60
A Practical Guide to Security Assessments
exists. If the need were determined to be valid, the assessment would have also
flagged the need for additional resources to administer the system or the possibility
of outsourcing the function.
D
ETERMINING
M
EASURES
TO
T
AKE
TO
A
DDRESS
A
NY
R
EGULATORY
C
ONCERNS
Unlike the financial statements of publicly traded companies, which have to be
audited by a third-party firm and where certain statements are filed with the Securities
and Exchange Commission (SEC), most companies have no such regulatory require-
ment related to having their information security evaluated. For some industries,
however, the government has felt compelled to pass laws to protect individuals’
personal information. Two such laws that have been touched on already are the
HIPAA (Health Insurance Portability and Accountability Act) and the GLBA
(Gramm–Leach–Bliley Act).
HIPAA applies to health care–related companies, and part of this regulation is
focused on information security. At a high level, this law mandates that health
care–related companies have information security programs in place that reasonably
protect patients’ personally identifiable information (in electronic form). All aspects
of an information security program, ranging from security policies and procedures,
risk analysis, and awareness at the foundation level to different technologies that
support the security policies, must be present.
GLBA does something similar for financial services companies. GLBA requires
financial service companies to have adequate security measures in place to protect
the privacy of customer information. The regulations also cover what institutions
may and may not do with customer information. Also, similar to HIPAA, the law,
at a high level, essentially requires a sound information security program.
The potential liabilities that health care and financial services companies face
are enough in themselves to make them want to put good security measures in place.
Legislation and the related threats are a clear justification for ensuring that related
security requirements are in place.
The Federal Trade Commission (FTC) is taking a very active role in holding
companies accountable for claims they make regarding security and privacy. The
FTC has gone after many companies that have not provided a reasonable level of
security based on claims companies have made.
With these laws in place, one of the challenges companies are having today is
that it is not clear what is required to be in compliance — i.e., they do not know,
from a governmental audit perspective, what is necessary to be compliant with
legislation. As the U.S. government does more audits against these laws, the inter-
pretation will become clearer. More importantly, empirical data related to the sizes
of the fines will also be established making quantification of risk easier. A security
assessment with a focus on meeting the requirements of these pieces of legislation
is a useful tool in determining where the gaps are and what needs to be done to
achieve compliance.
Besides these two laws, a number of other pieces of legislation affect companies
from an information security perspective. Information security professionals can
AU1706_book.fm Page 60 Wednesday, July 28, 2004 11:06 AM
The Information Security Program and How a Security Assessment Fits In
61
bring this type of expertise to the table to help ensure that companies are in com-
pliance with legislation that affects them. Information security legislation is dis-
cussed in greater detail in Chapter 10 of this book.
J
USTIFICATION
FOR
F
UNDS
In many companies, information security is perceived to be an expensive proposition.
Information security programs often introduce new processes, which many perceive
as being cumbersome or not worth doing. Information security programs also intro-
duce security-related technology that could be very expensive to purchase, imple-
ment, and manage.
In today’s environment, obtaining funds from shrinking budgets is no easy task.
With information security–related spending, it is even worse because people do not
necessarily see the value of it. For management, information security measures are
sometimes viewed as “nice to haves” instead of “must haves.”
Security assessments can provide this justification and demonstrate the value of
information security. Remember that recommendations are developed as a result of
the security assessment process and that recommendations should link back to
security risks identified. The negative impacts associated with those risks can help
demonstrate the value of implementing information security measures. This link
between business process, risk, impact, and recommendation can help show manage-
ment why it is important to provide funds for security measures. In this scenario,
information security can be viewed as a way to control potential costs related to
security incidents.
Another aspect to consider is looking at information security as a “revenue
enhancer.” An example of where security is a revenue enhancer is e-commerce.
Companies that generate revenues through e-commerce activities know that one of
the main considerations for consumers when shopping online is the security of their
personal information — e.g., name, address, and credit card information. Security
as it pertains to e-commerce can be viewed in two ways:
First, inadequate security measures can lead to a security breach where
consumers’ information is compromised resulting in short-term loss of
revenue because consumers would be hesitant to shop with that company.
