Now we are ready to create our first virtual machine, it will be the server that will host the web applications we'll use to practice and improve our penetration testing skills.
We will use a virtual machine called OWASP-bwa (OWASP Broken Web Apps) that is a collection of vulnerable web applications specially set up to perform security testing.
- Go to http://sourceforge.net/projects/owaspbwa/files/ and download the latest release's
.ovafile. At the time of writing, it isOWASP_Broken_Web_Apps_VM_1.1.1.ova.
- Wait for the download to finish and then open the file.
- VirtualBox's import dialog will launch. If you want to change the machine's name or description, you can do it by double-clicking on the values. We will name it
vulnerable_vm.and leave the rest of the options as they are. Click on Import.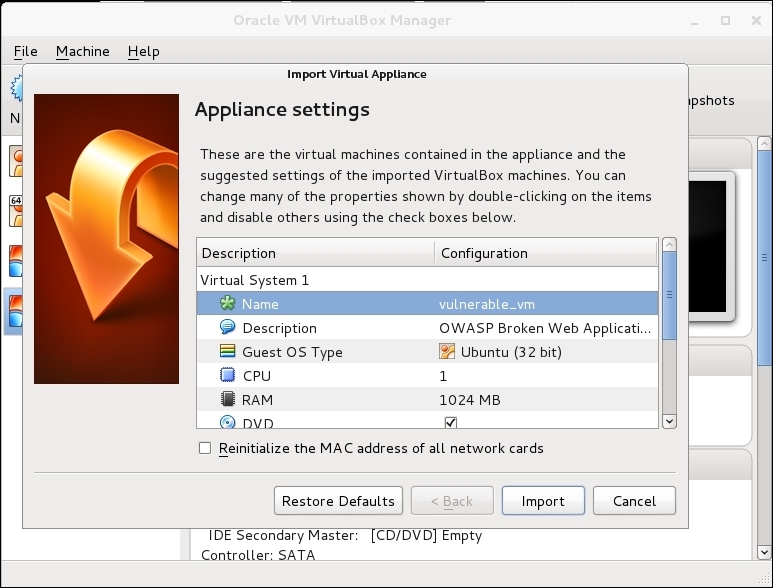
- The import should take a minute and after that we will see our virtual machine displayed in VirtualBox's list. Let's select it and click on Start.
- After the machine starts, we will be asked for login and password, type
rootas the login andowaspbwaas the password and we are set.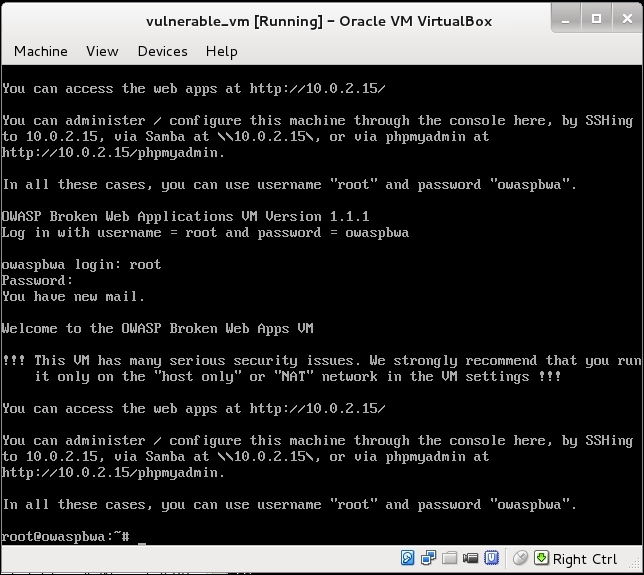
OWASP-bwa is a project aimed at providing security professionals and enthusiasts with a safe environment to develop attacking skills and identify and exploit vulnerabilities in web applications, in order to be able to help developers and administrators fix and prevent them.
This virtual machine includes different types of web applications, some of them are based on PHP, some in Java; we even have a couple of .NET-based vulnerable applications. There are also some vulnerable versions of known applications, such as WordPress or Joomla.
There are many options when we talk about vulnerable applications and virtual machines. A remarkable website that holds a great collection of such applications is VulnHub (https://www.vulnhub.com/). It also has walkthroughs that will help you to solve some challenges and develop your skills.
In this book, we will use another virtual machine for some recipes: bWapp Bee-box, which can also be downloaded from VulnHub: https://www.vulnhub.com/entry/bwapp-bee-box-v16,53/.
