4 must exist, plus new routes listed in 18-15. Specifically, the TTL=2 packet at the top requires R2 to have a route for 5.5.5.5, which sends the packets to R3 next. The TTL Exceeded message requires that R3 have a route that matches address 1.1.1.1, to send the packets back toward R1’s LAN IP address.
In this example, the traceroute 5.5.5.5 command does not list any routers beyond 2.2.2.2 and 3.3.3.3 However, based on the figures, it is clear that 4.4.4.4 should be the next IP address listed. To help isolate the problem further, why might the next messages—the message with TTL=3 and the response—fail?
Figure J-6 points out the routing issues that can cause this command to not be able to list 4.4.4.4 as the next router. First, R3 must have a forward route matching destination 5.5.5.5 and forwarding the packet to Router R4. The return message requires a reverse route matching destination 1.1.1.1 and forwarding the packet back to Router R3.
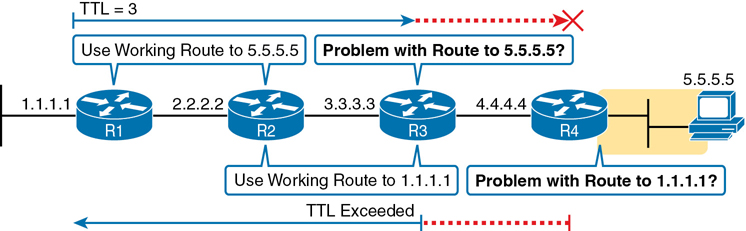
Figure J-6 Issues That Could Prevent traceroute from Listing 4.4.4.4
In conclusion, for this example, if a routing problem prevents the traceroute command from working, the problem exists in one of two places: the forward route to 5.5.5.5 on Router R3, or the reverse route to 1.1.1.1 on R4.
Note
The content under the heading “Troubleshooting Static IPv6 Routes” was most recently published in Chapter 32 of the Cisco CCNA ICND1 100-105 Official Cert Guide.
Troubleshooting Static IPv6 Routes
This last part of the chapter looks at troubleshooting IPv6 static routes, reviewing many of the same troubleshooting rules applied to IPv4 static routes, while focusing on the details specific to IPv6.
This topic breaks static route troubleshooting into two perspectives: the route is in the routing table but is incorrect and cases in which the route is not in the routing table.
Troubleshooting Incorrect Static Routes That Appear in the IPv6 Routing Table
A static route is only as good as the input typed into the ipv6 route command. IOS checks the syntax of the command, of course. However, IOS cannot tell if you choose the incorrect outgoing interface, incorrect next-hop address, or incorrect prefix/prefix-length in a static route. If the parameters pass the syntax checks, IOS places the ipv6 route command into the running-config file. Then, if no other problem exists (as discussed at the next heading), IOS puts the route into the IP routing table—even though the route may not work because of the poorly chosen parameters.
For instance, an exam question might show a figure with Router R1 having an address of 2001:1:1:1::1 and neighboring Router R2 with an address of 2001:1:1:1::2. If R1 lists a static route with the command ipv6 route 3333::/64 2001:1:1:1::1, the command would be accepted by IOS with correct syntax, but it would not be effective as a route. R1 cannot use its own IPv6 address as a next-hop address. IOS does not prevent the configuration of the command, however; it allows the command and adds the route to the IPv6 routing table, but the route cannot possibly forward packets correctly.
When you see an exam question that has static routes, and you see them in the output of show ipv6 route, remember that the routes may have incorrect parameters. Check for these types of mistakes:
Step 1. Prefix/Length: Does the ipv6 route command reference the correct subnet ID (prefix) and mask (prefix length)?
Step 2. If using a next-hop IPv6 address that is a link-local address:
A. Is the link-local address an address on the correct neighboring router? (It should be an address on another router on a shared link.)
B. Does the ipv6 route command also refer to the correct outgoing interface on the local router?
Step 3. If using a next-hop IPv6 address that is a global unicast or unique local address, is the address the correct unicast address of the neighboring router?
Step 4. If referencing an outgoing interface, does the ipv6 route command reference the interface on the local router (that is, the same router where the static route is configured)?
This troubleshooting checklist works through the various cases in which IOS would accept the configuration of the static IPv6 route, but the route would not work because of the incorrect parameters in context. It helps to see a few examples. Figure J-7 shows a sample network to use for the examples; all the examples focus on routes added to Router R1, for the subnet on the far right.
