Chapter 8
IP Subnetting, Troubleshooting IP, and Introduction to NAT
This chapter's focus will really zoom in on IP addressing to ensure that you have it nailed down tight. This is an integral aspect of networking, and it's important for your success on the exams and as a professional, too!
We'll start with subnetting an IP network. You're going to have to really apply yourself because it takes time and practice in order to do subnetting correctly and quickly. So be patient and do whatever it takes to get this stuff dialed in. This chapter truly is important—possibly the most important chapter in this book for you to understand. Make it part of you!
I'll thoroughly cover IP subnetting from the very beginning. I know this might sound weird to you, but I think you'll be much better off if you can try to forget everything you've learned about subnetting before reading this chapter—especially if you've been to a Microsoft class!
I'll also walk you through IP address troubleshooting and each of the recommended steps for troubleshooting an IP network. Finally, I'll finish up with an introduction to Network Address Translation (NAT)—there are various types of NAT, and you need to know when you would use each one.
So get psyched—you're about to go for quite a ride! This chapter will truly help you understand IP addressing and networking, so don't get discouraged or give up. If you stick with it, I promise that one day you'll look back on this and be really glad you decided to stay the course. It's one of those things that after you understand it, you'll laugh at that time, way back when, when you thought this was hard. So, are you ready now? Let's go!
Subnetting Basics
In Chapter 7, “IP Addressing,” you learned how to define and find the valid host ranges used in a Class A, Class B, or Class C network address by turning the host bits all off and then all on. This is very good, but here's the catch: You were defining only one network. What would happen if you wanted to take one network address range and create six networks from it? You would have to do something called subnetting, because that's what allows you to take one larger network and break it into a bunch of smaller networks.
There are loads of reasons in favor of subnetting, including the following benefits:
- Reduced Network Traffic We all appreciate less traffic of any kind. With networks, it's no different. Without trusty routers, packet traffic could grind the entire network down to a near standstill. With routers, most traffic will stay on the local network; only packets destined for other networks will pass through the router. Routers create broadcast domains. The more broadcast domains you create, the smaller the broadcast domains and the less network traffic on each network segment.
- Optimized Network Performance This is the very cool reward you get when you reduce network traffic!
- Simplified Management It's easier to identify and isolate network problems in a group of smaller connected networks than within one gigantic network.
- Facilitated Spanning of Large Geographical Distances Because WAN links are considerably slower and more expensive than LAN links, a single large network that spans long distances can create problems in every area previously listed. Connecting multiple smaller networks makes the system more efficient.
Next, we're going to move on to subnetting a network address. This is the good part—ready?
How to Create Subnets
To create subnetworks, you take bits from the host portion of the IP address and reserve them to define the subnet address. This means fewer bits for hosts, so the more subnets, the fewer bits are left available for defining hosts.
Soon, I'll show you how to create subnets, starting with Class C addresses. But before you actually implement subnetting, you really need to determine your current requirements as well as plan for future conditions.
Follow these steps—they're your recipe for solid design:
- Determine the number of required network IDs:
- One for each subnet
- One for each wide area network (WAN) connection
- Determine the number of required host IDs per subnet:
- One for each TCP/IP host
- One for each router interface
- Based on the previous requirements, create the following:
- One subnet mask for your entire network
- A unique subnet ID for each physical segment
- A range of host IDs for each subnet
Subnet Masks
For the subnet address scheme to work, every machine on the network must know which part of the host address will be used as the subnet address. This is accomplished by assigning a subnet mask to each machine. A subnet mask is a 32-bit value that allows the recipient of IP packets to distinguish the network ID portion of the IP address from the host ID portion of the IP address.
The network administrator creates a 32-bit subnet mask composed of 1s and 0s. The 1s in the subnet mask represent the positions that refer to the network, or subnet, addresses.
Not all networks need subnets, meaning they use the default subnet mask. This is basically the same as saying that a network doesn't have a subnet address.
Table 8.1 shows the default subnet masks for Classes A, B, and C. These default masks cannot and do not change. In other words, you can't make a Class B subnet mask read 255.0.0.0. If you try, the host will read that address as invalid and usually won't even let you type it in. For a Class A network, you can't change the first byte in a subnet mask; it must read 255.0.0.0 at a minimum. Similarly, you cannot assign 255.255.255.255, because this is all 1s—a broadcast address. A Class B address must start with 255.255.0.0, and a Class C has to start with 255.255.255.0. Check out Table 8.1.
TABLE 8.1 Default subnet masks
| Class | Format | Default subnet mask |
|---|---|---|
| A | network.host.host.host | 255.0.0.0 |
| B | network.network.host.host | 255.255.0.0 |
| C | network.network.network.host | 255.255.255.0 |
In Chapter 7 we discussed the addresses with the first octet of 224 to 255 are reserved for Class D and E networks. Class D (224–239) is used for multicast addresses and Class E (240–255) for scientific purposes. But they're really beyond the scope of this book, so I'm not going to go into detail about them here. But you do need to remember that the multicast range is from 224.0.0.0 through 239.255.255.255.
Classless Inter-Domain Routing (CIDR)
Another term you need to know is Classless Inter-Domain Routing (CIDR). It's basically the method that Internet service providers (ISPs) use to allocate a number of addresses to a company or a home connection. They provide addresses in a certain block size; I'll be going into that in greater detail later in this chapter. Another term for the use of different length subnet masks in the network is variable-length subnet masking (VLSM).
When you receive a block of addresses from an ISP, what you get will look something like this: 192.168.10.32/28. This is telling you what your subnet mask is. The slash notation (/) means how many bits are turned on (1s). Obviously, the maximum could only be /32 because a byte is 8 bits and there are 4 bytes in an IP address: 4 × 8 = 32. But keep in mind that the largest subnet mask available (regardless of the class of address) can only be a /30 because you have to keep at least 2 bits for host bits.
Take, for example, a Class A default subnet mask, which is 255.0.0.0. This means that the first byte of the subnet mask is all ones (1s), or 11111111. When referring to a slash notation, you need to count all the 1s bits to figure out your mask. The 255.0.0.0 is considered a /8 because it has 8 bits that are 1s—that is, 8 bits that are turned on.
A Class B default mask would be 255.255.0.0, which is a /16 because 16 bits are (1s): 11111111.11111111.00000000.00000000.
Table 8.2 offers a listing of every available subnet mask and its equivalent CIDR slash notation.
TABLE 8.2 CIDR values
| Subnet Mask | CIDR Value |
|---|---|
| 255.0.0.0 | /8 |
| 255.128.0.0 | /9 |
| 255.192.0.0 | /10 |
| 255.224.0.0 | /11 |
| 255.240.0.0 | /12 |
| 255.248.0.0 | /13 |
| 255.252.0.0 | /14 |
| 255.254.0.0 | /15 |
| 255.255.0.0 | /16 |
| 255.255.128.0 | /17 |
| 255.255.192.0 | /18 |
| 255.255.224.0 | /19 |
| 255.255.240.0 | /20 |
| 255.255.248.0 | /21 |
| 255.255.252.0 | /22 |
| 255.255.254.0 | /23 |
| 255.255.255.0 | /24 |
| 255.255.255.128 | /25 |
| 255.255.255.192 | /26 |
| 255.255.255.224 | /27 |
| 255.255.255.240 | /28 |
| 255.255.255.248 | /29 |
| 255.255.255.252 | /30 |
Although according to RFC 1518, any device or software that claims to be CIDR compliant will allow supernetting, meaning a traditional Class C address can be used with a /23 subnet mask, in almost all cases. The /8 through /15 can be used only with Class A network addresses; /16 through /23 can be used by Class A and B network addresses; /24 through /30 can be used by Class A, B, and C network addresses. This is a big reason most companies use Class A network addresses. By being allowed the use of all subnet masks, they gain the valuable benefit of maximum flexibility for their network design.
Subnetting Class C Addresses
There are many different ways to subnet a network. The right way is the way that works best for you. In a Class C address, only 8 bits are available for defining the hosts. Remember that subnet bits start at the left and go to the right, without skipping bits. This means that the only Class C subnet masks can be those listed here:
| Binary | Decimal | CIDR |
|---|---|---|
| 00000000 | 0 | /24 |
| 10000000 | 128 | /25 |
| 11000000 | 192 | /26 |
| 11100000 | 224 | /27 |
| 11110000 | 240 | /28 |
| 11111000 | 248 | /29 |
| 11111100 | 252 | /30 |
We can't use a /31 or /32 because, remember, we have to leave at least 2 host bits for assigning IP addresses to hosts.
Get ready for something special. I'm going to teach you an alternate method of subnetting that makes it a whole lot easier to subnet larger numbers in no time. And trust me, you really do need to be able to subnet fast!
Subnetting a Class C Address: The Fast Way!
When you've chosen a possible subnet mask for your network and need to determine the number of subnets, valid hosts, and broadcast addresses of a subnet that the mask provides, all you need to do is answer five simple questions:
- How many subnets does the chosen subnet mask produce?
- How many valid hosts per subnet are available?
- What are the valid subnets?
- What's the broadcast address of each subnet?
- What are the valid hosts in each subnet?
At this point, it's important that you both understand and have memorized your powers of 2. Please refer to the sidebar “Understanding the Powers of 2” earlier in this chapter if you need some help. Here's how you get the answers to those five big questions:
- How many subnets? 2x = number of subnets. x is the number of masked bits, or the 1s. For example, in 11000000, the number of 1s gives us 22 subnets. In this example, there are 4 subnets.
- How many hosts per subnet? 2y – 2 = number of hosts per subnet. y is the number of unmasked bits, or the 0s. For example, in 11000000, the number of 0s gives us 26 – 2 hosts. In this example, there are 62 hosts per subnet. You need to subtract 2 for the subnet address and the broadcast address, which are not valid hosts.
- What are the valid subnets? 256 – subnet mask = block size, or increment number. An example would be 256 – 192 = 64. The block size of a 192 mask is always 64. Start counting at zero in blocks of 64 until you reach the subnet mask value, and these are your subnets. 0, 64, 128, 192. Easy, huh?
- What's the broadcast address for each subnet? Now here's the really easy part. Because we counted our subnets in the last section as 0, 64, 128, and 192, the broadcast address is always the number right before the next subnet. For example, the 0 subnet has a broadcast address of 63 because the next subnet is 64. The 64 subnet has a broadcast address of 127 because the next subnet is 128. And so on. And remember, the broadcast address of the last subnet is always 255.
- What are the valid hosts? Valid hosts are the numbers between the subnets, omitting all the 0s and all the 1s. For example, if 64 is the subnet number and 127 is the broadcast address, then 65–126 is the valid host range—it's always the numbers between the subnet address and the broadcast address.
I know this can truly seem confusing. But it really isn't as hard as it seems to be at first—just hang in there! Why not try a few and see for yourself?
Subnetting Practice Examples: Class C Addresses
Here's your opportunity to practice subnetting Class C addresses using the method I just described. Exciting, isn't it? We're going to start with the first Class C subnet mask and work through every subnet that we can using a Class C address. When we're done, I'll show you how easy this is with Class B networks too!
Practice Example #1C: 255.255.255.128 (/25)
Because 128 is 10000000 in binary, there is only 1 bit for subnetting, and there are 7 bits for hosts. We're going to subnet the Class C network address 192.168.10.0.
- 192.168.10.0 = Network address
- 255.255.255.128 = Subnet mask
Now, let's answer the big five:
- How many subnets? Because 128 is 1 bit on (10000000), the answer is 21 = 2.
- How many hosts per subnet? We have 7 host bits off (10000000), so the equation is 27 – 2 = 126 hosts.
- What are the valid subnets? 256 – 128 = 128. Remember, we'll start at zero and count in our block size, so our subnets are 0, 128.
- What's the broadcast address for each subnet? The number right before the value of the next subnet is all host bits turned on and equals the broadcast address. For the 0 subnet, the next subnet is 128, so the broadcast address of the 0 subnet is 127.