More importantly, it would also result in some permanent loss of customers
leading to a long-term negative impact on revenue. This, by itself, is a
compelling case that justifies strong information security measures for
e-commerce.
Second, a security certification (e.g., BBB
OnLine
) might be worth spending
money on because it is something that might bring customers to an e-
commerce site. Customers might look for some third-party certification,
and it might be the criterion that determines whether a consumer will shop
at a site. The e-commerce company would suffer against its competitors if
it did not have the third-party seal that its competitors have. In this scenario,
spending on information security can be viewed as a “revenue enhancer.”
AU1706_book.fm Page 61 Wednesday, July 28, 2004 11:06 AM
62
A Practical Guide to Security Assessments
Companies often perform security assessments because IT management is look-
ing for a third party to help justify information security initiatives. Revenue enhance-
ment as a reason is very compelling and in that case, the questions will center around
what would happen if those measures were not taken and how quickly the investment
in the information security initiative will pay off. Return on Investment (ROI) is
something to think about when proposing a security solution and is something that
can be difficult when trying to demonstrate the probability that something might
happen.
Risk analysis and the concept of ROI are discussed in detail in Chapter 8 —
Risk Analysis and Final Presentation.
THE SECURITY ASSESSMENT PROCESS
We now have an understanding of information security programs and how security
assessments fit in. We also know some reasons why companies would potentially
conduct a security assessment. As with other processes, it is critical to have a
methodology for conducting a security assessment to ensure that:
• Assessments are performed in an efficient manner.
• The process facilitates the gathering and analysis of all relevant information.
• Assessments provide the client with a “security roadmap” that can be used
to improve the information security program.
Assessments can take time and require the time of staff from the client. Because
client personnel are busy people, the assessment methodology must be adequately
refined to use time efficiently. Assessments are intrusive to some degree because
employees from the client who are involved must take time from their daily respon-
sibilities to provide the information necessary for an assessment. Therefore, its
important that time with them is efficiently used to gather the information required.
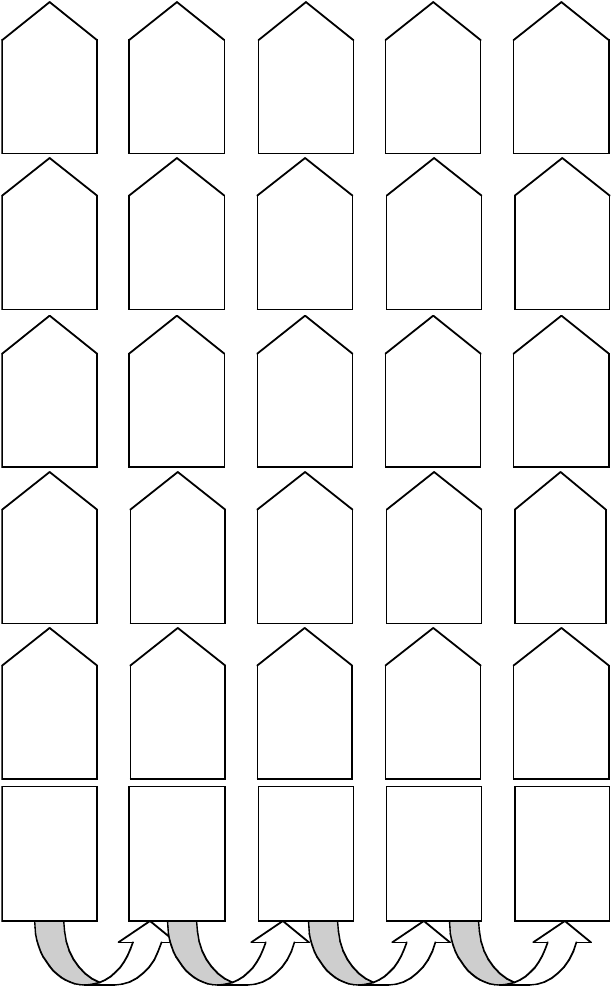
The next five chapters will provide a detailed discussion of a methodology for
conducting security assessments. Figure 3.9 illustrates that methodology. The dia-
gram details each of the phases along with the specific steps in each phase. The
methodology is meant to be followed so that each of the steps in each phase is
completed before beginning the next phase (with some exceptions). The approach
is flexible and provides a structure around conducting assessments.