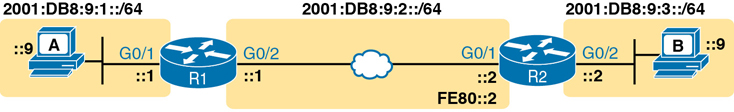
Figure J-7 Sample Topology for Incorrect IPv6 Route Examples
Example J-3 shows five ipv6 route commands. All have correct syntax, but all have one incorrect value; that is, the route will not work because of the types of problems in the troubleshooting checklist. Look for the short comment at the end of each configuration command to see why each is incorrect.
Example J-3 ipv6 route Commands with Correct Syntax but Incorrect Ideas
ipv6 route 2001:DB8:9:33::/64 2001:DB8:9:2::2 ! Step 1: Wrong prefix ipv6 route 2001:DB8:9:3::/64 G0/2 FE80::AAA9 ! Step 2A: Wrong neighbor link local ipv6 route 2001:DB8:9:3::/64 FE80::2 ! Step 2B: Missing outgoing interface ipv6 route 2001:DB8:9:3::/64 2001:DB8:9:2::1 ! Step 3: Wrong neighbor address ipv6 route 2001:DB8:9:3::/64 G0/1 FE80::2 ! Step 4: Wrong interface on R1
All these incorrect examples have correct syntax and would be added to R1’s IPv6 routing table if configured on R1. However, all have flaws. Working through the examples in order:
Step 1. The prefix (2001:DB8:9:33::) has a typo in the fourth quartet (33 instead of 3).
Step 2A. The figure shows R2’s G0/1 with link-local address FE80::2, but the command uses FE80::AAA9.
Step 2B. The command uses the correct link-local address on R2’s address on the common link (FE80::2 per the figure), but it omits the outgoing interface of R1’s G0/2 interface. (See the next example for more detail.)
Step 3. The figure shows the subnet in the center as 2001:DB8:9:2::/64, with R1 using the ::1 address and R2 using ::2. For the fourth command, R1’s command should use R2’s address 2001:DB8:9:2::2, but it uses R1’s own 2001:DB8:9:2::1 address instead.
Step 4. As a command on R1, the outgoing interface references R1’s own interfaces. R1’s G0/1 is the interface on the left, whereas R1 should use its G0/2 interface on the right when forwarding packets to subnet 2001:DB8:9:3::/64.
The key takeaway for this section is to know that a route in the IPv6 routing table may be incorrect due to poor choices for the parameters. The parameters should always include the neighboring router’s IPv6 addresses, but the local router’s interface type/number, and in all cases, the correct prefix/length. The fact that a route is in the IPv6 routing table, particularly a static route, does not mean it is a correct route.
Note that of the five example commands in Example J-3, IOS would accept all of them except the third one. IOS can notice the case of omitting the outgoing interface if the next-hop address is a link-local address. Example J-4 shows a sample of the error message from IOS.
Example J-4 IOS Rejects the ipv6 route Command with Link-Local and No Outgoing Interface
R1# configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)# ipv6 route 2001:DB8:9:3::/64 FE80::2
% Interface has to be specified for a link-local nexthop
R1(config)# ^Z
R1#
R1# show running-config | include ipv6 route
R1#
The Static Route Does Not Appear in the IPv6 Routing Table
The preceding few pages focused on IPv6 static routes that show up in the IPv6 routing table but unfortunately have incorrect parameters. The next page looks at IPv6 routes that have correct parameters, but IOS does not place them into the IPv6 routing table.
When you add an ipv6 route command to the configuration, and the syntax is correct, IOS considers that route to be added to the IPv6 routing table. IOS makes the following checks before adding the route; note that IOS uses this same kind of logic for IPv4 static routes:

For ipv6 route commands that list an outgoing interface, that interface must be in an up/up state.
For ipv6 route commands that list a global unicast or unique local next-hop IP address (that is, not a link-local address), the local router must have a route to reach that next-hop address.
If another IPv6 route exists for that exact same prefix/prefix-length, the static route must have a better (lower) administrative distance.
For example, Router R1, again from Figure J-7, has been configured with IPv6 addresses. Example J-5 shows the addition of an ipv6 route command for remote subnet 2001:DB8:9:3::/64, but with incorrect next-hop address 2001:DB8:9:3::2. That address is on R2, but it is the address on the far side of R2, on R2’s G0/2 interface.