- What are the valid hosts? These are the numbers between the subnet and broadcast address. The easiest way to find the hosts is to write out the subnet address and the broadcast address. This way, the valid hosts are obvious. The following table shows the 0 and 128 subnets, the valid host ranges of each, and the broadcast address of both subnets:
| Subnet | 0 | 128 |
|---|---|---|
| First host | 1 | 129 |
| Last host | 126 | 254 |
| Broadcast | 127 | 255 |
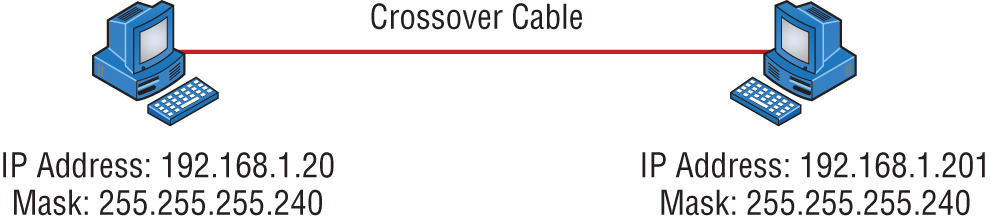
Before moving on to the next example, take a look at Figure 8.1. Okay, looking at a Class C /25, it's pretty clear there are two subnets. But so what—why is this significant? Well actually, it's not, but that's not the right question. What you really want to know is what you would do with this information!
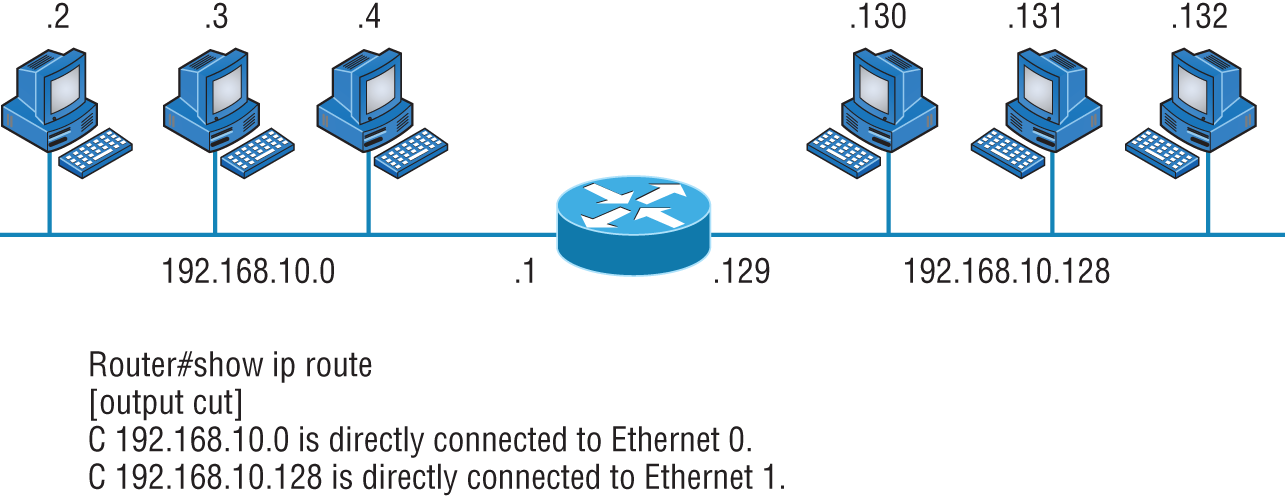
FIGURE 8.1 Implementing a Class C /25 logical network
The key to understanding subnetting is to understand the very reason you need to do it. And I'm going to demonstrate this by going through the process of building a physical network—and let's add a router. (We now have an internetwork, as I truly hope you already know!) Because we added that router, in order for the hosts on our internetwork to communicate, they must now have a logical network addressing scheme. We could use IPv6, but IPv4 is still the most popular, and it also just happens to be what we're studying at the moment, so that's what we're going with.
Now take a look back at Figure 8.1. By the way, the output you see below the diagram is the routing table of the router, which was displayed by executing the
show ip route
command on the router. There are two physical networks, so we're going to implement a logical addressing scheme that allows for two logical networks. As always, it's a really good idea to look ahead and consider any likely growth scenarios—both short and long term, but for this example, a /25 will do the trick.
Practice Example #2C: 255.255.255.192 (/26)
In this second example, we're going to subnet the network address 192.168.10.0 using the subnet mask 255.255.255.192.
- 192.168.10.0 = Network address
- 255.255.255.192 = Subnet mask
It's time to answer the big five:
- How many subnets? Because 192 is 2 bits on (11000000), the answer is 22 = 4 subnets.
- How many hosts per subnet? We have 6 host bits off (11000000), so the equation is 26 – 2 = 62 hosts.
- What are the valid subnets? 256 – 192 = 64. Remember, we start at zero and count in our block size, so our subnets are 0, 64, 128, and 192.
- What's the broadcast address for each subnet? The number right before the value of the next subnet is all host bits turned on and equals the broadcast address. For the 0 subnet, the next subnet is 64, so the broadcast address for the 0 subnet is 63.
- What are the valid hosts? These are the numbers between the subnet and broadcast address. The easiest way to find the hosts is to write out the subnet address and the broadcast address. This way, the valid hosts are obvious. The following table shows the 0, 64, 128, and 192 subnets, the valid host ranges of each, and the broadcast address of each subnet:
| The subnets (do this first) | 0 | 64 | 128 | 192 |
|---|---|---|---|---|
| Our first host (perform host addressing last) | 1 | 65 | 129 | 193 |
| Our last host | 62 | 126 | 190 | 254 |
| The broadcast address (do this second) | 63 | 127 | 191 | 255 |
Again, before getting into the next example, you can see that we can now subnet a /26. And what are you going to do with this fascinating information? Implement it! We'll use Figure 8.2 to practice a /26 network implementation.
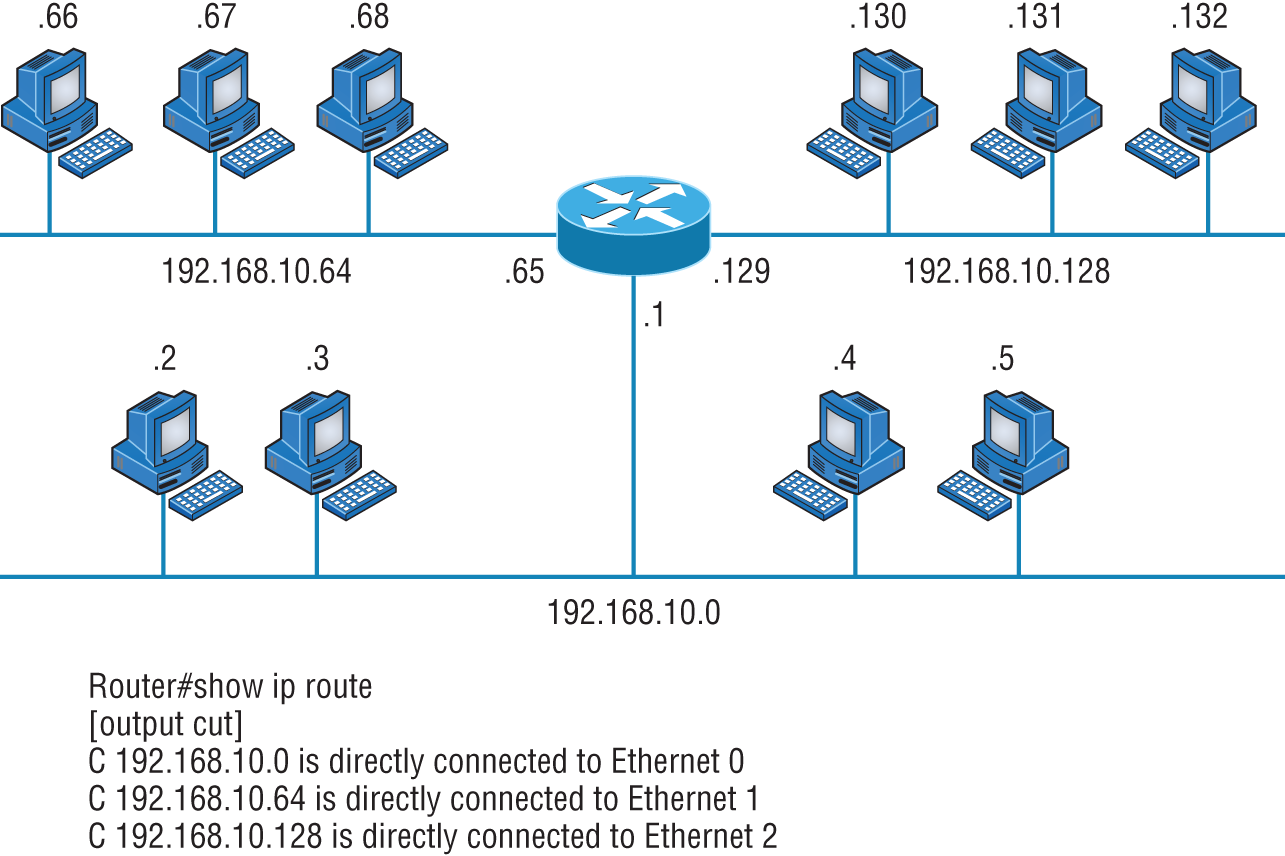
FIGURE 8.2 Implementing a Class C /26 logical network
The /26 mask provides four subnetworks, and we need a subnet for each router interface. With this mask, in this example, we actually have room to add another router interface.
Practice Example #3C: 255.255.255.224 (/27)
This time, we'll subnet the network address 192.168.10.0 and subnet mask 255.255.255.224.
- 192.168.10.0 = Network address
- 255.255.255.224 = Subnet mask
- How many subnets? 224 is 11100000, so our equation is 23 = 8.
- How many hosts? 25 – 2 = 30.
- What are the valid subnets? 256 – 224 = 32. We just start at zero and count to the subnet mask value in blocks (increments) of 32: 0, 32, 64, 96, 128, 160, 192, and 224.
- What's the broadcast address for each subnet (always the number right before the next subnet)?
- What are the valid hosts (the numbers between the subnet number and the broadcast address)?
To answer the last two questions, first just write out the subnets, and then write out the broadcast address—the number right before the next subnet. Last, fill in the host address. The following table gives you all the subnets for the 255.255.255.224 Class C subnet mask:
| The subnet address | 0 | 32 | 64 | 96 | 128 | 160 | 192 | 224 |
|---|---|---|---|---|---|---|---|---|
| The first valid host | 1 | 33 | 65 | 97 | 129 | 161 | 193 | 225 |
| The last valid host | 30 | 62 | 94 | 126 | 158 | 190 | 222 | 254 |
| The broadcast address | 31 | 63 | 95 | 127 | 159 | 191 | 223 | 255 |
Practice Example #4C: 255.255.255.240 (/28)
Let's practice on another one:
- 192.168.10.0 = Network address
- 255.255.255.240 = Subnet mask
- Subnets? 240 is 11110000 in binary. 24 = 16.
- Hosts? 4 host bits, or 24 – 2 = 14.
- Valid subnets? 256 – 240 = 16. 0, 16, 32, 48, 64, 80, 96, 112, 128, 144, 160, 176, 192, 208, 224, 240.
- Broadcast address for each subnet?
- Valid hosts?
To answer the last two questions, check out the following table. It gives you the subnets, valid hosts, and broadcast address for each subnet. First, find the address of each subnet using the block size (increment). Second, find the broadcast address of each subnet increment (it's always the number right before the next valid subnet); then, just fill in the host address. The following table shows the available subnets, hosts, and broadcast address provided by a Class C network 255.255.255.240 mask:
| Subnet | 0 | 16 | 32 | 48 | 64 | 80 | 96 | 112 | 128 | 144 | 160 | 176 | 192 | 208 | 224 | 240 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| First host | 1 | 17 | 33 | 49 | 65 | 81 | 97 | 113 | 129 | 145 | 161 | 177 | 193 | 209 | 225 | 241 |
| Last host | 14 | 30 | 46 | 62 | 78 | 94 | 110 | 126 | 142 | 158 | 174 | 190 | 206 | 222 | 238 | 254 |
| Broadcast | 15 | 31 | 47 | 63 | 79 | 95 | 111 | 127 | 143 | 159 | 175 | 191 | 207 | 223 | 239 | 255 |
Practice Example #5C: 255.255.255.248 (/29)
Let's keep practicing:
- 192.168.10.0 = Network address
- 255.255.255.248 = Subnet mask
- Subnets? 248 in binary = 11111000. 25 = 32.
