Initial Information Gathering
123
If the client does not provide information during this phase, more time will have to
be spent on “learning” during interviews with client personnel. Although time
constraints or other external factors may not allow the proper amount of initial
preparation, every effort should be made to devote a reasonable amount of time to
it. As part of setting expectations with the client, you should explain the mutual
benefit of the initial preparation phase and how good preparation will increase the
overall quality of the security assessment.
ANALYZE GATHERED INFORMATION
At this point, you have enough information between the client meeting and the public
information to do some initial analysis. Although the knowledge is fresh, it is best
to analyze the information and determine whether you have any findings or other
pertinent information to be aware of for the rest of the security assessment (Figure 5.3).
The first thing you should do is document the key points of the conversation. If
you document it electronically, you might be able to use it when developing the
final deliverable. Also, the notes from the conversation are easier to share with other
members of the team if they are documented electronically. One of the areas where
significant time is wasted is when notes are taken by hand and you must spend time
two weeks later trying to make sense out of them. If you are not diligent about
documenting what you learn, you can become confused later in the process. If your
notes are good, this is not a problem, but for many this can waste significant time
later when conducting analysis. Remember that the notes from client meetings are
the justification for your analysis. If you are questioned later about why you came
to certain conclusions, you should be able to go back and say what the basis of the
conclusion was.
Once you document the conversation, you should do a quick analysis of the
information and further refine your planning for the fieldwork phases of the security
assessment. If you were able to have a good discussion with the client, it is possible
that some findings already have begun to surface and if so, they should be docu-
mented. When documenting the potential findings, try to also determine the risk. This
documentation is preliminary and will be refined in later stages of the assessment.
Anything you can document now will be a big help to you later.
In summary, the main goals for this step include:
• Document the conversation with the client.
• Document any relevant information gained by searching publicly available
information.
• Document any potential findings.
• Determine how the information you have learned can be used to modify
the question sets, which are prepared in the next step.
PREPARE INITIAL QUESTION SETS
Question sets (Figure 5.4) will be used to facilitate meetings with business process
owners in the next two phases of the assessment — business process review
(Chapter 6) and technology review (Chapter 7). At this point in the assessment, you
AU1706_book.fm Page 123 Tuesday, August 17, 2004 11:02 AM
124 A Practical Guide to Security Assessments
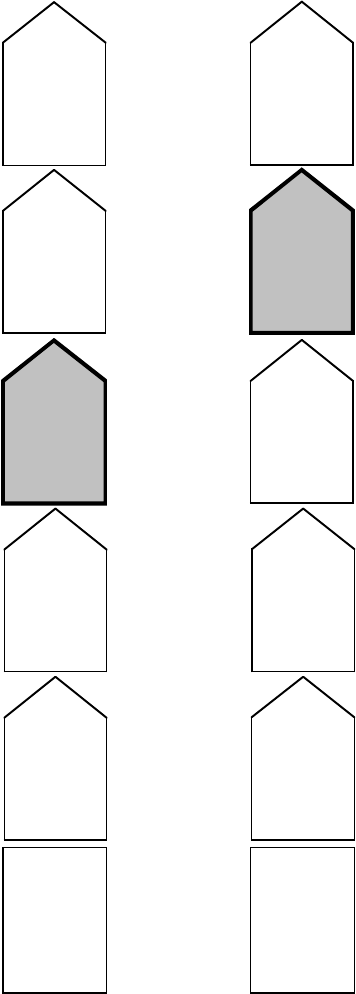
FIGURE 5.3
Analyze gathered information.
FIGURE 5.4
Prepare initial question sets.
Initial
Information
Gathering
Gather publicly
available
information
Gather
information from
the client
Analyze
gathered
information
Prepare initial
question sets
Develop and
populate template
for final report
Initial
Information
Gathering
Gather publicly
available
information
Gather
information from
the client
Analyze gathered
information
Prepare
initial
question sets
Develop and
populate template
for final report
AU1706_book.fm Page 124 Tuesday, August 17, 2004 11:02 AM
Initial Information Gathering 125
have enough information so that you can develop a good initial set of questions
because you have researched the company and a have an understanding of what they
do. There are some areas of the question sets that you will not be able to address,
such as things that are organization specific or about any specific business processes.
These more specific items will be addressed in the next phase, where time is allotted
to finalizing the question sets. For now, however, you can complete a very substantial
part of the question sets.
The question sets should be based on the answers to the initial questionnaire,
client documentation review, and the general research about the company, all of
which should have been done in the initial preparation phase of the assessment. The
main rule when developing the question sets is “don’t reinvent the wheel.” You
should start with sample questionnaires and questions you have used in the past and
then modify them based on the initial research performed in this phase and as you
go through the rest of the assessment. The appendices contain some sample question
sets that can be used as a starting point in developing the questions for the assessment.
Remember that the time to perform these assessments is usually limited, so you
should take advantage of any efficiency that can be gained in the process.
As you develop the questionnaires, keep in mind that the question sets are there
to guide the conversation with the client and they should not be used as a strict
checklist. When you discuss these topics with clients, the conversation can be all over
the map depending on how it goes. The purpose of the question sets is to help bring
structure to the conversation and to help you ensure that all relevant questions are asked.