Example J-5 No Route for Next-Hop IPv6 Address in Static Route
R1# configure terminal Enter configuration commands, one per line. End with CNTL/Z. R1(config)# ipv6 route 2001:DB8:9:3::/64 2001:DB8:9:3::2 R1(config)# ^Z R1# show ipv6 route IPv6 Routing Table - default - 5 entries Codes: C - Connected, L - Local, S - Static, U - Per-user Static route B - BGP, HA - Home Agent, MR - Mobile Router, R - RIP H - NHRP, I1 - ISIS L1, I2 - ISIS L2, IA - ISIS interarea IS - ISIS summary, D - EIGRP, EX - EIGRP external, NM - NEMO ND - ND Default, NDp - ND Prefix, DCE - Destination, NDr - Redirect RL - RPL, O - OSPF Intra, OI - OSPF Inter, OE1 - OSPF ext 1 OE2 - OSPF ext 2, ON1 - OSPF NSSA ext 1, ON2 - OSPF NSSA ext 2 la - LISP alt, lr - LISP site-registrations, ld - LISP dyn-eid a - Application C 2001:DB8:9:1::/64 [0/0] via GigabitEthernet0/1, directly connected L 2001:DB8:9:1::1/128 [0/0] via GigabitEthernet0/1, receive C 2001:DB8:9:2::/64 [0/0] via GigabitEthernet0/2, directly connected L 2001:DB8:9:2::1/128 [0/0] via GigabitEthernet0/2, receive L FF00::/8 [0/0] via Null0, receive
Note
The content under the heading “Default Routes with SLAAC on Router Interfaces” was most recently published in Chapter 32 of the Cisco CCNA ICND1 100-105 Official Cert Guide.
Default Routes with SLAAC on Router Interfaces
Routers can use DHCP on their own interface and learn their IP address, mask, and even a default IPv4 route. In particular, that process can be useful on a router that connects to the Internet. The enterprise router uses DHCP as a client, learning its own IPv4 address with DHCP and adding a default route pointing to the ISP’s router as the next-hop IPv4 address.
Routers can accomplish the same goals with IPv6, just with a few different protocols and methods. As with IPv4, the IPv6 enterprise router can dynamically learn its IPv6 address and dynamically create a default IPv6 route to the ISP’s router. This section shows the details, with the enterprise router using SLAAC to learn its address and the information needed to create a default route.
First, the enterprise router that connects to the ISP, like Router R1 in Figure J-8, requires the configuration of the interface subcommand ipv6 address autoconfig default. This command tells the router that, on that interface, use SLAAC to build its own IPv6 address. R1 would act like any host that uses SLAAC, as shown in Step 2 of the figure, and send an NDP RS message over the link. As noted at Step 3, the ISP router would send back an RA message, announcing router ISP1’s IPv6 address and the IPv6 prefix used on the link.

Figure J-8 Enterprise Router Using SLAAC to Build IPv6 Address and Default IPv6 Route
When R1 receives the NDP RA message, it does the following:
Interface address: Builds its own interface IPv6 address using the SLAAC process, based on the prefix in the RA.
Local /128 Route: Adds a local (/128) IPv6 route for the address, as it would for any interface IPv6 address.
Connected Route for Prefix: Adds a connected (/64) route for the prefix learned in the NDP RA message.
Default route: R1 adds a default route, to destination ::/0, with the next-hop address of ISP’s link-local address, as learned in the RA sent by router ISP1.
Note that the router can be configured to add this default route or not. As shown in the figure, the router builds a default route. Using the ipv6 address autoconfig subcommand without the default keyword causes the router to build its address with SLAAC but not add a default route.
Example J-6 shows the three IPv6 routes on Router R1 just mentioned in the list. In particular, note the codes for the connected route and the default route; both codes begin with ND, meaning the route was learned with NDP. In particular, as highlighted in the legend part of the output, ND refers to an NDP-learned default route, and NDp refers to an NDP-learned prefix (as listed in the NDP RA message in Figure J-9 in this case). Note also that these same two routes have an administrative distance of 2, which is the default administrative distance of IPv6 routes learned with NDP.
Example J-6 Learning an Address and Default Static Route with DHCP
R1# show ipv6 route
IPv6 Routing Table - default - 4 entries
Codes: C - Connected, L - Local, S - Static, U - Per-user Static route
B - BGP, HA - Home Agent, MR - Mobile Router, R - RIP
H - NHRP, I1 - ISIS L1, I2 - ISIS L2, IA - ISIS interarea
IS - ISIS summary, D - EIGRP, EX - EIGRP external, NM - NEMO
ND - ND Default, NDp - ND Prefix, DCE - Destination, NDr - Redirect
O - OSPF Intra, OI - OSPF Inter, OE1 - OSPF ext 1, OE2 - OSPF ext 2
ON1 - OSPF NSSA ext 1, ON2 - OSPF NSSA ext 2, la - LISP alt
lr - LISP site-registrations, ld - LISP dyn-eid, a - Application
ND ::/0 [2/0]
via FE80::22FF:FE22:2222, Serial0/0/0
NDp 2001:DB8:1:12::/64 [2/0]
via Serial0/0/0, directly connected
L 2001:DB8:1:12:32F7:DFF:FE29:8560/128 [0/0]
via Serial0/0/0, receive
! lines omitted for brevity