- Hosts? 23 – 2 = 6.
- Valid subnets? 256 – 248 = 8, start at zero: 0, 8, 16, 24, 32, 40, 48, 56, 64, 72, 80, 88, 96, 104, 112, 120, 128, 136, 144, 152, 160, 168, 176, 184, 192, 200, 208, 216, 224, 232, 240, and 248.
- Broadcast address for each subnet?
- Valid hosts?
Take a look at the following table. It shows some of the subnets (first four and last four only), valid hosts, and broadcast address for the Class C 255.255.255.248 mask:
| Subnet | 0 | 8 | 16 | 24 | … | 224 | 232 | 240 | 248 |
|---|---|---|---|---|---|---|---|---|---|
| First host | 1 | 9 | 17 | 25 | … | 225 | 233 | 241 | 249 |
| Last host | 6 | 14 | 22 | 30 | … | 230 | 238 | 246 | 254 |
| Broadcast | 7 | 15 | 23 | 31 | … | 231 | 239 | 247 | 255 |
Practice Example #6C: 255.255.255.252 (/30)
I know, I know—but just one more:
- 192.168.10.0 = Network address
- 255.255.255.252 = Subnet mask
- Subnets? 64.
- Hosts? 2.
- Valid subnets? 0, 4, 8, 12, and so on, all the way to 252.
- Broadcast address for each subnet (always the number right before the next subnet)?
- Valid hosts (the numbers between the subnet number and the broadcast address)?
The following table shows you the subnet, valid host, and broadcast address of the first four and last four subnets in the 255.255.255.252 Class C subnet:
| Subnet | 0 | 4 | 8 | 12 | … | 240 | 244 | 248 | 252 |
|---|---|---|---|---|---|---|---|---|---|
| First host | 1 | 5 | 9 | 13 | … | 241 | 245 | 249 | 253 |
| Last host | 2 | 6 | 10 | 14 | … | 242 | 246 | 250 | 254 |
| Broadcast | 3 | 7 | 11 | 15 | … | 243 | 247 | 251 | 255 |
Subnetting in Your Head: Class C Addresses
It really is possible to subnet in your head by looking at a valid IP address and subnet mask. This is extremely important for IP addressing and troubleshooting. Even if you don't believe me that you can subnet in your head, I'll show you how. And it's not all that hard either—take the following example: What is the subnet, broadcast address, and valid host range that this host IP address is a part of?
- 192.168.10.33 = Host address
- 255.255.255.224 = Subnet mask
First, determine the subnet and broadcast address of this IP address. You can do this by answering question 3 of the big five questions: 256 – 224 = 32. Start at zero: 0, 32, 64. The address of 33 falls between the two subnets of 32 and 64 and must be part of the 192.168.10.32 subnet. The next subnet is 64, so the broadcast address of the 32 subnet is 63. (Remember that the broadcast address of a subnet is always the number right before the next subnet.) The valid host range is 33–62 (the numbers between the subnet and broadcast address). I told you this is easy!
Okay, let's try another one. What is the subnet, broadcast address, and valid host range that this host IP address is a part of?
- 192.168.10.33 = Host address
- 255.255.255.240 = Subnet mask
256 – 240 = 16. Start at zero and count till you pass the valid host in the problem: 0, 16, 32, 48. Bingo—the host address is between the 32 and 48 subnets. The subnet is 192.168.10.32, and the broadcast address is 47 (the next subnet is 48). The valid host range is 33–46 (the numbers between the subnet number and the broadcast address).
We need to do more, just to make sure you have this down.
You have a host address of 192.168.10.174 with a mask of 255.255.255.240. What is the subnet, broadcast address, and valid host range that this host IP address is a part of?
The mask is 240, so we need our block size: 256 – 240 = 16. Just keep adding 16 until we pass the host address of 174, starting at zero, of course: 0, 16, 32, 48, 64, 80, 96, 112, 128, 144, 160, 176. The host address of 174 is between 160 and 176, so the subnet is 160. The broadcast address is 175; the valid host range is 161–174. That was a tough one.
Let's do one more just for fun. Of all Class C subnetting, this is the easiest:
- 192.168.10.17 = Host address
- 255.255.255.252 = Subnet mask
What subnet and broadcast address is this IP address a part of? 256 – 252 = 4. Start at zero (always start at zero unless told otherwise): 0, 4, 8, 12, 16, 20, and so on. You've got it! The host address is between the 16 and 20 subnets. The subnet is 192.168.10.16, and the broadcast address is 19. The valid host range is 17–18.
Now that you're all over Class C subnetting, let's move on to Class B subnetting. But before we do, let's do a quick review.
So What Do You Know Now?
Here's where you can really apply what you've learned so far and begin committing it all to memory. This is a very cool section that I've been using in my classes for years. It will really help you nail down subnetting!
When you see a subnet mask or slash notation (CIDR), you should know the following when working with Class C networks:
/25
What do you know about a /25?
- 128 mask
- 1 bit on and 7 bits off (10000000)
- Block size of 128
- 2 subnets, each with 126 hosts
/26
And what do you know about a /26?
- 192 mask
- 2 bits on and 6 bits off (11000000)
- Block size of 64
- 4 subnets, each with 62 hosts
/27
What about a /27?
- 224 mask
- 3 bits on and 5 bits off (11100000)
- Block size of 32
- 8 subnets, each with 30 hosts
/28
And what about a /28?
- 240 mask
- 4 bits on and 4 bits off
- Block size of 16
- 16 subnets, each with 14 hosts
/29
What do you know about a /29?
- 248 mask
- 5 bits on and 3 bits off
- Block size of 8
- 32 subnets, each with 6 hosts
/30
And last, what about a /30?
- 252 mask
- 6 bits on and 2 bits off
- Block size of 4
- 64 subnets, each with 2 hosts
Regardless of whether you have a Class A, Class B, or Class C address, the /30 mask will provide you with only two hosts, ever. This mask is suited almost exclusively for use on point-to-point links.
If you can memorize this “So What Do You Know Now?” section, you'll be much better off in your day-to-day job and in your studies. Try saying it out loud, which helps you memorize things—yes, your significant other and/or coworkers will think you've lost it, but they probably already do if you're in the networking field. And if you're not yet in the networking field but are studying all this to break into it, you might as well have people start thinking you're a little “different” now because they will eventually anyway.
It's also helpful to write these on some type of flashcards and have people test your skill. You'd be amazed at how fast you can get subnetting down if you memorize block sizes as well as this “So What Do You Know Now?” section.
Subnetting Class B Addresses
Before we dive into this, let's look at all the possible Class B subnet masks. Notice that we have a lot more possible subnet masks than we do with a Class C network address:
| 255.255.0.0 | (/16) |
| 255.255.128.0 | (/17) |
| 255.255.192.0 | (/18) |
| 255.255.224.0 | (/19) |
| 255.255.240.0 | (/20) |
| 255.255.248.0 | (/21) |
| 255.255.252.0 | (/22) |
| 255.255.254.0 | (/23) |
| 255.255.255.0 | (/24) |
| 255.255.255.128 | (/25) |
| 255.255.255.192 | (/26) |
| 255.255.255.224 | (/27) |
| 255.255.255.240 | (/28) |
| 255.255.255.248 | (/29) |
| 255.255.255.252 | (/30) |
We know the Class B network address has 16 bits available for host addressing. This means we can use up to 14 bits for subnetting (because we have to leave at least 2 bits for host addressing). Using a /16 means you are not subnetting with Class B, but it is a mask you can use.
The process of subnetting a Class B network is pretty much the same as it is for a Class C, except that you have more host bits and you start in the third octet.
Use the same subnet numbers for the third octet with Class B that you used for the fourth octet with Class C, but add a 0 to the network portion and a 255 to the broadcast section in the fourth octet. The following table shows you an example host range of two subnets used in a Class B 240 (/20) subnet mask:
| First Subnet | Second Subnet |
|---|---|
| 16.0 | 32.0 |
| 31.255 | 47.255 |
Notice that these are the same numbers we used in the fourth octet with a /28 mask, but we moved them to the third octet and added a .0 and .255 at the end. Just add the valid hosts between the numbers, and you're set!
Subnetting Practice Examples: Class B Addresses
The following sections will give you an opportunity to practice subnetting Class B addresses. Again, I have to mention that this is the same as subnetting with Class C, except we start in the third octet—with the exact same numbers!
Practice Example #1B: 255.255.128.0 (/17)
Let's take a look at our first example:
- 172.16.0.0 = Network address
- 255.255.128.0 = Subnet mask
- Subnets? 21 = 2 (same as Class C).
- Hosts? 215 – 2 = 32,766 (7 bits in the third octet, and 8 in the fourth).
- Valid subnets? 256 – 128 = 128. 0, 128. Remember that subnetting in Class B starts in the third octet, so the subnet numbers are really 0.0 and 128.0, as shown in the next table. These are the exact numbers we used with Class C; we use them in the third octet and add a 0 in the fourth octet for the network address.
- Broadcast address for each subnet?
The following table shows the two subnets available, the valid host range, and the broadcast address of each:
| Subnet | 0.0 | 128.0 |
|---|---|---|
| First host | 0.1 | 128.1 |
| Last host | 127.254 | 255.254 |
| Broadcast | 127.255 | 255.255 |
Notice that we just added the fourth octet's lowest and highest values and came up with the answers. And again, it's done exactly the same way as for a Class C subnet. We just use the same numbers in the third octet and added 0 and 255 in the fourth octet—pretty simple, huh? I really can't say this enough: It's not hard. The numbers never change. We just use them in different octets!
Practice Example #2B: 255.255.192.0 (/18)
Let's take a look at a second example with Class B.
- 172.16.0.0 = Network address
- 255.255.192.0 = Subnet mask
- Subnets? 22 = 4.
- Hosts? 214 – 2 = 16,382 (6 bits in the third octet, and 8 in the fourth).
- Valid subnets? 256 – 192 = 64. 0, 64, 128, 192. Remember that we're in the third octet, so the subnet numbers are really 0.0, 64.0, 128.0, and 192.0, as shown in the next table.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the four subnets available, the valid host range, and the broadcast address of each:
| Subnet | 0.0 | 64.0 | 128.0 | 192.0 |
|---|---|---|---|---|
| First host | 0.1 | 64.1 | 128.1 | 192.1 |
| Last host | 63.254 | 127.254 | 191.254 | 255.254 |
| Broadcast | 63.255 | 127.255 | 191.255 | 255.255 |
Again, it's pretty much the same as it is for a Class C subnet—we just added 0 and 255 in the fourth octet for each subnet in the third octet.
Practice Example #3B: 255.255.240.0 (/20)
Let's take a look:
- 172.16.0.0 = Network address
- 255.255.240.0 = Subnet mask
- Subnets? 24 = 16.
- Hosts? 212 – 2 = 4,094.
- Valid subnets? 256 – 240 = 16, but we start at 0 always. 0, 16, 32, 48, and so on, up to 240. Notice that these are the same numbers as a Class C 240 mask—we just put them in the third octet and add a 0 and 255 in the fourth octet.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the first four subnets, valid hosts, and broadcast address in a Class B 255.255.240.0 mask:
| Subnet | 0.0 | 16.0 | 32.0 | 48.0 |
|---|---|---|---|---|
| First host | 0.1 | 16.1 | 32.1 | 48.1 |
| Last host | 15.254 | 31.254 | 47.254 | 63.254 |
| Broadcast | 15.255 | 31.255 | 47.255 | 63.255 |
Practice Example #4B: 255.255.254.0 (/23)
Let's take a look:
- 172.16.0.0 = Network address
- 255.255.254.0 = Subnet mask
- Subnets? 27 = 128.