The question sets will include two types of questions:
• Business process–related questions
•Traditional security process–related questions based on the interviewee’s
job function
The question sets developed in this phase will be generic, and the same ones
can be used for all interviews. In the next phase (Chapter 6 — Business Process
Review), the question sets will be modified to include questions specific to business
process owners.
BUSINESS PROCESS-RELATED QUESTIONS
When developing the initial question sets, some standard questions for each of the
areas listed above can be used as a starting point and can be modified in the next
phase. These standard questions or topics should be used for all the people you
interview because these topics are general and applicable to anyone you talk to
during the assessment. The following list includes the general categories as well as
questions for each category:
• Significant business processes and supporting technologies
– Describe how the business process works.
– What are the critical roles in the process, and do backups exist in the
event that key individuals are not present?
– What technology supports this business process?
AU1706_book.fm Page 125 Tuesday, August 17, 2004 11:02 AM
126 A Practical Guide to Security Assessments
– Who is responsible for managing the supporting technology?
– If the supporting technology was unavailable and this business process
could not occur, what are the impacts related to revenue, operations,
legal or regulatory concerns, and reputation damage?
– What is the tolerable downtime for the technology supporting this
business process?
– Are there any manual or other workarounds that can be done while the
technology is unavailable? For how long can the workaround be done?
– What critical data is generated as a result of this process and where
does it reside?
• Integration with other departments
– Dependencies between departments
– System integration and determination of single points of failure
–Transmission of information
•Past security incidents (questions for each incident)
– What was the nature of the security incident?
–How soon did you become aware of the incident? Did you find out
because of a documented process or by accident (e.g., happened to be
talking to somebody)?
– What was the reaction?
– What was the impact of the incident?
– What has been done to prevent such incidents from happening in the
future?
• Planned initiatives
– Some examples of initiatives that can be asked about include:
–Offering services via the Internet — e.g., e-commerce, content
– Change in location
– Outsourcing processes or technology
– Use of Application Service Providers for key business processes
– Deployment of a major application
–Will the company be required to comply with certain regulations in
the future (HIPAA, GLBA, etc.)?
• Other interviewee-specific questions
– Questions can be added here that are specific to the business based on
what you have learned about the company so far.
The topics and questions above are generic in nature and are there to serve as
a guide for the conversation. You might already know some of the information related
to what is listed above and if so, you can modify the questions accordingly. They
are also applicable to almost any business process owner to whom you talk.
In the next few sections, we will discuss the specific questions listed above. The
entire set of business process–related questions is in Appendix B.
Significant Business Processes and Supporting Technologies
The significant business processes will drive the rest of the security assessment.
They will help determine where to focus your efforts relative to process analysis
AU1706_book.fm Page 126 Tuesday, August 17, 2004 11:02 AM
Initial Information Gathering 127
and supporting technologies in determining security weaknesses. Note that some of
the significant business processes should already be known at least at a high level
based on the information gathered thus far. For each of the significant business
processes, you should have a structured discussion with the appropriate subject
matter expert to help ensure that you are capturing the relevant information. Below
is a detailed discussion of specific questions you can ask related to significant
business processes and supporting technologies. These questions are generic and
can be used for any business process subject matter expert. To the extent that you
can customize the questions for the specific people you will interview, you should
do so. In the next phase, time is allotted for finalizing the question sets, so modifi-
cations can be made up until that time. As you discuss the processes, some or all
of the questions might be answered during the course of the conversation. These
questions will help ensure that you gain a comprehensive level of knowledge about
the different business processes.
As with the other questionnaires contained in the appendices, the questions are
there to serve as a guide and help ensure that all pertinent questions have been
answered. Below are questions and topics that should be addressed for each of the
significant business processes:
• Describe how the business process works — This is a general question to
start the discussion of specifics about the business process. Here, process
owners can talk about what they do and how they do it. This is a good
way to start the discussion because it provides you an understanding of
the process as well as other aspects, which will be discussed in the next
questions.
• What are the critical roles in the process and do backups exist in the event
that key individuals are not present? — Understanding the roles and
responsibilities as they relate to the business process is important for a
few reasons. First, you can determine whether any segregation of duties
issues exist, and if they exist, whether any mitigating controls are present.
Second, you can determine whether there is a dependency on specific
people to ensure the process is running. You should be particularly inter-
ested if there is a dependency that has a security implication (e.g., only
one person can administer a particular application or only one person has
a particular skill set that is critical). Third, you can determine whether
someone owns the key responsibilities related to the business process. Own-
ership is a fundamental concept in information security — without own-
ership, there is no accountability or assurance that tasks will be completed.
• What technology supports this business process? — Understanding the
supporting technology to determine what warrants further examination is
the purpose of this question. In this question, technology refers to critical
servers, applications, infrastructure, and any other technology that sup-
ports the process. In addition, things like general network connectivity,
Internet connectivity, printing services or the availability of a third-party
ASP (Application Service Provider) should be considered. When deter-
mining the key technologies that support the process, it is best to document
AU1706_book.fm Page 127 Tuesday, August 17, 2004 11:02 AM
..................Content has been hidden....................
You can't read the all page of ebook, please click here login for view all page.
