Name
chmod — stdin stdout - file -- opt --help --version
Synopsis
chmod [options]permissions files
The chmod (change mode)
command protects files and directories from unauthorized users on
the same system, by setting access permissions. Typical permissions
are read, write, and execute, and they may be limited to the file
owner, the file’s group owner, and/or other users. The permissions
argument can take three different forms:
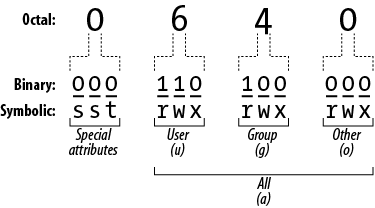
--reference=file, to set the same permissions as another given file.An octal number, up to four digits long, that specifies the file’s absolute permissions in bits, as in Figure 1-6. The leftmost digit is special (described later) and the second, third, and fourth represent the file’s owner, the file’s group, and all users.
One or more strings specifying absolute or relative permissions (i.e., relative to the file’s existing permissions). For example,
a+rmakes a file readable by all users.
In the third form, each string consists of three parts: an optional scope, a command, and permissions.
- Scope (optional)
ufor user,gfor group,ofor other users not in the group,afor all users. The default isa.- Command
+to add permissions;−to remove permissions; or=to set absolute permissions, ignoring existing ones.- Permissions
rfor read,wfor write/modify,xfor execute (for directories, this is permission tocdinto the directory),Xfor conditional execute (explained later),uto duplicate the user permissions,gto duplicate the group permissions,oto duplicate the “other users” permissions,sfor setuid or setgid, andtfor the sticky bit.
For example, ug+rw would
add read and write permission for the user and the group, a-x (or just -x) would remove execute permission for
everyone, and u=r would first
remove all existing permissions and then make the file readable only
by its owner. You can combine these strings by separating them with
commas, such as ug+rw,a-x.
Conditional execute permission (X) means the same as x, except that it succeeds only if the
file is already executable, or if the file is a directory.
Otherwise, it has no effect.
Setuid and setgid apply to executable files (programs and
scripts). Suppose we have an executable file F owned by user “smith” and the group
“friends”. If file F has setuid
(set user ID) enabled, then anyone who runs F will “become” user smith, with all her
rights and privileges, for the duration of the program. Likewise, if
F has setgid (set group ID)
enabled, anyone who executes F
becomes a member of the friends group for the duration of the
program. As you might imagine, setuid and setgid can impact system
security, so don’t use them unless you really
know what you’re doing. One misplaced chmod
+s can leave your whole system vulnerable to attack.
The sticky bit, most commonly used for /tmp directories, controls removal of files in that directory. Normally, if you have write permission in a directory, you can delete or move files within it, even if you don’t have this access to the files themselves. Inside a directory with the sticky bit set, you need write permission on a file in order to delete or move it.