- Hosts? 29 – 2 = 510.
- Valid subnets? 256 – 254 = 0, 2, 4, 6, 8, and so on, up to 254.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the first five subnets, valid hosts, and broadcast address in a Class B 255.255.254.0 mask:
| Subnet | 0.0 | 2.0 | 4.0 | 6.0 | 8.0 |
|---|---|---|---|---|---|
| First host | 0.1 | 2.1 | 4.1 | 6.1 | 8.1 |
| Last host | 1.254 | 3.254 | 5.254 | 7.254 | 9.254 |
| Broadcast | 1.255 | 3.255 | 5.255 | 7.255 | 9.255 |
Practice Example #5B: 255.255.255.0 (/24)
Contrary to popular belief, 255.255.255.0 used with a Class B network address is not called a Class B network with a Class C subnet mask. It's amazing how many people see this mask used in a Class B network and think it's a Class C subnet mask. This is a Class B subnet mask with 8 bits of subnetting—it's considerably different from a Class C mask. Subnetting this address is fairly simple:
- 172.16.0.0 = Network address
- 255.255.255.0 = Subnet mask
- Subnets? 28 = 256.
- Hosts? 28 – 2 = 254.
- Valid subnets? 256 – 255 = 1. 0, 1, 2, 3, and so on, all the way to 255.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the first four and last two subnets, the valid hosts, and the broadcast address in a Class B 255.255.255.0 mask:
| Subnet | 0.0 | 1.0 | 2.0 | 3.0 | … | 254.0 | 255.0 |
|---|---|---|---|---|---|---|---|
| First host | 0.1 | 1.1 | 2.1 | 3.1 | … | 254.1 | 255.1 |
| Last host | 0.254 | 1.254 | 2.254 | 3.254 | … | 254.254 | 255.254 |
| Broadcast | 0.255 | 1.255 | 2.255 | 3.255 | … | 254.255 | 255.255 |
Practice Example #6B: 255.255.255.128 (/25)
This is one of the hardest subnet masks you can play with. And worse, it actually is a really good subnet to use in production because it creates over 500 subnets with a whopping 126 hosts for each subnet—a nice mixture. So, don't skip over it!
- 172.16.0.0 = Network address
- 255.255.255.128 = Subnet mask
- Subnets? 29 = 512.
- Hosts? 27 – 2 = 126.
- Valid subnets? Now for the tricky part. 256 – 255 = 1. 0, 1, 2, 3, and so on for the third octet. But you can't forget the one subnet bit used in the fourth octet. Remember when I showed you how to figure one subnet bit with a Class C mask? You figure this out the same way. (Now you know why I showed you the 1-bit subnet mask in the Class C section—to make this part easier.) You actually get two subnets for each third octet value, hence the 512 subnets. For example, if the third octet is showing subnet 3, the two subnets would actually be 3.0 and 3.128.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows how you can create subnets, valid hosts, and broadcast addresses using the Class B 255.255.255.128 subnet mask (the first eight subnets are shown, and then the last two subnets):
| Subnet | 0.0 | 0.128 | 1.0 | 1.128 | 2.0 | 2.128 | 3.0 | 3.128 | … | 255.0 | 255.128 |
|---|---|---|---|---|---|---|---|---|---|---|---|
| First host | 0.1 | 0.129 | 1.1 | 1.129 | 2.1 | 2.129 | 3.1 | 3.129 | … | 255.1 | 255.129 |
| Last host | 0.126 | 0.254 | 1.126 | 1.254 | 2.126 | 2.254 | 3.126 | 3.254 | … | 255.126 | 255.254 |
| Broadcast | 0.127 | 0.255 | 1.127 | 1.255 | 2.127 | 2.255 | 3.127 | 3.255 | … | 255.127 | 255.255 |
Practice Example #7B: 255.255.255.192 (/26)
Now, this is where Class B subnetting gets easy. Because the third octet has a 255 in the mask section, whatever number is listed in the third octet is a subnet number. However, now that we have a subnet number in the fourth octet, we can subnet this octet just as we did with Class C subnetting. Let's try it:
- 172.16.0.0 = Network address
- 255.255.255.192 = Subnet mask
- Subnets? 210 = 1024.
- Hosts? 26 – 2 = 62.
- Valid subnets? 256 – 192 = 64. The subnets are shown in the following table. Do these numbers look familiar?
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the first eight subnet ranges, valid hosts, and broadcast address:
| Subnet | 0.0 | 0.64 | 0.128 | 0.192 | 1.0 | 1.64 | 1.128 | 1.192 |
|---|---|---|---|---|---|---|---|---|
| First host | 0.1 | 0.65 | 0.129 | 0.193 | 1.1 | 1.65 | 1.129 | 1.193 |
| Last host | 0.62 | 0.126 | 0.190 | 0.254 | 1.62 | 1.126 | 1.190 | 1.254 |
| Broadcast | 0.63 | 0.127 | 0.191 | 0.255 | 1.63 | 1.127 | 1.191 | 1.255 |
Notice that for each subnet value in the third octet, you get subnets 0, 64, 128, and 192 in the fourth octet.
Practice Example #8B: 255.255.255.224 (/27)
This is done the same way as the preceding subnet mask, except that we have more subnets and fewer hosts per subnet available.
- 172.16.0.0 = Network address
- 255.255.255.224 = Subnet mask
- Subnets? 211 = 2048.
- Hosts? 25 – 2 = 30.
- Valid subnets? 256 – 224 = 32. 0, 32, 64, 96, 128, 160, 192, 224.
- Broadcast address for each subnet?
- Valid hosts?
The following table shows the first eight subnets:
| Subnet | 0.0 | 0.32 | 0.64 | 0.96 | 0.128 | 0.160 | 0.192 | 0.224 |
|---|---|---|---|---|---|---|---|---|
| First host | 0.1 | 0.33 | 0.65 | 0.97 | 0.129 | 0.161 | 0.193 | 0.225 |
| Last host | 0.30 | 0.62 | 0.94 | 0.126 | 0.158 | 0.190 | 0.222 | 0.254 |
| Broadcast | 0.31 | 0.63 | 0.95 | 0.127 | 0.159 | 0.191 | 0.223 | 0.255 |
This next table shows the last eight subnets:
| Subnet | 255.0 | 255.32 | 255.64 | 255.96 | 255.128 | 255.160 | 255.192 | 255.224 |
|---|---|---|---|---|---|---|---|---|
| First host | 255.1 | 255.33 | 255.65 | 255.97 | 255.129 | 255.161 | 255.193 | 255.225 |
| Last host | 255.30 | 255.62 | 255.94 | 255.126 | 255.158 | 255.190 | 255.222 | 255.254 |
| Broadcast | 255.31 | 255.63 | 255.95 | 255.127 | 255.159 | 255.191 | 255.223 | 255.255 |
Subnetting in Your Head: Class B Addresses
Are you nuts? Subnet Class B addresses in our heads? It's actually easier than writing it out—I'm not kidding! Let me show you the steps:
- What subnet and broadcast address is the IP address 172.16.10.33 255.255.255.224 (/27) a member of?
The interesting octet is the fourth octet. 256 – 224 = 32. 32 + 32 = 64. Bingo: 33 is between 32 and 64. However, remember that the third octet is considered part of the subnet, so the answer is the 10.32 subnet. The broadcast is 10.63 because 10.64 is the next subnet. That was a pretty easy one.
- What subnet and broadcast address is the IP address 172.16.66.10 255.255.192.0 (/18) a member of?
The interesting octet is the third octet instead of the fourth octet. 256 – 192 = 64. 0, 64, 128. The subnet is 172.16.64.0. The broadcast must be 172.16.127.255 because 128.0 is the next subnet.
- What subnet and broadcast address is the IP address 172.16.50.10 255.255.224.0 (/19) a member of?
256 – 224 = 0, 32, 64 (remember, we always start counting at zero). The subnet is 172.16.32.0, and the broadcast must be 172.16.63.255 because 64.0 is the next subnet.
- What subnet and broadcast address is the IP address 172.16.46.255 255.255.240.0 (/20) a member of?
256 – 240 = 16. The third octet is interesting to us. 0, 16, 32, 48. This subnet address must be in the 172.16.32.0 subnet, and the broadcast must be 172.16.47.255 because 48.0 is the next subnet. So, yes, 172.16.46.255 is a valid host.
- What subnet and broadcast address is the IP address 172.16.45.14 255.255.255.252 (/30) a member of?
Where is the interesting octet? 256 – 252 = 0, 4, 8, 12, 16 (in the fourth octet). The subnet is 172.16.45.12, with a broadcast of 172.16.45.15 because the next subnet is 172.16.45.16.
- What is the subnet and broadcast address of the host 172.16.88.255/20?
What is a /20? If you can't answer this, you can't answer this question, can you? A /20 is 255.255.240.0, which gives us a block size of 16 in the third octet, and because no subnet bits are on in the fourth octet, the answer is always 0 and 255 in the fourth octet. 0, 16, 32, 48, 64, 80, 96. Bingo: 88 is between 80 and 96, so the subnet is 80.0 and the broadcast address is 95.255.
- A router receives a packet on an interface with a destination address of 172.16.46.191/26. What will the router do with this packet?
Discard it. Do you know why? 172.16.46.191/26 is a 255.255.255.192 mask, which gives us a block size of 64. Our subnets are then 0, 64, 128, 192. 191 is the broadcast address of the 128 subnet, so a router, by default, will discard any broadcast packets.
Troubleshooting IP Addressing
Troubleshooting IP addressing is obviously an important skill because running into trouble somewhere along the way is pretty much a sure thing, and it's going to happen to you. No—I'm not a pessimist; I'm just keeping it real. Because of this nasty fact, it will be great when you can save the day because you can both figure out (diagnose) the problem and fix it on an IP network whether you're at work or at home!
Let's use Figure 8.3 as an example of your basic IP trouble—poor Sally can't log in to the Windows server. Do you deal with this by calling the Microsoft team to tell them their server is a pile of junk and causing all your problems? Tempting, but probably not such a great idea—let's first double-check our network instead. Check out Figure 8.3.
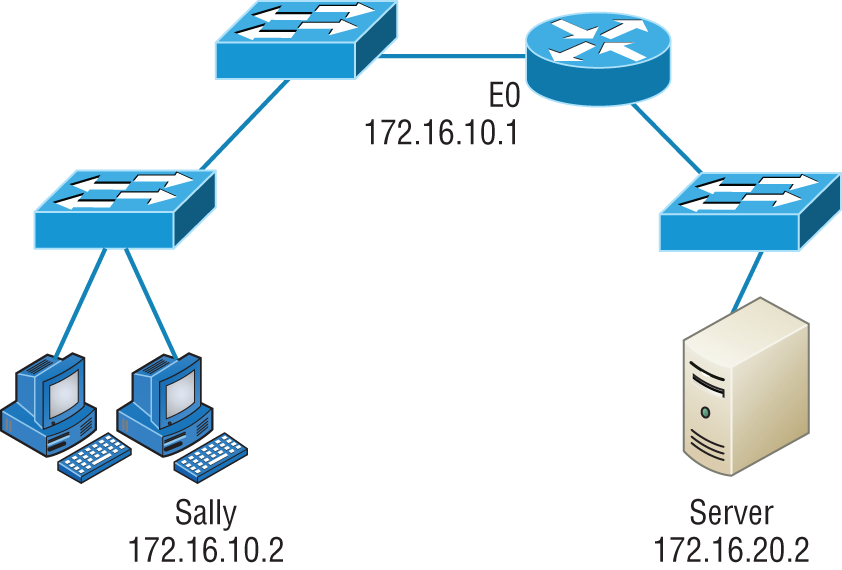
FIGURE 8.3 Basic IP troubleshooting
Let's get started by going over the basic troubleshooting steps. They're pretty simple, but important nonetheless. Pretend you're at Sally's host and she's complaining that she can't communicate to a server that just happens to be on a remote network:
- Open a command prompt window on Sally's host, and ping 127.0.0.1.