The five key phases and key tasks in each phase are:
•
Planning —
Define the scope, logistics, and scheduling.
•
Initial Preparation —
Gather publicly available information; prepare ini-
tial documentation.
•
Business Process Evaluation —
Gain understanding of the key business
processes; meet with business process owners; identify critical supporting
technologies.
•
Technology Evaluation —
Test critical technologies.
•
Risk Analysis and Final Presentation
— Quantify risks and develop
recommendations.
AU1706_book.fm Page 62 Wednesday, July 28, 2004 11:06 AM
The Information Security Program and How a Security Assessment Fits In
63
FIGURE 3.9
Security assessment methodology.
Planning
Initial
Information
Gathering
Define scope
Staffing
Kickoff meeting
Develop project
plan
Set client
expectations
Gather publicly
available
information
Gather
information from
the client
Analyze gathered
information
Business
Process
Evaluation
General review of
company and key
business processes
Finalize question
sets for process
reviews
Meet with
business process
owners
Analyze
information
collected and
document findings
Status meeting
with client
Technology
Evaluation
General review of
technology and
related
documentation
Develop question
sets for technology
reviews
Meet with
technology owners
and conduct hands
on testing
Analyze
information
collected and
document findings
Status meeting
with client
Risk Analysis
and Final
Presentation
Risk analysis &
Risk Score
calculation
Finalize findings
and risks
Develop
recommendations
and prepare draft
report
Discuss draft
report with client
Prepare initial
question sets
Develop and
populate template
for final report
Present final
report to
management
AU1706_book.fm Page 63 Wednesday, July 28, 2004 11:06 AM
64
A Practical Guide to Security Assessments
Many readers of this book have probably carried out some or most of this
methodology. The presentation here will put that methodology into a structured
format, where each step of the assessment is clear and where it is easy to see exactly
where you are in the process at any given time. The discussion of the methodology
will also show why each of the steps is important. As you go through the next five
chapters and read the details of the methodology, keep these key points to in mind:
•
The methodology is flexible.
Security assessments will rarely go exactly
the way the methodology is laid out, so you need to be flexible. The
methodology is meant to be flexible to allow for such things as scheduling
conflicts or resource issues. For example, the client may ask you to do
the first two phases, Planning and Initial Information Gathering, in a
compressed time frame in which some steps may not be performed as
thoroughly as you like (or maybe not at all). In this case, the other phases
might take longer because you were not able to do as much preparation
as you would have liked. The methodology is meant to provide a frame-
work within which you can work, and at times you will have to be flexible
with the steps, which is acceptable, as long as you stay within the general
framework of this methodology.
•
Steps can be combined.
In some cases, you may be able to combine steps.
If this can be done and it makes the process more efficient, then it should
be done. For example, consider a security assessment for a small company,
where you only conduct a handful of interviews. In this case, the last three
steps of the planning phase — holding the kickoff meeting, developing
the project plan, and setting client expectations — might all be performed
together because the scope of work might be very limited. Part of the
kickoff meeting can be used to go over a rough project plan consisting
of interviews and system testing. You can also set the client’s expectations
regarding the assessment in the same meeting. The point is that each of
the steps should be addressed. You should take advantage of opportunities
to combine steps and make the process more efficient.
•
Understanding the business is fundamental.
The basis for this methodol-
ogy is that a security assessment starts with having a solid understanding
of the business. You will read this time and again in this book. A funda-
mental aspect of this methodology is that you cannot understand the
criticality of security risks without understanding the business and the
mission-critical business processes. The methodology stresses the point
that the business drives security and not the other way around.
•
Communication with clients should be emphasized.
One of the common
steps in each of the phases of the methodology is communication with
the client. Clients should always be kept aware of the progress of the
assessment and of the findings that have been uncovered. This is important
for two reasons. First, clients have the opportunity to provide additional
information that might change the nature of a finding. Second, the client
is prepared to talk about it when the final report is presented to management.
AU1706_book.fm Page 64 Wednesday, July 28, 2004 11:06 AM
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