C:>ping 127.0.0.1Pinging 127.0.0.1 with 32 bytes of data:Reply from 127.0.0.1: bytes=32 time<1ms TTL=128Reply from 127.0.0.1: bytes=32 time<1ms TTL=128Reply from 127.0.0.1: bytes=32 time<1ms TTL=128Reply from 127.0.0.1: bytes=32 time<1ms TTL=128Ping statistics for 127.0.0.1:Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),Approximate round trip times in milli-seconds:Minimum = 0ms, Maximum = 0ms, Average = 0msThis is the diagnostic, or IPv4 loopback address, and if you get a successful ping, your IP stack is considered to be initialized. If it fails, then you have an IP stack failure and need to reinstall TCP/IP on the host.
- Now, from the same command prompt window, ping the IP address of the local host.
C:>ping 172.16.10.2Pinging 172.16.10.2 with 32 bytes of data:Reply from 172.16.10.2: bytes=32 time<1ms TTL=128Reply from 172.16.10.2: bytes=32 time<1ms TTL=128Reply from 172.16.10.2: bytes=32 time<1ms TTL=128Reply from 172.16.10.2: bytes=32 time<1ms TTL=128Ping statistics for 172.16.10.2:Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),Approximate round trip times in milli-seconds:Minimum = 0ms, Maximum = 0ms, Average = 0msIf that's successful, your network interface card (NIC) is functioning. If it fails, there is a problem with the NIC. Success here doesn't mean that a cable is plugged into the NIC, only that the IP protocol stack on the host can communicate to the NIC (via the LAN driver).
- From the command prompt window, ping the default gateway (router).
C:>ping 172.16.10.1Pinging 172.16.10.1 with 32 bytes of data:Reply from 172.16.10.1: bytes=32 time<1ms TTL=128Reply from 172.16.10.1: bytes=32 time<1ms TTL=128Reply from 172.16.10.1: bytes=32 time<1ms TTL=128Reply from 172.16.10.1: bytes=32 time<1ms TTL=128Ping statistics for 172.16.10.1:Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),Approximate round trip times in milli-seconds:Minimum = 0ms, Maximum = 0ms, Average = 0msIf the ping works, it means that the NIC is plugged into the network and can communicate on the local network. If it fails, you have a local physical network problem that could be anywhere from the NIC to the router.
- If steps 1 through 3 were successful, try to ping the remote server.
C:>ping 172.16.20.2Pinging 172.16.20.2 with 32 bytes of data:Reply from 172.16.20.2: bytes=32 time<1ms TTL=128Reply from 172.16.20.2: bytes=32 time<1ms TTL=128Reply from 172.16.20.2: bytes=32 time<1ms TTL=128Reply from 172.16.20.2: bytes=32 time<1ms TTL=128Ping statistics for 172.16.20.2:Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),Approximate round trip times in milli-seconds:Minimum = 0ms, Maximum = 0ms, Average = 0msIf that works, then you know that you have IP communication between the local host and the remote server. You also know that the remote physical network is working.
If the user still can't communicate with the server after steps 1 through 4 are successful, you probably have some type of name resolution problem and need to check your Domain Name System (DNS) settings. But if the ping to the remote server fails, then you know you have some type of remote physical network problem and need to go to the server and work through steps 1 to 3 until you find the snag.
Before we move on to determining IP address problems and how to fix them, I just want to mention some basic yet handy command-line tools that you can use to help troubleshoot your network from both a PC and a Cisco router (the commands might do the same thing, but they are implemented differently):
- Packet InterNet Groper (ping) Uses an Internet Control Message Protocol (ICMP) echo request and replies to test if a host IP stack is initialized and alive on the network.
TracerouteDisplays the list of routers on a path to a network destination by using time to live (TTL) time-outs and ICMP error messages. This command will work on a router, MAC, or Linux box, but not from a Windows command prompt.TracertSame command astraceroute, but it's a Microsoft Windows command and will not work on other devices, like a Cisco router or macOS or Linux box.arp -aDisplays IP–to–MAC-address mappings on a Windows PC.ipconfig /allUsed only from a command prompt. Shows you the PC network configuration.
Once you've gone through all these steps and used the appropriate command-line tools, if necessary, what do you do if you find a problem? How do you go about fixing an IP address configuration error? That's exactly what you're going to learn about next—how to determine specific IP address problems and what you can do to fix them.
Determining IP Address Problems
It's common for a host, router, or other network device to be configured with the wrong IP address, subnet mask, or default gateway. Because this happens way too often, I'm going to teach you how to both determine and fix IP address configuration errors.
Once you've worked through the four basic steps of troubleshooting and determined there's a problem, you obviously then need to find and fix it. It really helps to draw out the network and IP addressing scheme. If it's already done, consider yourself lucky and go buy a lottery ticket because although it should be done, it rarely is. And if it is, it's usually outdated or inaccurate anyway. Typically, it is not done, and you'll probably just have to bite the bullet and start from scratch.
Once you have your network accurately drawn out, including the IP addressing scheme, you need to verify each host's IP address, mask, and default gateway address to determine the problem. (I'm assuming that you don't have a physical problem or that if you did, you've already fixed it.)
Let's check out the example illustrated in Figure 8.4. A user in the sales department calls and tells you that she can't get to ServerA in the marketing department. You ask her if she can get to ServerB in the marketing department, but she doesn't know because she doesn't have rights to log on to that server. What do you do?
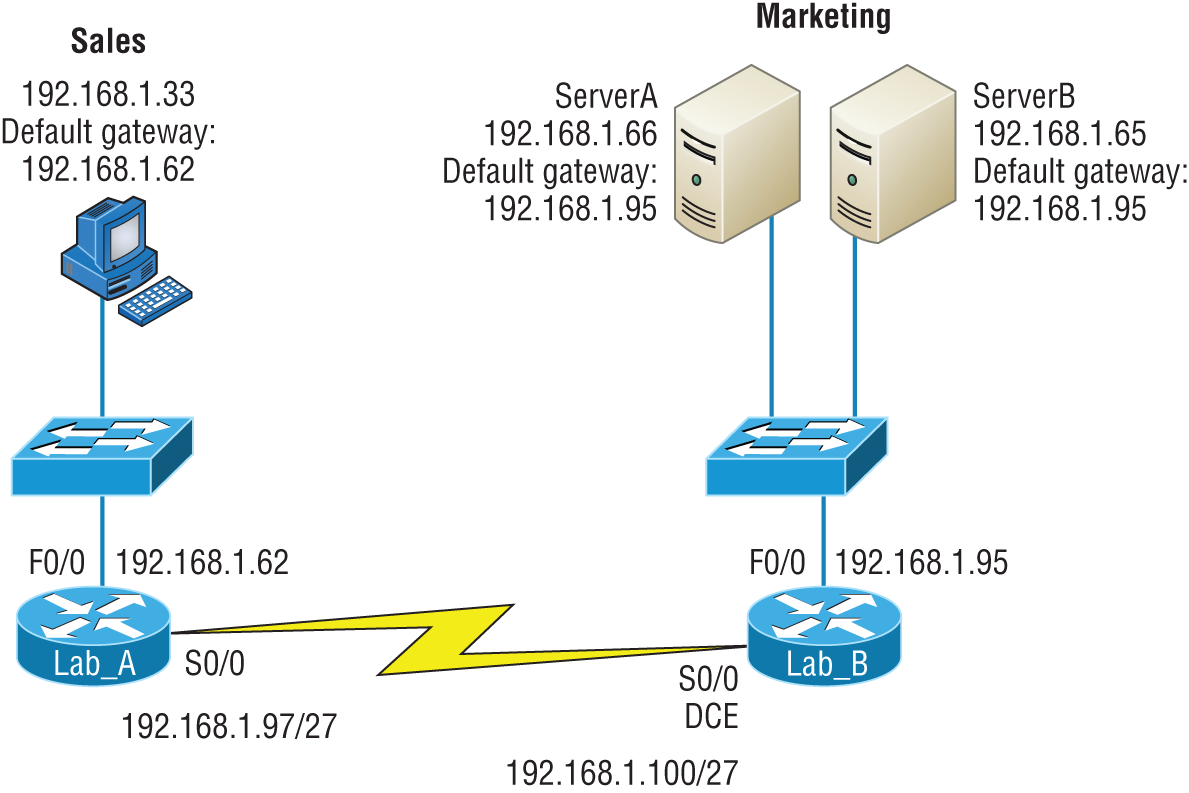
FIGURE 8.4 IP address problem 1
You ask the client to go through the four troubleshooting steps that you learned about in the preceding section. Steps 1 through 3 work, but step 4 fails. By looking at the figure, can you determine the problem? Look for clues in the network drawing. First, the WAN link between the Lab_A router and the Lab_B router shows the mask as a /27. You should already know that this mask is 255.255.255.224 and then determine that all networks are using this mask. The network address is 192.168.1.0. What are our valid subnets and hosts? 256 – 224 = 32, so this makes our subnets 0, 32, 64, 96, 128, and so on. So, by looking at the figure, you can see that subnet 32 is being used by the sales department, the WAN link is using subnet 96, and the marketing department is using subnet 64.
Now you have to determine what the valid host ranges are for each subnet. From what you learned at the beginning of this chapter, you should now be able to easily determine the subnet address, broadcast addresses, and valid host ranges. The valid hosts for the Sales LAN are 33 through 62—the broadcast address is 63 because the next subnet is 64, right? For the Marketing LAN, the valid hosts are 65 through 94 (broadcast 95), and for the WAN link, 97 through 126 (broadcast 127).
By looking at the figure, you can determine that the default gateway on the Lab_B router is incorrect. That address is the broadcast address of the 64 subnet, so there's no way it could be a valid host.
Did you get all that? Maybe we should try another one, just to make sure. Figure 8.5 shows a network problem. A user in the Sales LAN can't get to ServerB. You have the user run through the four basic troubleshooting steps and find that the host can communicate to the local network but not to the remote network. Find and define the IP addressing problem.
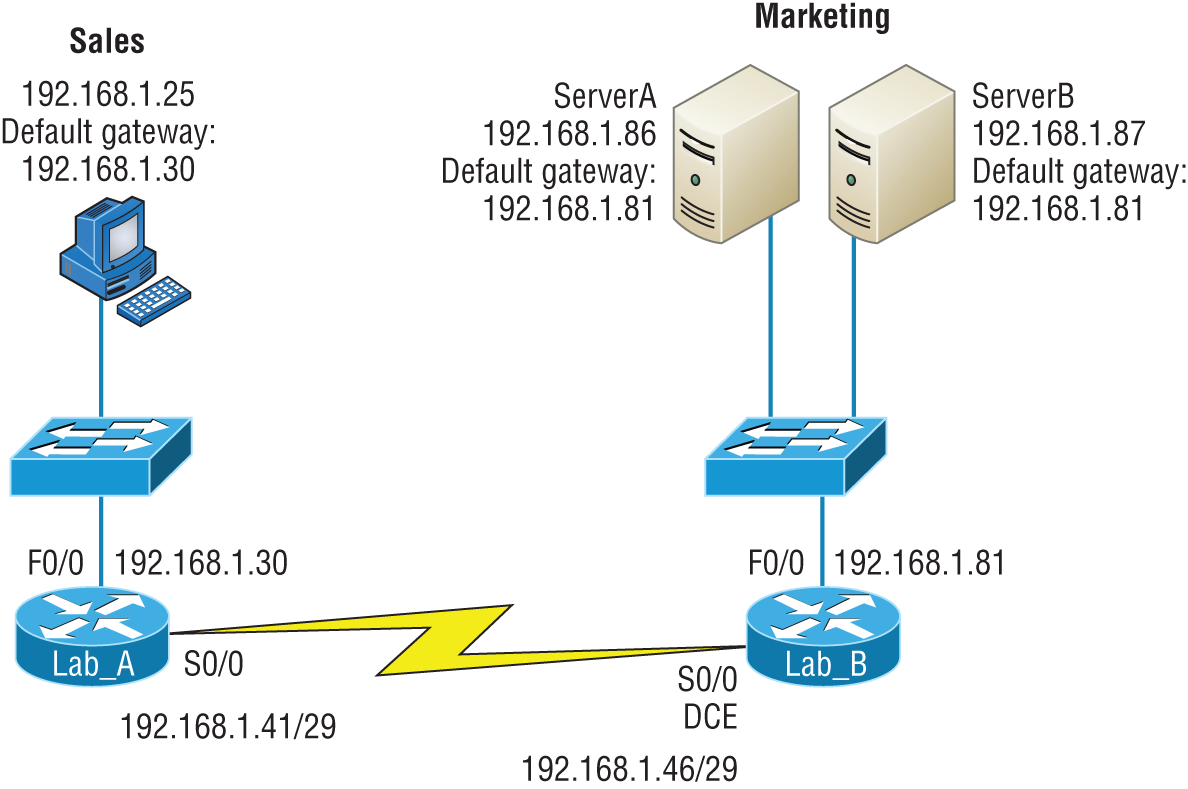
FIGURE 8.5 IP address problem 2
If you use the same steps used to solve the last problem, you can see first that the WAN link again provides the subnet mask to use— /29, or 255.255.255.248. You need to determine what the valid subnets, broadcast addresses, and valid host ranges are to solve this problem.
The 248 mask is a block size of 8 (256 – 248 = 8), so the subnets both start and increment in multiples of 8. By looking at the figure, you see that the Sales LAN is in the 24 subnet, the WAN is in the 40 subnet, and the Marketing LAN is in the 80 subnet. Can you see the problem yet? The valid host range for the Sales LAN is 25–30, and the configuration appears correct. The valid host range for the WAN link is 41–46, and this also appears correct. The valid host range for the 80 subnet is 81–86, with a broadcast address of 87 because the next subnet is 88. ServerB has been configured with the broadcast address of the subnet.
Now that you can figure out misconfigured IP addresses on hosts, what do you do if a host doesn't have an IP address and you need to assign one? What you need to do is look at other hosts on the LAN and figure out the network, mask, and default gateway. Let's take a look at a couple of examples of how to find and apply valid IP addresses to hosts.
You need to assign a server and router IP addresses on a LAN. The subnet assigned on that segment is 192.168.20.24/29, and the router needs to be assigned the first usable address and the server the last valid host ID. What are the IP address, mask, and default gateway assigned to the server?
To answer this, you must know that a /29 is a 255.255.255.248 mask, which provides a block size of 8. The subnet is known as 24, the next subnet in a block of 8 is 32, so the broadcast address of the 24 subnet is 31, which makes the valid host range 25–30:
- Server IP address: 192.168.20.30
- Server mask: 255.255.255.248
- Default gateway: 192.168.20.25 (router's IP address)
As another example, let's take a look at Figure 8.6 and solve this problem.
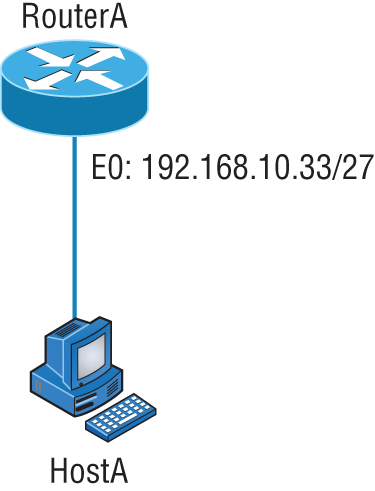
FIGURE 8.6 Find the valid host.
Look at the router's IP address on Ethernet0. What IP address, subnet mask, and valid host range could be assigned to the host?
The IP address of the router's Ethernet0 is 192.168.10.33/27. As you already know, a /27 is a 224 mask with a block size of 32. The router's interface is in the 32 subnet. The next subnet is 64, so that makes the broadcast address of the 32 subnet 63 and the valid host range 33–62:
- Host IP address: 192.168.10.34–62 (any address in the range except for 33, which is assigned to the router)
- Mask: 255.255.255.224
- Default gateway: 192.168.10.33
Figure 8.7 shows two routers with Ethernet configurations already assigned. What are the host addresses and subnet masks of hosts A and B?
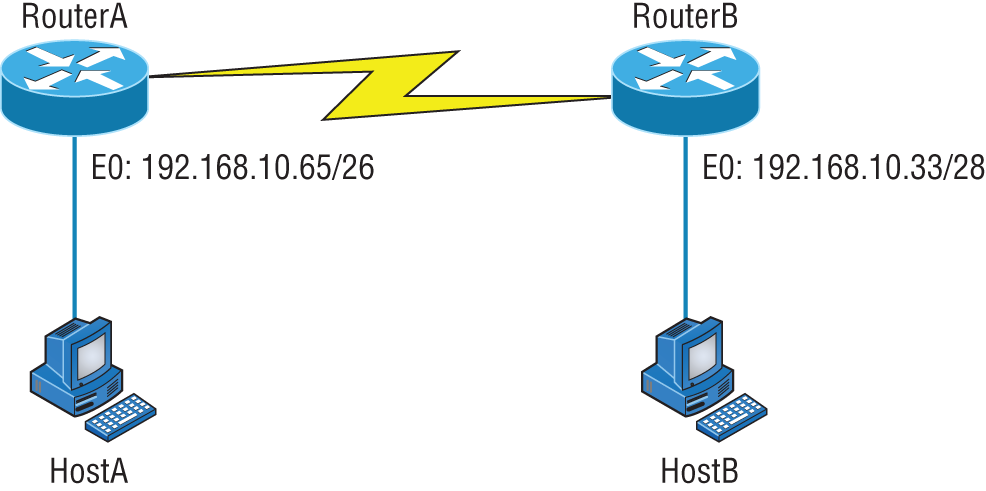
FIGURE 8.7 Find the valid host #2.
RouterA has an IP address of 192.168.10.65/26 and RouterB has an IP address of 192.168.10.33/28. What are the host configurations? RouterA Ethernet0 is in the 192.168.10.64 subnet, and RouterB Ethernet0 is in the 192.168.10.32 network:
- HostA IP address: 192.168.10.66–126
- HostA mask: 255.255.255.192
- HostA default gateway: 192.168.10.65
- HostB IP address: 192.168.10.34–46
- HostB mask: 255.255.255.240
- HostB default gateway: 192.168.10.33
Just a couple more examples, and then this section is history. Hang in there!
Figure 8.8 shows two routers; you need to configure the S0/0 interface on RouterA. The network assigned to the serial link is 172.16.16.0/22. What IP address can be assigned?
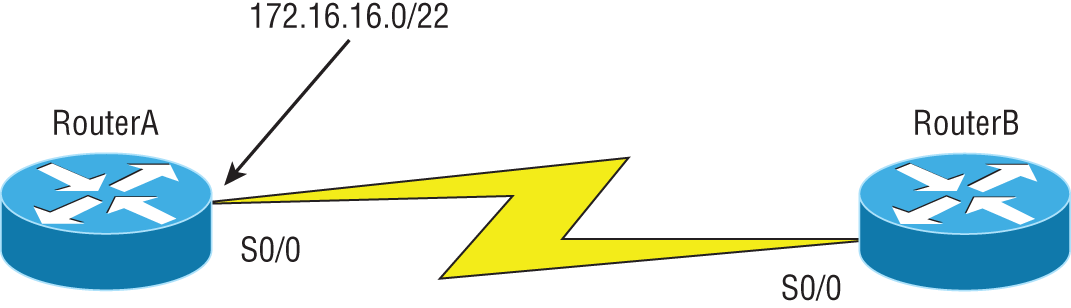
FIGURE 8.8 Find the valid host address #3.
First, you must know that a /22 CIDR is 255.255.252.0, which makes a block size of 4 in the third octet. Because 16 is listed, the available range is 16.1 through 19.254; so, for example, the IP address S0/0 could be 172.16.18.255 because that's within the range.
Okay, last one! You have one Class C network ID, and you need to provide one usable subnet per city while allowing enough usable host addresses for each city specified in Figure 8.9. What is your mask?
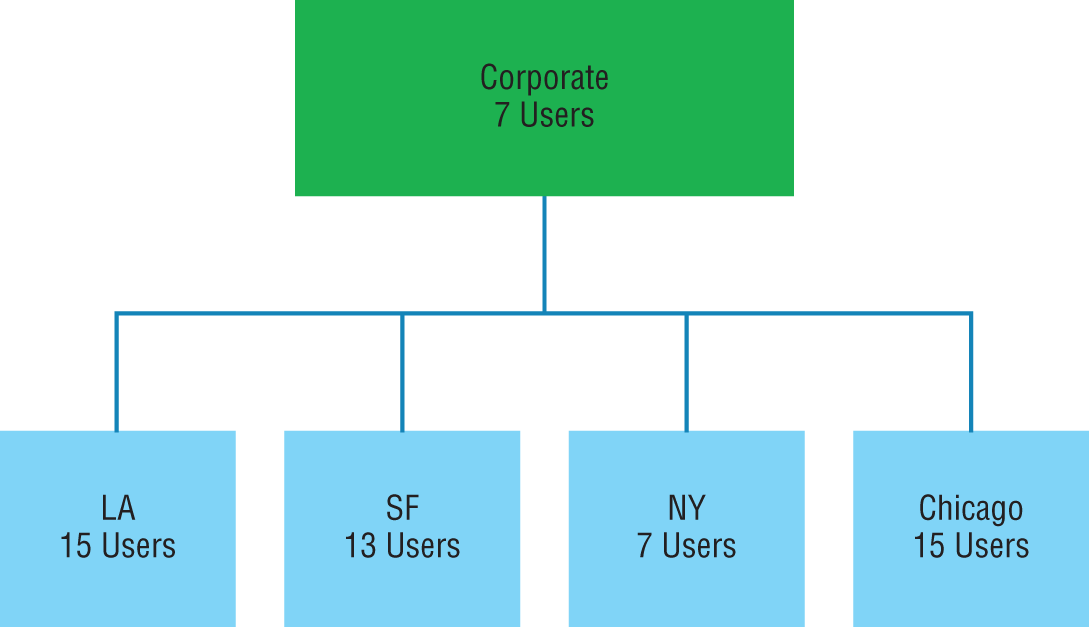
FIGURE 8.9 Find the valid subnet mask.
Actually, this is probably the easiest thing you've done all day! I count 5 subnets needed, and the Chicago office needs 15 users (always look for the network that needs the most hosts). What block size is needed for the Chicago office? 32. (Remember, you cannot use a block size of 16 because you always have to subtract 2!) What mask provides you with a block size of 32? 224. Bingo! This provides 8 subnets, each with 30 hosts.
Introduction to Network Address Translation (NAT)
Similar to Classless Inter-Domain Routing (CIDR), the original intention for NAT was to slow the depletion of available IP address space by allowing many private IP addresses to be represented by some smaller number of public IP addresses.
Since then, it's been discovered that NAT is also a useful tool for network migrations and mergers, server load sharing, and creating “virtual servers.” So I'm going to describe the basics of NAT functionality and the terminology common to NAT.
At times, NAT really decreases the overwhelming amount of public IP addresses required in your networking environment. And NAT comes in very handy when two companies that have duplicate internal addressing schemes merge. NAT is also great to have around when an organization changes its ISP and the networking manager doesn't want the hassle of changing the internal address scheme.
Here's a list of situations in which it's best to have NAT on your side:
- You need to connect to the Internet and your hosts don't have globally unique IP addresses.
- You change to a new ISP that requires you to renumber your network.
- You need to merge two intranets with duplicate addresses.
You typically use NAT on a border router. For an illustration of this, see Figure 8.10, where NAT would be configured on the Corporate router.
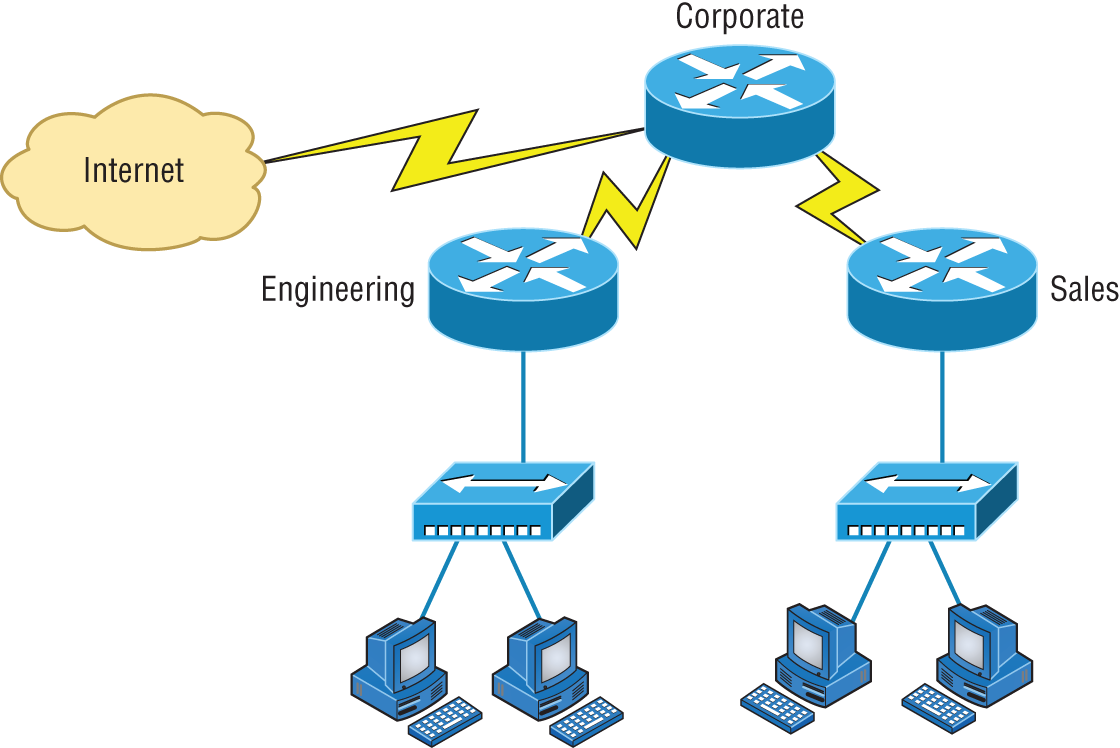
FIGURE 8.10 Where to configure NAT
Now you may be thinking, “NAT's totally cool. It's the grooviest, greatest network gadget, and I just gotta have it.” Well, hang on a minute. There are truly some serious snags related to NAT use. Oh, don't get me wrong: It really can save you sometimes, but there's a dark side you need to know about too. For a visual of the pros and cons linked to using NAT, check out Table 8.3.
TABLE 8.3 Advantages and disadvantages of implementing NAT
| Advantages | Disadvantages |
|---|---|
| Conserves legally registered addresses. | Translation introduces switching path delays. |
| Reduces address overlap occurrences. | Loss of end-to-end IP traceability. |
| Increases flexibility when connecting to the Internet. | Certain applications will not function with NAT enabled. |
| Eliminates address renumbering as the network changes. |
Types of Network Address Translation
In this section, I'm going to go over the three types of NAT with you:
- Static NAT (SNAT) This type of NAT is designed to allow one-to-one mapping between local and global addresses. Keep in mind that the static version requires you to have one real Internet IP address for every host on your network.
- Dynamic NAT (DNAT) This version gives you the ability to map an unregistered IP address to a registered IP address from a pool of registered IP addresses. You don't have to statically configure your router to map an inside-to-an-outside address as you would using static NAT, but you do have to have enough real, bona fide IP addresses for everyone who's going to be sending packets to and receiving them from the Internet.
- Overloading This is the most popular type of NAT configuration. Understand that overloading really is a form of dynamic NAT that maps multiple unregistered IP addresses to a single registered IP address—many-to-one—by using different ports. Now, why is this so special? Well, because it's also known as port address translation (PAT). And by using PAT (NAT Overload), you get to have thousands of users connect to the Internet using only one real global IP address—pretty slick, yeah? Seriously, NAT Overload is the real reason we haven't run out of valid IP address on the Internet. Really—I'm not joking.
NAT Names
The names we use to describe the addresses used with NAT are pretty simple. Addresses used after NAT translations are called global addresses. These are usually the public addresses used on the Internet, but remember, you don't need public addresses if you aren't going on the Internet.
Local addresses are the ones we use before network translation. So, the inside local address is actually the private address of the sending host that's trying to get to the Internet, while the outside local address is the address of the destination host. The latter is usually a public address (web address, mail server, and so on) and is how the packet begins its journey.
After translation, the inside local address is then called the inside global address, and the outside global address then becomes the name of the destination host. Check out Table 8.4, which lists all this terminology, for a clear picture of the various names used with NAT.
TABLE 8.4 NAT terms
| Name | Meaning |
|---|---|
| Inside local | Name of the inside source address before translation |
| Outside local | Name of the destination host before translation |
| Inside global | Name of the inside host after translation |
| Outside global | Name of the outside destination host after translation |
How NAT Works
Now it's time to look at how this whole NAT thing works. I'm going to start by using Figure 8.11 to describe the basic translation of NAT.
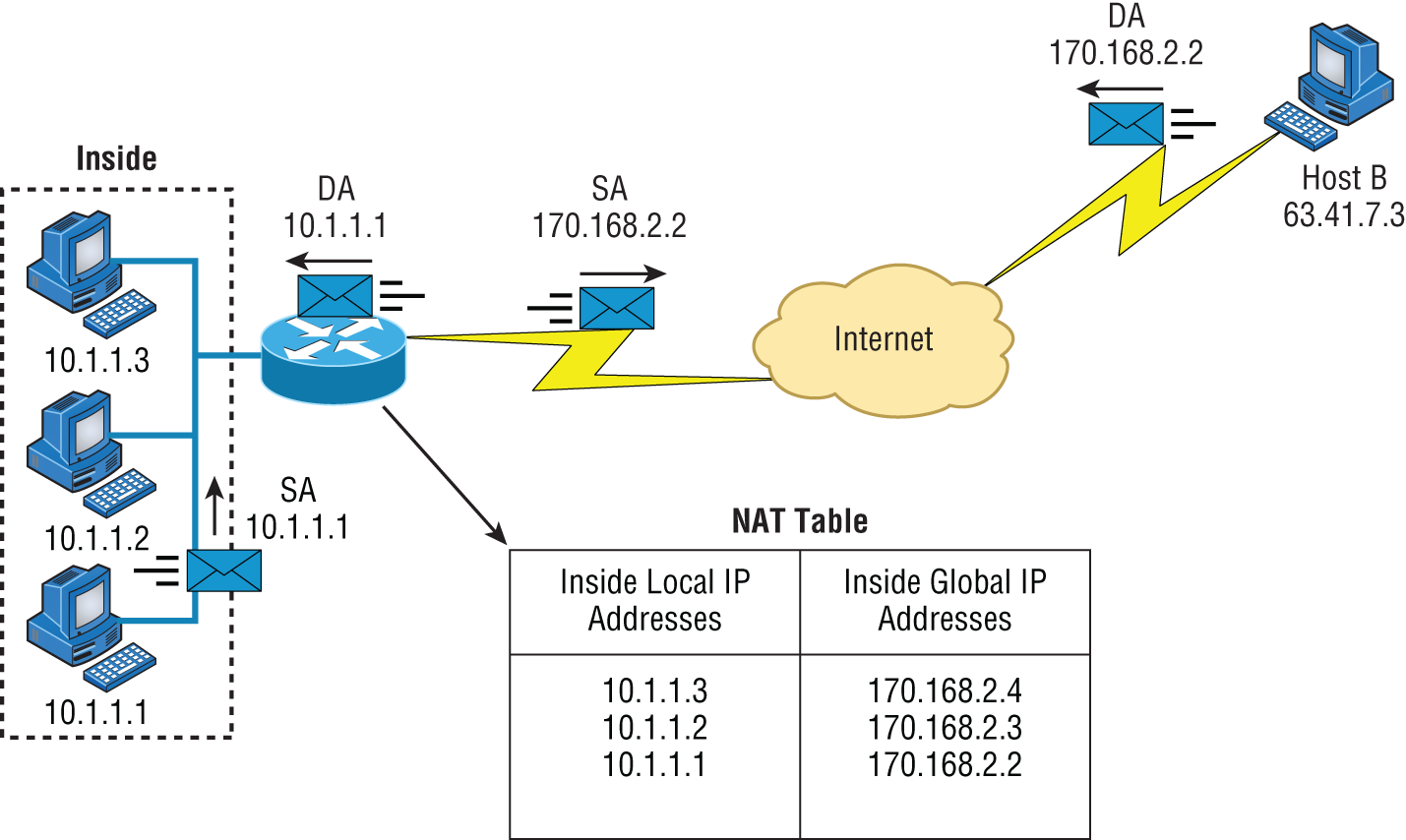
FIGURE 8.11 Basic NAT translation
In the example shown in Figure 8.11, host 10.1.1.1 sends an outbound packet to the border router configured with NAT. The router identifies the IP address as an inside local IP address destined for an outside network, translates the address, and documents the translation in the NAT table.
The packet is sent to the outside interface with the new translated source address. The external host returns the packet to the destination host, and the NAT router translates the inside global IP address back to the inside local IP address using the NAT table. This is as simple as it gets.
Let's take a look at a more complex configuration using overloading, or what is also referred to as PAT. I'll use Figure 8.12 to demonstrate how PAT works.
With overloading, all inside hosts get translated to one single IP address, hence the term overloading. Again, the reason we have not run out of available IP addresses on the Internet is because of overloading (PAT).
Take a look at the NAT table in Figure 8.12 again. In addition to the inside local IP address and outside global IP address, we now have port numbers. These port numbers help the router identify which host should receive the return traffic.
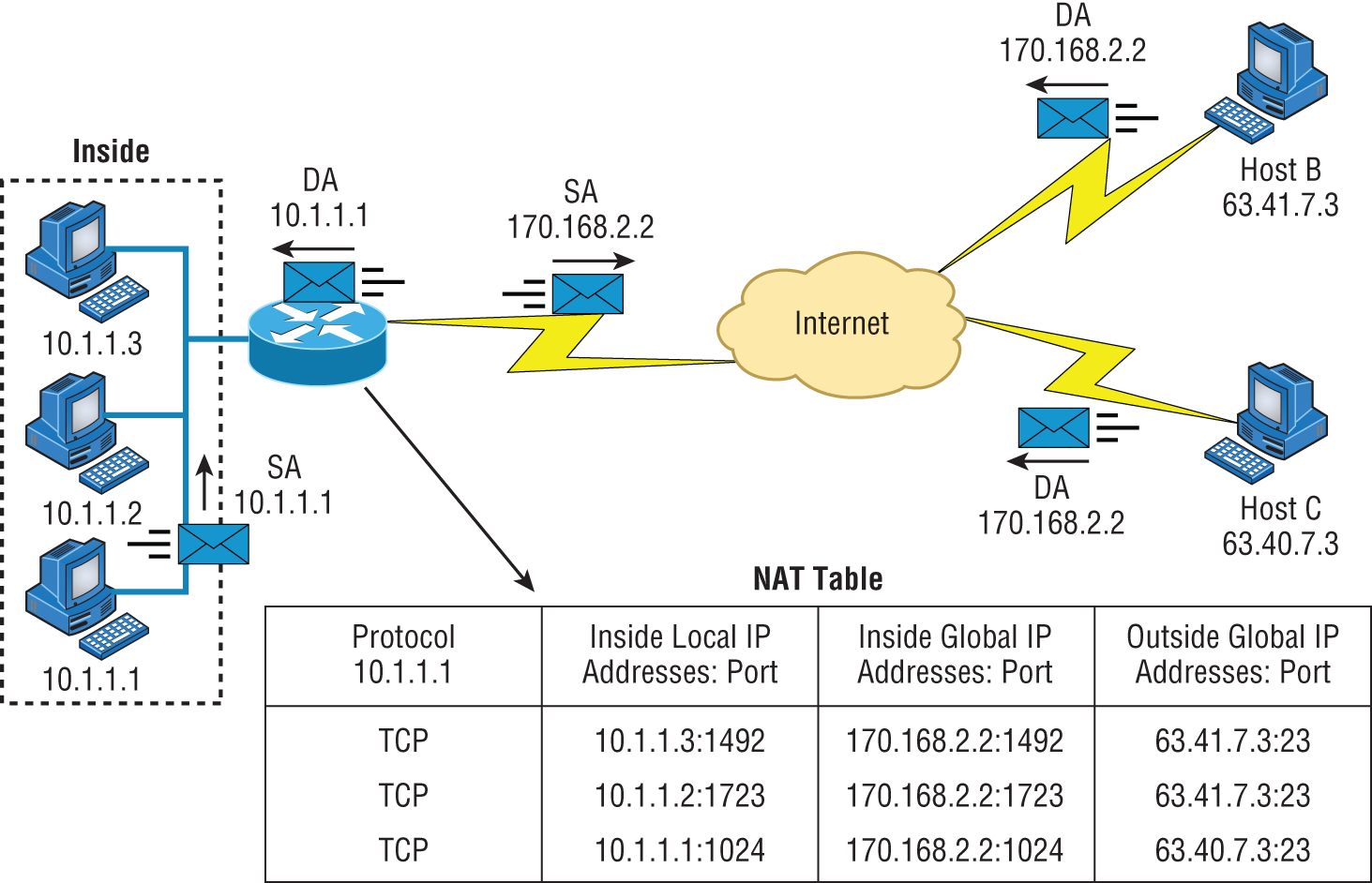
FIGURE 8.12 NAT overloading example (PAT)
Port numbers are used at the Transport layer to identify the local host in this example. If we had to use IP addresses to identify the source hosts, that would be called static NAT, and we would run out of addresses. PAT allows us to use the Transport layer to identify the hosts, which in turn allows us to use (theoretically) up to 65,000 hosts with one real IP address.
One last thing: We've been discussing translating IP addresses using some type of network address translation. However, using a router or firewall, you can also perform port forwarding, which is translating the port number of a packet to a new destination. The destination may be a predetermined network port (using any IP protocol, but typically TCP or UDP ports) on a host within a private network behind a NAT router. Based on the received port number, a remote host can communicate to servers behind the NAT gateway to the local network.
You're done, the diva has sung, the chicken has crossed the road … whew! Take a good break, and then come back and go through the written lab and review questions.
Summary
Did you read Chapter 7 and this chapter and understand everything on the first pass? If so, that is fantastic—congratulations! The thing is, you probably got lost a couple of times—and as I told you, that's what usually happens, so don't stress. Don't feel bad if you have to read each chapter more than once, or even 10 times, before you're truly good to go.
This chapter provided you with an important understanding of IP subnetting. After reading this chapter, you should be able to subnet IP addresses in your head.
You should also understand the basic troubleshooting methods. You must remember the four steps you take when trying to narrow down exactly where a network/IP addressing problem is and then know how to proceed systematically in order to fix it. In addition, you should be able to find valid IP addresses and subnet masks by looking at a network diagram.
I finished this chapter with an introduction to network address translation. I discussed the difference between static and dynamic NAT and NAT overloading (PAT).
Exam Essentials
Remember the steps to subnet in your head. Understand how IP addressing and subnetting work. First, determine your block size by using the 256-subnet mask math. Then, count your subnets and determine the broadcast address of each subnet—it is always the number right before the next subnet. Your valid hosts are the numbers between the subnet address and the broadcast address.
Understand the various block sizes. This is an important part of understanding IP addressing and subnetting. The valid block sizes are always 4, 8, 16, 32, 64, 128, and so on. You can determine your block size by using the 256-subnet mask math.
Remember the four diagnostic steps. The four simple steps for troubleshooting are ping the loopback address, ping the NIC, ping the default gateway, and ping the remote device.
You must be able to find and fix an IP addressing problem. Once you go through the four troubleshooting steps, you should be able to determine the IP addressing problem by drawing out the network and finding the valid and invalid hosts addressed in your network.
Understand basic NAT terminology. You want to know the difference between inside local and inside global. Inside local is before translation, and inside global is after translation. Inside global is defined as a registered address that represents an inside host to an outside network. You should also understand PAT and how it works by using different port numbers to map multiple private IP addresses to a single registered IP address.
Written Lab
You can find the answers to the written labs in Appendix A.
Write the subnet mask, subnet address, broadcast address, and valid host range for question 1 through question 6:
- 192.168.100.25/30
- 192.168.100.37/28
- 192.168.100.66/27
- 192.168.100.17/29
- 192.168.100.99/26
- 192.168.100.99/25
- You have a Class B network and need 29 subnets. What is your mask?
- What is the broadcast address of 192.168.192.10/29?
- How many hosts are available with a Class C /29 mask?
- What is the subnet for host ID 172.16.3.65/23?
Review Questions
You can find the answers to the review questions in Appendix B.
- What is the maximum number of IP addresses that can be assigned to hosts on a local subnet that uses the 255.255.255.224 subnet mask?
- 14
- 15
- 16
- 30
- 31
- 62
- You have a Class A host of 10.0.0.110/25. It needs to communicate to a host with an IP address of 10.0.0.210/25. Which of the following devices do you need to use in order for these hosts to communicate?
- A layer 2 switch
- Router
- DNS server
- Hub
- What is the subnetwork address for a host with the IP address 200.10.5.68/28?
- 200.10.5.56
- 200.10.5.32
- 200.10.5.64
- 200.10.5.0
- The network address of 172.16.0.0/19 provides how many subnets and hosts?
- 7 subnets, 30 hosts each
- 7 subnets, 2,046 hosts each
- 7 subnets, 8,190 hosts each
- 8 subnets, 30 hosts each
- 8 subnets, 2,046 hosts each
- 8 subnets, 8,190 hosts each
- You receive a call from a user who is complaining that they cannot get on the Internet. You have them verify their IP address, mask, and default gateway. The IP address is 10.0.37.144, with a subnet mask of 255.255.254.0. The default gateway is 10.0.38.1. What is the problem?
- Incorrect DNS server address
- Invalid subnet mask
- Incorrect gateway IP
- IP address and mask not compatible
- If a host on a network has the address 172.16.45.14/30, what is the subnetwork this host belongs to?
- 172.16.45.0
- 172.16.45.4
- 172.16.45.8
- 172.16.45.12
- 172.16.45.16
- On a network, which mask should you use on point-to-point WAN links in order to reduce the waste of IP addresses?
- /27
- /28
- /29
- /30
- /31
- On which of the following devices are you most likely to be able to implement NAT?
- Hub
- Ethernet switch
- Router
- Bridge
- You have an interface on a router with the IP address of 192.168.192.10/29. Including the router interface, how many hosts can have IP addresses on the LAN attached to the router interface?
- 6
- 8
- 30
- 62
- 126
- When configuring the IP settings on a computer on one subnet to ensure that it can communicate with a computer on another subnet, which of the following is desirable?
- Configure the computer with the same default gateway as the other computer.
- Configure the computer with the same subnet mask as the other computer.
- Configure the computer with a default gateway that matches the IP address of the interface of the router that is attached to the same subnet as the computer.
- Configure the computer with a subnet mask that matches the IP address of the interface of the router that is attached to the same subnet as the computer.
- You have an interface on a router with the IP address of 192.168.192.10/29. What is the broadcast address the hosts will use on this LAN?
- 192.168.192.15
- 192.168.192.31
- 192.168.192.63
- 192.168.192.127
- 192.168.192.255
- What is the highest usable address on the 172.16.1.0/24 network?
- 172.16.1.255
- 172.16.1.254
- 172.16.1.253
- 172.16.1.23
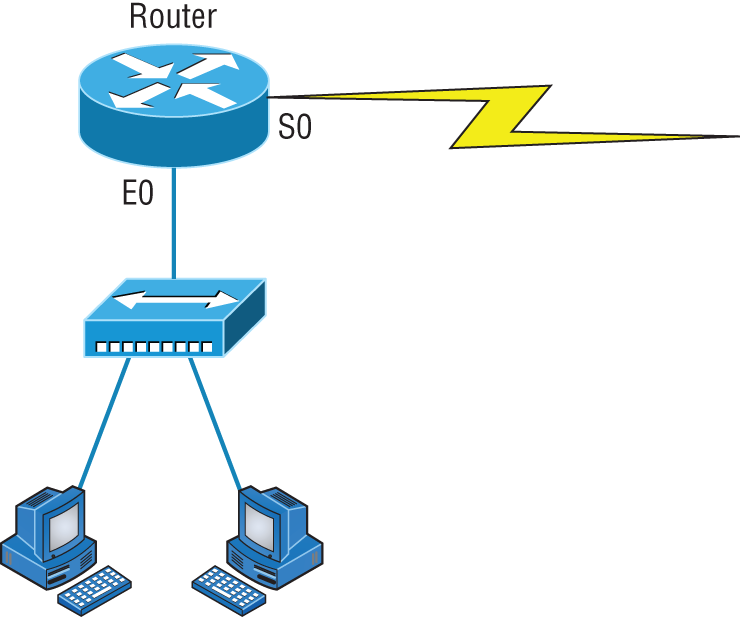
- A network administrator is connecting two hosts directly through their Ethernet interfaces, as shown in the illustration. Ping attempts between the hosts are unsuccessful. What can be done to provide connectivity between the hosts? (Choose two.)
- A crossover cable should be used in place of the straight-through cable.
- A rollover cable should be used in place of the straight-through cable.
- The subnet masks should be set to 255.255.255.192.
- A default gateway needs to be set on each host.
- The subnet masks should be set to 255.255.255.0.
- If an Ethernet port on a router was assigned an IP address of 172.16.112.1/25, what would be the subnet address of this host?
- 172.16.112.0
- 172.16.0.0
- 172.16.96.0
- 172.16.255.0
- 172.16.128.0
- Using the following illustration, what would be the IP address of E0 if you were using the eighth subnet? The network ID is 192.168.10.0/28, and you need to use the last available IP address in the range. The 0 subnet should not be considered valid for this question.
- 192.168.10.142
- 192.168.10.66
- 192.168.100.254
- 192.168.10.143
- 192.168.10.126
- Using the illustration in question 15, what would be the IP address of E0 if you were using the first subnet? The network ID is 192.168.10.0/28, and you need to use the last available IP address in the range. Again, the 0 subnet should not be considered valid for this question.
- 192.168.10.24
- 192.168.10.62
- 192.168.10.30
- 192.168.10.127
- If you are forced to replace a router that has failed to the point that you are unable to access its current configuration to aid in setting up interface addresses on the new router, which of the following can you reference for assistance?
- The default gateway settings on computers from each subnet that the old router interconnected.
- The router's configuration that was periodically cached on the DHCP server.
- The router's configuration that was periodically cached on the DNS server.
- The new router will auto-configure itself with the correct settings.
- You have a network with a subnet of 172.16.17.0/22. Which of the following is a valid host address?
- 172.16.17.1 255.255.255.252
- 172.16.0.1 255.255.240.0
- 172.16.20.1 255.255.254.0
- 172.16.16.1 255.255.255.240
- 172.16.18.255 255.255.252.0
- 172.16.0.1 255.255.255.0
- Your router has the following IP address on Ethernet0: 172.16.2.1/23. Which of the following can be valid host IDs on the LAN interface attached to the router? (Choose two.)
- 172.16.0.5
- 172.16.1.100
- 172.16.1.198
- 172.16.2.255
- 172.16.3.0
- 172.16.3.255
- You have one IP address provided from your ISP with a /30 mask. However, you have 300 users that need to access the Internet. What technology will you use to implement a solution?
- PAT
- VPN
- DNS
- LANs
